It is impossible to pass Cisco 200-301 exam without any help in the short term. Come to Exambible soon and find the most advanced, correct and guaranteed Cisco 200-301 practice questions. You will get a surprising result by our Down to date Cisco Certified Network Associate practice guides.
Cisco 200-301 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Refer to the exhibit.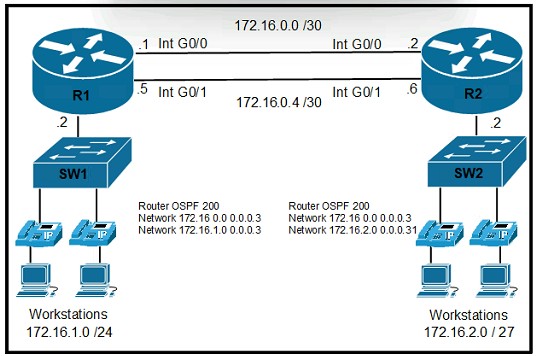
The primary route across Gi0/0 is configured on both routers. A secondary route must be configured to establish connectivity between the workstation networks. Which command set must be configured to complete this task?
A)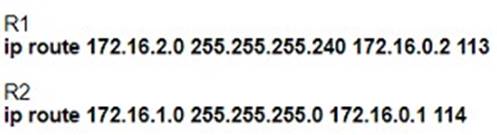
B)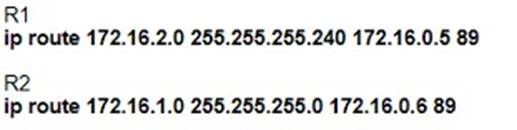
C)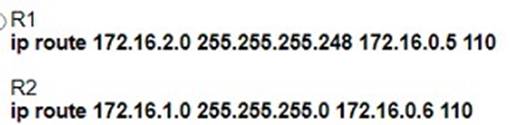
D)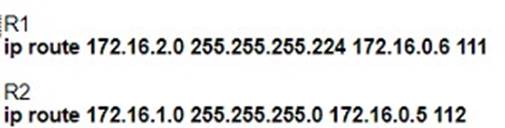
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 2
SIMULATION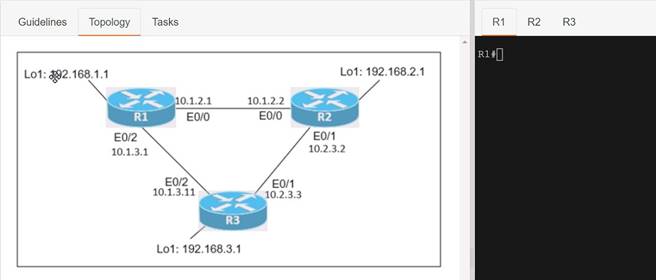
Connectivity between three routers has been established, and IP services must be configured jn the order presented to complete the implementation Tasks assigned include configuration of NAT, NTP, DHCP, and SSH services.
* 1. All traffic sent from R3 to the R1 Loopback address must be configured for NAT on R2. All source addresses must be translated from R3 to the IP address of Ethernet0/0 on R2, while using only a standard access list named NAT To verify, a ping must be successful to the R1 Loopback address sourced from R3. Do not use NVI NAT configuration.
* 2. Configure R1 as an NTP server and R2 as a client, not as a peer, using the IP address of the R1 Ethernet0/2 interface. Set the clock on the NTP server for midnight on January 1, 2019.
* 3. Configure R1 as a DHCP server for the network 10.1.3.0/24 in a pool named TEST. Using a single command, exclude addresses 1-10 from the range. Interface Ethernet0/2 on R3 must be issued the IP address of 10.1.3.11 via DHCP.
* 4. Configure SSH connectivity from R1 to R3, while excluding access via other remote connection protocols. Access for user root and password Cisco must be set on router R3 using RSA and 1024 bits. Verify connectivity using an SSH session from router R1 using a destination address of 10.1.3.11. Do NOT modify console access or line numbers to accomplish this task.
Solution:
Answer as below configuration:
conf t
R1(config)#ntp master 1
R2(config)#ntp server 10.1.2.1
Exit
Router#clock set 00:00:00 jan 1 2019 ip dhcp pool TEST
network 10.1.3.0 255.255.255.0
ip dhcp exluded-address 10.1.3.1 10.1.3.10 R3(config)#int e0/3
R3(config)#int e0/2 ip address dhcp no shut
crypto key generate RSA 1024
Copy run start
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 3
What is the function of the controller in a software-defined network?
