we provide Simulation Fortinet NSE8 exams which are the best for clearing NSE8 test, and to get certified by Fortinet NSE8. The NSE8 Questions & Answers covers all the knowledge points of the real NSE8 exam. Crack your Fortinet NSE8 Exam with latest dumps, guaranteed!
NEW QUESTION 1
Your FortiGate has multiple CPUs. You want to verify the load for each CPU. Which two commands will accomplish this task? (Choose two.)
- A. get system performance status
- B. diag system mpstat
- C. diag system cpu stat
- D. diag system top
Answer: AD
Explanation:
References: http://kb.fortinet.com/kb/documentLink.do?externalID=13825
NEW QUESTION 2
Given the following FortiOS 5.2 commands: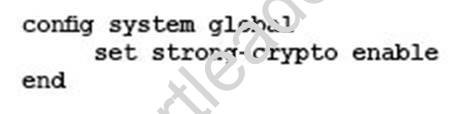
Which vulnerability is being addresses when managing FortiGate through an encrypted management protocol?
- A. Remote Exploit Vulnerability in Bash (ShellShock)
- B. Information Disclosure Vulnerability in OpenSSL (Heartbleed)
- C. SSL v3 POODLE Vulnerability
- D. SSL/TLS MITM vulnerability (CVE-2014-0224)
Answer: C
Explanation:
References: http://kb.fortinet.com/kb/documentLink.do?externalID=FD36913
NEW QUESTION 3
Which three configuration scenarios will result in an IPsec negotiation failure between two FortiGate devices? (Choose three.)
- A. mismatched phase 2 selectors
- B. mismatched Anti-Replay configuration
- C. mismatched Perfect Forward Secrecy
- D. failed Dead Peer Detection negotiation
- E. mismatched IKE version
Answer: ACE
Explanation:
In IPsec negotiations, Perfect Forward Secrecy (PFS) ensures that each new cryptographic key is unrelated to any previous key. Either enable or disable PFS on both the tunnel peers; otherwise, the LAN-to-LAN (L2L) IPsec tunnel is not established
NEW QUESTION 4
The output shown in the exhibit from FortiManager is displayed during an import of the device configuration.
Which statement describes the correct action taken for these duplicate objects?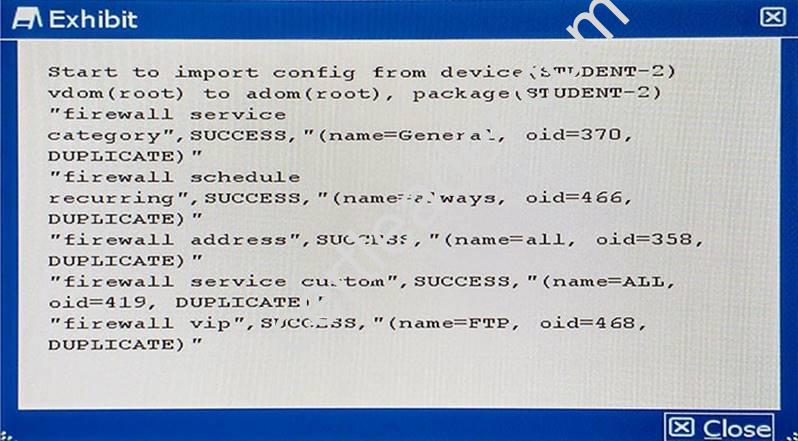
- A. The import fails because of the duplicate entries detected which exist in the ADOM database.
- B. FortiManager installs these duplicate objects to the managed device from the ADOM database.
- C. FortiManager does not import these duplicate entries into the ADOM database because they already exist in the ADOM database.
- D. FortiManager creates indexed duplicate entries for these objects in the ADOM database.
Answer: B
Explanation:
References:
http://docs.fortinet.com/uploaded/files/2905/FortiManager-5.4.0-Administration-Guide.pdf
NEW QUESTION 5
Which Fortinet product is used for antispam protection?
- A. FortiSwitch
- B. FortiGate
- C. FortiWeb
- D. FortiDB
Answer: B
NEW QUESTION 6
You are managing a FortiAnalyzer appliance. After an upgrade, you notice that the unit no longer displays historical logs, reports do not produce any data, and FortiView summary views are empty. However, you notice that the unit is receiving logs on the dashboard widgets.
Which step resolves this problem?
- A. Execute the CLI command exec sql-local rebuild-db.
- B. Execute the CLI command diag sql remove hcache.
- C. Execute the CLI command exec sql-local reinsert-logs.
