Exam Code: NSE4_FGT-6.2 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Fortinet NSE 4 - FortiOS 6.2
Certification Provider: Fortinet
Free Today! Guaranteed Training- Pass NSE4_FGT-6.2 Exam.
Free NSE4_FGT-6.2 Demo Online For Fortinet Certifitcation:
NEW QUESTION 1
An administrator has configured a dialup IPsec VPN with XAuth. Which statement best describes what occurs during this scenario?
- A. Phase 1 negotiations will skip preshared key exchange.
- B. Only digital certificates will be accepted as an authentication method in phase 1.C
- C. Dialup clients must provide a username and password for authentication.
- D. Dialup clients must provide their local ID during phase 2 negotiations.
Answer: C
NEW QUESTION 2
Which statement is true regarding the policy ID number of a firewall policy?
- A. Defines the order in which rules are processed.
- B. Represents the number of objects used in the firewall policy.
- C. Required to modify a firewall policy using the CLI.
- D. Changes when firewall policies are reordered.
Answer: C
NEW QUESTION 3
Why must you use aggressive mode when a local FortiGate IPSec gateway hosts multiple dialup tunnels?
- A. In aggressive mode, the remote peers are able to provide their peer IDs in the first message.
- B. FortiGate is able to handle NATed connections only in aggressive mode.
- C. FortiClient only supports aggressive mode.
- D. Main mode does not support XAuth for user authentication.
Answer: A
NEW QUESTION 4
Examine the network diagram and the existing FGTI routing table shown in the exhibit, and then answer the following question: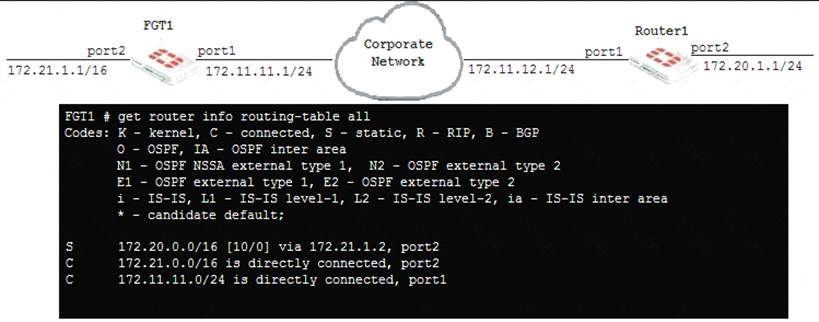
An administrator has added the following static route on FGTI.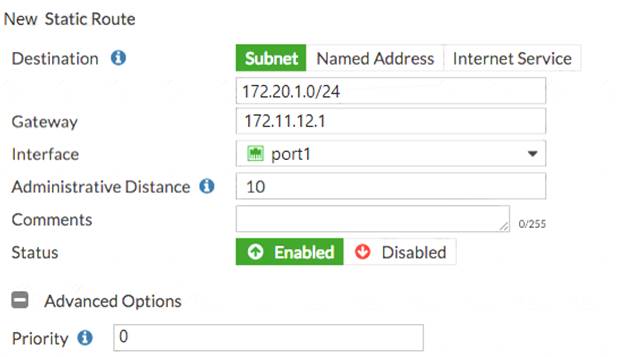
Since the change, the new static route is not showing up in the routing table. Given the information provided, which of the following describes the cause of this problem?
- A. The new route’s destination subnet overlaps an existing route.
- B. The new route’s Distance value should be higher than 10.
- C. The Gateway IP address is not in the same subnet as port1.
- D. The Priority is 0, which means that this route will remain inactive.
Answer: C
NEW QUESTION 5
Which statement is true regarding SSL VPN timers? (Choose two.)
- A. Allow to mitigate DoS attacks from partial HTTP requests.
- B. SSL VPN settings do not have customizable timers.
- C. Disconnect idle SSL VPN users when a firewall policy authentication timeout occurs.
- D. Prevent SSL VPN users from being logged out because of high network latency.
Answer: AD
NEW QUESTION 6
Examine the following web filtering log.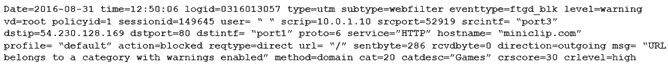
Which statement about the log message is true?
- A. The action for the category Games is set to block.
- B. The usage quota for the IP address 10.0.1.10 has expired
- C. The name of the applied web filter profile is default.
- D. The web site miniclip.com matches a static URL filter whose action is set to Warning.
Answer: C
NEW QUESTION 7
Which of the following conditions are required for establishing an IPSec VPN between two FortiGate devices? (Choose two.)
- A. If XAuth is enabled as a server in one peer, it must be enabled as a client in the other peer.
- B. If the VPN is configured as route-based, there must be at least one firewall policy with the action set toIPSec.