- A. multicast replication at the hardware level
- B. fragmenting and reassembling packets
- C. making routing decisions
- D. forwarding packets
Answer: D
NEW QUESTION 4
DRAG DROP
Drag and drop the statements about AAA services firm the left onto the corresponding AAA services on the right Not all options are used.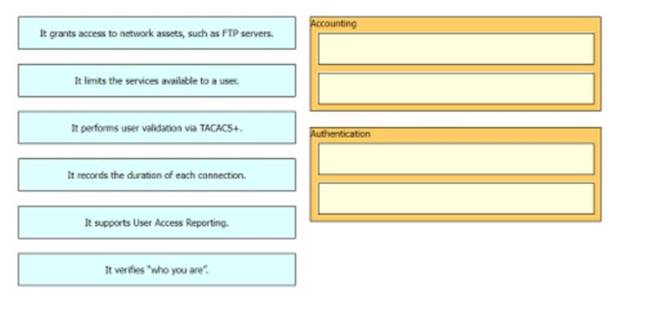
Solution:
1&6 authentication 2&4 authorization
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 5
An email user has been lured into clicking a link in an email sent by their company's security organization. The webpage that opens reports that it was safe but the link could have contained malicious code. Which type of security program is in place?
- A. Physical access control
- B. Social engineering attack
- C. brute force attack
- D. user awareness
Answer: D
Explanation:
This is a training program which simulates an attack, not a real attack (as it says “The webpage that opens reports that it was safe”) so we believed it should be called a “user awareness” program.Therefore the best answer here should be “user awareness”. This is the definition of“User awareness” from CCNA 200- 301 Offical Cert Guide Book:“User awareness: All users should be made aware of the need for data confidentiality to protect corporate information, as well as their own credentials and personal information. They should also be made aware of potential threats, schemes to mislead, and proper procedures to report security incidents. ” Note: Physical access control means infrastructure locations, such as network closets and data centers, should remain securely locked.
NEW QUESTION 6
Refer to the exhibit.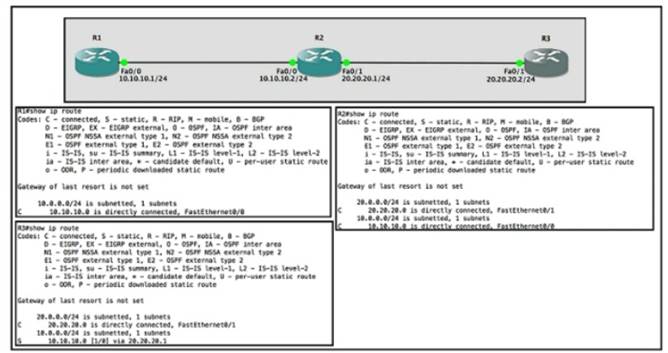
Router R1 Fa0/0 is unable ping router R3 Fa0/1.
Which action must be taken in router R1 to help resolve the configuration issue?
- A. set the default network as 20.20.20.0/24
- B. set the default gateway as 20.20.20.2
- C. configure a static route with Fa0/1 as the egress interface to reach the 20.20.20.0/24 network
- D. configure a static route with 10.10.10.2 as the next hop to reach the 20.20.20.0/24 network
Answer: D
NEW QUESTION 7
Refer to the exhibit.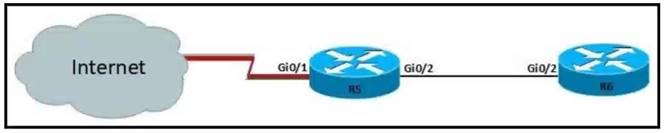
For security reasons, automatic neighbor discovery must be disabled on the R5 Gi0/1 interface. These tasks must be completed:
• Disable all neighbor discovery methods on R5 interface GiO/1.
• Permit neighbor discovery on R5 interface GiO/2.
• Verify there are no dynamically learned neighbors on R5 interface Gi0/1.
• Display the IP address of R6*s interface Gi0/2. Which configuration must be used?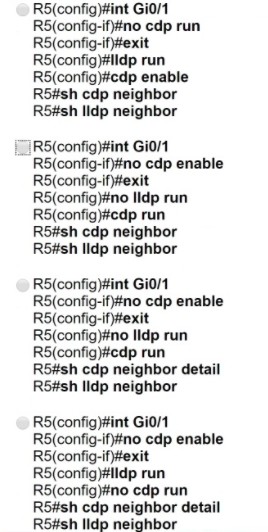
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: C
NEW QUESTION 8
DRAG DROP
Refer to Exhibit.
