We provide real SC-300 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Microsoft SC-300 Exam quickly & easily. The SC-300 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Microsoft SC-300 dumps pdf and vce product and material, you can easily pass the SC-300 exam.
Free demo questions for Microsoft SC-300 Exam Dumps Below:
NEW QUESTION 1
You have a Microsoft 365 tenant.
Sometimes, users use external, third-party applications that require limited access to the Microsoft 365 data of the respective user. The users register the applications in Azure Active Directory (Azure AD).
You need to receive an alert if a registered application gains read and write access to the users’ email. What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.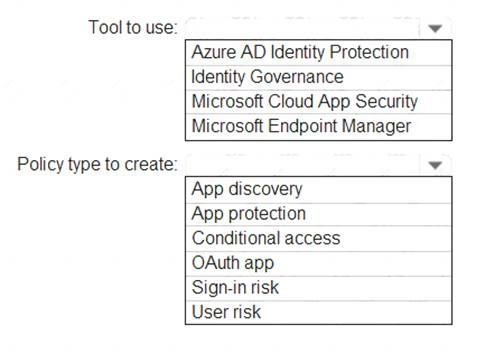
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference:
https://docs.microsoft.com/en-us/cloud-app-security/app-permission-policy
NEW QUESTION 2
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.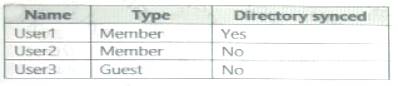
For which users can you configure the Job title property and the Usage location property in Azure AD? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.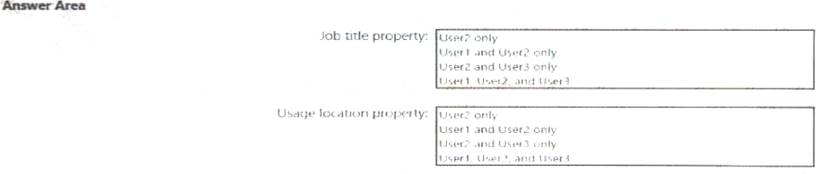
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 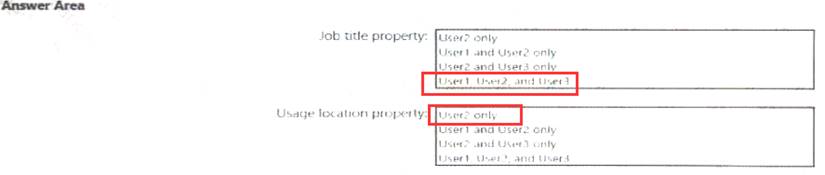
NEW QUESTION 3
Your network contains an on-premises Active Directory domain that sync to an Azure Active Directory (Azure AD) tenant. The tenant contains the shown in the following table.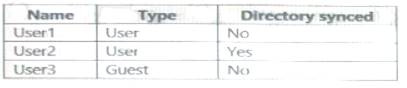
All the users work remotely.
Azure AD Connect is configured in Azure as shown in the following exhibit.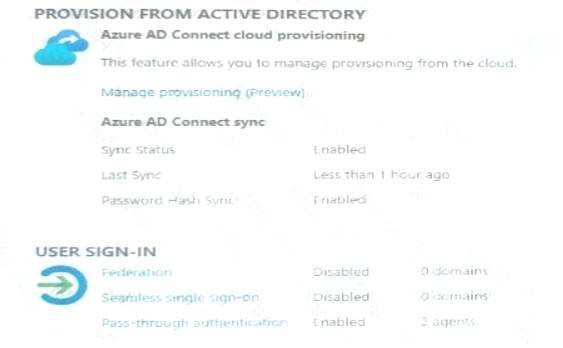
Connectivity from the on-premises domain to the internet is lost. Which user can sign in to Azure AD?
- A. User1 only
- B. User1 and User 3 only
- C. User1, and User2 only
- D. User1, User2, and User3
Answer: A
NEW QUESTION 4
You have a Microsoft 365 tenant.
The Azure Active Directory (Azure AD) tenant syncs to an on-premises Active Directory domain. The domain contains the servers shown in the following table.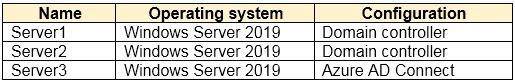
The domain controllers are prevented from communicating to the internet. You implement Azure AD Password Protection on Server1 and Server2. You deploy a new server named Server4 that runs Windows Server 2019.
You need to ensure that Azure AD Password Protection will continue to work if a single server fails. What should you implement on Server4?