- D. Restore the unit settings from a previous backup.
Answer: A
NEW QUESTION 7
You are asked to write a FortiAnalyzer report that lists the session that has consumed the most bandwidth. You are required to include the source IP, destination IP, application, application category, hostname, and total bandwidth consumed.
Which dataset meets these requirements?
- A. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘recbyte “, 0)) as bandwidth from $log where $filter LIMIT 1
- B. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘recbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
- C. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘rcvdbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
- D. select from_itime(itime) as timestamp, sourceip, destip, app, appcat, hostname, sum(coalesce(‘sentbyte’, 0)+coalesce(‘rcvdbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
Answer: C
Explanation:
References:
http://docs.fortinet.com/uploaded/files/2617/fortianalyzer-5.2.4-dataset-reference.pdf
NEW QUESTION 8
A customer is authenticating users using a FortiGate and an external LDAP server. The LDAP user, John Smith, cannot authenticate. The administrator runs the debug command diagnose debug application fnbamd 255 while John Smith attempts the authentication:
Based on the output shown in the exhibit, what is causing the problem?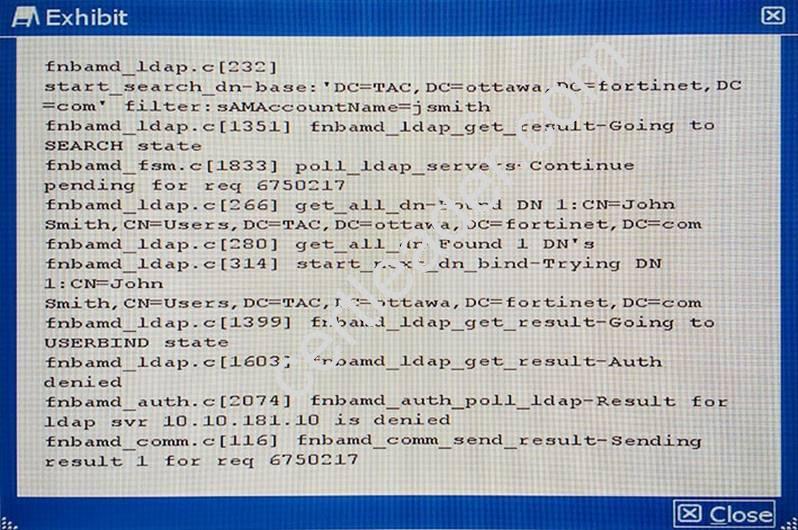
- A. The LDAP administrator password in the FortiGate configuration is incorrect.
- B. The user, John Smith, does have an account in the LDAP server.
- C. The user, John Smith, does not belong to any allowed user group.
- D. The user, John Smith, is using an incorrect password.
Answer: A
Explanation:
Fortigate not binded with LDAP server because of failed authentication. References:
NEW QUESTION 9
You want to enable traffic between 2001:db8:1::/64 and 2001:db8:2::/64 over the public IPv4 Internet.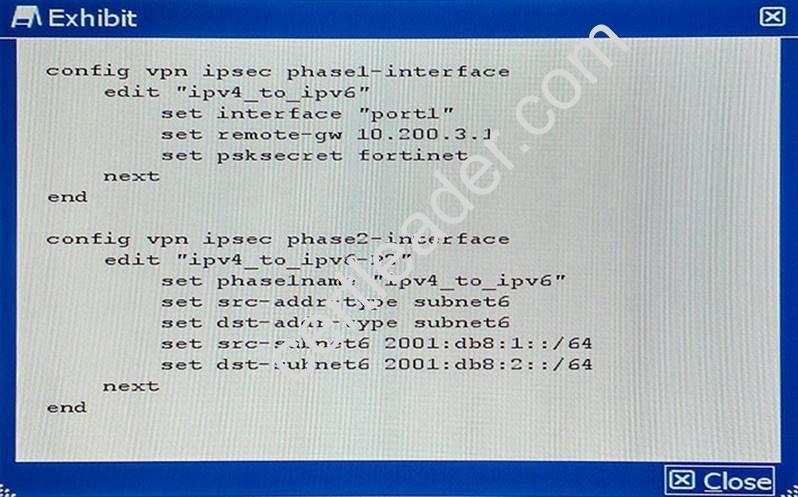
Given the CLI configuration shown in the exhibit, which two additional settings are required on this device to implement tunneling for the IPv6 transition? (Choose two.)
- A. IPv4 firewall policies to allow traffic between the local and remote IPv6 subnets.
- B. IPv6 static route to the destination phase2 destination subnet.
