Proper study guides for Renewal Fortinet Fortinet NSE 4 - FortiOS 7.0 certified begins with Fortinet NSE4_FGT-7.0 preparation products which designed to deliver the Highest Quality NSE4_FGT-7.0 questions by making you pass the NSE4_FGT-7.0 test at your first time. Try the free NSE4_FGT-7.0 demo right now.
Online Fortinet NSE4_FGT-7.0 free dumps demo Below:
NEW QUESTION 1
Refer to the exhibit.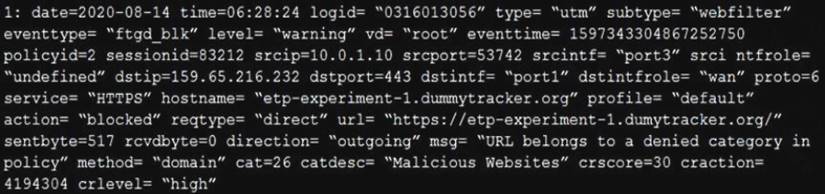
Based on the raw log, which two statements are correct? (Choose two.)
- A. Traffic is blocked because Action is set to DENY in the firewall policy.
- B. Traffic belongs to the root VDOM.
- C. This is a security log.
- D. Log severity is set to error on FortiGate.
Answer: AC
NEW QUESTION 2
An administrator has configured two-factor authentication to strengthen SSL VPN access. Which additional best practice can an administrator implement?
- A. Configure Source IP Pools.
- B. Configure split tunneling in tunnel mode.
- C. Configure different SSL VPN realms.
- D. Configure host check.
Answer: D
NEW QUESTION 3
An administrator wants to configure Dead Peer Detection (DPD) on IPSEC VPN for detecting dead tunnels. The requirement is that FortiGate sends DPD probes only when no traffic is observed in the tunnel.
Which DPD mode on FortiGate will meet the above requirement?
- A. Disabled
- B. On Demand
- C. Enabled
- D. On Idle
Answer: D
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD40813
NEW QUESTION 4
An administrator needs to increase network bandwidth and provide redundancy.
What interface type must the administrator select to bind multiple FortiGate interfaces?
- A. VLAN interface
- B. Software Switch interface
- C. Aggregate interface
- D. Redundant interface
Answer: C
Explanation:
Reference: https://forum.fortinet.com/tm.aspx?m=120324
NEW QUESTION 5
Which two statements are true about the FGCP protocol? (Choose two.)
- A. Not used when FortiGate is in Transparent mode
- B. Elects the primary FortiGate device
- C. Runs only over the heartbeat links
- D. Is used to discover FortiGate devices in different HA groups
Answer: BC
Explanation:
Reference:
https://docs.fortinet.com/document/fortigate/6.4.0/ports-and-protocols/564712/fgcp-fortigate-clustering-protocol
NEW QUESTION 6
A network administrator wants to set up redundant IPsec VPN tunnels on FortiGate by using two IPsec VPN tunnels and static routes.
* All traffic must be routed through the primary tunnel when both tunnels are up
* The secondary tunnel must be used only if the primary tunnel goes down
* In addition, FortiGate should be able to detect a dead tunnel to speed up tunnel failover
Which two key configuration changes are needed on FortiGate to meet the design requirements? (Choose two,)
- A. Configure a high distance on the static route for the primary tunnel, and a lower distance on the static route for the secondary tunnel.
- B. Enable Dead Peer Detection.
- C. Configure a lower distance on the static route for the primary tunnel, and a higher distance on the static route for the secondary tunnel.
- D. Enable Auto-negotiate and Autokey Keep Alive on the phase 2 configuration of both tunnels.
Answer: BC
Explanation:
B - because the customer requires the tunnels to notify when a tunnel goes down. DPD is designed for that purpose. To send a packet over a firewall to determine a failover for the next tunnel after a specific amount of time of not receiving a response from its peer.
C - remember when it comes to choosing a route with regards to Administrative Distance. The route with the lowest distance for that particular route will be chosen. So, by configuring a lower routing distance on the primary tunnel, means that the primary tunnel will be chosen to route packets towards their destination.
NEW QUESTION 7
Which three security features require the intrusion prevention system (IPS) engine to function? (Choose three.)
- A. Web filter in flow-based inspection
- B. Antivirus in flow-based inspection
- C. DNS filter
- D. Web application firewall
- E. Application control
Answer: ABE
NEW QUESTION 8
An administrator observes that the port1 interface cannot be configured with an IP address. What can be the reasons for that? (Choose three.)
- A. The interface has been configured for one-arm sniffer.
- B. The interface is a member of a virtual wire pair.
- C. The operation mode is transparent.
- D. The interface is a member of a zone.
- E. Captive portal is enabled in the interface.
Answer: ABC
Explanation:
https://help.fortinet.com/fos50hlp/54/Content/FortiOS/fortigate-whats-new-54/Top_VirtualWirePair.htm
NEW QUESTION 9
Which two statements are true about the RPF check? (Choose two.)
- A. The RPF check is run on the first sent packet of any new session.
