Your success in CompTIA PT0-001 is our sole target and we develop all our PT0-001 braindumps in a way that facilitates the attainment of this target. Not only is our PT0-001 study material the best you can find, it is also the most detailed and the most updated. PT0-001 Practice Exams for CompTIA PT0-001 are written to the highest standards of technical accuracy.
Free demo questions for CompTIA PT0-001 Exam Dumps Below:
NEW QUESTION 1
A security consultant is trying to attack a device with a previous identified user account.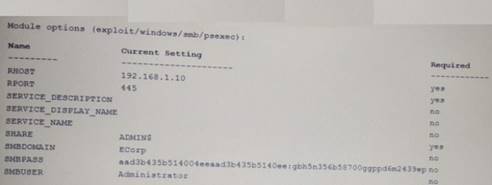
Which of the following types of attacks is being executed?
- A. Credential dump attack
- B. DLL injection attack
- C. Reverse shell attack
- D. Pass the hash attack
Answer: D
NEW QUESTION 2
A penetration tester is preparing to conduct API testing Which of the following would be MOST helpful in preparing for this engagement?
- A. NiktO
- B. WAR
- C. W3AF
- D. Swagger
Answer: A
NEW QUESTION 3
A penetration tester ran the following Nmap scan on a computer nmap -sV 192.168.1.5
The organization said it had disabled Telnet from its environment However, the results of the Nmap scan show port 22 as closed and port 23 as open to SSH Which of the following is the BEST explanation for what happened?
- A. The organization failed to disable Telnet.
- B. Nmap results contain a false positive for port 23.
- C. Port 22 was filtered.
- D. The service is running on a non-standard por
Answer: A
NEW QUESTION 4
While engaging clients for a penetration test from highly regulated industries, which of the following is usually the MOST important to the clients from a business perspective?
- A. Letter of engagement and attestation of findings
- B. NDA and MSA
- C. SOW and final report
- D. Risk summary and executive summary
Answer: D
NEW QUESTION 5
A penetration tester locates a few unquoted service paths during an engagement. Which of the following can the tester attempt to do with these?
- A. Attempt to crack the service account passwords.
- B. Attempt DLL hijacking attacks.
- C. Attempt to locate weak file and folder permissions.
- D. Attempt privilege escalation attack
Answer: D
NEW QUESTION 6
A security analyst has uncovered a suspicious request in the logs for a web application. Given the following URL: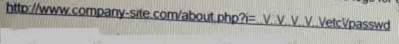
- A. Directory traversal
- B. Cross-site scripting
- C. Remote file inclusion
- D. User enumeration
Answer: D
NEW QUESTION 7
Joe, a penetration tester, is asked to assess a company's physical security by gaining access to its corporate office. Joe ism looking for a method that will enable him to enter the building during business hours or when there are no employee on-site. Which of the following would be MOST effective in accomplishing this?
- A. Badge cloning
- B. Lock picking
- C. Tailgating
- D. Piggybacking
Answer: A
NEW QUESTION 8
A penetration tester is performing a remote scan to determine if the server farm is compliant with the company's software baseline . Which of the following should the penetration tester perform to verify compliance with the baseline?
- A. Discovery scan
- B. Stealth scan
- C. Full scan
- D. Credentialed scan
Answer: A
NEW QUESTION 9
Click the exhibit button.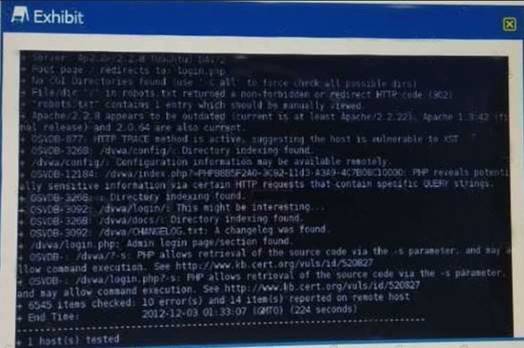
Given the Nikto vulnerability scan output shown in the exhibit, which of the following explogtation techniques might be used to explogt the target system? (Select TWO)
- A. Arbitrary code execution
- B. Session hijacking
- C. SQL injection
- D. Login credential brute-forcing
- E. Cross-site request forgery
Answer: CE
NEW QUESTION 10
A penetration tester successfully explogts a DM2 server that appears to be listening on an outbound port The penetration tester wishes to forward that traffic back to a device Which of the following are the BEST tools to use few this purpose? (Select TWO)
- A. Tcpdump
- B. Nmap
- C. Wiresrtark
- D. SSH
- E. Netcat
- F. Cain and Abel
Answer: CD
NEW QUESTION 11
A penetration tester has a full shell to a domain controller and wants to discover any user account that has not authenticated to the domain in 21 days. Which of the following commands would BEST accomplish this?