Rotor to the exhibit. The IP address configurations must be completed on the DC-1 and HQ-1 routers based on these requirements:
DC-1 Gi1/0 must be the last usable address on a /30 DC-1 Gi1/1 must be the first usable address on a /29 DC-1 Gi1/2 must be the last usable address on a /28 HQ-1 Gil/3 must be the last usable address on a /29
Drag and drop the commands from the left onto the destination interfaces on the right. Not all commands are used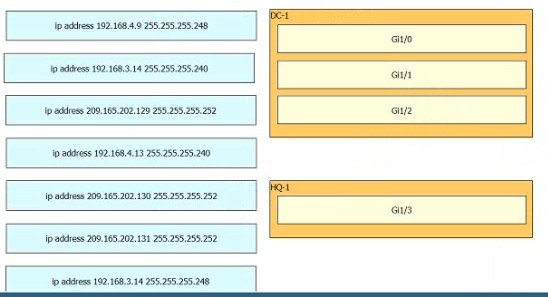
Solution:
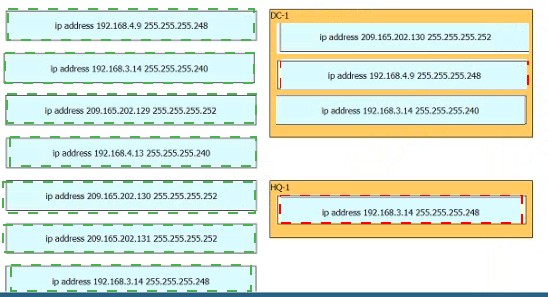
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 9
Refer to the exhibit.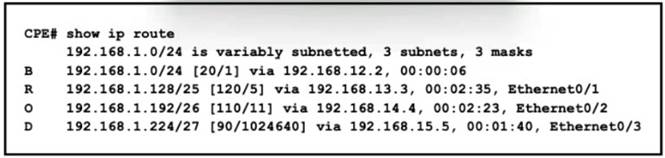
All traffic enters the CPE router from interface Serial0/3 with an IP address of 192 168 50 1 Web traffic from the WAN is destined for a LAN network where servers are load-balanced An IP packet with a destination address of the HTTP virtual IP of 192 1681 250 must be forwarded Which routing table entry does the router use?
- A. 192.168.1.0/24 via 192.168.12.2
- B. 192.168.1.128/25 via 192.168.13.3
- C. 192.168.1.192/26 via 192.168.14.4
- D. 192.168.1.224/27 via 192.168.15.5
Answer: B
NEW QUESTION 10
SIP-based Call Admission Control must be configured in the Cisco WLC GUI. SIP call- snooping ports are configured. Which two actions must be completed next? (Choose two.)
- A. Set the QoS level to silver or greater for voice traffic.
- B. Set the QoS level to platinum for voice traffic.
- C. Enable Media Session Snooping on re WLAN.
- D. Enable traffic shaping for the LAN interlace of the WLC.
- E. Configure two different QoS rotes tor data and voice traffic.
Answer: DE
NEW QUESTION 11
An organization secures its network with multi-factor authentication using an authenticator app on employee smartphone. How is the application secured in the case of a user’s smartphone being lost or stolen?
- A. The application requires an administrator password to reactivate after a configured Interval.
- B. The application requires the user to enter a PIN before it provides the second factor.
- C. The application challenges a user by requiring an administrator password to reactivate when the smartphone is rebooted.
- D. The application verifies that the user is in a specific location before it provides the second factor.
Answer: B
NEW QUESTION 12
Which device separates networks by security domains?
- A. firewall
- B. access point
- C. intrusion protection system
- D. wireless controller
Answer: A
Explanation:
Firewalls are devices that are used to separate networks into different security domains. They act as a barrier between two networks and control the flow of traffic between them. Firewalls use a set of rules to determine what types of traffic are allowed to pass through and what is blocked. This helps protect a network from malicious traffic and unauthorized access. Additionally, firewalls can be configured to log traffic and provide additional security measures such as packet filtering and stateful inspection.
NEW QUESTION 13
A packet from a company s branch office is destined to host 172.31.0.1 at headquarters. The sending router has three possible matches in its routing table for the packet prefixes: 172. 31.0 .0/16.72.31.0.0724. and 172.31 0 0/25.
How does the router handle the packet?
