It is impossible to pass Check-Point 156-315.80 exam without any help in the short term. Come to Certleader soon and find the most advanced, correct and guaranteed Check-Point 156-315.80 practice questions. You will get a surprising result by our Renew Check Point Certified Security Expert - R80 practice guides.
Free demo questions for Check-Point 156-315.80 Exam Dumps Below:
NEW QUESTION 1
To help SmartEvent determine whether events originated internally or externally you must define using the Initial Settings under General Settings in the Policy Tab. How many options are available to calculate the traffic direction?
- A. 5 Network; Host; Objects; Services; API
- B. 3 Incoming; Outgoing; Network
- C. 2 Internal; External
- D. 4 Incoming; Outgoing; Internal; Other
Answer: D
NEW QUESTION 2
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were
dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
- A. fw ctl multik dynamic_dispatching on
- B. fw ctl multik dynamic_dispatching set_mode 9
- C. fw ctl multik set_mode 9
- D. fw ctl multik pq enable
Answer: C
NEW QUESTION 3
Why would an administrator see the message below?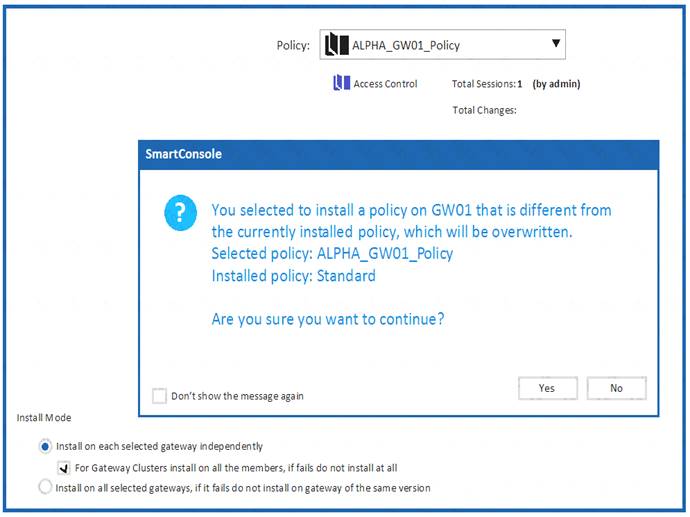
- A. A new Policy Package created on both the Management and Gateway will be deleted and must be backed up first before proceeding.
- B. A new Policy Package created on the Management is going to be installed to the existing Gateway.
- C. A new Policy Package created on the Gateway is going to be installed on the existing Management.
- D. A new Policy Package created on the Gateway and transferred to the Management will be overwritten by the Policy Package currently on the Gateway but can be restored from a periodic backup on the Gateway.
Answer: B
NEW QUESTION 4
Which command collects diagnostic data for analyzing customer setup remotely?
- A. cpinfo
- B. migrate export
- C. sysinfo
- D. cpview
Answer: A
Explanation:
CPInfo is an auto-updatable utility that collects diagnostics data on a customer's machine at the time of execution and uploads it to Check Point servers (it replaces the standalone cp_uploader utility for uploading files to Check Point servers).
The CPInfo output file allows analyzing customer setups from a remote location. Check Point support engineers can open the CPInfo file in a demo mode, while viewing actual customer Security Policies and Objects. This allows the in-depth analysis of customer's configuration and environment settings.
NEW QUESTION 5
Where you can see and search records of action done by R80 SmartConsole administrators?
- A. In SmartView Tracker, open active log
- B. In the Logs & Monitor view, select “Open Audit Log View”
- C. In SmartAuditLog View
- D. In Smartlog, all logs
Answer: B
NEW QUESTION 6
SandBlast has several functional components that work together to ensure that attacks are prevented in real-time. Which the following is NOT part of the SandBlast component?
- A. Threat Emulation
- B. Mobile Access
- C. Mail Transfer Agent
- D. Threat Cloud
Answer: C
NEW QUESTION 7
What are the two high availability modes?
- A. Load Sharing and Legacy
- B. Traditional and New
- C. Active and Standby
- D. New and Legacy
Answer: D
Explanation:
ClusterXL has four working modes. This section briefly describes each mode and its relative advantages and disadvantages.
NEW QUESTION 8
Fill in the blanks: A ________ license requires an administrator to designate a gateway for attachment whereas a ________ license is automatically attached to a Security Gateway.
