we provide Practical HP HPE7-A01 exam answers which are the best for clearing HPE7-A01 test, and to get certified by HP Aruba Certified Campus Access Professional Exam. The HPE7-A01 Questions & Answers covers all the knowledge points of the real HPE7-A01 exam. Crack your HP HPE7-A01 Exam with latest dumps, guaranteed!
Also have HPE7-A01 free dumps questions for you:
NEW QUESTION 1
Which statements regarding 0SPFv2 route redistribution are true for Aruba OS CX switches? (Select two.)
- A. The "redistribute connected" command will redistribute all connected routes for the switch including local loopback addresses
- B. The "redistribute ospf" command will redistribute routes from all OSPF V2 and V3 processes
- C. The "redistribute static route-map connected-routes" command will redistribute all static routes without a matching deny in the route map "connected-routes".
- D. The "redistribute connected" command will redistribute all connected routes for the switch except local loopback addresses.
- E. The "redistribute static route-map connected-routes" command will redistribute all static routes with a matching permit in the route map "connected-routes-
Answer: AE
Explanation:
These are two correct statements regarding OSPFv2 route redistribution for Aruba OS CX switches. Route redistribution is a process that allows routes from one routing protocol or source to be injected into another routing protocol or destination. OSPFv2 is a link-state routing protocol that supports route redistribution from various sources, such as connected, static, BGP, etc. The ??redistribute connected?? command will redistribute all connected routes for the switch, including local loopback addresses, into OSPFv2. The ??redistribute static route-map connected-routes?? command will redistribute all static routes that have a matching permit statement in the route map named ??connected- routes?? into OSPFv2. The other statements are incorrect because they either do not reflect the correct behavior of route redistribution commands or do not exist as valid commands. References: https://www.arubanetworks.com/techdocs/AOS-CX/10.04/HTML/5200- 6728/bk01-ch02.html https://www.arubanetworks.com/techdocs/AOS- CX/10.04/HTML/5200-6728/bk01-ch03.html
NEW QUESTION 2
DRAG DROP
What is the order of operations tor Key Management service for a wireless client roaming from AP1 to AP2?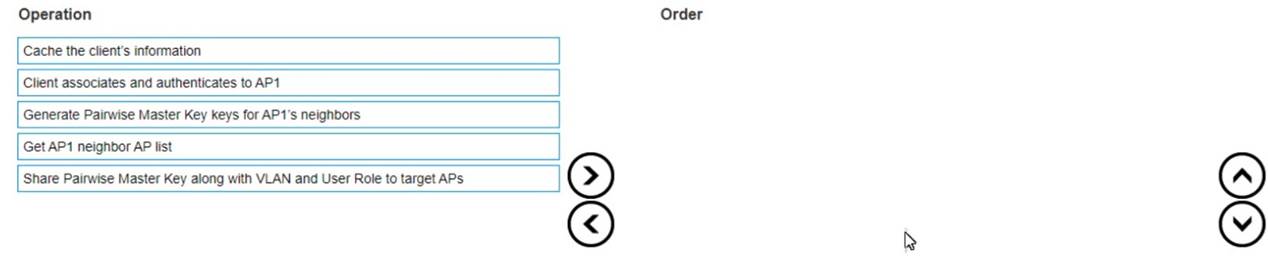
Solution:
https://www.arubanetworks.com/techdocs/Instant_85_WebHelp/Content/instant-ug/wlan-ssid-conf/conf-fast-roam.htm
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 3
What is true regarding 802.11k?
- A. It extends radio measurements to define mechanisms for wireless network management of stations
- B. It reduces roaming delay by pre-authenticating clients with multiple target APs before a client roams to an AP
- C. It provides mechanisms for APs and clients to dynamically measure the available radio resources.
