Our pass rate is high to 98.9% and the similarity percentage between our NSE7_EFW-7.2 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Fortinet NSE7_EFW-7.2 exam in just one try? I am currently studying for the Fortinet NSE7_EFW-7.2 exam. Latest Fortinet NSE7_EFW-7.2 Test exam practice questions and answers, Try Fortinet NSE7_EFW-7.2 Brain Dumps First.
Online NSE7_EFW-7.2 free questions and answers of New Version:
NEW QUESTION 1
You contoured an address object on the tool fortiGate in a Security Fabric. This object is not synchronized with a downstream device. Which two reasons could be the cause? (Choose two)
- A. The address object on the tool FortiGate has fabric-object set to disable
- B. The root FortiGate has configuration-sync set to enable
- C. The downstream TortiGate has fabric-object-unification set to local
- D. The downstream FortiGate has configuration-sync set to local
Answer: AC
Explanation:
✑ Option A is correct because the address object on the tool FortiGate will not be synchronized with the downstream devices if it has fabric-object set to disable. This option controls whether the address object is shared with other FortiGate devices in the Security Fabric or not1.
✑ Option C is correct because the downstream FortiGate will not receive the address object from the tool FortiGate if it has fabric-object-unification set to local. This option controls whether the downstream FortiGate uses the address objects from the root FortiGate or its own local address objects2.
✑ Option B is incorrect because the root FortiGate has configuration-sync set to enable by default, which means that it will synchronize the address objects with the downstream devices unless they are disabled by the fabric-object option3.
✑ Option D is incorrect because the downstream FortiGate has configuration-sync set to local by default, which means that it will receive the address objects from the root FortiGate unless they are overridden by the fabric-object-unification
option4. References: =
✑ 1: Group address objects synchronized from FortiManager5
✑ 2: Security Fabric address object unification6
✑ 3: Configuration synchronization7
✑ 4: Configuration synchronization7
✑ : Security Fabric - Fortinet Documentation
NEW QUESTION 2
Exhibit.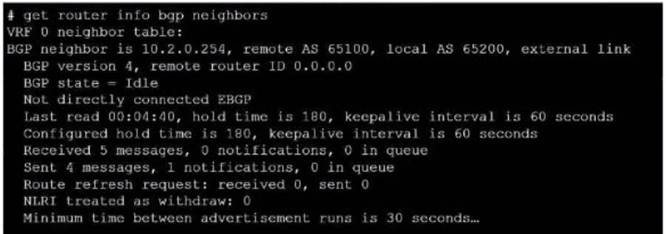
Refer to the exhibit, which provides information on BGP neighbors. Which can you conclude from this command output?
- A. The router are in the number to match the remote peer.
- B. You must change the AS number to match the remote peer.
- C. BGP is attempting to establish a TCP connection with the BGP peer.
- D. The bfd configuration to set to enable.
Answer: C
Explanation:
The BGP state is “Idle”, indicating that BGP is attempting to establish a TCP connection with the peer. This is the first state in the BGP finite state machine, and it means that no TCP connection has been established yet. If the TCP connection fails, the BGP state will reset to either active or idle, depending on the configuration. References: You can find more information about BGP states and troubleshooting in the following Fortinet Enterprise Firewall 7.2 documents:
✑ Troubleshooting BGP
✑ How BGP works
NEW QUESTION 3
Exhibit.
Refer to the exhibit, which shows an ADVPN network.
The client behind Spoke-1 generates traffic to the device located behind Spoke-2. Which first message floes the hub send to Spoke-110 bring up the dynamic tunnel?
- A. Shortcut query
- B. Shortcut reply
- C. Shortcut offer
- D. Shortcut forward
Answer: A
Explanation:
In an ADVPN scenario, when traffic is initiated from a client behind one spoke to another spoke, the hub sends a shortcut query to the initiating spoke. This query is used to determine if there is a more direct path for the traffic, which can then trigger the establishment of a dynamic tunnel between the spokes.
NEW QUESTION 4
Which two statements about the Security fabric are true? (Choose two.)
- A. FortiGate uses the FortiTelemetry protocol to communicate with FortiAnatyzer.
- B. Only the root FortiGate sends logs to FortiAnalyzer
- C. Only FortiGate devices with configuration-sync receive and synchronize global CMDB objects that the toot FortiGate sends
- D. Only the root FortiGate collects network topology information and forwards it to FortiAnalyzer
Answer: BC
Explanation:
In the Security Fabric, only the root FortiGate sends logs to FortiAnalyzer (B). Additionally, only FortiGate devices withconfiguration-syncenabled receive and synchronize global Central Management Database (CMDB) objects that the root FortiGate sends (C). FortiGate uses the FortiTelemetry protocol to communicate with other FortiGates, not FortiAnalyzer (A). The last option (D) is incorrect as all FortiGates can collect and forward network topology information to FortiAnalyzer.
