Exam Code: JN0-230 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Security - Associate (JNCIA-SEC)
Certification Provider: Juniper
Free Today! Guaranteed Training- Pass JN0-230 Exam.
Check JN0-230 free dumps before getting the full version:
NEW QUESTION 1
BY default, revenue interface are placed into which system-defined security zone on an SRX series device?
- A. Trust
- B. Null
- C. Junos-trust
- D. untrust
Answer: D
NEW QUESTION 2
Your company has been assigned one public IP address. You want to enable internet traffic to reach multiple servers in your DMZ that are configured with private address.
In this scenario, which type of NAT would be used to accomplish this tasks?
- A. Static NAT
- B. Destination NAT
- C. Source NAT
- D. NAT without PAT
Answer: B
NEW QUESTION 3
Referring to the exhibit.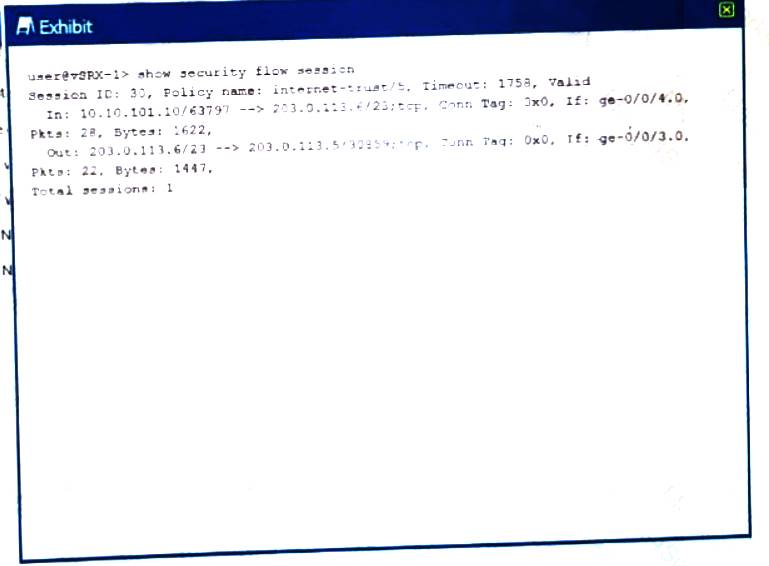
Which type of NAT is being performed?
- A. Source NAT with PAT
- B. Source NAT without PAT
- C. Destination NAT without PAT
- D. Destination NAT with PAT
Answer: A
NEW QUESTION 4
Your company uses SRX Series devices to secure the edge of the network. You are asked protect the company from ransom ware attacks.
Which solution will satisfy this requirement?
- A. Sky ATP
- B. AppSecure
- C. Unified security policies
- D. screens
Answer: A
NEW QUESTION 5
What are the valid actions for a source NAT rule in J-Web? (choose three.)
- A. On
- B. Off
- C. Pool
- D. Source
- E. interface
Answer: BCE
Explanation:
Explanation
https://www.juniper.net/documentation/en_US/junos/topics/topic-map/nat-security-source-and-source-pool.html
NEW QUESTION 6
What are two characteristic of static NAT SRX Series devices? (Choose two.)
- A. Source and destination NAT rules take precedence over static NAT rules.
- B. A reverse mapping rule is automatically created for the source translation.
- C. Static NAT rule take precedence over source and destination NAT rules.
- D. Static rules cannot coexist with destination NAT rules on the same SRX Series device configuration.
Answer: BC
NEW QUESTION 7
Which flow module components handles processing for UTM?
- A. Policy
- B. Zones
- C. Services
- D. Screen options
Answer: C
NEW QUESTION 8
Which two statements are correct about functional zones? (Choose two.)
- A. A functional zone uses security policies to enforce rules for transit traffic.
- B. Traffic received on the management interface in the functional zone cannot transit out other interface.
- C. Functional zones separate groups of users based on their function.
- D. A function is used for special purpose, such as management interface
Answer: BD
NEW QUESTION 9
You are designing a new security policy on an SRX Series device. You must block an application and log all occurrence of the application access attempts.
In this scenario, which two actions must be enabled in the security policy? (Choose two.)