- C. If the VPN is configured as DialUp User in one peer, it must be configured as either Static IP Address or Dynamic DNS in the other peer.
- D. If the VPN is configured as a policy-based in one peer, it must also be configured as policy-based in the other peer.
Answer: AC
NEW QUESTION 8
HTTP Public Key Pinning (HPKP) can be an obstacle to implementing full SSL inspection. What solutions could resolve this problem? (Choose two.)
- A. Enable Allow Invalid SSL Certificates for the relevant security profile.
- B. Change web browsers to one that does not support HPKP.
- C. Exempt those web sites that use HPKP from full SSL inspection.
- D. Install the CA certificate (that is required to verify the web server certificate) stores of users’ computers.
Answer: BC
NEW QUESTION 9
Examine the IPS sensor configuration shown in the exhibit, and then answer the question below.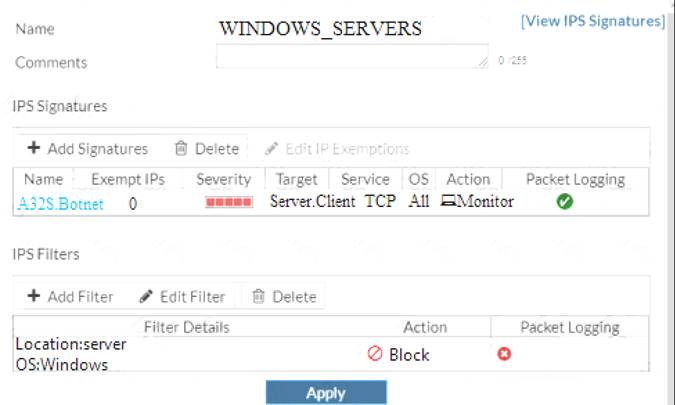
What are the expected actions if traffic matches this IPS sensor? (Choose two.)
- A. The sensor will gather a packet log for all matched traffic.
- B. The sensor will not block attackers matching the A32S.Botnet signature.
- C. The sensor will block all attacks for Windows servers.
- D. The sensor will reset all connections that match these signatures.
Answer: BC
NEW QUESTION 10
If the Issuer and Subject values are the same in a digital certificate, which type of entity was the certificate issued to?
- A. A CRL
- B. A person
- C. A subordinate CA
- D. A root CA
Answer: D
NEW QUESTION 11
View the exhibit. Which of the following statements is true regarding the configuration settings?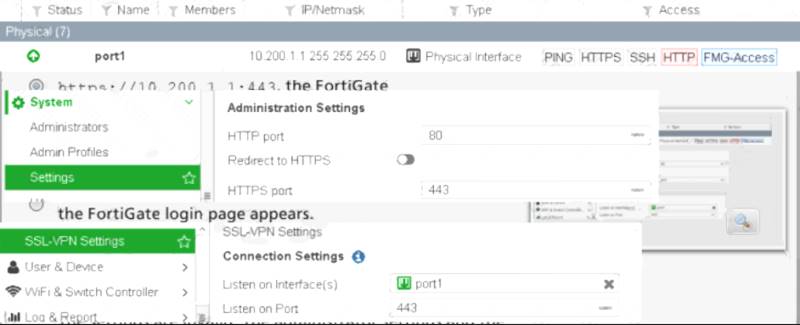
Response:
- A. When a remote user accesses https://10.200.1.1:443, the FortiGate login page appears.
- B. When a remote user accesses https://10.200.1.1:443, the FortiGate login page appears.
- C. When a remote user accesses http: //10.200.1.1 :443, the FortiGate login page appears.
- D. When a remote user accesses http: /110.200.1.1:443, the SSL VPN login page appears.
- E. The settings are invali
- F. The administrator settings and the SSL VPN settings cannot use the same port.
Answer: B
NEW QUESTION 12
An administrator is running the following sniffer command:
diagnose sniffer packet any “host 10.0.2.10” 3
What information will be included in the sniffer output? (Choose three.)
- A. IP header
- B. Ethernet header
- C. Packet payload
- D. Application header
- E. Interface name
Answer: ABC
NEW QUESTION 13
Which of the following are purposes of NAT traversal in IPsec? (Choose two.)
- A. To delete intermediary NAT devices in the tunnel path.
- B. To dynamically change phase 1 negotiation mode aggressive mode.
- C. To encapsulation ESP packets in UDP packets using port 4500.
- D. To force a new DH exchange with each phase 2 rekey.
Answer: AC
NEW QUESTION 14
By default, when logging to disk, when does FortiGate delete logs?