References:
✑ FortiOS Handbook - Security Fabric
NEW QUESTION 5
Refer to the exhibit, which shows the output of a BGP summary.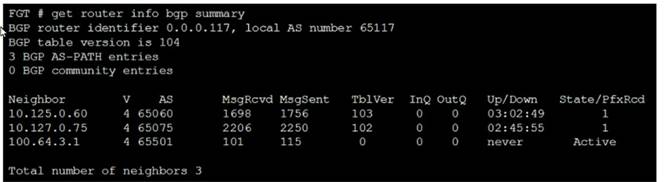
What two conclusions can you draw from this BGP summary? (Choose two.)
- A. External BGP (EBGP) exchanges routing information.
- B. The BGP session with peer 10. 127. 0. 75 is established.
- C. The router 100. 64. 3. 1 has the parameter bfd set to enable.
- D. The neighbors displayed are linked to a local router with the neighbor-range set to a value of 4.
Answer: AB
Explanation:
The output of the BGP (Border Gateway Protocol) summary shows details about the BGP neighbors of a router, their Autonomous System (AS) numbers, the state of the BGP session, and other metrics like messages received and sent.
From the BGP summary provided:
* A.External BGP (EBGP) exchanges routing information.This conclusion can be inferred because the AS numbers for the neighbors are different from the local AS number (65117), which suggests that these are external connections.
* B.The BGP session with peer 10.127.0.75 is established.This is indicated by the state/prefix received column showing a numeric value (1), which typically means that the session is established and a number of prefixes has been received.
* C.The router 100.64.3.1 has the parameter bfd set to enable.This cannot be concluded directly from the summary without additional context or commands specifically showing
BFD (Bidirectional Forwarding Detection) configuration.
* D.The neighbors displayed are linked to a local router with the neighbor-range set to a value of 4.The neighbor-range concept does not apply here; the value 4 in the 'V' column stands for the BGP version number, which is typically 4.
NEW QUESTION 6
Refer to the exhibit, which shows an ADVPN network.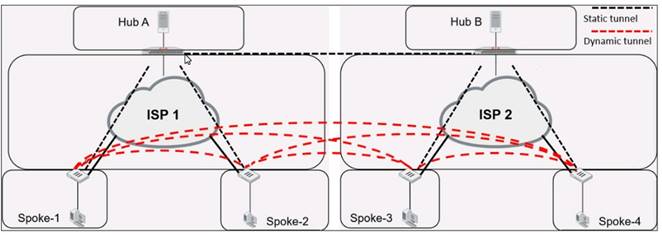
Which VPN phase 1 parameters must you configure on the hub for the ADVPN feature to function? (Choose two.)
- A. set auto-discovery-forwarder enable
- B. set add-route enable
- C. set auto-discovery-receiver enable
- D. set auto-discovery-sender enable
Answer: AC
Explanation:
For the ADVPN feature to function properly on the hub, the following phase 1 parameters must be configured:
* A. set auto-discovery-forwarder enable: This enables the hub to forward shortcut information to the spokes, which is essential for them to establish direct tunnels.
* C. set auto-discovery-receiver enable: This allows the hub to receive shortcut offers from the spokes.
This information is corroborated by the Fortinet documentation, which explains that in an ADVPN setup, the hub must be able to both forward and receive shortcut information for dynamic tunnel creation between spokes.
NEW QUESTION 7
Exhibit.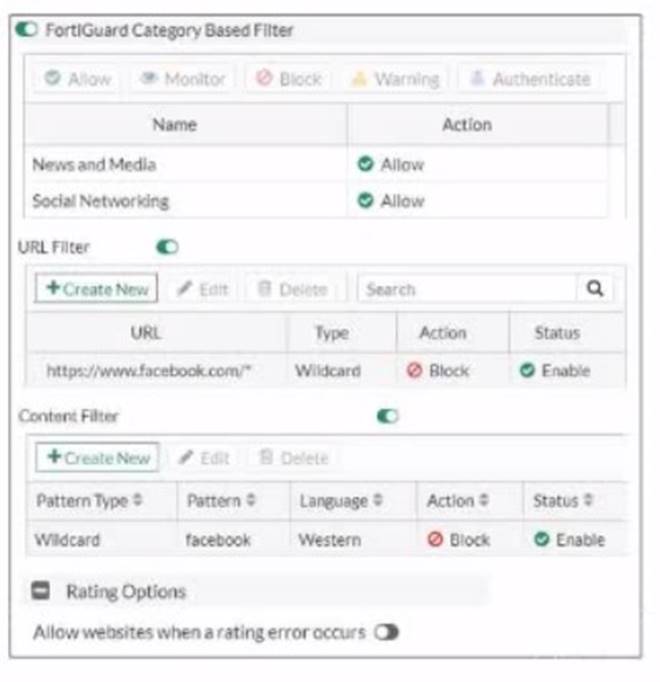
Refer to the exhibit, which shows a partial web filter profile conjuration
What can you cone udo from this configuration about access towww.facebook, com, which is categorized as Social Networking?
