we provide Highest Quality EC-Council 412-79v9 exam price which are the best for clearing 412-79v9 test, and to get certified by EC-Council EC-Council Certified Security Analyst (ECSA) v9. The 412-79v9 Questions & Answers covers all the knowledge points of the real 412-79v9 exam. Crack your EC-Council 412-79v9 Exam with latest dumps, guaranteed!
EC-Council 412-79v9 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
A Blind SQL injection is a type of SQL Injection attack that asks the database true or false questions and determines the answer based on the application response. This attack is often used when the web application is configured to show generic error messages, but has not mitigated the code that is vulnerable to SQL injection.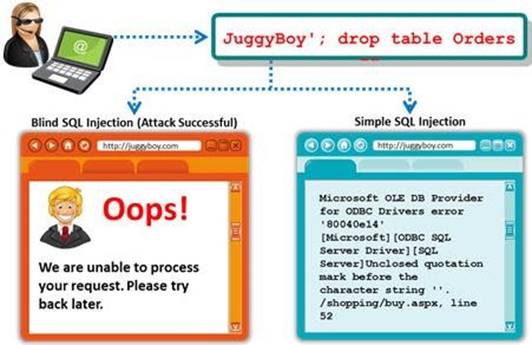
It is performed when an error message is not received from application while trying to exploit SQL vulnerabilities. The developer's specific message is displayed instead of an error message. So it is quite difficult to find SQL vulnerability in such cases.
A pen tester is trying to extract the database name by using a blind SQL injection. He tests the database using the below query and finally finds the database name.
http://juggyboy.com/page.aspx?id=1; IF (LEN(DB_NAME())=4) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),1,1)))=97) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),2,1)))=98) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),3,1)))=99) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),4,1)))=100) WAITFOR DELAY '00:00:10'--
What is the database name?
- A. WXYZ
- B. PQRS
- C. EFGH
- D. ABCD
Answer: D
Explanation:
Reference: http://www.scribd.com/doc/184891028/CEHv8-Module-14-SQL-Injection-pdf (see module 14, page 2049 to 2051)
NEW QUESTION 2
Which of the following defines the details of services to be provided for the client’s organization and the list of services required for performing the test in the organization?
- A. Draft
- B. Report
- C. Requirement list
- D. Quotation
Answer: D
NEW QUESTION 3
Which of the following statements is true about the LM hash?
- A. Disabled in Windows Vista and 7 OSs
- B. Separated into two 8-character strings
- C. Letters are converted to the lowercase
- D. Padded with NULL to 16 characters
Answer: A
Explanation:
Reference: http://www.onlinehashcrack.com/how_to_crack_windows_passwords.php (first paragraph of the page)
NEW QUESTION 4
Which of the following password cracking techniques is used when the attacker has some information about the password?
- A. Hybrid Attack
- B. Dictionary Attack
- C. Syllable Attack
- D. Rule-based Attack
Answer: D
Explanation:
Reference: http://202.154.59.182/mfile/files/Information%20System/Computer%20Forensics%3B%20H ard%20Disk%20and%20Operating%20Systems/CHAPTER%207%20Application%20Password%20Crackers.pdf (page 4, rule-based attack)
NEW QUESTION 5
Which one of the following architectures has the drawback of internally considering the hosted services individually?