- B. The RPF check is run on the first reply packet of any new session.
- C. The RPF check is run on the first sent and reply packet of any new session.
- D. RPF is a mechanism that protects FortiGate and your network from IP spoofing attacks.
Answer: AD
Explanation:
Reference: https://www.programmersought.com/article/16383871634/
NEW QUESTION 10
An administrator is configuring an IPsec VPN between site A and site B. The Remote Gateway setting in both sites has been configured as Static IP Address. For site A, the local quick mode selector is 192.168.1.0/24 and the remote quick mode selector is 192.168.2.0/24.
Which subnet must the administrator configure for the local quick mode selector for site B?
- A. 192.168.1.0/24
- B. 192.168.0.0/24
- C. 192.168.2.0/24
- D. 192.168.3.0/24
Answer: C
NEW QUESTION 11
Which three statements about security associations (SA) in IPsec are correct? (Choose three.)
- A. Phase 2 SAs are used for encrypting and decrypting the data exchanged through the tunnel.
- B. An SA never expires.
- C. A phase 1 SA is bidirectional, while a phase 2 SA is directional.
- D. Phase 2 SA expiration can be time-based, volume-based, or both.
- E. Both the phase 1 SA and phase 2 SA are bidirectional.
Answer: ACD
NEW QUESTION 12
Exhibit: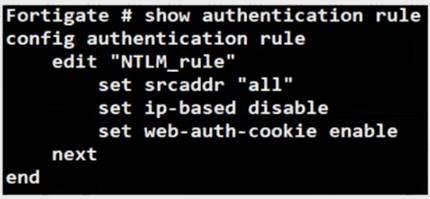
Refer to the exhibit to view the authentication rule configuration In this scenario, which statement is true?
- A. IP-based authentication is enabled
- B. Route-based authentication is enabled
- C. Session-based authentication is enabled.
- D. Policy-based authentication is enabled
Answer: C
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD45387
NEW QUESTION 13
Which two configuration settings are synchronized when FortiGate devices are in an active-active HA cluster? (Choose two.)
- A. FortiGuard web filter cache
- B. FortiGate hostname
- C. NTP
- D. DNS
Answer: CD
NEW QUESTION 14
Refer to the FortiGuard connection debug output.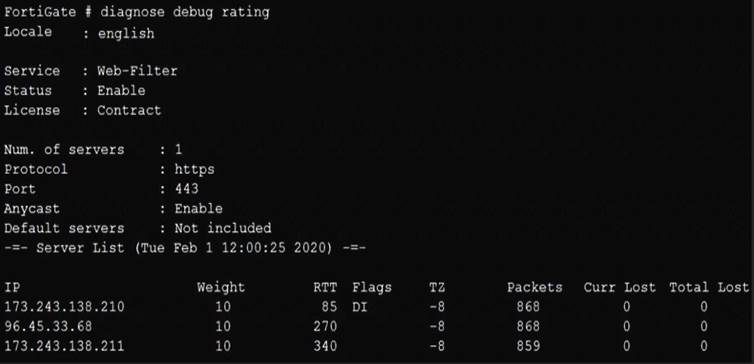
Based on the output shown in the exhibit, which two statements are correct? (Choose two.)
- A. A local FortiManager is one of the servers FortiGate communicates with.
- B. One server was contacted to retrieve the contract information.
- C. There is at least one server that lost packets consecutively.
- D. FortiGate is using default FortiGuard communication settings.
Answer: BD
NEW QUESTION 15
Which three authentication timeout types are availability for selection on FortiGate? (Choose three.)
- A. hard-timeout
- B. auth-on-demand
- C. soft-timeout
- D. new-session
- E. Idle-timeout
Answer: ADE
Explanation:
https://kb.fortinet.com/kb/documentLink.do?externalID=FD37221
NEW QUESTION 16
Refer to the exhibit.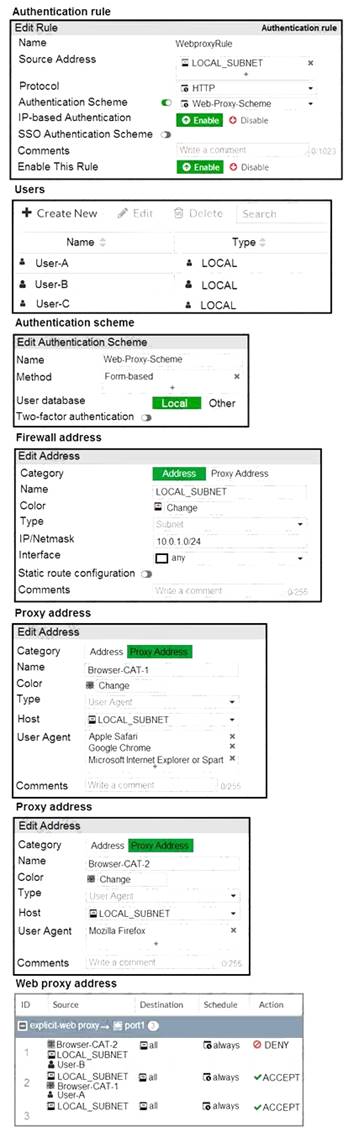
The exhibit shows proxy policies and proxy addresses, the authentication rule and authentication scheme, users, and firewall address.