- A. The access is blocked based on the Content Filter configuration
- B. The access is allowed based on the FortiGuard Category Based Filter configuration
- C. The access is blocked based on the URL Filter configuration
- D. The access is hocked if the local or the public FortiGuard server does not reply
Answer: C
Explanation:
The access to www.facebook.com is blocked based on the URL Filter configuration. In the exhibit, it shows that the URL “www.facebook.com” is specifically set to “Block” under the URL Filter section1. References := Fortigate: How to configure Web Filter function on Fortigate, Web filter | FortiGate / FortiOS 7.0.2 | Fortinet Document
Library, FortiGate HTTPS web URL filtering … - Fortinet … - Fortinet Community
NEW QUESTION 8
Which two statements about metadata variables are true? (Choose two.)
- A. You create them on FortiGate
- B. They apply only to non-firewall objects.
- C. The metadata format is $<metadata_variabie_name>.
- D. They can be used as variables in scripts
Answer: AD
Explanation:
Metadata variables in FortiGate are created to store metadata associated
with different FortiGate features. These variables can be used in various configurations and scripts to dynamically replace the variable with its actual value during processing. A: You create metadata variables on FortiGate. They are used to store metadata for FortiGate features and can be called upon in different configurations. D: They can be used as variables in scripts. Metadata variables are utilized within the scripts to dynamically insert values as per the context when the script runs.
Fortinet FortiOS Handbook: CLI Reference
NEW QUESTION 9
Refer to the exhibit, which shows a network diagram.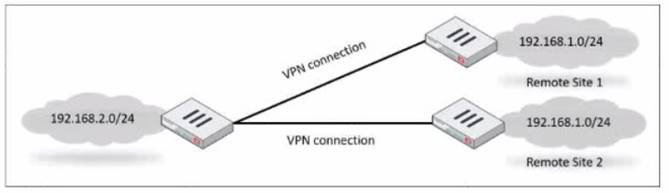
Which IPsec phase 2 configuration should you impalement so that only one remote site is connected at any time?
- A. Set route-overlap to allow.
- B. Set single-source to enable
- C. Set route-overlap to either use—new or use-old
- D. Set net-device to enable
Answer: C
Explanation:
To ensure that only one remote site is connected at any given time in an
IPsec VPN scenario, you should useroute-overlapwith the option to either use-new or use- old. This setting dictates which routes are preferred and how overlaps in routes are handled, allowing for one connection to take precedence over the other (C).
References:
✑ FortiOS Handbook - IPsec VPN
NEW QUESTION 10
Refer to the exhibit, which shows an error in system fortiguard configuration.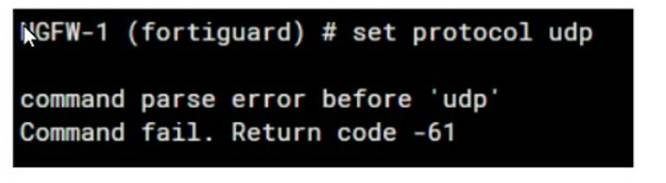
What is the reason you cannot set the protocol to udp in config system fortiguard?
- A. FortiManager provides FortiGuard.
- B. fortiguard-anycast is set to enable.
- C. You do not have the corresponding write access.
- D. udp is not a protocol option.
Answer: D
Explanation:
The reason for the command failure when trying to set the protocol to UDP in theconfig system fortiguardis likely that UDP is not a protocol option in this context. The command syntax might be incorrect or the option to set a protocol for FortiGuard updates might not exist in this manner. So the correct answer is D. udp is not a protocol option.
NEW QUESTION 11
Refer to the exhibit, which shows a routing table.
What two options can you configure in OSPF to block the advertisement of the 10.1.10.0 prefix? (Choose two.)
- A. Remove the 16.1.10.C prefix from the OSPF network
- B. Configure a distribute-list-out
- C. Configure a route-map out
- D. Disable Redistribute Connected
Answer: BC
Explanation:
To block the advertisement of the 10.1.10.0 prefix in OSPF, you can configure a distribute-list-out or a route-map out. A distribute-list-out is used to filter outgoing routing updates from being advertised to OSPF neighbors1. A route-map out can also be used for filtering and is applied to outbound routing
updates2. References := Technical Tip: Inbound route filtering in OSPF usi … - Fortinet Community, OSPF | FortiGate / FortiOS 7.2.2 - Fortinet Documentation
NEW QUESTION 12
Which two statements about IKE version 2 fragmentation are true? (Choose two.)