- A. Weak Screened Subnet Architecture
- B. "Inside Versus Outside" Architecture
- C. "Three-Homed Firewall" DMZ Architecture
- D. Strong Screened-Subnet Architecture
Answer: C
NEW QUESTION 6
In Linux, /etc/shadow file stores the real password in encrypted format for user’s account with added properties associated with the user’s password.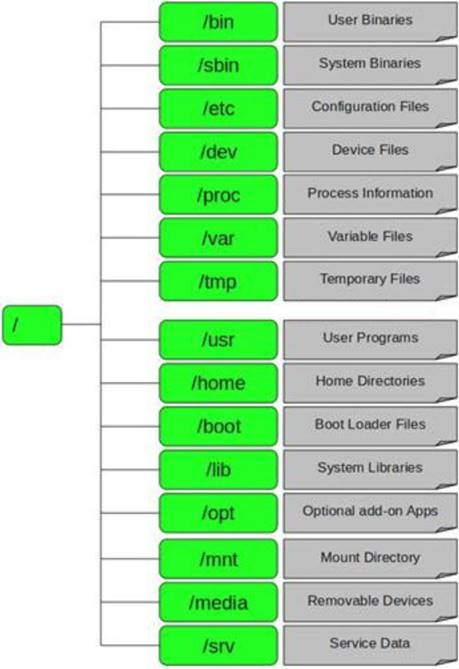
In the example of a /etc/shadow file below, what does the bold letter string indicate?
Vivek: $1$fnffc$GteyHdicpGOfffXX40w#5:13064:0:99999:7
- A. Number of days the user is warned before the expiration date
- B. Minimum number of days required between password changes
- C. Maximum number of days the password is valid
- D. Last password changed
Answer: B
Explanation:
Reference: http://www.cyberciti.biz/faq/understanding-etcshadow-file/ (bullet # 4)
NEW QUESTION 7
Which one of the following is a supporting tool for 802.11 (wireless) packet injections, it spoofs 802.11 packets to verify whether the access point is valid or not?
- A. Airsnort
- B. Aircrack
- C. Airpwn
- D. WEPCrack
Answer: C
NEW QUESTION 8
The term social engineering is used to describe the various tricks used to fool people (employees, business partners, or customers) into voluntarily giving away information that would not normally be known to the general public.
What is the criminal practice of social engineering where an attacker uses the telephone system in an attempt to scam the user into surrendering private information?
- A. Phishing
- B. Spoofing
- C. Tapping
- D. Vishing
Answer: D
NEW QUESTION 9
Nessus can test a server or a network for DoS vulnerabilities. Which one of the following script tries to kill a service?
- A. ACT_DENIAL
- B. ACT_FLOOD
- C. ACT_KILL_HOST
- D. ACT_ATTACK
Answer: A
NEW QUESTION 10
Mason is footprinting an organization to gather competitive intelligence. He visits the company's website for contact information and telephone numbers but does not find any. He knows the entire staff directory was listed on their website 12 months. How can he find the directory?
- A. Visit Google’s search engine and view the cached copy
- B. Crawl and download the entire website using the Surfoffline tool and save them to his computer
- C. Visit the company's partners’ and customers' website for this information
- D. Use WayBackMachine in Archive.org web site to retrieve the Internet archive
Answer: D
NEW QUESTION 11
Wireless communication allows networks to extend to places that might otherwise go untouched by the wired networks. When most people say ‘Wireless’ these days, they are referring to one of the 802.11 standards. There are three main 802.11 standards: B, A, and
- A. Which one of the following 802.11 types uses DSSS Modulation, splitting the 2.4ghz band into channels?
- B. 802.11b
- C. 802.11g
- D. 802.11-Legacy
- E. 802.11n
Answer: A
NEW QUESTION 12
During the process of fingerprinting a web application environment, what do you need to do in order to analyze HTTP and HTTPS request headers and the HTML source code?
- A. Examine Source of the Available Pages
- B. Perform Web Spidering
- C. Perform Banner Grabbing
- D. Check the HTTP and HTML Processing by the Browser
Answer: D
NEW QUESTION 13
Internet Control Message Protocol (ICMP) messages occur in many situations, such as whenever a datagram cannot reach the destination or the gateway does not have the buffering capacity to forward a datagram. Each ICMP message contains three fields: type, code, and checksum. Different types of Internet Control Message Protocols (ICMPs) are identified by a TYPE field. If the destination is not reachable, which one of the following are generated?
- A. Type 8 ICMP codes
- B. Type 12 ICMP codes
- C. Type 3 ICMP codes
- D. Type 7 ICMP codes
Answer: C
NEW QUESTION 14
Before performing the penetration testing, there will be a pre-contract discussion with different pen-testers (the team of penetration testers) to gather a quotation to perform pen testing.