- C. IPv4 static route to the destination phase2 destination subnet.
- D. IPv6 firewall policies to allow traffic between the local and remote IPv6 subnets.
Answer: BD
Explanation:
References: http://docs.fortinet.com/uploaded/files/1969/IPv6%20Handbook%20for%20FortiOS%205.2. pdf
NEW QUESTION 10
Which three statements about throughput on a wireless network are true? (Choose three.)
- A. A wireless device labelled as 300 Mbps should be expected to provide a throughput of 300Mbps.
- B. Be careful to ensure the capabilities of the wireless clients match those of the access points, in order to achieve higher throughput.
- C. Reducing the duty cycles of the wireless media by generating fewer beacons may improve throughput.
- D. Because of the higher level of RF noise that is typical in the 2.4 GHz ISM band, throughput of 2.4 GHz devices will typically be less than 5 GHz devices.
- E. Because of the full-duplex nature of the medium and the minimal overhead generated by CSMA/CA, the actual aggregate throughput is typically close to the data rate.
Answer: BCD
Explanation:
References:
http://www.tp-link.in/faq-499.html
NEW QUESTION 11
Your company uses a cluster of two FortiGate 3600C units in active-passive mode to protect the corporate network. The FortiGate cluster sends its logs to a FortiAnalyzer and you have configured scheduled weekly reports for the Internet bandwidth usage of each corporate VLAN. During a scheduled maintenance window, you make a series of configuration changes. When the next FortiAnalyzer weekly report is generated, you notice that Internet bandwidth usage reported by the FortiAnalyzer is far less than expected.
What is the reason for this discrepancy?
- A. You applied an antivirus profile on some of the policies, and no traffic can be accelerated.
- B. You disabled all security profiles on some of the firewall policies, and the traffic matching those policies is now accelerated.
- C. You enabled HA session-pickup, which is turn disabled session accounting.
- D. You changed from active-passive to active-active, causing the session traffic counters to become inaccurate.
Answer: D
Explanation:
Because of Active/Active failover traffic segregate to boxes where it reduces the bandwidth utilization
NEW QUESTION 12
A customer wants to secure the network shown in the exhibit with a full redundancy design. Which security design would you use?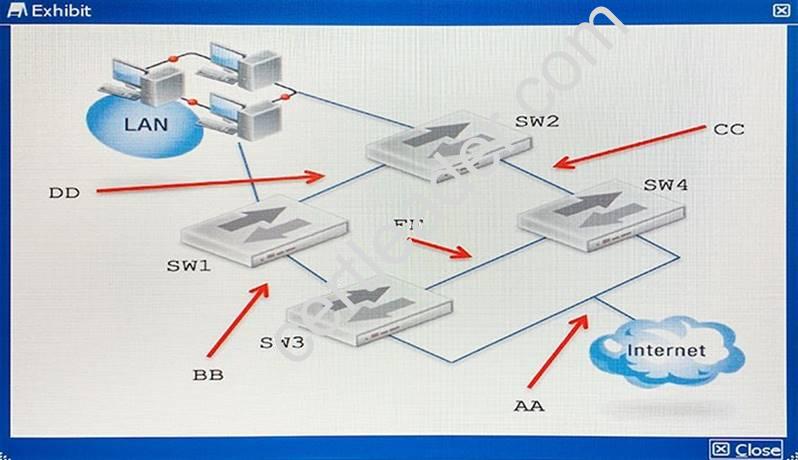
- A. Place a FortiGate FGCP Cluster between DD and AA, then connect it to SW1, SW2, SW3, and SW4.
- B. Place a FortiGate FGCP Cluster between BB and CC, then connect it to SW1, SW2, SW3, and SW4.
- C. Place a FortiGate FGCP Cluster between BB and AA, then connect it to SW1, SW2, SW3, and SW4.
- D. Place a FortiGate FGCP Cluster between DD and FF, then connect it to SW1, SW2, SW3, and SW4.
Answer: A
NEW QUESTION 13
You are asked to implement a wireless network for a conference center and need to provision a high number of access points to support a large number of wireless client
connections.
Which statement describes a valid solution for this requirement?
- A. Use a captive portal for guest acces
- B. Use both 2.4 GHz and 5 GHz band
- C. Enable frequency and access point hand-of
- D. Use more channels, thereby supporting more clients.
- E. Use an open wireless network with no porta
- F. Use both 2.4 GHz and 5 GHz band
- G. Use 802.11ac capable access points and configure channel bonding to support greater throughput for wireless clients.