An explicit web proxy is configured for subnet range 10.0.1.0/24 with three explicit web proxy policies. The authentication rule is configured to authenticate HTTP requests for subnet range 10.0.1.0/24 with a
form-based authentication scheme for the FortiGate local user database. Users will be prompted for
authentication.
How will FortiGate process the traffic when the HTTP request comes from a machine with the source IP 10.1.1.10 to the destination http://www.fortinet.com? (Choose two.)
- A. If a Mozilla Firefox browser is used with User-B credentials, the HTTP request will be allowed.
- B. If a Google Chrome browser is used with User-B credentials, the HTTP request will be allowed.
- C. If a Mozilla Firefox browser is used with User-A credentials, the HTTP request will be allowed.
- D. If a Microsoft Internet Explorer browser is used with User-B credentials, the HTTP request will be allowed.
Answer: BD
NEW QUESTION 17
Refer to the exhibit.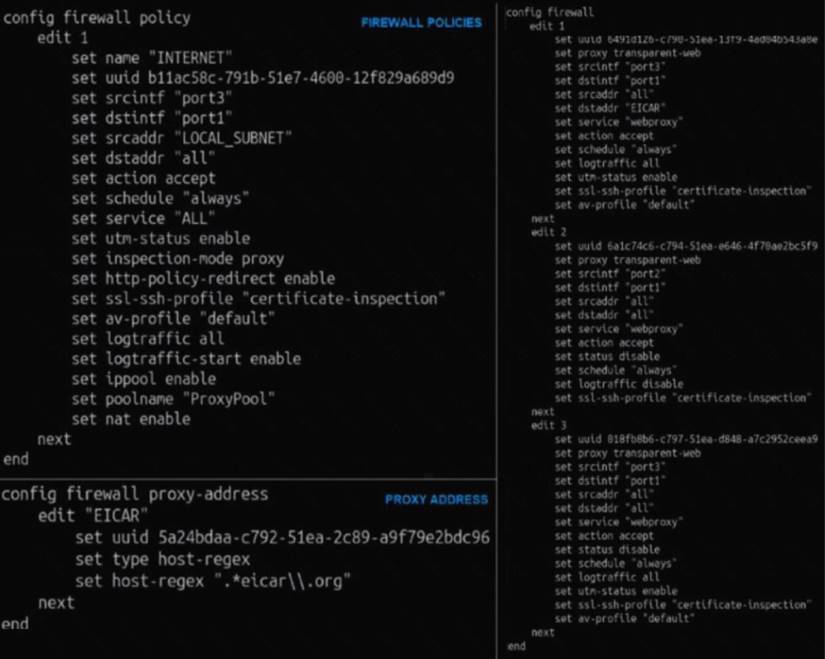
The exhibit shows a CLI output of firewall policies, proxy policies, and proxy addresses.
How does FortiGate process the traffic sent to http://www.fortinet.com?
- A. Traffic will be redirected to the transparent proxy and it will be allowed by proxy policy ID 3.
- B. Traffic will not be redirected to the transparent proxy and it will be allowed by firewall policy ID 1.
- C. Traffic will be redirected to the transparent proxy and It will be allowed by proxy policy ID 1.
- D. Traffic will be redirected to the transparent proxy and it will be denied by the proxy implicit deny policy.
Answer: D
NEW QUESTION 18
Which three CLI commands can you use to troubleshoot Layer 3 issues if the issue is in neither the physical layer nor the link layer? (Choose three.)
- A. diagnose sys top
- B. execute ping
- C. execute traceroute
- D. diagnose sniffer packet any
- E. get system arp
Answer: BCD
NEW QUESTION 19
Which statement is correct regarding the inspection of some of the services available by web applications embedded in third-party websites?
- A. The security actions applied on the web applications will also be explicitly applied on the third-party websites.
- B. The application signature database inspects traffic only from the original web application server.
- C. FortiGuard maintains only one signature of each web application that is unique.
- D. FortiGate can inspect sub-application traffic regardless where it was originated.
Answer: D
Explanation:
Reference:
https://help.fortinet.com/fortiproxy/11/Content/Admin%20Guides/FPX-AdminGuide/300_System/303d_FortiG
NEW QUESTION 20
An administrator wants to configure timeouts for users. Regardless of the user€™s behavior, the timer should start as soon as the user authenticates and expire after the configured value.
Which timeout option should be configured on FortiGate?
- A. auth-on-demand
- B. soft-timeout
- C. idle-timeout
- D. new-session
- E. hard-timeout
Answer: E
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD37221#:~:text=Hard%20timeout%3A%20User%20
NEW QUESTION 21
......
P.S. Dumps-files.com now are offering 100% pass ensure NSE4_FGT-7.0 dumps! All NSE4_FGT-7.0 exam questions have been updated with correct answers: https://www.dumps-files.com/files/NSE4_FGT-7.0/ (172 New Questions)