Which of the following factors is NOT considered while preparing a price quote to perform pen testing?
- A. Total number of employees in the client organization
- B. Type of testers involved
- C. The budget required
- D. Expected time required to finish the project
Answer: A
NEW QUESTION 15
An antenna is a device that is designed to transmit and receive the electromagnetic waves that are generally called radio waves. Which one of the following types of antenna is
developed from waveguide technology?
- A. Leaky Wave Antennas
- B. Aperture Antennas
- C. Reflector Antenna
- D. Directional Antenna
Answer: B
NEW QUESTION 16
A directory traversal (or path traversal) consists in exploiting insufficient security validation/sanitization of user-supplied input file names, so that characters representing "traverse to parent directory" are passed through to the file APIs.
The goal of this attack is to order an application to access a computer file that is not intended to be accessible. This attack exploits a lack of security (the software is acting exactly as it is supposed to) as opposed to exploiting a bug in the code.
To perform a directory traversal attack, which sequence does a pen tester need to follow to manipulate variables of reference files?
- A. dot-dot-slash (../) sequence
- B. Denial-of-Service sequence
- C. Brute force sequence
- D. SQL Injection sequence
Answer: A
Explanation:
Reference: https://www.cs.ucsb.edu/~vigna/publications/2010_doupe_cova_vigna_dimva10.pdf (pae 7, directory traversal)
NEW QUESTION 17
TCP/IP provides a broad range of communication protocols for the various applications on the network. The TCP/IP model has four layers with major protocols included within each layer. Which one of the following protocols is used to collect information from all the network devices?
- A. Simple Network Management Protocol (SNMP)
- B. Network File system (NFS)
- C. Internet Control Message Protocol (ICMP)
- D. Transmission Control Protocol (TCP)
Answer: A
NEW QUESTION 18
Which of the following reports provides a summary of the complete pen testing process, its outcomes, and recommendations?
- A. Vulnerability Report
- B. Executive Report
- C. Client-side test Report
- D. Host Report
Answer: B
NEW QUESTION 19
Which one of the following log analysis tools is a Cisco Router Log Format log analyzer and it parses logs, imports them into a SQL database (or its own built-in database), aggregates them, and generates the dynamically filtered reports, all through a web interface?
- A. Event Log Tracker
- B. Sawmill
- C. Syslog Manager
- D. Event Log Explorer
Answer: B
NEW QUESTION 20
Wireshark is a network analyzer. It reads packets from the network, decodes them, and presents them in an easy-to-understand format. Which one of the following is the command-line version of Wireshark, which can be used to capture the live packets from the wire or to read the saved capture files?
- A. Tcpdump
- B. Capinfos
- C. Tshark
- D. Idl2wrs
Answer: B
NEW QUESTION 21
Port numbers are used to keep track of different conversations crossing the network at the same time. Both TCP and UDP use port (socket) numbers to pass information to the upper layers. Port numbers have the assigned ranges.
Port numbers above 1024 are considered which one of the following?
- A. Dynamically assigned port numbers
- B. Statically assigned port numbers
- C. Well-known port numbers
- D. Unregistered port numbers
Answer: A
Explanation:
Reference: http://stackoverflow.com/questions/136709/what-port-number-should-i-use-when-testing-connections-in-my-local-intranet-in (see post 4)
NEW QUESTION 22
Identify the person who will lead the penetration-testing project and be the client point of contact.
