We provide real 300-710 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Cisco 300-710 Exam quickly & easily. The 300-710 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Cisco 300-710 dumps pdf and vce product and material, you can easily pass the 300-710 exam.
Free demo questions for Cisco 300-710 Exam Dumps Below:
NEW QUESTION 1
An organization is migrating their Cisco ASA devices running in multicontext mode to Cisco FTD devices. Which action must be taken to ensure that each context on the Cisco ASA is logically separated in the Cisco FTD devices?
- A. Add a native instance to distribute traffic to each Cisco FTD context.
- B. Add the Cisco FTD device to the Cisco ASA port channels.
- C. Configure a container instance in the Cisco FTD for each context in the Cisco ASA.
- D. Configure the Cisco FTD to use port channels spanning multiple networks.
Answer: C
NEW QUESTION 2
On the advanced tab under inline set properties, which allows interfaces to emulate a passive interface?
- A. transparent inline mode
- B. TAP mode
- C. strict TCP enforcement
- D. propagate link state
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/640/configuration/guide/fpmc-config- guide-v64/inline_sets_and_passive_interfaces_for_firepower_threat_defense.html
NEW QUESTION 3
Refer to the exhibit.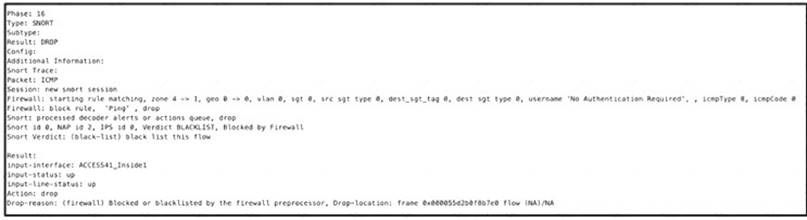
A systems administrator conducts a connectivity test to their SCCM server from a host machine and gets no response from the server. Which action ensures that the ping packets reach the destination and that the host receives replies?
- A. Create an access control policy rule that allows ICMP traffic.
- B. Configure a custom Snort signature to allow ICMP traffic after Inspection.
- C. Modify the Snort rules to allow ICMP traffic.
- D. Create an ICMP allow list and add the ICMP destination to remove it from the implicit deny list.
Answer: A
NEW QUESTION 4
An organization is configuring a new Cisco Firepower High Availability deployment. Which action must be taken to ensure that failover is as seamless as possible to end users?
- A. Set up a virtual failover MAC address between chassis.
- B. Use a dedicated stateful link between chassis.
- C. Load the same software version on both chassis.
- D. Set the same FQDN for both chassis.
Answer: B
NEW QUESTION 5
Which Cisco Firepower feature is used to reduce the number of events received in a period of time?
- A. rate-limiting
- B. suspending
- C. correlation
- D. thresholding
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firesight/541/firepower-module-user-guide/asa- firepower-module-user-guide-v541/Intrusion-Global-Threshold.html
NEW QUESTION 6
When do you need the file-size command option during troubleshooting with packet capture?
- A. when capture packets are less than 16 MB
- B. when capture packets are restricted from the secondary memory
- C. when capture packets exceed 10 GB
- D. when capture packets exceed 32 MB
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-config- guide-v62/troubleshooting_the_system.html
NEW QUESTION 7
An engineer must build redundancy into the network and traffic must continuously flow if a redundant switch in front of the firewall goes down. What must be configured to accomplish this task?
- A. redundant interfaces on the firewall cluster mode and switches
- B. redundant interfaces on the firewall noncluster mode and switches
- C. vPC on the switches to the interface mode on the firewall duster
- D. vPC on the switches to the span EtherChannel on the firewall cluster
Answer: D
Explanation:
Reference: https://www.ciscolive.com/c/dam/r/ciscolive/us/docs/2018/pdf/BRKSEC-2020.pdf
NEW QUESTION 8
While integrating Cisco Umbrella with Cisco Threat Response, a network security engineer wants to automatically push blocking of domains from the Cisco Threat Response interface to Cisco Umbrella. Which API meets this requirement?
- A. investigate
- B. reporting
- C. enforcement
- D. REST
Answer: D
NEW QUESTION 9
Which command is run at the CLI when logged in to an FTD unit, to determine whether the unit is managed locally or by a remote FMC server?
- A. system generate-troubleshoot
- B. show configuration session
- C. show managers
- D. show running-config | include manager
Answer: C
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/command_ref/b_Command_Reference_for_Firepower_Threat_Defense/c_3.html
NEW QUESTION 10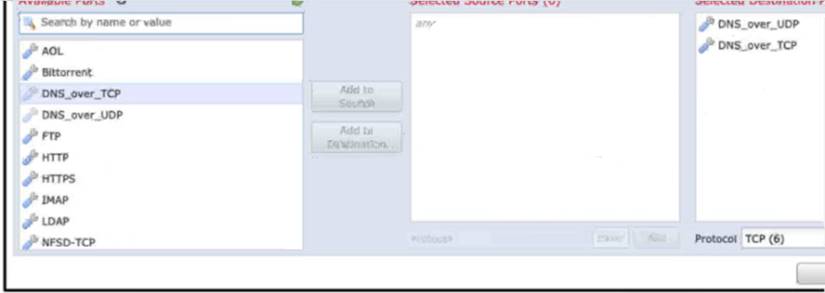
Refer to the exhibit An engineer is modifying an access control pokey to add a rule to inspect all DNS traffic that passes through the firewall After making the change and deploying the pokey they see that DNS traffic is not bang inspected by the Snort engine What is the problem?