- A. dsrm -users "DN=compony.com; OU=hq CN=usera"
- B. dsuser -name -account -limit 3
- C. dsquery uaer -inactive 3
- D. dsquery -o -rein -limit 21
Answer: B
NEW QUESTION 12
Which of the following types of physical security attacks does a mantrap mitigate-?
- A. Lock picking
- B. Impersonation
- C. Shoulder surfing
- D. Tailgating
Answer: D
NEW QUESTION 13
If a security consultant comes across a password hash that resembles the following b117 525b3454 7Oc29ca3dBaeOb556ba8
Which of the following formats is the correct hash type?
- A. Kerberos
- B. NetNTLMvl
- C. NTLM
- D. SHA-1
Answer: C
NEW QUESTION 14
DRAG DROP
During a penetration test, you gain access to a system with a limited user interface. This machine appears to have access to an isolated network that you would like to port scan. INSTRUCTIONS:
Analyze the code segments to determine which sections are needed to complete a port scanning script.
Drag the appropriate elements into the correct locations to complete the script.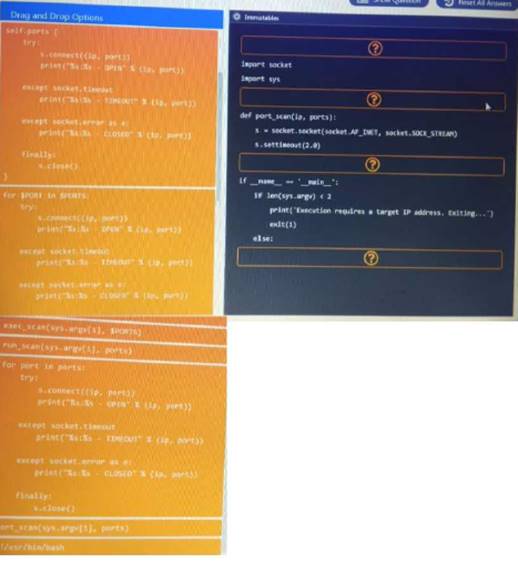
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 15
Which of the following is the reason why a penetration tester would run the chkconfig --del servicename command at the end of an engagement?
- A. To remove the persistence
- B. To enable penitence
- C. To report persistence
- D. To check for persistence
Answer: A
NEW QUESTION 16
A penetration tester successfully explogts a Windows host and dumps the hashes Which of the following hashes can the penetration tester use to perform a pass-the-hash attack?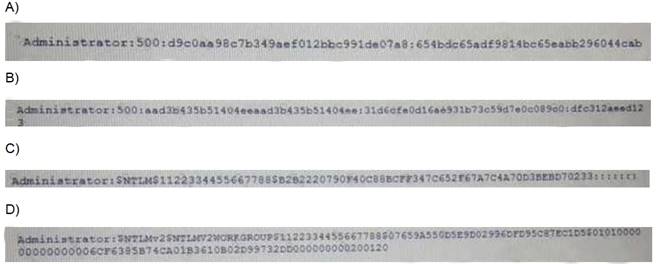
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 17
A penetration testet is attempting to capture a handshake between a client and an access point by monitoring a WPA2-PSK secured wireless network The (ester is monitoring the correct channel tor the identified network but has been unsuccessful in capturing a handshake Given this scenario, which of the following attacks would BEST assist the tester in obtaining this handshake?
- A. Karma attack
- B. Deauthentication attack
- C. Fragmentation attack
- D. SSID broadcast flood
Answer: B
NEW QUESTION 18
During an internal penetration test, several multicast and broadcast name resolution requests are observed traversing the network. Which of the following tools could be used to impersonate network resources and collect authentication requests?
- A. Ettercap
- B. Tcpdump
- C. Responder
- D. Medusa
Answer: D
NEW QUESTION 19
......
P.S. 2passeasy now are offering 100% pass ensure PT0-001 dumps! All PT0-001 exam questions have been updated with correct answers: https://www.2passeasy.com/dumps/PT0-001/ (248 New Questions)