- A. Formal; corporate
- B. Local; formal
- C. Local; central
- D. Central; local
Answer: D
NEW QUESTION 9
Which component is NOT required to communicate with the Web Services API?
- A. API key
- B. session ID token
- C. content-type
- D. Request payload
Answer: A
NEW QUESTION 10
What is true about the IPS-Blade?
- A. In R80, IPS is managed by the Threat Prevention Policy
- B. In R80, in the IPS Layer, the only three possible actions are Basic, Optimized and Strict
- C. In R80, IPS Exceptions cannot be attached to “all rules”
- D. In R80, the GeoPolicy Exceptions and the Threat Prevention Exceptions are the same
Answer: A
NEW QUESTION 11
In which VPN community is a satellite VPN gateway not allowed to create a VPN tunnel with another satellite VPN gateway?
- A. Pentagon
- B. Combined
- C. Meshed
- D. Star
Answer: D
NEW QUESTION 12
Due to high CPU workload on the Security Gateway, the security administrator decided to purchase a new CPU to replace the existing single core CPU. After installation, is the administrator required to perform any additional tasks?
- A. Go to clash-Run cpstop | Run cpstart
- B. Go to clash-Run cpconfig | Configure CoreXL to make use of the additional Cores | Exit cpconfig | Reboot Security Gateway
- C. Administrator does not need to perform any tas
- D. Check Point will make use of the newly installed CPU and Cores
- E. Go to clash-Run cpconfig | Configure CoreXL to make use of the additional Cores | Exit cpconfig | Reboot Security Gateway | Install Security Policy
Answer: B
NEW QUESTION 13
Which command will allow you to see the interface status?
- A. cphaprob interface
- B. cphaprob –I interface
- C. cphaprob –a if
- D. cphaprob stat
Answer: C
NEW QUESTION 14
Which of the completed statements is NOT true? The WebUI can be used to manage user accounts and:
- A. assign privileges to users.
- B. edit the home directory of the user.
- C. add users to your Gaia system.
- D. assign user rights to their home directory in the Security Management Server.
Answer: D
NEW QUESTION 15
You notice that your firewall is under a DDoS attack and would like to enable the Penalty Box feature, which command you use?
- A. sim erdos –e 1
- B. sim erdos – m 1
- C. sim erdos –v 1
- D. sim erdos –x 1
Answer: A
NEW QUESTION 16
Joey wants to upgrade from R75.40 to R80 version of Security management. He will use Advanced Upgrade with Database Migration method to achieve this.
What is one of the requirements for his success?
- A. Size of the /var/log folder of the source machine must be at least 25% of the size of the /var/log directory on the target machine
- B. Size of the /var/log folder of the target machine must be at least 25% of the size of the /var/log directory on the source machine
- C. Size of the $FWDIR/log folder of the target machine must be at least 30% of the size of the$FWDIR/log directory on the source machine
- D. Size of the /var/log folder of the target machine must be at least 25GB or more
Answer: B
NEW QUESTION 17
Which is NOT an example of a Check Point API?
- A. Gateway API
- B. Management API
- C. OPSEC SDK
- D. Threat Prevention API
Answer: A
NEW QUESTION 18
When using CPSTAT, what is the default port used by the AMON server?
- A. 18191
- B. 18192
- C. 18194
- D. 18190
Answer: B
NEW QUESTION 19
Which of the following blades is NOT subscription-based and therefore does not have to be renewed on a regular basis?
- A. Application Control
- B. Threat Emulation
- C. Anti-Virus
- D. Advanced Networking Blade
Answer: B
NEW QUESTION 20
The “Hit count” feature allows tracking the number of connections that each rule matches. Will the Hit count feature work independently from logging and Track the hits if the Track option is set to “None”?
- A. No, it will work independentl
- B. Hit Count will be shown only for rules Track option set as Log or alert.
- C. Yes it will work independently as long as “analyze all rules” tick box is enabled on the Security Gateway.
- D. No, it will not work independently because hit count requires all rules to be logged.
- E. Yes it will work independently because when you enable Hit Count, the SMS collects the data from supported Security Gateways.
Answer: D
NEW QUESTION 21
......
Recommend!! Get the Full 156-315.80 dumps in VCE and PDF From Dumpscollection.com, Welcome to Download: https://www.dumpscollection.net/dumps/156-315.80/ (New 428 Q&As Version)