- D. It considers several metrics before it determines if a client should be steered to the 5GHz band, including client RSSI
Answer: C
Explanation:
802.11k is a standard that provides mechanisms for APs and clients to dynamically measure the available radio resources in a wireless network. 802.11k defines radio resource management (RRM) functions, such as neighbor reports, link measurement, beacon reports, etc., that allow APs and clients to exchange information about the RF environment and make better roaming decisions. The other options are incorrect because they describe other standards, such as 802.11r, 802.11v, or 802.11ax. References: https://www.arubanetworks.com/assets/wp/WP_WiFi6.pdf https://www.arubanetworks.com/assets/ds/DS_AP510Series.pdf
NEW QUESTION 4
A customer is using stacked Aruba CX 6200 and CX 6300 switches for access and a VSX pair of Aruba CX 8325 as a collapsed core 802 1X is implemented for authentication. Due to the lack of cabling, some unmanaged switches are still in use Sometimes devices behind these switches cause network outages The switch should send a warning to the helpdesk when the problem occurs You have been asked to implement an effective solution to the problem
What is the solution for this?
- A. Configure spanning tree on the Aruba CX 8325 switches Set the trap-option
- B. Configure loop protection on all edge ports of the Aruba CX 6200 and CX 6300 switches No trap option is needed
- C. Configure loop protection on all edge ports of the Aruba CX 6200 and CX 6300 switches Set up the trap-option
- D. Configure spanning tree on the Aruba CX 6200 and CX 6300 switches No trap option is needed
Answer: C
Explanation:
This is the correct solution to the problem of devices behind unmanaged switches causing network outages due to loops. Loop protection is a feature that allows an Aruba CX switch to detect and prevent loops by sending loop protection packets on each port, LAG, or VLAN on which loop protection is enabled. If a loop protection packet is received by the same switch that sent it, it indicates a loop exists and an action is taken based on the configuration. Loop protection should be configured on all edge ports of the Aruba CX 6200 and CX 6300 switches, which are the ports that connect to end devices or unmanaged switches. The trap-option should be set up to send a warning to the helpdesk when a loop is detected. The other options are incorrect because they either do not configure loop protection or do not set up the trap-option. References: https://www.arubanetworks.com/techdocs/AOS-CX/10.05/HTML/5200-7540/GUID-99A8B276-0DA3-4458-AFD8-42BFEC29D4F5.html
https://www.arubanetworks.com/techdocs/AOS-CX/10.05/HTML/5200-7540/GUID-D8613BDE-CD21-4B83-8561-17DB0311ED8F.html
NEW QUESTION 5
Which component is used by the Aruba Network Analytics Engine (NAE)?
- A. JSON-based scripts
- B. Lisp-based agents
- C. Ruby-based scripts
- D. Current State Database
Answer: A
Explanation:
The component that is used by the Aruba Network Analytics Engine (NAE) is D. Current State Database.
The Current State Database is a database that stores the configuration and state information of the switch, such as interfaces, VLANs, routing protocols, statistics, and more. The NAE can access this database through the AOS-CX REST API and monitor the values of any data point using monitors. The NAE can also track the history of the values in a time-series database and correlate them with network events or configuration changes1. The Current State Database provides NAE with direct visibility into the entire current state of the device, which enables intelligent troubleshooting and automation of network tasks1. The other options are incorrect because:
✑ A. JSON-based scripts: JSON is a data format that is used to exchange information between applications. It is not a scripting language that can be used by NAE. NAE scripts are written in Python, which is a popular and powerful programming language1.
✑ B. Lisp-based agents: Lisp is a family of programming languages that are mainly used for artificial intelligence and functional programming. It is not a language that can be used by NAE. NAE agents are instances of scripts that run on the switch and collect relevant network information and trigger alerts or actions1.
✑ C. Ruby-based scripts: Ruby is a general-purpose programming language that is known for its expressiveness and elegance. It is not a language that can be used by NAE. NAE scripts are written in Python, which is a popular and powerful programming language1.
