Actualtests offers free demo for 400-007 exam. "Cisco Certified Design Expert (CCDE v3.0) Written Exam", also known as 400-007 exam, is a Cisco Certification. This set of posts, Passing the Cisco 400-007 exam, will help you answer those questions. The 400-007 Questions & Answers covers all the knowledge points of the real exam. 100% real Cisco 400-007 exams and revised by experts!
Online 400-007 free questions and answers of New Version:
NEW QUESTION 1
Refer to the exhibit. OSPF is running as the IGP to provide reachability to all AS100 networks. R3 and R4 are the current ABRs at the boundary of OSPF Area0 and Areal. Now BGP must be deployed within AS 100 because it will be receiving. Internet routes from its eBGP peers (the service provider) connected to R1 and R2.
What is an optimal solution for this deployment to configure BGP relationships and redistribute BGP learned routes into OSPF?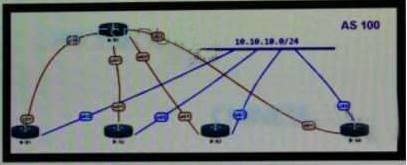
- A. R5 should be configured as a route reflector for R1, R2, R3 and R4. BGP routes must beredistributed at R1 and R2 into OSPF.
- B. Configuration should be set up with R1 and R2, and R3 in one sub AS, with and R4 in another,and redistribution at R1 and R2.
- C. A full mesh should be deployed between all the routers with mutual redistribution to take place atR1 and R2.
- D. R1, R2, R3 and R4 must be set up with a neighbor relationship with R5 only must not be a routereflector.
Answer: C
NEW QUESTION 2
A multicast network is sing Bidirectional PIM. Which two combined actions achieve high availability
so that two RPs within the same network can act in a redundant manner? (Choose two)
- A. Use two phantom RP addresses
- B. Manipulate the administration distance of the unicast routes to the two RPs
- C. Manipulate the multicast routing table by creating static mroutes to the two RPs
- D. Advertise the two RP addresses in the routing protocol
- E. Use anycast RP based on MSDP peering between the two RPs
- F. Control routing to the two RPs through a longest match prefix
Answer: AF
NEW QUESTION 3
Which effect of using ingress filtering to prevent spoofed addresses on a network design is true?
- A. It reduces the effectiveness of DDoS attacks when associated with DSCP remarking to Scavenger.
- B. It protects the network Infrastructure against spoofed DDoS attacks.
- C. It Classifies bogon traffic and remarks it with DSCP bulk.
- D. It filters RFC 1918 IP addresses.
Answer: B
NEW QUESTION 4
Company XYZ is planning to deploy primary and secondary (disaster recovery) data center sites. Each of these sites will have redundant SAN fabrics and data protection is expected between the data center sites. The sites are 100 miles (160 km) apart and target RPO/RTO are 3 hrs and 24 hrs, respectively. Which two considerations must Company XYZ bear in mind when deploying replication in their scenario? (Choose two.)
- A. Target RPO/RTO requirements cannot be met due to the one-way delay introduced by thedistance between sites.
- B. VSANs must be routed between sites to isolate fault domains and increase overall availability.
- C. Synchronous data replication must be used to meet the business requirements
- D. Asynchronous data replication should be used in this scenario to avoid performance impact in theprimary site.
- E. VSANs must be extended from the primary to the secondary site to improve performance andavailability.
Answer: BD
NEW QUESTION 5
Which two aspects are considered when designing a dual hub dual DMVPN cloud topology? (Choose two )
- A. will only work with single-tier headend architecture
- B. hub sites must connect to both DMVPN clouds
- C. recommended for high availability
- D. spoke-to-spoke traffic will transit the hub unless spokes exchange dynamic routing directly
- E. requires all sites to have dual Internet connections
Answer: AC
NEW QUESTION 6
Which technology is an open-source infrastructure automation tool that automates repetitive tasks
for users who work in networks such as cloud provisioning and intraservice orchestration?
- A. Ansible
- B. Contrail
- C. Java
- D. Jinja2
Answer: A
NEW QUESTION 7
SDWAN networks capitalize the usage of broadband Internet links over traditional MPLS links to offer more cost benefits to enterprise customers. However, due to the insecure nature of the public Internet, it is mandatory to use encryption of traffic between any two SDWAN edge devices installed behind NAT gateways.