- A. 30 days
- B. 1 year
- C. Never
- D. 7 days
Answer: D
NEW QUESTION 15
You are configuring the root FortiGate to implement the security fabric. You are configuring port10 to communicate with a downstream FortiGate. View the default Edit Interface in the exhibit below: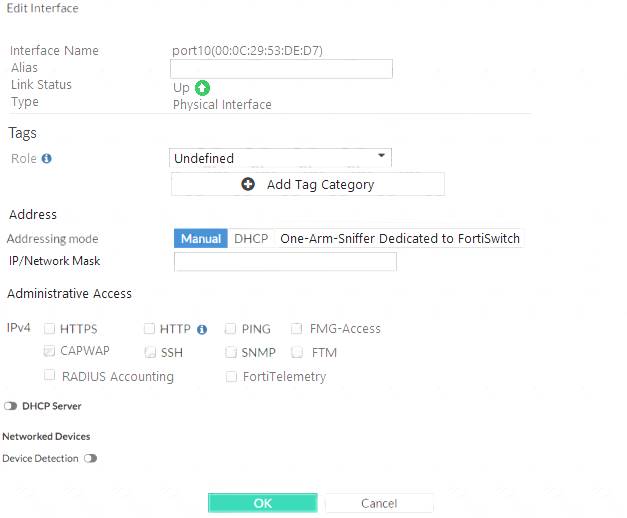
When configuring the root FortiGate to communicate with a downstream FortiGate, which settings are required to be configured? (Choose two.)
- A. Device detection enabled.
- B. Administrative Access: FortiTelemetry.
- C. IP/Network Mask.
- D. Role: Security Fabric.
Answer: BC
NEW QUESTION 16
Examine the IPS sensor and DoS policy configuration shown in the exhibit, then answer the question below.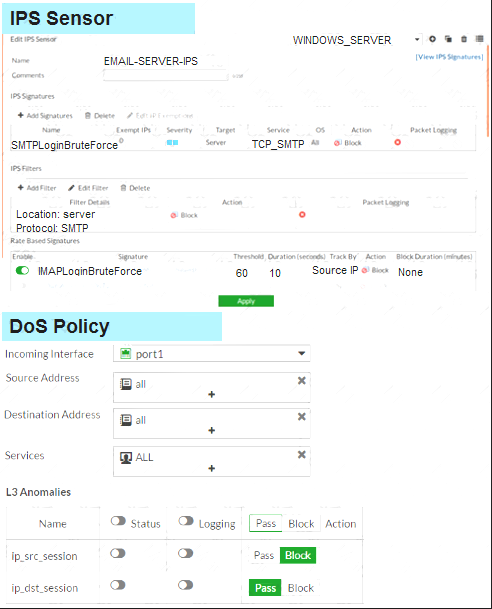
When detecting attacks, which anomaly, signature, or filter will FortiGate evaluate first?
- A. SMTP.Login.Brute.Force
- B. IMAP.Login.brute.Force
- C. ip_src_session
- D. Location: server Protocol: SMTP
Answer: B
NEW QUESTION 17
Which statements correctly describe transparent mode operation? (Choose three.)
- A. All interfaces of the transparent mode FortiGate device must be on different IP subnets.
- B. Ethernet packets are forwarded based on destination MAC addresses, not IP addresses.
- C. The transparent FortiGate is visible to network hosts in an IP traceroute.
- D. It permits inline traffic inspection and firewalling without changing the IP scheme of the network.
- E. FortiGate acts as transparent bridge and forwards traffic at Layer 2.
Answer: BDE
NEW QUESTION 18
Which of the following FortiGate configuration tasks will create a route in the policy route table? (Choose two.)
- A. Static route created with a Named Address object
- B. Static route created with an Internet Services object
- C. SD-WAN route created for individual member interfaces
- D. SD-WAN rule created to route traffic based on link latency
Answer: BD
NEW QUESTION 19
Examine the exhibit, which shows the partial output of an IKE real-time debug.
Which of the following statement about the output is true?
- A. The VPN is configured to use pre-shared key authentication.
- B. Extended authentication (XAuth) was successful.
- C. Remote is the host name of the remote IPsec peer.
- D. Phase 1 went down.
Answer: A
NEW QUESTION 20
Examine this PAC file configuration.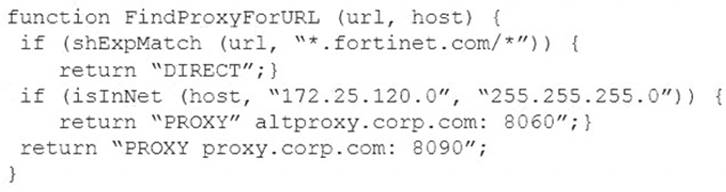
Which of the following statements are true? (Choose two.)
- A. Browsers can be configured to retrieve this PAC file from the FortiGate.
- B. Any web request to the 172.25.120.0/24 subnet is allowed to bypass the proxy.
