It is more faster and easier to pass the Cisco 350-701 exam by using Free Cisco Implementing and Operating Cisco Security Core Technologies questuins and answers. Immediate access to the Most up-to-date 350-701 Exam and find the same core area 350-701 questions with professionally verified answers, then PASS your exam with a high score now.
Free demo questions for Cisco 350-701 Exam Dumps Below:
NEW QUESTION 1
Which two activities can be done using Cisco DNA Center? (Choose two.)
- A. DHCP
- B. design
- C. accounting
- D. DNS
- E. provision
Answer: BE
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/cloud-systems-management/network-automation-and-management/dna-center/1-2-1/user_guide/b_dnac_ug_1_2_1/b_dnac_ug_1_2_chapter_00.pdf
NEW QUESTION 2
Which API is used for Content Security?
- A. NX-OS API
- B. IOS XR API
- C. OpenVuln API
- D. AsyncOS API
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/security_management/sma/sma12-0/api/b_SMA_API_12/test_chapter_01.html
NEW QUESTION 3
An engineer configured a new network identity in Cisco Umbrella but must verify that traffic is being routed through the Cisco Umbrella network. Which action tests the routing?
- A. Ensure that the client computers are pointing to the on-premises DNS servers.
- B. Enable the Intelligent Proxy to validate that traffic is being routed correctly.
- C. Add the public IP address that the client computers are behind to a Core Identity.
- D. Browse to http://welcome.umbrella.com/ to validate that the new identity is working.
Answer: B
NEW QUESTION 4
Why would a user choose an on-premises ESA versus the CES solution?
- A. Sensitive data must remain onsite.
- B. Demand is unpredictable.
- C. The server team wants to outsource this service.
- D. ESA is deployed inline.
Answer: A
NEW QUESTION 5
Which two behavioral patterns characterize a ping of death attack? (Choose two.)
- A. The attack is fragmented into groups of 16 octets before transmission.
- B. The attack is fragmented into groups of 8 octets before transmission.
- C. Short synchronized bursts of traffic are used to disrupt TCP connections.
- D. Malformed packets are used to crash systems.
- E. Publicly accessible DNS servers are typically used to execute the attack.
Answer: BD
Explanation:
Reference: https://en.wikipedia.org/wiki/Ping_of_death
NEW QUESTION 6
Refer to the exhibit.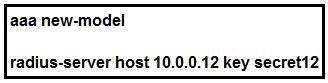
Which statement about the authentication protocol used in the configuration is true?
- A. The authentication request contains only a password
- B. The authentication request contains only a username
- C. The authentication and authorization requests are grouped in a single packet.
- D. There are separate authentication and authorization request packets.
Answer: C
NEW QUESTION 7
Which Cisco solution does Cisco Umbrella integrate with to determine if a URL is malicious?
- A. AMP
- B. AnyConnect
- C. DynDNS
- D. Talos
Answer: D
NEW QUESTION 8
An engineer is configuring AMP for endpoints and wants to block certain files from executing. Which outbreak control method is used to accomplish this task?
- A. device flow correlation
- B. simple detections
- C. application blocking list
- D. advanced custom detections
Answer: C
NEW QUESTION 9
Where are individual sites specified to be blacklisted in Cisco Umbrella?
- A. application settings
- B. content categories
- C. security settings
- D. destination lists
Answer: D
NEW QUESTION 10
Which command enables 802.1X globally on a Cisco switch?
- A. dot1x system-auth-control
- B. dot1x pae authenticator
- C. authentication port-control auto
- D. aaa new-model
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/routers/nfvis/switch_command/b-nfvis-switch-command-reference/802_1x_commands.html
NEW QUESTION 11
Which Cisco product provides proactive endpoint protection and allows administrators to centrally manage the deployment?
