Exam Code: 312-49v9 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: ECCouncil Computer Hacking Forensic Investigator (V9)
Certification Provider: EC-Council
Free Today! Guaranteed Training- Pass 312-49v9 Exam.
NEW QUESTION 1
What is the "Best Evidence Rule"?
- A. It states that the court only allows the original evidence of a document, photograph, or recording at the trial rather than a copy
- B. It contains system time, logged-on user(s), open files, network information, process information, process-to-port mapping, process memory, clipboard contents, service/driverinformation, and command history
- C. It contains hidden files, slack space, swap file, index.dat files, unallocated clusters, unused partitions, hidden partitions, registry settings, and event logs
- D. It contains information such as open network connection, user logout, programs that reside in memory, and cache data
Answer: A
NEW QUESTION 2
Determine the message length from following hex viewer record: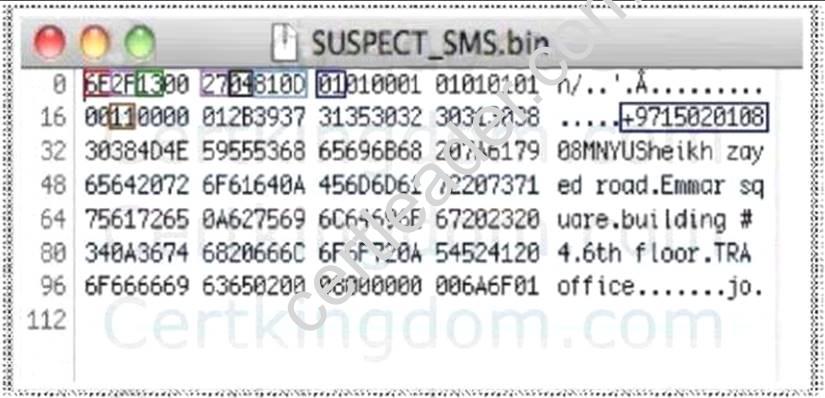
- A. 6E2F
- B. 13
- C. 27
- D. 810D
Answer: D
NEW QUESTION 3
Which of the following password cracking techniques works like a dictionary attack, but adds some numbers and symbols to the words from the dictionary and tries to crack the password?
- A. Brute forcing attack
- B. Hybrid attack
- C. Syllable attack
- D. Rule-based attack
Answer: B
NEW QUESTION 4
SIM is a removable component that contains essential information about the subscriber. It has both volatile and non- volatile memory. The file system of a SIM resides in ___ memory.
- A. Volatile
- B. Non-volatile
Answer: B
NEW QUESTION 5
Email archiving is a systematic approach to save and protect the data contained in emails so that it can tie easily accessed at a later date.
- A. True
- B. False
Answer: A
NEW QUESTION 6
How many characters long is the fixed-length MD5 algorithm checksum of a critical system file?
- A. 16
- B. 32
- C. 64
- D. 48
Answer: B
NEW QUESTION 7
Printing under a Windows Computer normally requires which one of the following files types to be created?
- A. EME
- B. MEM
- C. EMF
- D. CME
Answer: C
NEW QUESTION 8
Lance wants to place a honeypot on his network. Which of the following would be your recommendations?
- A. Use a system that has a dynamic addressing on the network
- B. Use a system that is not directly interacing with the router
- C. Use it on a system in an external DMZ in front of the firewall
- D. It doesn’t matter as all replies are faked
Answer: D
NEW QUESTION 9
What file structure database would you expect to find on floppy disks?
- A. NTFS
- B. FAT32
- C. FAT16
- D. FAT12
Answer: D
Explanation:
NTFS is not designed for removable media, although used on some removable media that is very large, never for floppy disks.
FAT32 has a minimum space requirement which is larger than floppy disks FAT16 would seem like a logical choice, but is not usually used on floppies FAT12 would be on floppy disks, and probably not seen on anything else. Since floppy disk media is small in size (less than 2 MB), a FAT12 file system has lower overhead and is more efficient.
NEW QUESTION 10
Area density refers to:
- A. the amount of data per disk
- B. the amount of data per partition
- C. the amount of data per square inch
- D. the amount of data per platter
Answer: AC
NEW QUESTION 11
When collecting evidence from the RAM, where do you look for data?
- A. Swap file
- B. SAM file
- C. Data file
- D. Log file
Answer: A
NEW QUESTION 12
Where are files temporarily written in Unix when printing?
- A. /usr/spool
- B. /var/print
- C. /spool
- D. /var/spool
Answer: D
NEW QUESTION 13
Jones had been trying to penetrate a remote production system for the past two weeks. This time however, he is able to get into the system. He was able to use the system for a period of three weeks. However law enforcement agencies were recording his every activity and this was later presented as evidence. The organization had used a virtual environment to trap Jones. What is a virtual environment?
- A. A system using Trojaned commands
- B. A honeypot that traps hackers
- C. An environment set up after the user logs in
- D. An environment set up before an user logs in
Answer: B
NEW QUESTION 14
Which legal document allows law enforcement to search an office, place of business, or other locale for evidence relating to an alleged crime?