NEW QUESTION 6
A customer is using a legacy application that communicates at layer-2. The customer would like to keep this application working to a remote site connected via layer-3 All legacy devices are connected to a dedicated Aruba CX 6200 switch at each site.
What technology on the Aruba CX 6200 could be used to meet this requirement?
- A. Inclusive Multicast Ethernet Tag (IMET)
- B. Ethernet over IP (EolP)
- C. Generic Routing Encapsulation (GRE)
- D. Static VXLAN
Answer: A
Explanation:
VXLAN is a technology that can be used to meet the requirement of using a legacy application that communicates at layer-2 across a layer-3 network. Static VXLAN is a feature that allows the creation of layer-2 overlay networks over a layer-3 underlay network using VXLAN tunnels. Static VXLAN does not require any control plane protocol or VTEP discovery mechanism, and can be configured manually on the Aruba CX 6200 switches. The other options are incorrect because they either do not support layer-2 communication over layer-3 network or are not supported by Aruba CX 6200 switches. References: https://www.arubanetworks.com/techdocs/AOS-CX/10.04/HTML/5200- 6728/bk01-ch03.html https://www.arubanetworks.com/techdocs/AOS- CX/10.04/HTML/5200-6728/bk01-ch05.html
NEW QUESTION 7
Refer to Exhibit: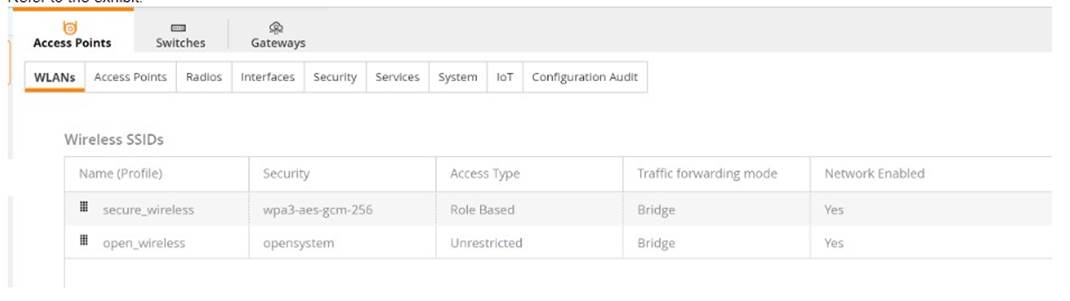
A company has deployed 200 AP-635 access points. To take advantage of the 6 GHz band, the administrator has attempted to configure a new WPA3-OWE SSID in Central but is not working as expected.
What would be the correct action to fix the issue?
- A. Change the SSID to WPA3-Enterprise (CNSA).
- B. Change the SSID to WPA3-Personal.
- C. Change the SSID to WPA3-Enhanced Open.
- D. Change the SSID to WPA3-Enterprise (CCM).
Answer: C
Explanation:
The correct action to fix the issue is C. Change the SSID to WPA3-Enhanced Open.
WPA3-OWE is not a valid SSID type in Central. OWE stands for Opportunistic Wireless Encryption, and it is a feature that provides encryption for open networks without requiring authentication. OWE is also known as Enhanced Open, and it is one of the options for WPA3 SSIDs in Central1.
According to the Aruba document Configuring WLAN Settings for an SSID Profile, one of the steps to configure a WPA3 SSID is:
✑ Select the Security Level from the drop-down list. The following options are available:
The other options are incorrect because:
✑ A. WPA3-Enterprise (CNSA) is a valid SSID type, but it requires 802.1X authentication with a RADIUS server, which may not be suitable for the company??s use case.
✑ B. WPA3-Personal is a valid SSID type, but it requires a passphrase to join the network, which may not be suitable for the company??s use case.
✑ D. WPA3-Enterprise (CCM) is a valid SSID type, but it requires 802.1X authentication with a RADIUS server, which may not be suitable for the company??s use case.