- A. Azure AD Connect
- B. Azure AD Application Proxy
- C. Password Change Notification Service (PCNS)
- D. the Azure AD Password Protection proxy service
Answer: D
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-password-ban-bad-on-premisesdep
NEW QUESTION 5
You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs.
Yon receive more than 100 email alerts each day for tailed Azure Al) user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure monitor, you create a data collection rule.
Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 6
You have a Microsoft 36S tenant.
You create a named location named HighRiskCountries that contains a list of high-risk countries.
You need to limit the amount of time a user can stay authenticated when connecting from a high-risk country. What should you configure in a conditional access policy? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.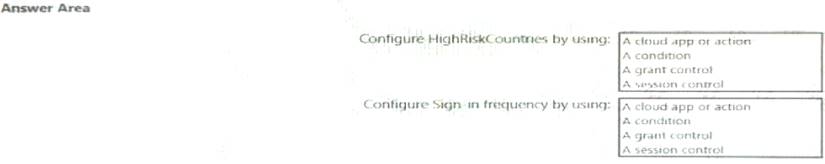
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 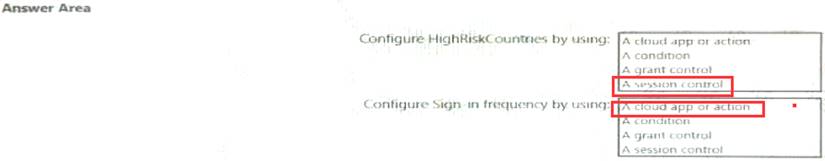
NEW QUESTION 7
You have a Microsoft 365 tenant.
All users have computers that run Windows 10. Most computers are company-owned and joined to Azure Active Directory (Azure AD). Some computers are user-owned and are only registered in Azure AD.
You need to prevent users who connect to Microsoft SharePoint Online on their user-owned computer from downloading or syncing files. Other users mustNOTbe restricted.
Which policy type should you create?
- A. a Microsoft Cloud App Security activity policy that has Microsoft Office 365 governance actions configured
- B. an Azure AD conditional access policy that has session controls configured
- C. an Azure AD conditional access policy that has client apps conditions configured
- D. a Microsoft Cloud App Security app discovery policy that has governance actions configured
Answer: B
Explanation:
Reference:
https://docs.microsoft.com/en-us/cloud-app-security/proxy-intro-aad
NEW QUESTION 8
You have an Azure Active Directory (Azure AD) tenant named contoso.com.
You plan to bulk invite Azure AD business-to-business (B2B) collaboration users.
Which two parameters must you include when you create the bulk invite? Each correct answer presents part of the solution
NOTE:Each correct selection is worth one point.
- A. email address
- B. redirection URL
- C. username
- D. shared key
- E. password
Answer: AB
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/external-identities/tutorial-bulk-invite
NEW QUESTION 9
You configure Azure Active Directory (Azure AD) Password Protection as shown in the exhibit. (Click theExhibittab.)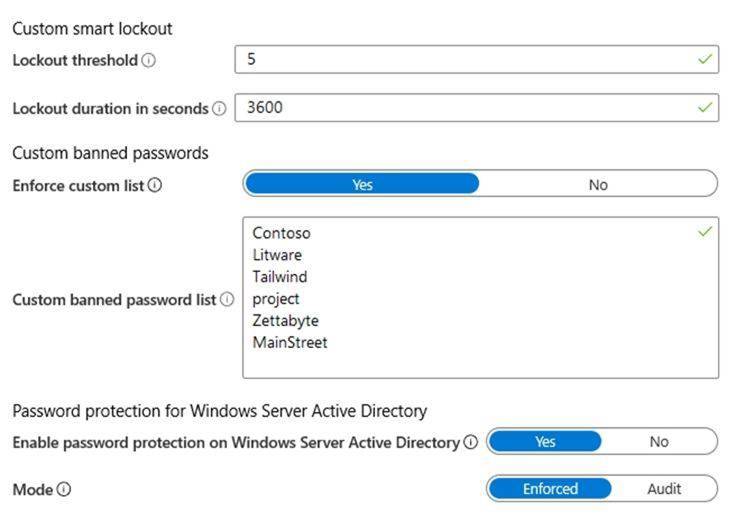
You are evaluating the following passwords:  Pr0jectlitw@re
Pr0jectlitw@re T@ilw1nd
T@ilw1nd  C0nt0s0
C0nt0s0
Which passwords will be blocked?