- A. The rule must specify the security zone that originates the traffic
- B. The rule must define the source network for inspection as well as the port
- C. The action of the rule is set to trust instead of allow.
- D. The rule is configured with the wrong setting for the source port
Answer: C
NEW QUESTION 11
An organization has seen a lot of traffic congestion on their links going out to the internet There is a Cisco Firepower device that processes all of the traffic going to the internet prior to leaving the enterprise. How is the congestion alleviated so that legitimate business traffic reaches the destination?
- A. Create a flexconfig policy to use WCCP for application aware bandwidth limiting
- B. Create a VPN policy so that direct tunnels are established to the business applications
- C. Create a NAT policy so that the Cisco Firepower device does not have to translate as many addresses
- D. Create a QoS policy rate-limiting high bandwidth applications
Answer: D
NEW QUESTION 12
What are two application layer preprocessors? (Choose two.)
- A. CIFS
- B. IMAP
- C. SSL
- D. DNP3
- E. ICMP
Answer: BC
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-config-guide-v60/Applic
NEW QUESTION 13
Remote users who connect via Cisco AnyConnect to the corporate network behind a Cisco FTD device report that they get no audio when calling between remote users using their softphones. These same users can call internal users on the corporate network without any issues. What is the cause of this issue?
- A. The hairpinning feature is not available on FTD.
- B. Split tunneling is enabled for the Remote Access VPN on FTD
- C. FTD has no NAT policy that allows outside to outside communication
- D. The Enable Spoke to Spoke Connectivity through Hub option is not selected on FTD.
Answer: A
NEW QUESTION 14
An engainer must add DNS-specific rules to me Cisco FTD intrusion policy. The engineer wants to use the rules currently in the Cisco FTD Snort database that are not already enabled but does not want to enable more than are needed. Which action meets these requirements?
- A. Change the dynamic state of the rule within the policy.
- B. Change the base policy to Security over Connectivity.
- C. Change the rule state within the policy being used.
- D. Change the rules using the Generate and Use Recommendations feature.
Answer: C
NEW QUESTION 15
A network engineer implements a new Cisco Firepower device on the network to take advantage of its intrusion detection functionality. There is a requirement to analyze the traffic going across the device, alert on any malicious traffic, and appear as a bump in the wire How should this be implemented?
- A. Specify the BVl IP address as the default gateway for connected devices.
- B. Enable routing on the Cisco Firepower
- C. Add an IP address to the physical Cisco Firepower interfaces.
- D. Configure a bridge group in transparent mode.
Answer: D
Explanation:
Traditionally, a firewall is a routed hop and acts as a default gateway for hosts that connect to one of its screened subnets. A transparent firewall, on the other hand, is a Layer 2 firewall that acts like a “bump in the wire,” or a “stealth firewall,” and is not seen as a router hop to connected devices. However, like any other firewall, access control between interfaces is controlled, and all of the usual firewall checks are in place. Layer 2 connectivity is achieved by using a "bridge group" where you group together the inside and outside interfaces for a network, and the ASA uses bridging techniques to pass traffic between the interfaces. Each bridge group includes a Bridge Virtual Interface (BVI) to which you assign an IP address on the network. You can have multiple bridge groups for multiple networks. In transparent mode, these bridge groups cannot communicate with each other.
https://www.cisco.com/c/en/us/td/docs/security/asa/asa97/configuration/general/asa-97-general-config/intro-fw.
NEW QUESTION 16
Which command is typed at the CLI on the primary Cisco FTD unit to temporarily stop running high- availability?
- A. configure high-availability resume
- B. configure high-availability disable
- C. system support network-options
- D. configure high-availability suspend
Answer: B
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/610/configuration/guide/fpmc-config- guide-v61/firepower_threat_defense_high_availability.html
NEW QUESTION 17
An organization is setting up two new Cisco FTD devices to replace their current firewalls and cannot have any network downtime During the setup process, the synchronization between the two devices is failing What action is needed to resolve this issue?
- A. Confirm that both devices have the same port-channel numbering
- B. Confirm that both devices are running the same software version
- C. Confirm that both devices are configured with the same types of interfaces
- D. Confirm that both devices have the same flash memory sizes
Answer: B
NEW QUESTION 18
A security engineer must configure a Cisco FTD appliance to inspect traffic coming from the internet. The Internet traffic will be mirrored from the Cisco Catalyst 9300 Switch. Which configuration accomplishes the task?
- A. Set interface configuration mode to none.
- B. Set the firewall mode to transparent.
- C. Set the firewall mode to routed.
- D. Set interface configuration mode to passive.
Answer: D
NEW QUESTION 19
After using Firepower for some time and learning about how it interacts with the network, an administrator is trying to correlate malicious activity with a user Which widget should be configured to provide this visibility on the Cisco Firepower dashboards?
- A. Custom Analysis
- B. Current Status
- C. Current Sessions
- D. Correlation Events
Answer: A
NEW QUESTION 20
......
Thanks for reading the newest 300-710 exam dumps! We recommend you to try the PREMIUM Downloadfreepdf.net 300-710 dumps in VCE and PDF here: https://www.downloadfreepdf.net/300-710-pdf-download.html (260 Q&As Dumps)