NEW QUESTION 8
You are configuring an SVI on an Aruba CX switch that needs to have the following characteristics:
• VLANID = 25
. IPv4 address 10 105 43 1 with mask 255 255 255.0
• IPv6 address fd00:5708::f02d:4df6 with a 64 bit prefix length
• member of VRF eng
• VRF eng and VLAN 25 have not yet been created
Which command lists will satisfy the requirements with the least number of commands?
A)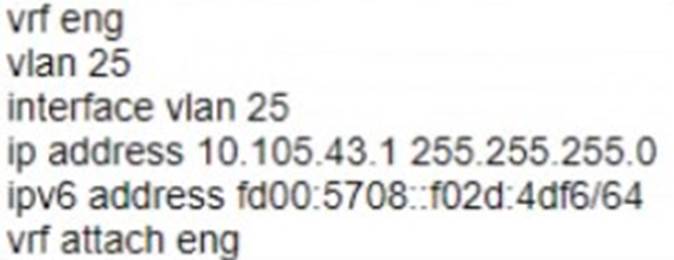
B)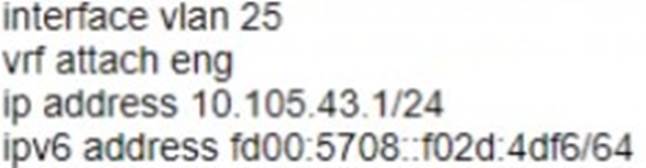
C)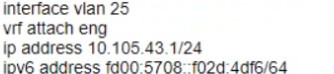
D)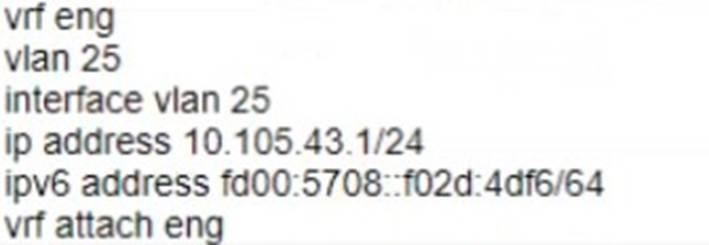
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: C
Explanation:
The other options either use more commands or do not create the VRF or the VLAN.
Option C uses the following commands:
✑ vrf eng: This command creates a VRF named eng and enters the VRF configuration mode1.
✑ vlan 25: This command creates a VLAN with ID 25 and enters the VLAN configuration mode2.
✑ interface vlan 25: This command creates an SVI on VLAN 25 and enters the interface configuration mode3.
✑ ip address 10.105.43.1/24 ipv6 address fd00:5780::102d:4df6/64 vrf attach eng: This command assigns an IPv4 address of 10.105.43.1 with a subnet mask of 255.255.255.0 and an IPv6 address of fd00:5780::102d:4df6 with a prefix length of 64 to the SVI, and attaches it to the VRF eng.
NEW QUESTION 9
DRAG DROP
Select the Aruba stacking technology matching each option (Options may be used more than once or not at all.)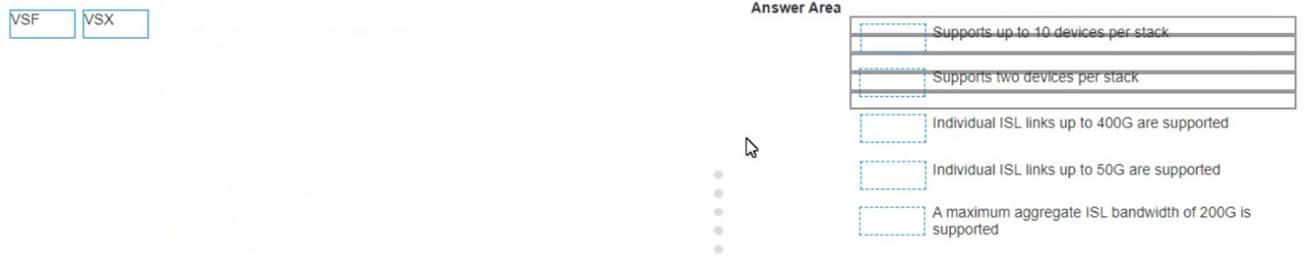
Solution:
a) Support up to 10 devices per stack -> VSF
b) Support two devices per stack -> VSX
c) Individual ISL links up to 400G are supported -> VSX
d) individual ISL links up to 50G are supported -> VSF
e) A maximum aggregate ISL bandwidth of 200G is supported -> VSF
References: 1 https://www.arubanetworks.com/techdocs/AOS-CX/10.04/HTML/5200-6728/GUID-2E425DAE-EC54-4313-9DEA-A61817F903C0.html
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
You are setting up a customer's 15 headless loT devices that do not support 802.1X. What should you use?
