Master the H12-711_V3.0 HCIA-Security V3.0 content and be ready for exam day success quickly with this Passleader H12-711_V3.0 exam question. We guarantee it!We make it a reality and give you real H12-711_V3.0 questions in our HUAWEI H12-711_V3.0 braindumps.Latest 100% VALID HUAWEI H12-711_V3.0 Exam Questions Dumps at below page. You can use our HUAWEI H12-711_V3.0 braindumps and pass your exam.
Also have H12-711_V3.0 free dumps questions for you:
NEW QUESTION 1
According to the logical architecture of the HiSec solution, please drag the HiSec solutions on the left to the right box and arrange them in order from top to bottom
Solution:
analyzers, controllers, actuators
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 2
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
Solution:
3124
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 3
When we use digital signature technology, the receiver needs to use the sender's ( ) to unlock the digital signature to get the digital fingerprint. (fill in the blank)
Solution:
public key
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 4
some applications such asOracleFor database applications, the firewall session connection is interrupted due to no data flow transmission for a long time, resulting in service interruption. Which of the following is the optimal solution?
- A. Configure a long-term connection for a service
- B. turn onASPFFeatures
- C. Optimize security policies
- D. Enable shard cache
Answer: A
NEW QUESTION 5
NAPTtechnology can realize a public networkIPThe address is used by multiple private network hosts
- A. True
- B. False
Answer: A
NEW QUESTION 6
MACWhich of the following mechanisms are used by flood attacks? (multiple choice)
- A. switchMAClearning mechanism
- B. Switch Forwarding Mechanism
- C. ARPlearning mechanism
- D. MACLimit on the number of entries
Answer: ABCD
NEW QUESTION 7
Which of the following is true about the difference between pre-incident prevention strategies and post-incident recovery strategies? (multiple choice)
- A. Prevention strategies focus on minimizing the likelihood of an accident before a story occur
- B. Recovery strategies focus on minimizing the impact and damage to the business after an incident
- C. The role of pre-disaster prevention strategies does not include minimizing economic and reputational losses caused by accidents
- D. Recovery strategies are used to improve business high availability
- E. A recovery strategy is part of a business continuity plan
Answer: ACD
NEW QUESTION 8
ASPF(Application Specific Packet Filter) is a packet filtering technology based on the application layer and is passed throughserver-mapTables implement special security mechanisms.
aboutASPFandserver-mapWhich of the following statements is correct? (multiple choice)
- A. ASPFMonitor messages during communication
- B. ASPFcan be created dynamicallyserver-mapsurface
- C. ASPFpass throughserver-mapTable implementation dynamically allows multi-channel protocol data to pass through
- D. Quintupleserver-mapThe table entry implements a similar function to the session table
Answer: ABC
NEW QUESTION 9
Social engineering is a means of harm such as deception, harm, etc., through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims.
- A. True
- B. False
Answer: A
NEW QUESTION 10
In order to obtain criminal evidence, it is necessary to master the technology of intrusion tracking. Which of the following options are correct for the description of tracking technology? (multiple choice)
- A. Packet logging technology through the tracedIPInsert trace data into packets to mark packets on each router they pass through
- B. Link testing technology determines the information of the attack source by testing the network link between routers
- C. Packet marking technology extracts attack source information by logging packets on routers and then using data drilling techniques
- D. Shallow mail behavior analysis can achieveIPAnalysis of addresses, sent time, sending frequency, number of recipients, shallow email headers, and more.
Answer: ABD
NEW QUESTION 11
According to the number of users operating at the same time, the operating system can be divided into
single-user operating system and multi-user operating system. Which of the following items is not a multi-user operating system?
- A. UNIX
- B. OS/2
- C. Linux
- D. MSDOS
Answer: BD
NEW QUESTION 12
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules? ( )[Multiple choice]*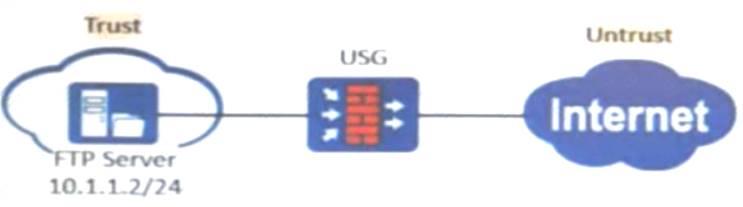
- A. rule name
- B. source-zone untrus
- C. destination-zone trus
- D. destination-address 202.106.1.132, action permit
- E. rule name d, source- zone untrus
- F. destination- zone trus
- G. destination- address10.l0.1.1 32, action permit
- H. rule name b, source- zone untrust, destination- zone trust, source- address10.10.1.1 32, action permit
- I. rule name b, source-zone untrust, destination-zone trust, source-address202.106.l.1 32, action permit
Answer: B
NEW QUESTION 13
Please sort from large to small according to the table processing priority of iptables.[fill in the blank]*
Solution:
raw.mangle nat.filter
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
The key used by DES encryption is bits, while the key used by 3DES encryption is bits.
- A. 56168
- B. 64168
- C. 64128
- D. 56128
Answer: D
NEW QUESTION 15
existClient-Initiated VPNDuring the configuration, it is generally recommended to plan the address pool and the headquarters network address as different network segments. Otherwise, the proxy forwarding function needs to be enabled on the gateway device.
- A. True
- B. False
Answer: B
NEW QUESTION 16
......
P.S. Easily pass H12-711_V3.0 Exam with 492 Q&As Dumps-files.com Dumps & pdf Version, Welcome to Download the Newest Dumps-files.com H12-711_V3.0 Dumps: https://www.dumps-files.com/files/H12-711_V3.0/ (492 New Questions)
