Testking offers free demo for PCCET exam. "Palo Alto Networks Certified Cybersecurity Entry-level Technician", also known as PCCET exam, is a Paloalto-Networks Certification. This set of posts, Passing the Paloalto-Networks PCCET exam, will help you answer those questions. The PCCET Questions & Answers covers all the knowledge points of the real exam. 100% real Paloalto-Networks PCCET exams and revised by experts!
Free demo questions for Paloalto-Networks PCCET Exam Dumps Below:
NEW QUESTION 1
DRAG DROP
Match each description to a Security Operating Platform key capability.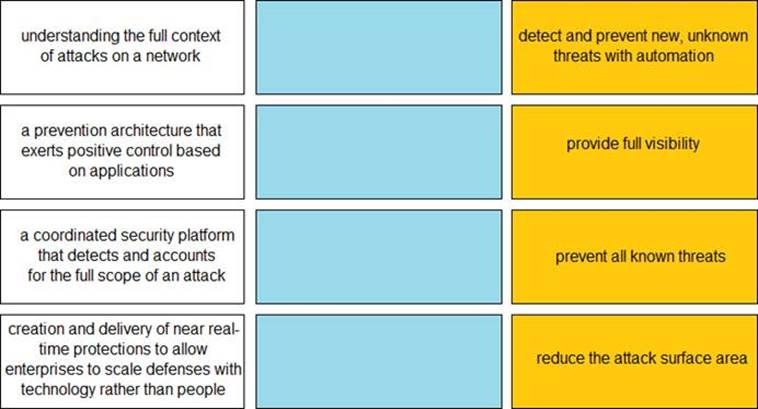
Solution:

Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 2
How does DevSecOps improve the Continuous Integration/Continuous Deployment (CI/CD) pipeline?
- A. DevSecOps improves pipeline security by assigning the security team as the lead team for continuous deployment
- B. DevSecOps ensures the pipeline has horizontal intersections for application code deployment
- C. DevSecOps unites the Security team with the Development and Operations teams to integrate security into the CI/CD pipeline
- D. DevSecOps does security checking after the application code has been processed through the CI/CDpipeline
Answer: C
NEW QUESTION 3
What does Palo Alto Networks Cortex XDR do first when an endpoint is asked to run an executable?
- A. run a static analysis
- B. check its execution policy
- C. send the executable to WildFire
- D. run a dynamic analysis
Answer: B
NEW QUESTION 4
In addition to local analysis, what can send unknown files to WildFire for discovery and deeper analysis to rapidly detect potentially unknown malware?
- A. Cortex XDR
- B. AutoFocus
- C. MineMild
- D. Cortex XSOAR
Answer: A
NEW QUESTION 5
Which model would a customer choose if they want full control over the operating system(s) running on their cloud computing platform?
- A. SaaS
- B. DaaS
- C. PaaS
- D. IaaS
Answer: D
NEW QUESTION 6
Which attacker profile uses the internet to recruit members to an ideology, to train them, and to spread fear and include panic?
- A. Cybercriminals
- B. state-affiliated groups
- C. hacktivists
- D. cyberterrorists
Answer: D
NEW QUESTION 7
In the attached network diagram, which device is the switch?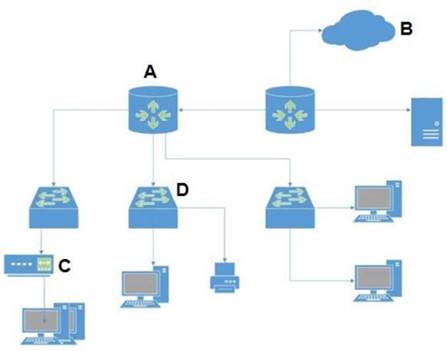
- A. A
- B. B
- C. C
- D. D
Answer: D
NEW QUESTION 8
Which Palo Alto subscription service identifies unknown malware, zero-day exploits, and advanced persistent threats (APTs) through static and dynamic analysis in a scalable, virtual environment?
- A. DNS Security
- B. URL Filtering
- C. WildFire
- D. Threat Prevention
Answer: C
NEW QUESTION 9
Which option is an example of a North-South traffic flow?
- A. Lateral movement within a cloud or data center
- B. An internal three-tier application
- C. Client-server interactions that cross the edge perimeter
- D. Traffic between an internal server and internal user
Answer: C
NEW QUESTION 10
In addition to integrating the network and endpoint components, what other component does Cortex integrate to speed up IoC investigations?
- A. Computer
- B. Switch
- C. Infrastructure
- D. Cloud
Answer: C
NEW QUESTION 11
How does Prisma SaaS provide protection for Sanctioned SaaS applications?
- A. Prisma SaaS connects to an organizations internal print and file sharing services to provide protection and sharing visibility
- B. Prisma SaaS does not provide protection for Sanctioned SaaS applications because they are secure
- C. Prisma access uses Uniform Resource Locator (URL) Web categorization to provide protection and sharing visibility
- D. Prisma SaaS connects directly to sanctioned external service providers SaaS application service to provide protection and sharing visibility
Answer: D
NEW QUESTION 12
Which pillar of Prisma Cloud application security addresses ensuring that your cloud resources and SaaS applications are correctly configured?
- A. visibility, governance, and compliance
- B. network protection
- C. dynamic computing
- D. compute security
Answer: A
NEW QUESTION 13
What is the key to “taking down” a botnet?
- A. prevent bots from communicating with the C2
- B. install openvas software on endpoints
- C. use LDAP as a directory service
- D. block Docker engine software on endpoints
Answer: A
NEW QUESTION 14
Which aspect of a SaaS application requires compliance with local organizational security policies?
- A. Types of physical storage media used
- B. Data-at-rest encryption standards
- C. Acceptable use of the SaaS application
- D. Vulnerability scanning and management
Answer: C
NEW QUESTION 15
Which statement describes DevOps?
- A. DevOps is its own separate team
- B. DevOps is a set of tools that assists the Development and Operations teams throughout the software delivery process
- C. DevOps is a combination of the Development and Operations teams
- D. DevOps is a culture that unites the Development and Operations teams throughout the software delivery process
Answer: B
NEW QUESTION 16
Which item accurately describes a security weakness that is caused by implementing a “ports first” data security solution in a traditional data center?
- A. You may have to use port numbers greater than 1024 for your business-critical applications.
- B. You may have to open up multiple ports and these ports could also be used to gain unauthorized entry into your datacenter.
- C. You may not be able to assign the correct port to your business-critical applications.
- D. You may not be able to open up enough ports for your business-critical applications which will increase the attack surface area.
Answer: B
NEW QUESTION 17
Anthem server breaches disclosed Personally Identifiable Information (PII) from a number of its servers. The infiltration by hackers was attributed to which type of vulnerability?
- A. an intranet-accessed contractor’s system that was compromised
- B. exploitation of an unpatched security vulnerability
- C. access by using a third-party vendor’s password
- D. a phishing scheme that captured a database administrator’s password
Answer: D
NEW QUESTION 18
Which subnet does the host 192.168.19.36/27 belong?
- A. 192.168.19.0
- B. 192.168.19.16
- C. 192.168.19.64
- D. 192.168.19.32
Answer: D
NEW QUESTION 19
......
P.S. Easily pass PCCET Exam with 75 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy PCCET Dumps: https://www.2passeasy.com/dumps/PCCET/ (75 New Questions)