- A. Multiple Pre-Shared Keys (MPSK) Local
- B. Clearpass with WPA3-PSK
- C. Clearpass with WPA3-AES
- D. Multiple Pre-Shared Keys (MPSK) with WPA3-AES
Answer: A
Explanation:
MPSK Local is a feature that can be used to set up 15 headless IoT devices that do not support 802.1X authentication. MPSK Local allows the switch to automatically generate and assign unique pre-shared keys for devices based on their MAC addresses, without requiring any configuration on the devices or an external authentication server. The other options are incorrect because they either require 802.1X authentication, which is not supported by the IoT devices, or WPA3 encryption, which is not supported by Aruba CX switches. References: https://www.arubanetworks.com/techdocs/AOS- CX/10.04/HTML/5200-6728/bk01-ch05.html https://www.arubanetworks.com/techdocs/AOS-CX/10.04/HTML/5200-6728/bk01- ch06.html
NEW QUESTION 11
A customer wants to provide wired security as close to the source as possible The wired security must meet the following requirements:
-allow ping from the IT management VLAN to the user VLAN
-deny ping sourcing from the user VLAN to the IT management VLAN
The customer is using Aruba CX 6300s
What is the correct way to implement these requirements?
- A. Apply an outbound ACL on the user VLAN allowing temp echo-reply traffic toward the IT management VLAN
- B. Apply an inbound ACL on the user VLAN allowing icmp echo-reply traffic toward the IT management VLAN
- C. Apply an inbound ACL on the user VLAN denying icmp echo traffic toward the IT management VLAN
- D. Apply an outbound ACL on the user VLAN denying icmp echo traffic toward the IT management VLAN
Answer: C
Explanation:
An inbound ACL is applied to traffic entering a port or VLAN. An outbound ACL is applied to traffic leaving a port or VLAN4. To deny ping sourcing from the user VLAN to the IT management VLAN, an inbound ACL on the user VLAN should be used to filter icmp echo traffic toward the IT management VLAN. Icmp echo-reply traffic is not needed to be allowed because it is already permitted by default5. References: 4
https://techhub.hpe.com/eginfolib/Aruba/OS-CX_10.04/5200-6692/GUID-9B8F6E8F-9C7A-4F0D-AE7B-9D8E6C5B6A7F.html 5 https://techhub.hpe.com/eginfolib/Aruba/OS-CX_10.04/5200-6692/GUID-0C3A9D0F-6E5B-4E1A-AF3C-8D8B2F9C1A7B.html
NEW QUESTION 12
You are doing tests in your lab and with the following equipment specifications
• AP1 has a radio that generates a 10 dBm signal
• AP2 has a radio that generates a 11 dBm signal
• AP1 has an antenna with a gain of 9 dBi
• AP2 has an antenna with a gain of 12 dBi.
• The antenna cable for AP1 has a 2 dB loss
• The antenna cable for AP2 has a 3 dB loss
What would be the calculated Equivalent Isotropic Radiated Power (EIRP) for APT?