- A. Only some IKE version 2 packets are considered fragmentable.
- B. The reassembly timeout default value is 30 seconds.
- C. It is performed at the IP layer.
- D. The maximum number of IKE version 2 fragments is 128.
Answer: AD
Explanation:
In IKE version 2, not all packets are fragmentable. Only certain messages within the IKE negotiation process can be fragmented. Additionally, there is a limit to the number of fragments that IKE version 2 can handle, which is 128. This is specified in the Fortinet documentation and ensures that the IKE negotiation process can proceed even in networks that have issues with large packets. The reassembly timeout and the layer at which fragmentation occurs are not specified in this context within Fortinet documentation.
NEW QUESTION 13
You want to block access to the website ww.eicar.org using a custom IPS signature. Which custom IPS signature should you configure?
A)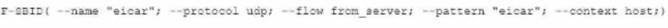
B)
C)
D)
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
Explanation:
Option D is the correct answer because it specifically blocks access to the website “www.eicar.org” using TCP protocol and HTTP service, which are commonly used for web browsing. The other options either use the wrong protocol (UDP), the wrong service (DNS or SSL), or the wrong pattern (“eicar” instead of
“www.eicar.org”). References := Configuring custom signatures | FortiGate / FortiOS 7.4.0 - Fortinet Document Library, section “Signature to block access to example.com”.
NEW QUESTION 14
Which, three conditions are required for two FortiGate devices to form an OSPF adjacency? (Choose three.)
- A. OSPF interface network types match
- B. OSPF router IDs are unique
- C. OSPF interface priority settings are unique
- D. OSPF link costs match
- E. Authentication settings match
Answer: ABE
Explanation:
✑ Option A is correct because the OSPF interface network types determine how the routers form adjacencies and exchange LSAs on a network segment. The network types must match for the routers to become neighbors1.
✑ Option B is correct because the OSPF router IDs are used to identify each router in the OSPF domain and to establish adjacencies. The router IDs must be unique for the routers to become neighbors2.
✑ Option E is correct because the authentication settings control how the routers authenticate each other before exchanging OSPF packets. The authentication settings must match for the routers to become neighbors3.
✑ Option C is incorrect because the OSPF interface priority settings are used to elect
the designated router (DR) and the backup designated router (BDR) on a broadcast or non-broadcast multi-access network. The priority settings do not have to be unique for the routers to become neighbors, but they affect the DR/BDR election process4.
✑ Option D is incorrect because the OSPF link costs are used to calculate the
shortest path to a destination network based on the bandwidth of the links. The link costs do not have to match for the routers to become neighbors, but they affect the routing decisions5. References: =
✑ 1: OSPF network types
✑ 2: OSPF router ID
✑ 3: OSPF authentication
✑ 4: OSPF interface priority
✑ 5: OSPF link cost
NEW QUESTION 15
Which FortiGate in a Security I auric sends togs to FortiAnalyzer?
- A. Only the root FortiGate.
- B. Each FortiGate in the Security fabric.
- C. The FortiGate devices performing network address translation (NAT) or unified threat management (UTM). if configured.
- D. Only the last FortiGate that handled a session in the Security Fabric
Answer: B
Explanation:
✑ Option B is correct because each FortiGate in the Security Fabric can send logs to FortiAnalyzer for centralized logging and analysis12. This allows you to monitor and manage the entire Security Fabric from a single console and view aggregated reports and dashboards.
✑ Option A is incorrect because the root FortiGate is not the only device that can send logs to FortiAnalyzer. The root FortiGate is the device that initiates the Security Fabric and acts as the central point of contact for other FortiGate devices3. However, it does not have to be the only log source for FortiAnalyzer.
✑ Option C is incorrect because the FortiGate devices performing NAT or UTM are not the only devices that can send logs to FortiAnalyzer. These devices can perform additional security functions on the traffic that passes through them, such as firewall, antivirus, web filtering, etc4. However, they are not the only devices that generate logs in the Security Fabric.
✑ Option D is incorrect because the last FortiGate that handled a session in the Security Fabric is not the only device that can send logs to FortiAnalyzer. The last FortiGate is the device that terminates the session and applies the final security policy5. However, it does not have to be the only device that reports the session information to FortiAnalyzer. References: =
✑ 1: Security Fabric - Fortinet Documentation1
✑ 2: FortiAnalyzer Demo6
✑ 3: Security Fabric topology
✑ 4: Security Fabric UTM features
✑ 5: Security Fabric session handling
NEW QUESTION 16
......
P.S. Certshared now are offering 100% pass ensure NSE7_EFW-7.2 dumps! All NSE7_EFW-7.2 exam questions have been updated with correct answers: https://www.certshared.com/exam/NSE7_EFW-7.2/ (50 New Questions)