- C. All requests not made to Fortinet.com or the 172.25.120.0/24 subnet, have to go through altproxy.corp.com: 8060.
- D. Any web request fortinet.com is allowed to bypass the proxy.
Answer: AD
NEW QUESTION 21
Refer to the following exhibit.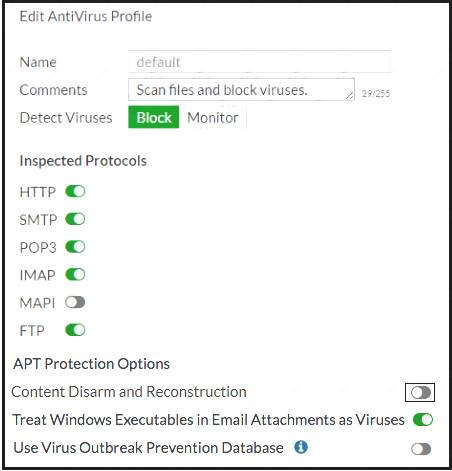
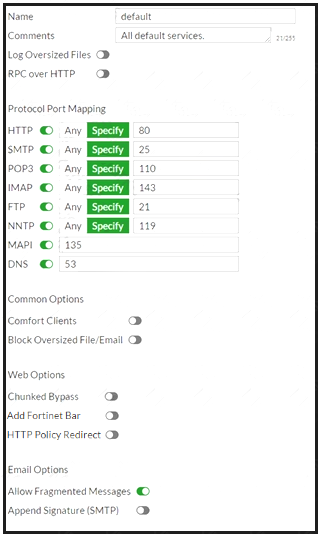
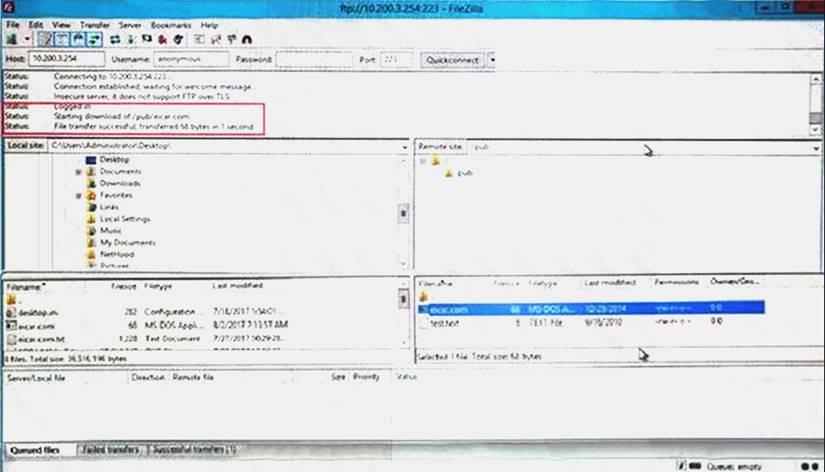
Why is FortiGate not blocking the test file over FTP download?
- A. Deep-inspection must be enabled for FortiGate to fully scan FTP traffic.
- B. FortiGate needs to be operating in flow-based inspection mode in order to scan FTP traffic.
- C. The FortiSandbox signature database is required to successfully scan FTP traffic.
- D. The proxy options profile needs to scan FTP traffic on a non-standard port.
Answer: D
NEW QUESTION 22
You have tasked to design a new IPsec deployment with the following criteria: Which topology should be used to satisfy all of the requirements?
- A. Partial mesh
- B. Hub-and-spoke
- C. Fully meshed
- D. Redundant
Answer: B
NEW QUESTION 23
Which of the following statements describe WMI polling mode for the FSSO collector agent? (Choose two.)
- A. The NetSessionEnum function is used to track user logoffs.
- B. WMI polling can increase bandwidth usage in large networks.
- C. The collector agent uses a Windows API to query DCs for user logins.
- D. The collector agent do not need to search any security event logs.
Answer: CD
NEW QUESTION 24
Which of the following statements about policy-based IPsec tunnels are true? (Choose two.)
- A. They can be configured in both NAT/Route and transparent operation modes.
- B. They support L2TP-over-IPsec.
- C. They require two firewall policies: one for each directions of traffic flow.
- D. They support GRE-over-IPsec.
Answer: AB
NEW QUESTION 25
Which of the following features is supported by web filter in flow-based inspection mode with NGFW mode set to profile-based?
- A. FortiGuard Quotas
- B. Static URL
- C. Search engines
- D. Rating option
Answer: B
NEW QUESTION 26
......
P.S. Easily pass NSE4_FGT-6.2 Exam with 129 Q&As prep-labs.com Dumps & pdf Version, Welcome to Download the Newest prep-labs.com NSE4_FGT-6.2 Dumps: https://www.prep-labs.com/dumps/NSE4_FGT-6.2/ (129 New Questions)