- A. 26 dBm
- B. 30 dBm
- C. 17 dBm
- D. -12 dBm
Answer: C
Explanation:
The calculated Equivalent Isotropic Radiated Power (EIRP) for AP1 is 17 dBm.
EIRP is the measured radiated power of an antenna in a specific direction. It is equal to the input power to the antenna multiplied by the gain of the antenna. It can also take into account the losses in transmission line, connectors, and other components. The formula for EIRP is:
EIRP = P + G - L
where P is the output power of the radio, G is the gain of the antenna, and L is the loss of the cable and connectors.
For AP1, we have:
P = 10 dBm G = 9 dBi L = 2 dB
Therefore,
EIRP = 10 + 9 - 2 EIRP = 17 dBm
NEW QUESTION 13
What is the best practice for handling voice traffic with dynamic segmentation on AOS-CX switches?
- A. Switch authentication and local forwarding of the voice traffic
- B. Switch authentication and user-based tunneling of the voice traffic.
- C. Central authentication and port-based tunneling of the voice traffic.
- D. Controller authentication and port-based tunneling of all traffic
Answer: A
Explanation:
This is the best practice for handling voice traffic with dynamic segmentation on AOS-CX switches. Dynamic segmentation is a feature that allows AOS-CX switches to tunnel user traffic to a controller or another switch based on user roles and policies. For voice traffic, it is recommended to use switch authentication and local forwarding, which means the voice devices are authenticated by the switch and their traffic is forwarded locally without tunneling. This reduces latency and jitter for voice traffic and improves voice quality. The other options are incorrect because they either use central authentication or tunneling, which are not optimal for voice traffic. References: https://www.arubanetworks.com/techdocs/AOS-CX/10.04/HTML/5200-6728/bk01- ch05.html https://www.arubanetworks.com/assets/ds/DS_AOS-CX.pdf
NEW QUESTION 14
For the Aruba CX 6400 switch, what does virtual output queueing (VOQ) implement that is different from most typical campus switches?
- A. large ingress packet buffers
- B. large egress packet buffers
- C. per port ASICs
- D. VSX
Answer: A
Explanation:
The Aruba CX 6400 switch is a modular switch that supports high- performance and high-density Ethernet switching for campus and data center networks. One of the features that distinguishes the Aruba CX 6400 switch from most typical campus switches is virtual output queueing (VOQ). VOQ is a technique that implements large ingress packet buffers on each port to prevent head-of-line blocking and packet loss due to congestion2. VOQ allows each port to have multiple queues for different output ports and prioritize packets based on their destination and QoS class2. VOQ enables the Aruba CX 6400 switch to achieve high throughput and low latency for various traffic types and
scenarios. References: 2 https://www.arubanetworks.com/assets/ds/DS_CX6400Series.pdf
NEW QUESTION 15
Your manufacturing client is deploying two hundred wireless IP cameras and fifty headless scanners in their warehouse. These new devices do not support 802.1X authentication.
How can HPE Aruba enhance security for these new IP cameras in this environment?
- A. Use MPSK Local to automatically provide unique pre-shared Keys for devices.
- B. Aruba ClearPass performs the 802.1X authentication and installs a certificate.
- C. MPSK provides for each device in the WLAN to have its own unique pre-shared Key.
- D. MPSK Local will allow the cameras to share a rey and the scanners to share a different
Answer: C
Explanation:
The best option to enhance security for the new IP cameras and scanners in this environment is C. MPSK provides for each device in the WLAN to have its own unique pre- shared key.
MPSK stands for Multi Pre-Shared Key, and it is a feature that allows different devices to connect to the same SSID with different pre-shared keys. This improves the security and scalability of the network, as each device can have its own key and role without requiring 802.1X authentication or an external policy engine. MPSK can be configured either locally on the AP or centrally on Aruba Central12.