- H. Use a pre-shared key only for wireless client securit
- I. Use the 5 GHz band only for greater securit
- J. Use 802.11ac capable access points and configure channel bonding to support greater throughput for wireless clients.
- K. Use a captive portal for guest acces
- L. Use both the 2.4 GHz and 5 GHz bands, and configure frequency steerin
- M. Configure rogue access point detection in order to automatically control the transmit power of each AP.
Answer: D
NEW QUESTION 14
You must establish a BGP peering with a service provider. The provider has supplied you with BGP peering parameters and you performed the basic configuration shown in the exhibit on your FortiGate unit. You notice that your peering session is not coming up.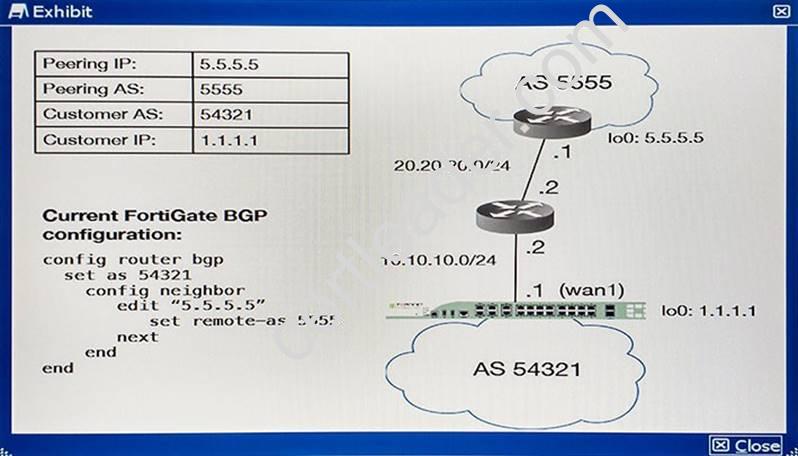
Which three missing configuration statements are needed to make this configuration functional? (Choose three.)
- A.
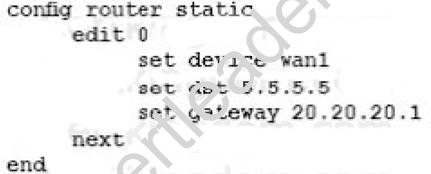
- B.
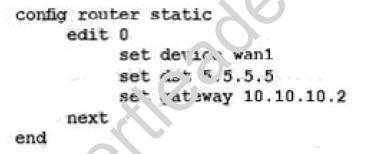
- C.
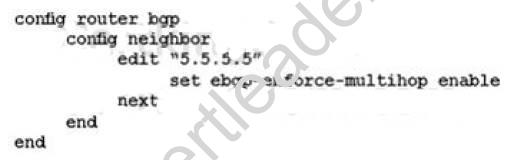
- D.
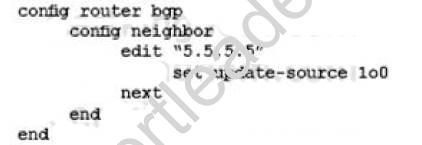
- E.
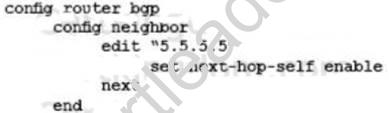
Answer: CDE
NEW QUESTION 15
You are installing a new FortiAP as shown in the exhibit, however, the FortiAP cannot discover the FortiGate. The FortiAP obtained an IP from the DHCP server and is reachable.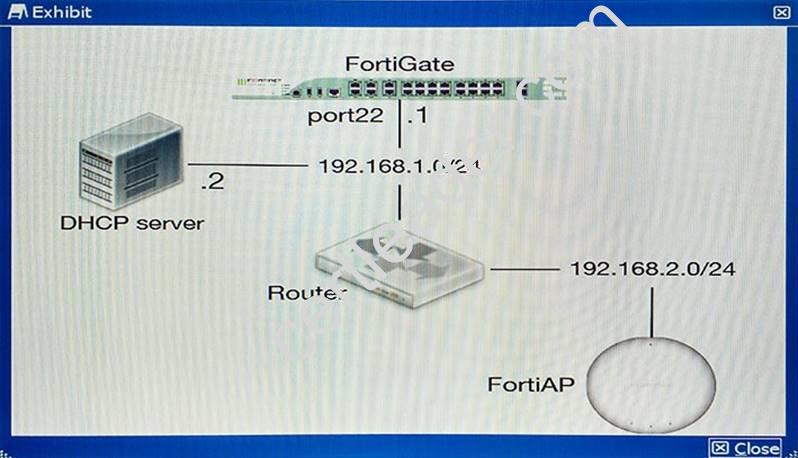
Which two configurations will resolve the problem? (Choose two.)