- A. It sends the traffic via prefix 172.31.0.0/16
- B. It sends the traffic via the default gateway 0.0.0.070.
- C. It sends the traffic via prefix 172.31.0.0/24
- D. It sends the traffic via prefix 172.31.0.0/25
Answer: D
NEW QUESTION 14
Which type of address is the public IP address of a NAT device?
- A. outside global
- B. outsdwde local
- C. inside global
- D. insride local
- E. outside public
- F. inside public
Answer: C
Explanation:
NAT use four types of addresses:* Inside local address – The IP address assigned to a host on the inside network. The address is usually not an IP address assigned by the Internet Network Information Center (InterNIC) or service provider.This address is likely to be an RFC 1918 private address.* Inside global address – A legitimate IP address assigned by the InterNIC or service provider that represents one or more inside local IP addresses to the outside world.* Outside local address – The IP address of an outside host as it is known to the hosts on the inside network.* Outside global address – The IP address assigned to a host on the outside network. The owner of the host assigns
this address.
NEW QUESTION 15
Refer to the exhibit.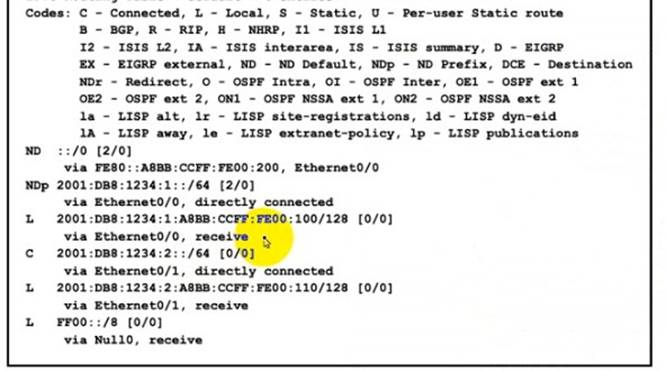
The administrator must configure a floating sialic default route that points to 2001:db8:1234:2::1 and replaces the current default route only if it fails. Which command must the engineer configure on the CPE?
- A. ipv6 route ::/0 2001:db8:1234:2::1 3
- B. ipv6 route ::/128 2001 :db8:1234:2::1 3
- C. ipv6 route ::/0 2001:db8:1234:2::1 1
- D. ipv6 route ::/0 2001:db8:1234:2::1 2
Answer: B
NEW QUESTION 16
Refer the exhibit.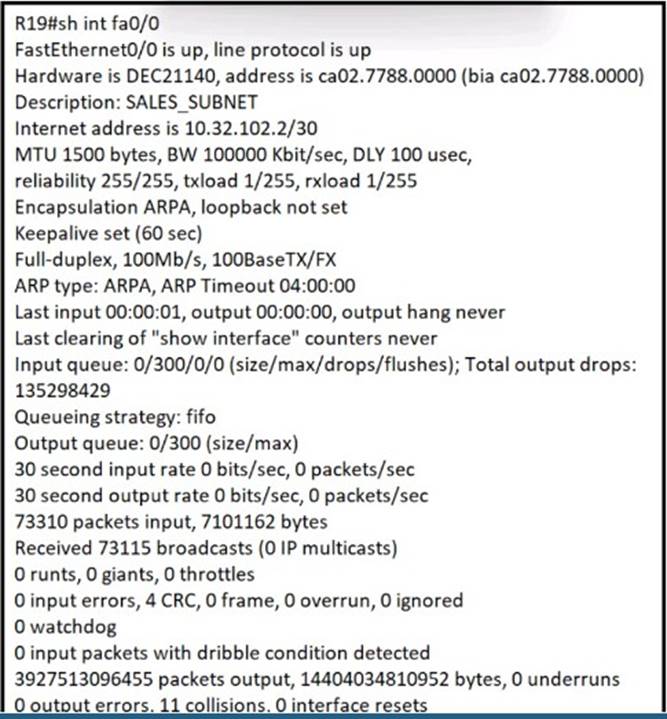
What is the cause of poor performance on router R19?
- A. excessive collisions
- B. speed and duplex mismatch
- C. port oversubscription
- D. excessive CRC errors
Answer: A
NEW QUESTION 17
......
Thanks for reading the newest 200-301 exam dumps! We recommend you to try the PREMIUM 2passeasy 200-301 dumps in VCE and PDF here: https://www.2passeasy.com/dumps/200-301/ (903 Q&As Dumps)