Which overlay method can provide optimal transport over unreliable underlay networks that are behind NAT gateways?
- A. TLS
- B. DTLS
- C. IPsec
- D. GRE
Answer: C
NEW QUESTION 8
Company XYZ needs advice in redesigning their legacy Layer 2 infrastructure.
Which technology should be included in the design to minimize or avoid convergence delays due to STP or FHRP and provide a loop-free topology?
- A. Use switch clustering in the access layer.
- B. Use switch clustering in the core/distribution layer.
- C. Use spanning-tree PortFast.
- D. Use BFD.
Answer: B
NEW QUESTION 9
Which design benefit of PortF ast is true?
- A. PortFast does not generate a spanning tree topology change hen a station on a port is connectedor disconnected
- B. PortFast disables spanning tree on the port, which puts the port into the forwarding stateimmediately after it is connected
- C. PortFast allows small, unmanaged switches to be plugged into ports of access switches withoutrisking switch loops
- D. PortFast detects one-way communications on the physical port, which prevents switch loops
- E. PortFast prevents switch loops that are caused by a unidirectional point to point link condition onRapid PVST+ and MST
- F. PortFast prevents switched traffic from traversing suboptimal paths on the network
Answer: A
NEW QUESTION 10
According to the CIA triad principles for network security design, which principle should be priority for a Zero Trust network?
- A. requirement for data-in-motion encryption and 2FA authentication
- B. requirement for data-at-rest encryption foe user identification within the VPN terminationhardware
- C. categorization of systems, data, and enterprise BYOD assets that are connected to networkzones based on individual privacy needs
- D. ensuring that authorized users have high-availability system access from defined zones todefined systems or zones
Answer: A
NEW QUESTION 11
Which protocol does an SD-Access wireless Access Point use for its fabric data plane?
- A. GRE
- B. MPLS
- C. VXLAN
- D. LISP
- E. CAPWAP
Answer: C
NEW QUESTION 12
Which two types of planning approaches are used to develop business-driven network designs and to facilitate the design decisions? (Choose two)
- A. cost optimization approach
- B. strategic planning approach
- C. modular approach
- D. tactical planning approach
- E. business optimization approach
Answer: BD
NEW QUESTION 13
What best describes the difference between Automation and Orchestration?
- A. Automation refers to an automatic process for completing a single task and Orchestration refersto assembling and coordinating a set of tasks and conditions.
- B. Automation describes a hands-off configuration process while Orchestration refers to sets ofautomation tasks that require the network administrator to coordinate
- C. Automation refers to an automatic process for completing multiple tasks with conditions andOrchestration refers to executing tasks in parallel.
- D. Automation refers to scripting languages (Pytho
- E. Ansible etc.) and Orchestration refers tocommercial products that control configuration deployment
Answer: A
NEW QUESTION 14
SD-WAN can be used to provide secure connectivity to remote offices, branch offices, campus networks, data centers, and the cloud over any type of IP-based underlay transport network. Which two statements describe SD WAN solutions? (Choose two.)
- A. SD-WAN networks are inherently protected against slow performance.
- B. Control and data forwarding planes are kept separate.
- C. Improved operational efficiencies result In cost savings.
- D. Solutions include centralized orchestration, control, and zero-touch provisioning.
- E. Solutions allow for variations of commodity and specialized switching hardware.
Answer: BD
NEW QUESTION 15
Company XYZ runs OSPF in their network. A design engineer decides to implement hot-potato routing architecture.
How can this implementation be achieved?
- A. Enable iBGP and apply prepend to ensure all prefixes will have the same length of the AS pathattribute value.
- B. Redistribute the external prefixes onto OSPF and ensure the total metric calculation includes onlythe ext value and the value is the same in all ASBRs.
- C. Enable OSPF load-balancing over unequal cost path.
- D. Redistribute the external prefixes onto OSPF and ensure that the total metric calculation includesexternal internal values.
Answer: D
NEW QUESTION 16
......
Recommend!! Get the Full 400-007 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/400-007/ (New 0 Q&As Version)