The other options are incorrect because:
✑ A. MPSK Local is a feature that allows the user to configure 24 PSKs per SSID locally on the device. These local PSKs would serve as an extension of the base MPSK functionality. However, MPSK Local is not suitable for this scenario, as it can only support up to 24 devices per SSID, while the client has 250 devices1.
✑ B. Aruba ClearPass is a network access control solution that can perform 802.1X authentication and install certificates for devices. However, this option is not feasible for this scenario, as the new IP cameras and scanners do not support 802.1X authentication3.
✑ D. MPSK Local will not allow the cameras to share a key and the scanners to share a different key. MPSK Local will assign a different key to each device, regardless of their type. Moreover, MPSK Local can only support up to 24 devices per SSID, while the client has 250 devices1.
NEW QUESTION 16
A client is connecting to 802.1X SSID that has been configured in tunnel mode with the default AP-group settings.
After receiving Access-Accept from the RADIUS server, the Aruba Gateway will send Access-Accept to the AP through which tunnel?
- A. IPsec tunnel
- B. Split tunnel
- C. GRE tunnel
- D. PAR tunnel
Answer: C
Explanation:
According to the Aruba Documentation Portal1, 802.1X is a standard for port- based network access control that uses a RADIUS server to authenticate and authorize wireless clients. 802.1X can be configured in different modes, such as bridge mode, tunnel mode, or split tunnel mode.
Option C: GRE tunnel
This is because option C shows how to configure an SSID in tunnel mode with the default AP-group settings on an Aruba switch. In tunnel mode, all client traffic from the access points is tunneled back to the controller and the controller would in turn put the client traffic onto the network2. The GRE protocol is used to encapsulate and decapsulate the traffic between the access points and the controller3.
Therefore, option C is correct.
1: https://www.arubanetworks.com/techdocs/AOS-CX/10.06/HTML/5200-7696/GUID-581D2976-694B-46C7-8497-F6B788AA05B2.html 2:
https://community.arubanetworks.com/discussion/bridge-and-tunnel-mode 3: https://www.twingate.com/blog/ipsec-tunnel-mode
NEW QUESTION 17
DRAG DROP
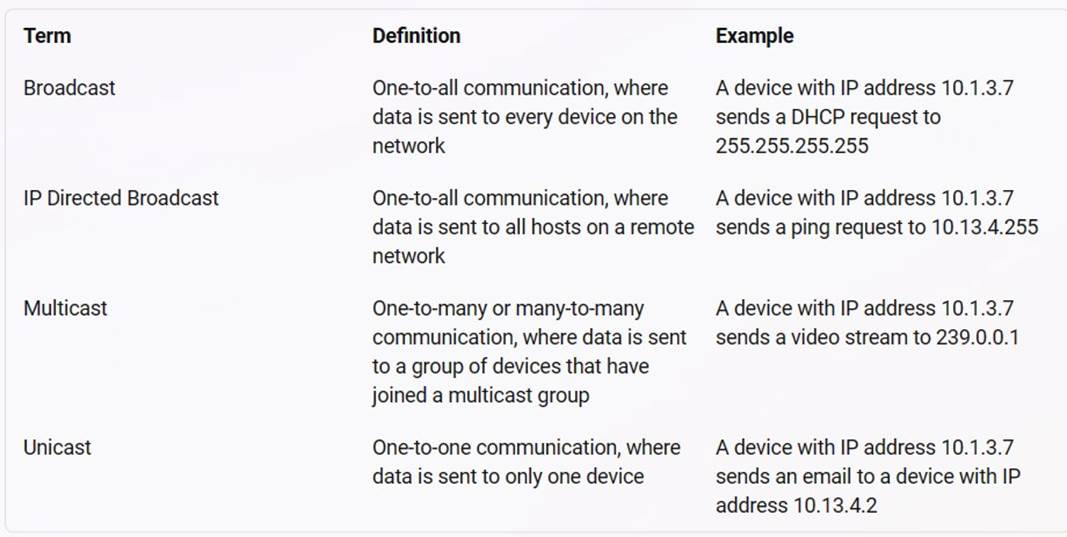
Match the terms below to their characteristics (Options may be used more than once or not at all.)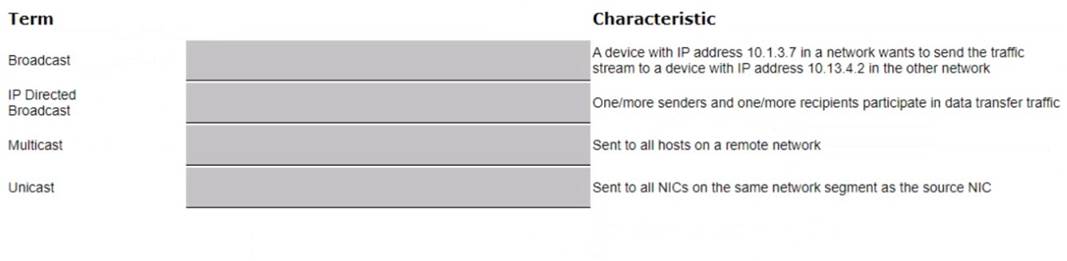
Solution:
a) A device with IP address 10.1.3.7 in a network wants to send the traffic stream to a device with IP address 10.13.4.2 in the other network -> Unicast
b) One/more senders and one/more recipients participate in data transfer traffic ->