- A. Log the session initiations
- B. Enable a reject action
- C. Log the session closures
- D. Enable a deny action
Answer: AD
NEW QUESTION 10
On an SRX device, you want to regulate traffic base on network segments. In this scenario, what do you configure to accomplish this task?
- A. Screens
- B. Zones
- C. ALGs
- D. NAT
Answer: B
NEW QUESTION 11
Which type of security policy protect restricted services from running on non-standard ports?
- A. Application firewall
- B. IDP
- C. Sky ATP
- D. antivirus
Answer: B
NEW QUESTION 12
Which three actions would be performed on traffic traversing an IPsec VPAN? (Choose three.)
- A. Port forwarding
- B. Authentication
- C. Encryption
- D. Deep inspection
- E. Payload verification
Answer: BCE
NEW QUESTION 13
Which statements is correct about global security policies?
- A. Global policies allow you to regulate traffic with addresses and applications, regardless of their security zones.
- B. Traffic matching global is not added to the session table.
- C. Global policies eliminate the need to assign interface to security zones.
- D. Global security require you to identify a source and destination zone.
Answer: A
NEW QUESTION 14
Which statement about IPsec is correct?
- A. IPsec can be used to transport native Layer 2 packets.
- B. IPsec can provide encapsulation but not encryption
- C. IPsec is a standards-based protocol.
- D. IPsec is used to provide data replication
Answer: C
NEW QUESTION 15
What is the purpose of the Shadow Policies workspace in J-Web?
- A. The Shadow Policies workspace shows unused security policies due to policy overlap.
- B. The Shadow Policies workspace shows unused IPS policies due to policy overlap.
- C. The Shadow Policies workspace shows used security policies due to policy overlap
- D. The Shadow Policies workspace shows used IPS policies due to policy overlap
Answer: A
NEW QUESTION 16
On an SRX Series device, how should you configure your IKE gateway if the remote endpoint is a branch office-using a dynamic IP address?
- A. Configure the IPsec policy to use MDS authentication.
- B. Configure the IKE policy to use aggressive mode.
- C. Configure the IPsec policy to use aggressive mode.
- D. Configure the IKE policy to use a static IP address
Answer: B
NEW QUESTION 17
You are concerned that unauthorized traffic is using non-standardized ports on your network.
In this scenario, which type of security feature should you implement?
- A. Application firewall
- B. Sky ATP
- C. Firewall filters
- D. Zone-based policies
Answer: A
NEW QUESTION 18
You want to generate reports from the l-Web on an SRX Series device. Which logging mode would you use in this scenario?
- A. Syslog
- B. Stream
- C. Event
- D. local
Answer: B
NEW QUESTION 19
Which two statements are true regarding zone-based security policies? (Choose two.)
- A. Zone-based policies must reference a source address in the match criteria.
- B. Zone-based policies must reference a URL category in the match criteria.
- C. Zone-based policies must reference a destination address in the match criteria
- D. Zone-based policies must reference a dynamic application in the match criteria.
Answer: AC
NEW QUESTION 20
Which two notifications are available when the antivirus engine detects and infected file? (Choose two.)
- A. e-mail notifications
- B. SNMP notifications
- C. SMS notifications
- D. Protocol-only notification
Answer: AD
NEW QUESTION 21
You want to integrate an SRX Series device with SKY ATP. What is the first action to accomplish task?
- A. Issue the commit script to register the SRX Series device.
- B. Copy the operational script from the Sky ATP Web UI.
- C. Create an account with the Sky ATP Web UI.
- D. Create the SSL VPN tunnel between the SRX Series device and Sky ATP.
Answer: C
NEW QUESTION 22
You have configured a Web filtering UTM policy?
Which action must be performed before the Web filtering UTM policy takes effect?
- A. The UTM policy must be linked to an egress interface
- B. The UTM policy be configured as a routing next hop.
- C. The UTM policy must be linked to an ingress interface.
- D. The UTM policy must be linked to a security policy
Answer: D
NEW QUESTION 23
Which two statements are true about UTM on an SRX340? (Choose two.)
- A. A default UTM policy is created.
- B. No default profile is created.
- C. No default UTM policy is created
- D. A default UTM profile is created
Answer: BC
NEW QUESTION 24
......
100% Valid and Newest Version JN0-230 Questions & Answers shared by Certstest, Get Full Dumps HERE: https://www.certstest.com/dumps/JN0-230/ (New 65 Q&As)