- A.
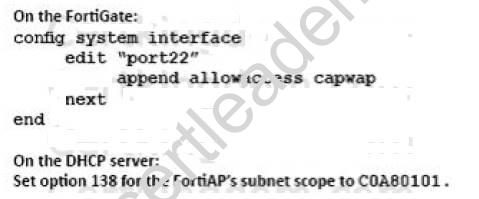
- B.
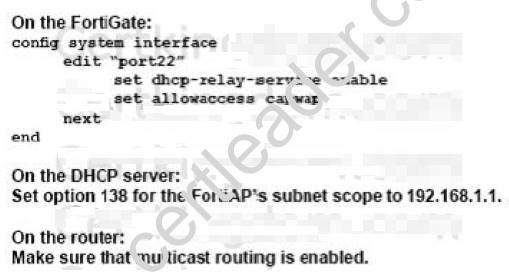
- C.
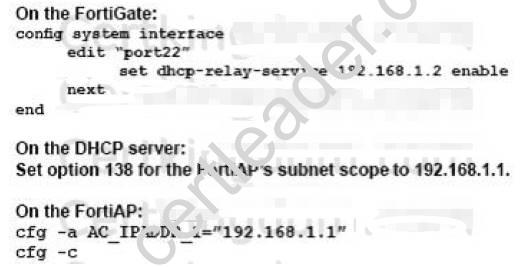
- D.
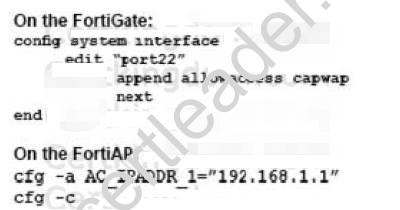
Answer: BD
Explanation:
https://forum.fortinet.com/tm.aspx?m=112739
NEW QUESTION 16
Referring to the exhibit, you want to know if aggregating port7 and port22 will work. Which statement is correct?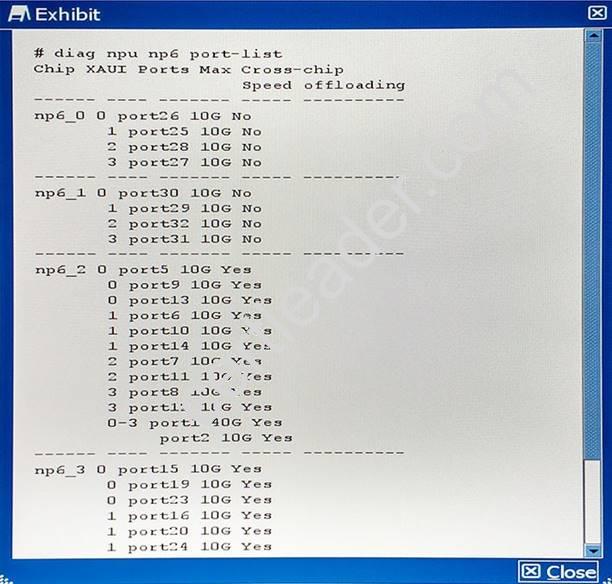
- A. Yes, LACP is supported on all ports regardless if they are connected to the same NP6.
- B. No, LACP is not supported on NP6 platforms.
- C. No, LACP is only supported on ports connected to the same NP6.
- D. Yes, LACP is supported on ports that are linked together with integrated Switch Fabric.