- A. Search warrant
- B. Subpoena
- C. Wire tap
- D. Bench warrant
Answer: A
NEW QUESTION 15
With regard to using an antivirus scanner during a computer forensics investigation, you should:
- A. Scan the suspect hard drive before beginning an investigation
- B. Never run a scan on your forensics workstation because it could change your system configurationNever run a scan on your forensics workstation because it could change your system? configuration
- C. Scan your forensics workstation at intervals of no more than once every five minutes during an investigation
- D. Scan your forensics workstation before beginning an investigation
Answer: D
NEW QUESTION 16
Which of the following log injection attacks uses white space padding to create unusual log entries?
- A. Word wrap abuse attack
- B. HTML injection attack
- C. Terminal injection attack
- D. Timestamp injection attack
Answer: A
NEW QUESTION 17
John is using Firewalk to test the security of his Cisco PIX firewall. He is also utilizing a sniffer located on a subnet that resides deep inside his network. After analyzing the sniffer log files, he does not see any of the traffic produced by Firewalk. Why is that?
- A. Firewalk sets all packets with a TTL of one
- B. Firewalk sets all packets with a TTL of zero
- C. Firewalk cannot pass through Cisco firewalls
- D. Firewalk cannot be detected by network sniffers
Answer: A
NEW QUESTION 18
Centralized logging is defined as gathering the computer system logs for a group of systems in a centralized location. It is used to efficiently monitor computer system logs with the frequency required to detect security violations and unusual activity.
- A. True
- B. False
Answer: A
NEW QUESTION 19
During the course of a corporate investigation, you find that an employee is committing a federal crime. Can the employer file a criminal complain with the police?
- A. Yes, and all evidence can be turned over to the police
- B. Yes, but only if you turn the evidence over to a district judge
- C. No, because the investigation was conducted without following standard police procedures
- D. No, because the investigation was conducted without a warrant
Answer: A
NEW QUESTION 20
Which of the following attacks allows an attacker to access restricted directories, including application source code, configuration and critical system files, and to execute commands outside of the web server's root directory?
- A. Unvalidated input
- B. Parameter/form tampering
- C. Directory traversal
- D. Security misconfiguration
Answer: C
NEW QUESTION 21
Wireless network discovery tools use two different methodologies to detect, monitor and log a WLAN device (i.e. active scanning and passive scanning). Active scanning methodology involves ____ and waiting for responses from available wireless networks.
- A. Broadcasting a probe request frame
- B. Sniffing the packets from the airwave
- C. Scanning the network
- D. Inspecting WLAN and surrounding networks
Answer: A
NEW QUESTION 22
What is static executable file analysis?
- A. It is a process that consists of collecting information about and from an executable file without actually launching the file under any circumstances
- B. It is a process that consists of collecting information about and from an executable file by launching the file under any circumstances
- C. It is a process that consists of collecting information about and from an executable file without actually launching an executable file in a controlled and monitored environment
- D. It is a process that consists of collecting information about and from an executable file by launching an executable filein a controlled and monitored environment
Answer: A
NEW QUESTION 23
Why would a company issue a dongle with the software they sell?
- A. To provide source code protection
- B. To provide wireless functionality with the software
- C. To provide copyright protection
- D. To ensure that keyloggers cannot be used
Answer: C
NEW QUESTION 24
What must an investigator do before disconnecting an iPod from any type of computer?
- A. Unmount the iPod
- B. Mount the iPod
- C. Disjoin the iPod
- D. Join the iPod
Answer: A
NEW QUESTION 25
The need for computer forensics is highlighted by an exponential increase in the number of cybercrimes and litigations where large organizations were involved. Computer forensics plays an important role in tracking the cyber criminals. The main role of computer forensics is to:
- A. Maximize the investigative potential by maximizing the costs
- B. Harden organization perimeter security
- C. Document monitoring processes of employees of the organization
- D. Extract, process, and interpret the factual evidence so that it proves the attacker's actions in the court
Answer: D
NEW QUESTION 26
You are running known exploits against your network to test for possible vulnerabilities. To test the strength of your virus software, you load a test network to mimic your production
network. Your software successfully blocks some simple macro and encrypted viruses. You decide to really test the software by using virus code where the code rewrites itself entirely and the signatures change from child to child, but the functionality stays the same. What type of virus is this that you are testing?
- A. Oligomorhic
- B. Transmorphic
- C. Polymorphic
- D. Metamorphic
Answer: D
NEW QUESTION 27
Jason, a renowned forensic investigator, is investigating a network attack that resulted in the compromise of several systems in a reputed multinational's network. He started Wireshark to capture the network traffic. Upon investigation, he found that the DNS packets travelling across the network belonged to a non-company configured IP. Which of the following attack Jason can infer from his findings?
- A. DNS Poisoning
- B. Cookie Poisoning Attack
- C. DNS Redirection
- D. Session poisoning
Answer: A
NEW QUESTION 28
......
P.S. Easily pass 312-49v9 Exam with 209 Q&As Simply pass Dumps & pdf Version, Welcome to Download the Newest Simply pass 312-49v9 Dumps: https://www.simply-pass.com/EC-Council-exam/312-49v9-dumps.html (209 New Questions)