- A. NGFW
- B. AMP
- C. WSA
- D. ESA
Answer: B
NEW QUESTION 12
DRAG DROP
Drag and drop the Firepower Next Generation Intrustion Prevention System detectors from the left onto the correct definitions on the right.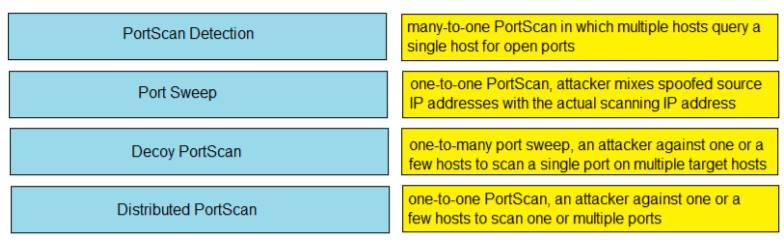
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/640/configuration/guide/fpmc-config-guide-v64/detecting_specific_threats.html
NEW QUESTION 13
Which cloud service model offers an environment for cloud consumers to develop and deploy applications without needing to manage or maintain the underlying cloud infrastructure?
- A. PaaS
- B. XaaS
- C. IaaS
- D. SaaS
Answer: A
NEW QUESTION 14
How does Cisco Umbrella archive logs to an enterprise- owned storage?
- A. by using the Application Programming Interface to fetch the logs
- B. by sending logs via syslog to an on-premises or cloud-based syslog server
- C. by the system administrator downloading the logs from the Cisco Umbrella web portal
- D. by being configured to send logs to a self-managed AWS S3 bucket
Answer: D
Explanation:
Reference: https://docs.umbrella.com/deployment-umbrella/docs/log-management
NEW QUESTION 15
Which two features are used to configure Cisco ESA with a multilayer approach to fight viruses and malware? (Choose two.)
- A. Sophos engine
- B. white list
- C. RAT
- D. outbreak filters
- E. DLP
Answer: AD
NEW QUESTION 16
When wired 802.1X authentication is implemented, which two components are required? (Choose two.)
- A. authentication server: Cisco Identity Service Engine
- B. supplicant: Cisco AnyConnect ISE Posture module
- C. authenticator: Cisco Catalyst switch
- D. authenticator: Cisco Identity Services Engine
- E. authentication server: Cisco Prime Infrastructure
Answer: AC
Explanation:
Reference: https://www.lookingpoint.com/blog/ise-series-802.1x
NEW QUESTION 17
What are two Detection and Analytics Engines of Cognitive Threat Analytics? (Choose two.)
- A. data exfiltration
- B. command and control communication
- C. intelligent proxy
- D. snort
- E. URL categorization
Answer: AB
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/products/collateral/security/cognitive-threat-analytics/at-a-glance-c45-736555.pdf
NEW QUESTION 18
Which solution protects hybrid cloud deployment workloads with application visibility and segmentation?
- A. Nexus
- B. Stealthwatch
- C. Firepower
- D. Tetration
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/solutions/security/secure-data-center-solution/index.html#~products
NEW QUESTION 19
Which network monitoring solution uses streams and pushes operational data to provide a near real-time view of activity?
- A. SNMP
- B. SMTP
- C. syslog
- D. model-driven telemetry
Answer: D
Explanation:
Reference: https://developer.cisco.com/docs/ios-xe/#!streaming-telemetry-quick-start-guide
NEW QUESTION 20
Which technology is used to improve web traffic performance by proxy caching?
- A. WSA
- B. Firepower
- C. FireSIGHT
- D. ASA
Answer: A
NEW QUESTION 21
Which Talos reputation center allows you to track the reputation of IP addresses for email and web traffic?
- A. IP Blacklist Center
- B. File Reputation Center
- C. AMP Reputation Center
- D. IP and Domain Reputation Center
Answer: D
NEW QUESTION 22
Which feature is configured for managed devices in the device platform settings of the Firepower Management Center?
- A. quality of service
- B. time synchronization
- C. network address translations
- D. intrusion policy
Answer: B
NEW QUESTION 23
......
P.S. Certshared now are offering 100% pass ensure 350-701 dumps! All 350-701 exam questions have been updated with correct answers: https://www.certshared.com/exam/350-701/ (102 New Questions)