Answer: C
Explanation:
References:
http://help.fortinet.com/fos50hlp/54/Content/FortiOS/fortigate-hardware-acceleration- 52/NP6.htm
NEW QUESTION 17
The wireless controller diagnostic output is shown in the exhibit. Which three statements are true? (Choose three.)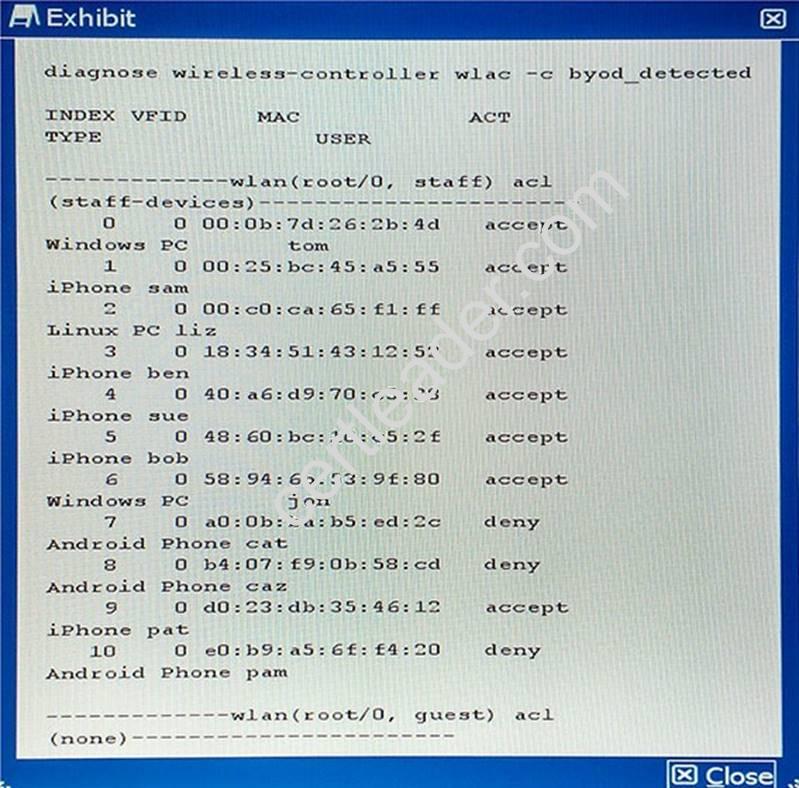
- A. Firewall policies using device types are blocking Android devices.
- B. An access control list applied to the VAP interface blocks Android devices.
- C. This is a CAPWAP control channel diagnostic command.
- D. There are no wireless clients connected to the guest wireless network.
- E. The “src-vis” process is active on the staff wireless network VAP interface.
Answer: ACD
Explanation:
References:
http://docs.fortinet.com/uploaded/files/1083/fortigate-managing-devices-50.pdf
NEW QUESTION 18
The exhibit shows an LDAP server configuration in a FortiGate device.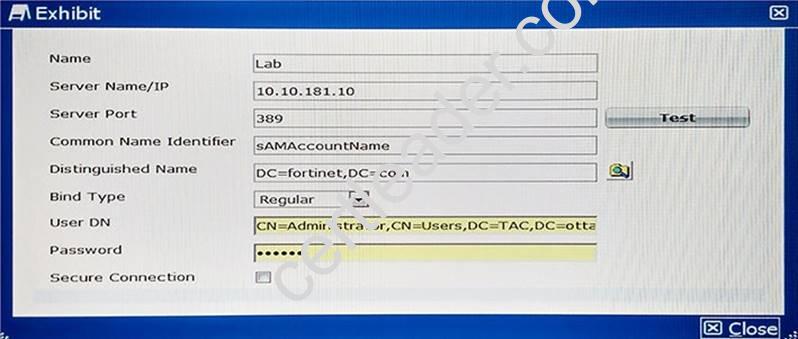
The LDAP user, John Smith, has the following LDAP attributes: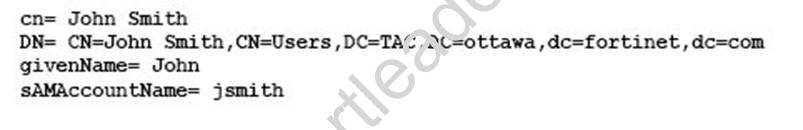
John Smith’s LDAP password is ABC123.
Which CLI command should you use to test the LDAP authentication using John Smith’s credentials?
- A. diagnose test authserver ldap Lab jsmith ABC123
- B. diagnose test authserver ldap-direct Lab jsmith ABC123
- C. diagnose test authserver ldap Lab ‘John Smith’ ABC123
- D. diagnose test authserver ldap-direct Lab john ABC123
Answer: A
Explanation:
References: https://forum.fortinet.com/tm.aspx?m=119178
NEW QUESTION 19
Which command detects where a routing path is broken?