- A. Pr0jectlitw@re and T@ilw1nd only
- B. C0nt0s0 only
- C. C0nt0s0, Pr0jectlitw@re, and T@ilw1nd
- D. C0nt0s0 and T@ilw1nd only
- E. C0nt0s0 and Pr0jectlitw@re only
Answer: C
Explanation:
Reference:
https://blog.enablingtechcorp.com/azure-ad-password-protection-password-evaluation
NEW QUESTION 10
You have an Azure Active Directory (Azure AD) tenant that contains a user named SecAdmin1. SecAdmin1 is assigned the Security administrator role.
SecAdmin1 reports that she cannot reset passwords from the Azure AD Identity Protection portal.
You need to ensure that SecAdmin1 can manage passwords and invalidate sessions on behalf of nonadministrative
users. The solution must use the principle of least privilege. Which role should you assign to SecAdmin1?
- A. Authentication administrator
- B. Helpdesk administrator
- C. Privileged authentication administrator
- D. Security operator
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/roles/permissions-reference
NEW QUESTION 11
You have a Microsoft 365 tenant.
In Azure Active Directory (Azure AD), you configure the terms of use.
You need to ensure that only users who accept the terms of use can access the resources in the tenant. Other users must be denied access.
What should you configure?
- A. an access policy in Microsoft Cloud App Security.
- B. Terms and conditions in Microsoft Endpoint Manager.
- C. a conditional access policy in Azure AD
- D. a compliance policy in Microsoft Endpoint Manager
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/terms-of-use
NEW QUESTION 12
You need to implement password restrictions to meet the authentication requirements. You install the Azure AD password Protection DC agent on DC1.
What should you do next? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.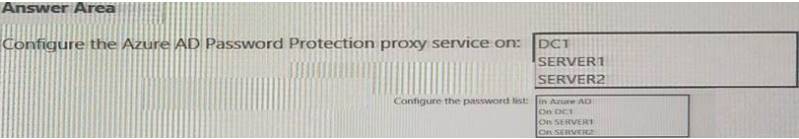
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 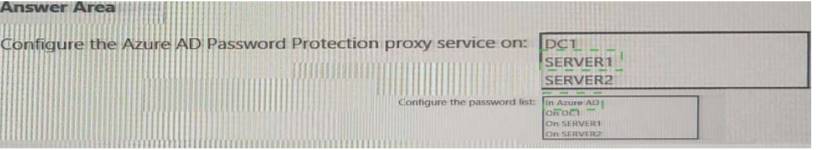
NEW QUESTION 13
Your company has a Microsoft 365 tenant.
The company has a call center that contains 300 users. In the call center, the users share desktop computers and might use a different computer every day. The call center computers areNOTconfigured for biometric identification.
The users are prohibited from having a mobile phone in the call center.
You need to require multi-factor authentication (MFA) for the call center users when they access Microsoft 365
services.
What should you include in the solution?
- A. a named network location
- B. the Microsoft Authenticator app
- C. Windows Hello for Business authentication
- D. FIDO2 tokens
Answer: D
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-authentication-passwordless
NEW QUESTION 14
You have a Microsoft 365 tenant.
All users must use the Microsoft Authenticator app for multi-factor authentication (MFA) when accessing Microsoft 365 services.
Some users report that they received an MFA prompt on their Microsoft Authenticator app without initiating a sign-in request.
You need to block the users automatically when they report an MFA request that they did not Initiate. Solution: From the Azure portal, you configure the Block/unblock users settings for multi-factor
authentication (MFA).
Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 15
HOTSPOT
You have an Azure Active Directory (Azure AD) tenant that contains Azure AD Privileged Identity Management (PIM) role settings for the User administrator role as shown in the following exhibit.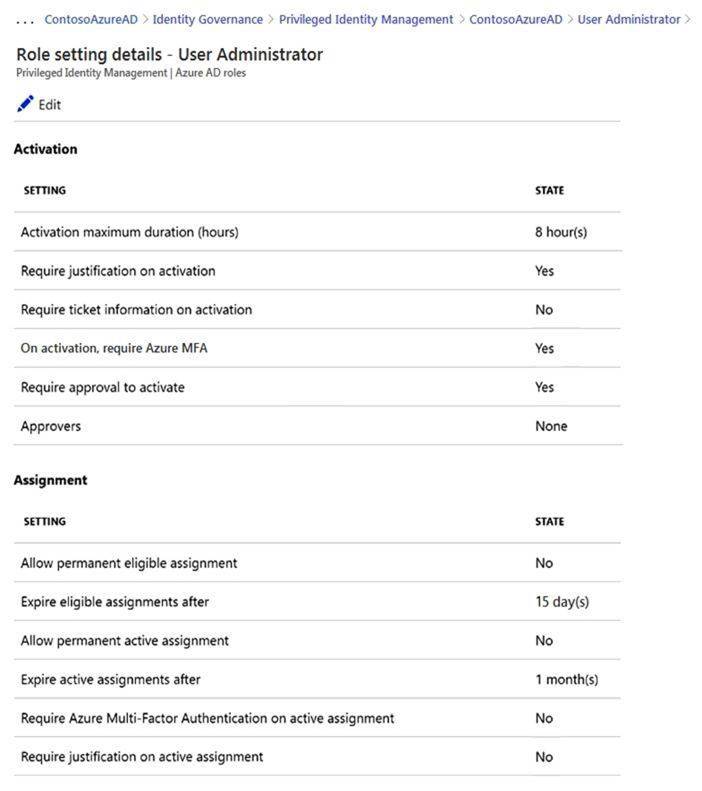
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE:Each correct selection is worth one point.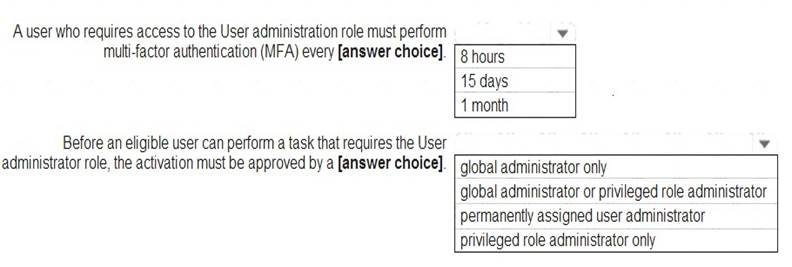
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-configure https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-deployment-plan
NEW QUESTION 16
You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs.
Yon receive more than 100 email alerts each day for tailed Azure Al) user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure AD, you create an assignment for the Insights at administrator role. Does this meet the goal?
- A. Yes
- B. No
Answer: B
NEW QUESTION 17
You have an Azure Active Directory (Azure AD) tenant named contoso.com.
All users who run applications registered in Azure AD are subject to conditional access policies. You need to prevent the users from using legacy authentication.
What should you include in the conditional access policies to filter out legacy authentication attempts?
- A. a cloud apps or actions condition
- B. a user risk condition
- C. a client apps condition
- D. a sign-in risk condition
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/block-legacy-authentication
NEW QUESTION 18
You have an on-premises datacenter that contains the hosts shown in the following table.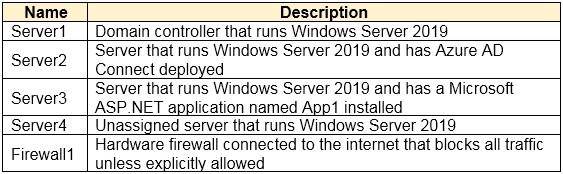
You have an Azure Active Directory (Azure AD) tenant that syncs to the Active Directory forest. Multi-factor authentication (MFA) is enforced for Azure AD.
You need to ensure that you can publish App1 to Azure AD users.
What should you configure on Server and Firewall1? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.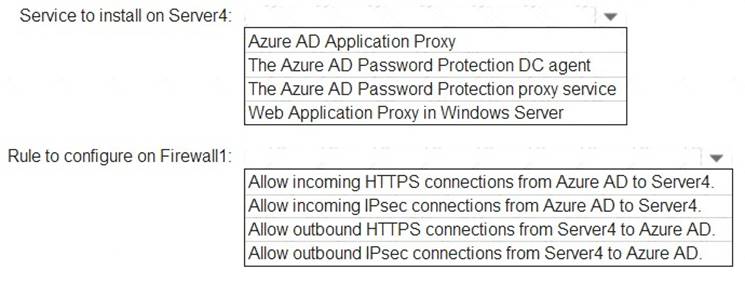
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/application-proxy
NEW QUESTION 19
You have a Microsoft 365 tenant.
You need to identify users who have leaked credentials. The solution must meet the following requirements.
• Identity sign-Ins by users who ate suspected of having leaked credentials.
• Rag the sign-ins as a high risk event.