Multicast
c) Sent to all hosts on a remote network -> IP Directed Broadcast
d) Sent to all NICs on the same network segment as the source NIC -> Broadcast
References: 1 https://www.thestudygenius.com/unicast-broadcast-multicast/
The terms broadcast, IP directed broadcast, multicast, and unicast are different types of communication or data transmission over a network. They differ in how many devices are involved in the communication and how they address the messages. The following table summarizes the characteristics of each term1:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 18
you need to have different routing-table requirements With Aruba CX 6300 VSF configuration.
Assuming the correct layer-2 VLAN already exists, how would you create a new SVI for a separate routing table?
- A. create a new VLAN, and attach the VRF to it.
- B. Create a new routing table, and attach VLANS to it
- C. Create a new SVI and use attach command.
- D. Create a new VLA
- E. and attach the routing table to it
Answer: C
Explanation:
The correct answer is C. Create a new SVI and use attach command.
To create a new SVI for a separate routing table, you need to use the attach command to associate the SVI with a VRF (Virtual Routing and Forwarding) instance. A VRF is a logical entity that allows multiple routing tables to coexist on the same switch. Each VRF has its own set of interfaces, routing protocols, and routes that are isolated from other VRFs. According to the AOS-CX Virtual Switching Framework (VSF) Guide1, one of the steps to configure VRF-aware VSF is:
✑ Configure the VRFs on each member switch and assign the SVIs to the respective
VRFs using the attach command. For example: switch(config)# vrf red
switch(config-vrf)# exit switch(config)# interface vlan 10
switch(config-if-vlan)# ip address 10.1.1.1/24 switch(config-if-vlan)# attach vrf red
The above commands create a VRF named red and assign VLAN 10 SVI to it. The SVI has an IP address of 10.1.1.1/24.
The other options are incorrect because:
✑ A. You cannot attach a VRF to a VLAN directly. You need to create an SVI for the VLAN and then attach the VRF to the SVI.
✑ B. You cannot create a new routing table manually. You need to create a VRF and then use routing protocols or static routes to populate the routing table for the VRF.
✑ D. You cannot attach a routing table to a VLAN directly. You need to create an SVI for the VLAN and then attach a VRF that has a routing table associated with it.
NEW QUESTION 19
......
Recommend!! Get the Full HPE7-A01 dumps in VCE and PDF From Dumps-hub.com, Welcome to Download: https://www.dumps-hub.com/HPE7-A01-dumps.html (New 119 Q&As Version)