- A. exec traceroute <destination>
- B. exec route ping <destination>
- C. diag route null
- D. diag debug route <destination>
Answer: A
NEW QUESTION 20
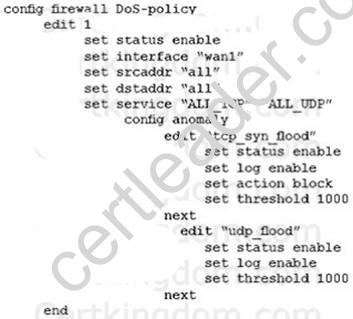
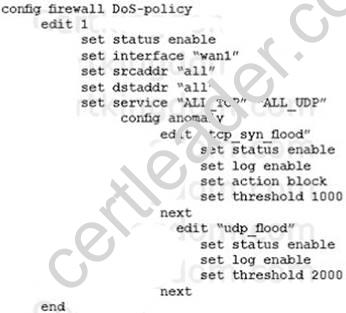
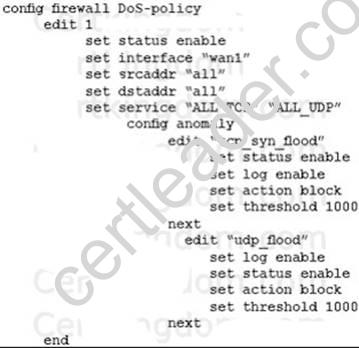
A company wants to protect against Denial of Service attacks and has launched a new project. They want to block the attacks that go above a certain threshold and for some others they are just trying to get a baseline of activity for those types of attacks so they are
letting the traffic pass through without action. Given the following:
- The interface to the Internet is on WAN1.
- There is no requirement to specify which addresses are being protected or protected from.
- The protection is to extend to all services.
- The tcp_syn_flood attacks are to be recorded and blocked.
- The udp_flood attacks are to be recorded but not blocked.
- The tcp_syn_flood attack’s threshold is to be changed from the default to 1000. The exhibit shows the current DoS-policy.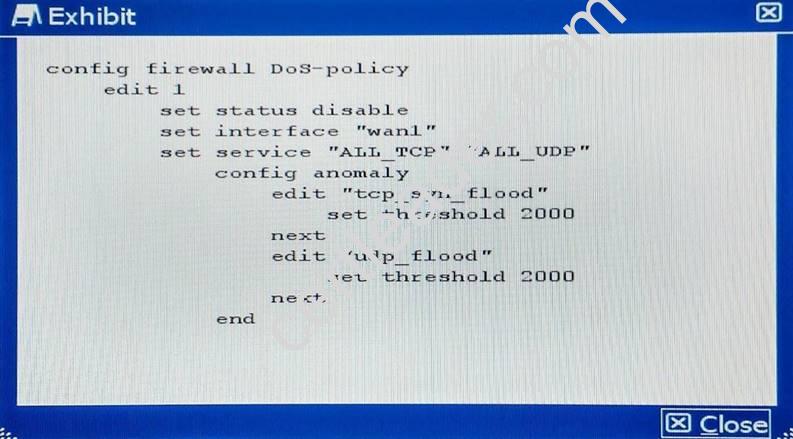
Which policy will implement the project requirements?
- A.
- B.
- C.
- D.
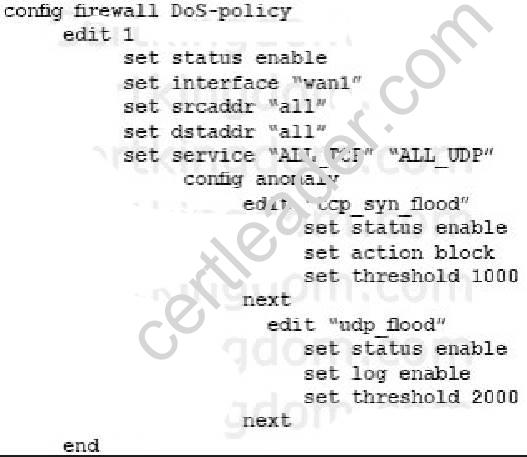
Answer: BD
Explanation:
B&D both have same policy which fulfills the above criteria. http://help.fortinet.com/fos50hlp/52data/Content/FortiOS/fortigate-firewall-52/Examples/Example-%20DoS%20Policy.htm
NEW QUESTION 21
You are asked to design a secure solution using Fortinet products for a company. The company recently has Web servers that were exploited and defaced. The customer has also experienced Denial or Service due to SYN Flood attacks. Taking this into consideration, the customer’s solution should have the following requirements:
- management requires network-based content filtering with man-in-the-middle inspection
- the customer has no existing public key infrastructure but requires centralized certificate management
- users are tracked by their active directory username without installing any software on their hosts
- Web servers that have been exploited need to be protected from the OWASP Top 10
- notification of high volume SYN Flood attacks when a threshold has been triggered Which three solutions satisfy these requirements? (Choose three.)
- A. FortiGate
- B. FortiClient
- C. FortiWeb
- D. FortiAuthenticator
- E. FortiDDOS
Answer: ACE
NEW QUESTION 22
You notice that memory usage is high and FortiGate has entered conserve mode. You want FortiGate’s IPS engine to focus only on exploits and attacks that are applicable to your specific network.
