Master the PT0-001 Exam Questions and Answers content and be ready for exam day success quickly with this PT0-001 Dumps. We guarantee it!We make it a reality and give you real PT0-001 Dumps in our CompTIA PT0-001 braindumps. Latest 100% VALID PT0-001 Exam Dumps at below page. You can use our CompTIA PT0-001 braindumps and pass your exam.
Online CompTIA PT0-001 free dumps demo Below:
NEW QUESTION 1
A penetration tester successfully explogts a Windows host and dumps the hashes Which of the following hashes can the penetration tester use to perform a pass-the-hash attack?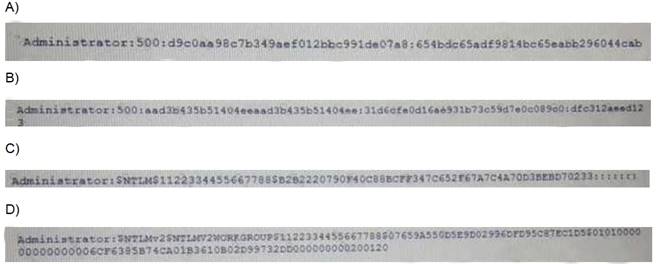
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 2
A penetration tester locates a few unquoted service paths during an engagement. Which of the following can the tester attempt to do with these?
- A. Attempt to crack the service account passwords.
- B. Attempt DLL hijacking attacks.
- C. Attempt to locate weak file and folder permissions.
- D. Attempt privilege escalation attack
Answer: D
NEW QUESTION 3
A penetration tester ran the following Nmap scan on a computer nmap -sV 192.168.1.5
The organization said it had disabled Telnet from its environment However, the results of the Nmap scan show port 22 as closed and port 23 as open to SSH Which of the following is the BEST explanation for what happened?
- A. The organization failed to disable Telnet.
- B. Nmap results contain a false positive for port 23.
- C. Port 22 was filtered.
- D. The service is running on a non-standard por
Answer: A
NEW QUESTION 4
A penetration tester wants to target NETBIOS name service. Which of the following is the most likely command to explogt the NETBIOS name service?
- A. arPspoof
- B. nmap
- C. responder
- D. burpsuite
Answer: C
NEW QUESTION 5
While prioritizing findings and recommendations for an executive summary, which of the following considerations would De MOST valuable to the client?
- A. Levels of difficulty to explogt identified vulnerabilities
- B. Time taken to accomplish each step
- C. Risk tolerance of the organization
- D. Availability of patches and remediations
Answer: C
NEW QUESTION 6
An attacker uses SET to make a copy of a company's cloud-hosted web mail portal and sends an email m to obtain the CEO s login credentials Which of the following types of attacks is this an example of?
- A. Elicitation attack
- B. Impersonation attack
- C. Spear phishing attack
- D. Drive-by download attack
Answer: B
NEW QUESTION 7
A client requests that a penetration tester emulate a help desk technician who was recently laid off. Which of the following BEST describes the abilities of the threat actor?
- A. Advanced persistent threat
- B. Script kiddie
- C. Hacktivist
- D. Organized crime
Answer: A
NEW QUESTION 8
A recently concluded penetration test revealed that a legacy web application is vulnerable lo SQL injection Research indicates that completely remediating the vulnerability would require an architectural change, and the stakeholders are not m a position to risk the availability of the application Under such circumstances, which of the following controls are low-effort, short-term solutions to minimize the SQL injection risk? (Select TWO).
- A. Identify and eliminate inline SQL statements from the code.
- B. Identify and eliminate dynamic SQL from stored procedures.
- C. Identify and sanitize all user inputs.
- D. Use a whitelist approach for SQL statements.
- E. Use a blacklist approach for SQL statements.
- F. Identify the source of malicious input and block the IP addres
Answer: DE
NEW QUESTION 9
A penetration testet is attempting to capture a handshake between a client and an access point by monitoring a WPA2-PSK secured wireless network The (ester is monitoring the correct channel tor the identified network but has been unsuccessful in capturing a handshake Given this scenario, which of the following attacks would BEST assist the tester in obtaining this handshake?
- A. Karma attack
- B. Deauthentication attack
- C. Fragmentation attack
- D. SSID broadcast flood
Answer: B
NEW QUESTION 10
A security analyst has uncovered a suspicious request in the logs for a web application. Given the following URL: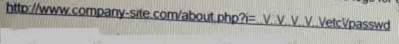
- A. Directory traversal
- B. Cross-site scripting
- C. Remote file inclusion
- D. User enumeration
Answer: D
NEW QUESTION 11
The results of a basic compliance scan show a subset of assets on a network. This data differs from what is shown on the network architecture diagram, which was supplied at the beginning of the test. Which of the following are the MOST likely causes for this difference? (Select TWO)
- A. Storage access
- B. Limited network access
- C. Misconfigured DHCP server
- D. Incorrect credentials
- E. Network access controls
Answer: A
NEW QUESTION 12
Click the exhibit button.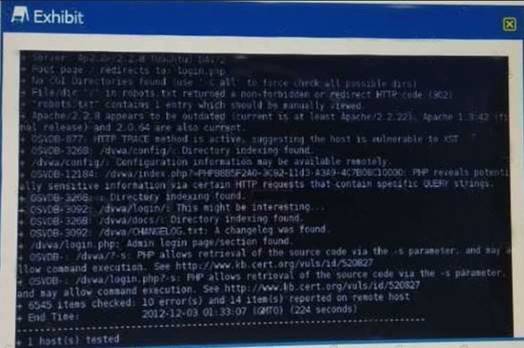
Given the Nikto vulnerability scan output shown in the exhibit, which of the following explogtation techniques might be used to explogt the target system? (Select TWO)
- A. Arbitrary code execution
- B. Session hijacking
- C. SQL injection
- D. Login credential brute-forcing
- E. Cross-site request forgery
Answer: CE
NEW QUESTION 13
A constant wants to scan all the TCP Pots on an identified device. Which of the following Nmap switches will complete this task?
- A. -p-
- B. -p ALX,
- C. -p 1-65534
- D. -port 1-65534
Answer: A
NEW QUESTION 14
A penetration tester has been asked to conduct OS fingerprinting with Nmap using a companyprovide text file that contain a list of IP addresses.
Which of the following are needed to conduct this scan? (Select TWO).
- A. -O
- B. _iL
- C. _sV
- D. -sS
- E. -oN
- F. -oX
Answer: EF
NEW QUESTION 15
A client has voiced concern about the number of companies being branched by remote attackers, who are looking for trade secrets. Which of following BEST describes the types of adversaries this would identify?
- A. Script kiddies
- B. APT actors
- C. Insider threats
- D. Hacktrvist groups
Answer: B
NEW QUESTION 16
After successfully capturing administrator credentials to a remote Windows machine, a penetration tester attempts to access the system using PSExec but is denied permission. Which of the following shares must be accessible for a successful PSExec connection?
- A. IPCS and C$
- B. C$ and ADMINS
- C. SERVICES and ADMINS
- D. ADMINS and IPCS
Answer: C
Recommend!! Get the Full PT0-001 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/PT0-001-dumps.html (New 131 Q&As Version)