- A. Database Penetration Tester
- B. Policy Penetration Tester
- C. Chief Penetration Tester
- D. Application Penetration Tester
Answer: C
Explanation:
Reference: http://www.scribd.com/doc/133635286/LPTv4-Module-15-Pre-Penetration-Testing-Checklist-NoRestriction (page 15)
NEW QUESTION 23
Attackers create secret accounts and gain illegal access to resources using backdoor while bypassing the authentication procedures. Creating a backdoor is a where an attacker obtains remote access to a computer on a network.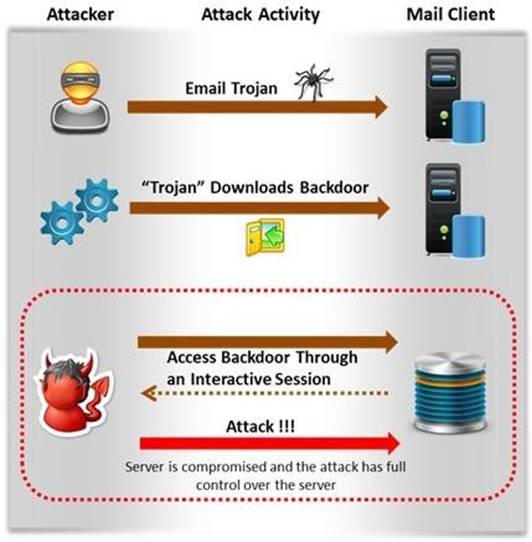
Which of the following techniques do attackers use to create backdoors to covertly gather
critical information about a target machine?
- A. Internal network mapping to map the internal network of the target machine
- B. Port scanning to determine what ports are open or in use on the target machine
- C. Sniffing to monitor all the incoming and outgoing network traffic
- D. Social engineering and spear phishing attacks to install malicious programs on the target machine
Answer: D
NEW QUESTION 24
Identify the framework that comprises of five levels to guide agency assessment of their security programs and assist in prioritizing efforts for improvement:
- A. Information System Security Assessment Framework (ISSAF)
- B. Microsoft Internet Security Framework
- C. Nortells Unified Security Framework
- D. Federal Information Technology Security Assessment Framework
Answer: D
NEW QUESTION 25
Port numbers are used to keep track of different conversations crossing the network at the same time. Both TCP and UDP use port (socket) numbers to pass information to the upper
layers. Port numbers have the assigned ranges. The port numbers above 1024 are considered as which one of the following? (Select all that apply)
- A. Well-known port numbers
- B. Dynamically assigned port numbers
- C. Unregistered port numbers
- D. Statically assigned port numbers
Answer: B
NEW QUESTION 26
What is a difference between host-based intrusion detection systems (HIDS) and network- based intrusion detection systems (NIDS)?
- A. NIDS are usually a more expensive solution to implement compared to HIDS.
- B. Attempts to install Trojans or backdoors cannot be monitored by a HIDS whereas NIDS can monitor and stop such intrusion events.
- C. NIDS are standalone hardware appliances that include network intrusion detection capabilities whereas HIDS consist of software agents installed on individual computers within the system.
- D. HIDS requires less administration and training compared to NIDS.
Answer: C
NEW QUESTION 27
A pen tester has extracted a database name by using a blind SQL injection. Now he begins to test the table inside the database using the below query and finds the table:
http://juggyboy.com/page.aspx?id=1; IF (LEN(SELECT TOP 1 NAME from sysobjects where xtype='U')=3) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),1,1)))=101) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),2,1)))=109) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),3,1)))=112) WAITFOR DELAY '00:00:10'—
What is the table name?
- A. CTS
- B. QRT
- C. EMP
- D. ABC
Answer: C
NEW QUESTION 28
This is a group of people hired to give details of the vulnerabilities present in the system found after a penetration test. They are elite and extremely competent penetration testers and intrusion analysts. This team prepares a report on the vulnerabilities in the system, attack methods, and how to defend against them.
What is this team called?
- A. Blue team
- B. Tiger team
- C. Gorilla team
- D. Lion team
Answer: B
NEW QUESTION 29
......
Thanks for reading the newest 412-79v9 exam dumps! We recommend you to try the PREMIUM Surepassexam 412-79v9 dumps in VCE and PDF here: https://www.surepassexam.com/412-79v9-exam-dumps.html (203 Q&As Dumps)