Which two steps would you take to reduce RAM usage without weakening security? (Choose two.)
- A. Configure IPS to pass files that are larger than a specific threshold, instead of buffering and scanning them.
- B. Reduce the size of the signature three (filters) that FortiGate must search by disabling scans for applications and OS stacks that do not exist on your network.
- C. Disable application control for protocols that are not used on your network.
- D. Disable IPS for traffic destined for the FortiGate itself.
Answer: BD
NEW QUESTION 23
Referring to the diagram shown in the exhibit, you deployed VRRP load balancing using two FortiGate units and two VRRP groups with a VRRP virtual MAC address enabled on both FortiGate’s port2 interface. During normal operation, both FortiGate units are processing traffic and the VRRP groups are used to load balance the traffic between the two FortiGate units.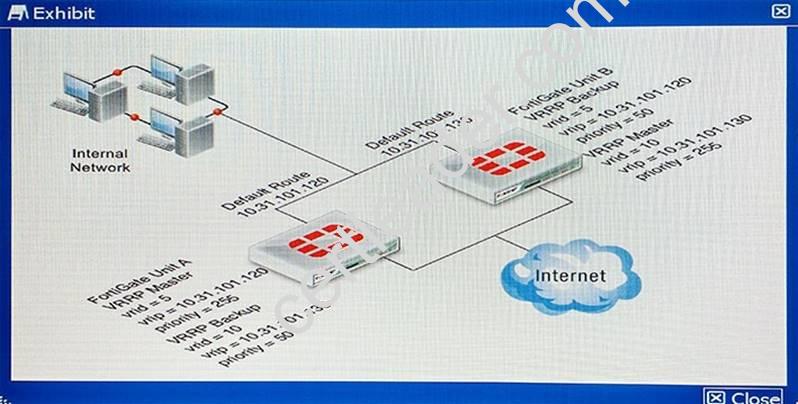
If FortiGate unit A fails, what would happen?
- A. The FortiGate Unit B port2 interface sends gratuitous ARPs to associate the VRRPvirtual router IP address with its own MAC address, and all traffic fails over to it.
- B. The FortiGate Unit B port2 interface will use virtual MAC addresses of 00-00-5e-00-01- 05 and 00-00-5e-00-01-0a, and all traffic fails over to it.
- C. The FortiGate Unit B port2 interface will use virtual MAC addresses of 00-a0-5e-00-01- 05 and 00-a0-5e-00-01-0a, and all traffic fails over to it.
- D. The FortiGate Unit B port2 interface will use the physical MAC addresses of the FortiGate Unit A port2 interface, and all traffic fails over to it.
Answer: B
Explanation:
If primary fails secondary device uses virtual mac address to forward traffic
NEW QUESTION 24
A café offers free Wi-Fi. Customers’ portable electronic devices often do not have antivirus software installed and may be hosting worms without their knowledge. You must protect all customers from any other customers’ infected devices that join the same SSID.
Which step meets the requirement?
- A. Enable deep SSH inspection with antivirus and IPS.
- B. Use a captive portal to redirect unsecured connections such as HTTP and SMTP to their secured equivalents, preventing worms on infected clients from tampering with other customer traffic.
- C. Use WPA2 encryption and configure a policy on FortiGate to block all traffic between clients.
- D. Use WPA2 encryption, and enable “Block Intra-SSID Traffic”.
Answer: B
NEW QUESTION 25
There is an interface-mode IPsec tunnel configured between FortiGate1 and FortiGate2. You want to run OSPF over the IPsec tunnel. On both FortiGates. the IPsec tunnel is based on physical interface port1. Port1 has the default MTU setting on both FortiGate units.
Which statement is true about this scenario?
- A. A multicast firewall policy must be added on FortiGate1 and FortiGate2 to allow protocol 89.
- B. The MTU must be set manually in the OSPF interface configuration.
- C. The MTU must be set manually on the IPsec interface.
- D. An IP address must be assigned to the IPsec interface on FortiGate1 and FortiGate2.
Answer: B
Explanation:
If MTU doesn’t match then the neighbour ship gets stuck in exchange state.
NEW QUESTION 26
......
P.S. Easily pass NSE8 Exam with 65 Q&As Dumpscollection Dumps & pdf Version, Welcome to Download the Newest Dumpscollection NSE8 Dumps: http://www.dumpscollection.net/dumps/NSE8/ (65 New Questions)