• Immediately enforce a control to mitigate the risk, while still allowing the user to access applications. What should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.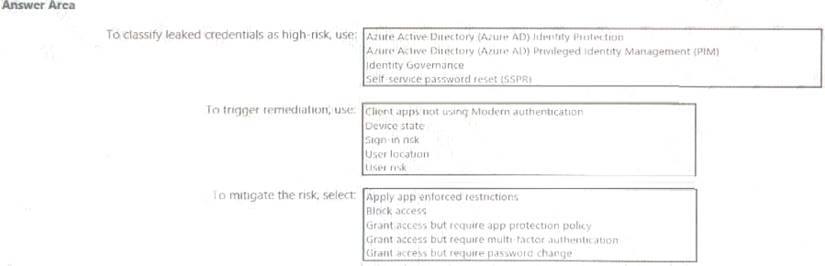
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 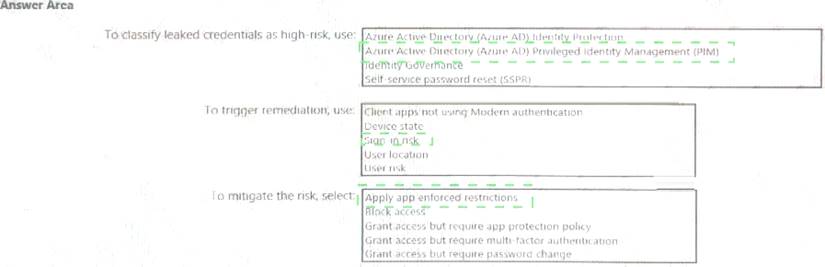
NEW QUESTION 20
You have an Azure Active Directory (Azure AD) tenant named conto.so.com that has Azure AD Identity Protection enabled. You need to Implement a sign-in risk remediation policy without blocking access.
What should you do first?
- A. Configure access reviews in Azure AD.
- B. Enforce Azure AD Password Protection.
- C. implement multi-factor authentication (MFA) for all users.
- D. Configure self-service password reset (SSPR) for all users.
Answer: D
NEW QUESTION 21
You have a Microsoft 365 tenant.
The Azure Active Directory (Azure AD) tenant syncs to an on-premises Active Directory domain.
Users connect to the internet by using a hardware firewall at your company. The users authenticate to the firewall by using their Active Directory credentials.
You plan to manage access to external applications by using Azure AD.
You need to use the firewall logs to create a list of unmanaged external applications and the users who access them.
What should you use to gather the information?
- A. Application Insights in Azure Monitor
- B. access reviews in Azure AD
- C. Cloud App Discovery in Microsoft Cloud App Security
- D. enterprise applications in Azure AD
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/cloud-app-security/create-snapshot-cloud-discovery-reports#using-traffic-logs
NEW QUESTION 22
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure Active Directory (Azure AD) tenant that syncs to an Active Directory forest.
You discover that when a user account is disabled in Active Directory, the disabled user can still authenticate to Azure AD for up to 30 minutes.
You need to ensure that when a user account is disabled in Active Directory, the user account is immediately prevented from authenticating to Azure AD.
Solution: You configure password writeback. Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/choose-ad-authn
NEW QUESTION 23
You have a Microsoft 365 tenant.
All users have mobile phones and laptops.
The users frequently work from remote locations that do not have Wi-Fi access or mobile phone connectivity. While working from the remote locations, the users connect their laptop to a wired network that has internet access.
You plan to implement multi-factor authentication (MFA).
Which MFA authentication method can the users use from the remote location?
- A. a verification code from the Microsoft Authenticator app
- B. security questions
- C. voice
- D. SMS
Answer: B
NEW QUESTION 24
You have an Azure Active Directory (Azure AD) tenant.
You configure self-service password reset (SSPR) by using the following settings:
• Require users to register when signing in: Yes
• Number of methods required to reset: 1
What is a valid authentication method available to users?
- A. home prions
- B. mobile app notification
- C. a mobile app code
- D. an email to an address in your organization
Answer: A
NEW QUESTION 25
You have a Microsoft 365 tenant.
You need to ensure that you tan view Azure Active Directory (Azure AD) audit log information by using Azure Monitor.
What should you do first?
- A. Run the Get-AzureADAuditDirectoryLogs cmdlet.
- B. Create an Azure AD workbook.
- C. Run the Set-AzureADTenantDetail cmdlet.
- D. Modify the Diagnostics settings for Azure AD.
Answer: A
NEW QUESTION 26
......
P.S. Easily pass SC-300 Exam with 52 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy SC-300 Dumps: https://www.2passeasy.com/dumps/SC-300/ (52 New Questions)
