It is more faster and easier to pass the EC-Council 312-49v10 exam by using Verified EC-Council Computer Hacking Forensic Investigator (CHFI-v10) questuins and answers. Immediate access to the Renewal 312-49v10 Exam and find the same core area 312-49v10 questions with professionally verified answers, then PASS your exam with a high score now.
EC-Council 312-49v10 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
When setting up a wireless network with multiple access points, why is it important to set each access point on a different channel?
- A. Multiple access points can be set up on the same channel without any issues
- B. Avoid over-saturation of wireless signals
- C. So that the access points will work on different frequencies
- D. Avoid cross talk
Answer: D
NEW QUESTION 2
Which of the following standard represents a legal precedent set in 1993 by the Supreme Court of the United States regarding the admissibility of expert witnesses' testimony during federal legal proceedings?
- A. SWGDE & SWGIT
- B. IOCE
- C. Frye
- D. Daubert
Answer: D
NEW QUESTION 3
Which of the following is a record of the characteristics of a file system, including its size, the block size, the empty and the filled blocks and their respective counts, the size and location of the inode tables, the disk block map and usage information, and the size of the block groups?
- A. Inode bitmap block
- B. Superblock
- C. Block bitmap block
- D. Data block
Answer: B
NEW QUESTION 4
E- mail logs contain which of the following information to help you in your investigation? (Choose four.)
- A. user account that was used to send the account
- B. attachments sent with the e-mail message
- C. unique message identifier
- D. contents of the e-mail message
- E. date and time the message was sent
Answer: ACDE
NEW QUESTION 5
When investigating a computer forensics case where Microsoft Exchange and Blackberry Enterprise server are used, where would investigator need to search to find email sent from a Blackberry device?
- A. RIM Messaging center
- B. Blackberry Enterprise server
- C. Microsoft Exchange server
- D. Blackberry desktop redirector
Answer: C
NEW QUESTION 6
This is a statement, other than one made by the declarant while testifying at the trial or hearing, offered in evidence to prove the truth of the matter asserted. Which among the following is suitable for the above statement?
- A. Testimony by the accused
- B. Limited admissibility
- C. Hearsay rule
- D. Rule 1001
Answer: C
NEW QUESTION 7
Select the tool appropriate for examining the dynamically linked libraries of an application or malware.
- A. DependencyWalker
- B. SysAnalyzer
- C. PEiD
- D. ResourcesExtract
Answer: A
NEW QUESTION 8
An Expert witness give an opinion if:
- A. The Opinion, inferences or conclusions depend on special knowledge, skill or training not within the ordinary experience of lay jurors
- B. To define the issues of the case for determination by the finder of fact
- C. To stimulate discussion between the consulting expert and the expert witness
- D. To deter the witness form expanding the scope of his or her investigation beyond the requirements of the case
Answer: A
NEW QUESTION 9
The following is a log file screenshot from a default installation of IIS 6.0.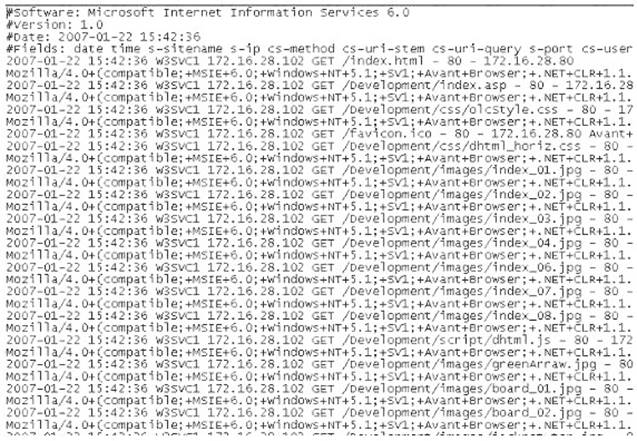
What time standard is used by IIS as seen in the screenshot?
- A. UTC
- B. GMT
- C. TAI
- D. UT
Answer: A
NEW QUESTION 10
Jim’s company regularly performs backups of their critical servers. But the company can’t afford to send backup tapes to an off-site vendor for long term storage and archiving. Instead Jim’s company keeps the backup tapes in a safe in the office. Jim’s company is audited each year, and the results from this year’s audit show a risk because backup tapes aren’t stored off-site. The Manager of Information Technology has a plan to take the backup tapes home with him and wants to know what two things he can do to secure the backup tapes while in transit?
- A. Encrypt the backup tapes and use a courier to transport them.
- B. Encrypt the backup tapes and transport them in a lock box
- C. Degauss the backup tapes and transport them in a lock box.
- D. Hash the backup tapes and transport them in a lock box.
Answer: B
NEW QUESTION 11
You are a computer forensics investigator working with local police department and you are called to assist in an investigation of threatening emails. The complainant has printer out 27 email messages from the suspect and gives the printouts to you. You inform her that you will need to examine her computer because you need access to the in order to track the emails back to the suspect.
- A. Routing Table
- B. Firewall log
- C. Configuration files
- D. Email Header
Answer: D
NEW QUESTION 12
Which MySQL log file contains information on server start and stop?
- A. Slow query log file
- B. General query log file
- C. Binary log
- D. Error log file
Answer: D
NEW QUESTION 13
Email archiving is a systematic approach to save and protect the data contained in emails so that it can be accessed fast at a later date. There are two main archive types, namely Local Archive and Server Storage Archive. Which of the following statements is correct while dealing with local archives?
- A. Server storage archives are the server information and settings stored on a local system, whereas the local archives are the local email client information stored on the mail server
- B. It is difficult to deal with the webmail as there is no offline archive in most case
- C. So consult your counsel on the case as to the best way to approach and gain access to the required data on servers
- D. Local archives should be stored together with the server storage archives in order to be admissible in a court of law
- E. Local archives do not have evidentiary value as the email client may alter the message data
Answer: B
NEW QUESTION 14
What is the role of Alloc.c in Apache core?
- A. It handles allocation of resource pools
- B. It is useful for reading and handling of the configuration files
- C. It takes care of all the data exchange and socket connections between the client and the server
- D. It handles server start-ups and timeouts
Answer: A
NEW QUESTION 15
In conducting a computer abuse investigation you become aware that the suspect of the investigation is using ABC Company as his Internet Service Provider (ISP). You contact ISP and request that they provide you assistance with your investigation. What assistance can the ISP provide?
- A. The ISP can investigate anyone using their service and can provide you with assistance
- B. The ISP can investigate computer abuse committed by their employees, but must preserve the privacy of their customers and therefore cannot assist you without a warrant
- C. The ISP can't conduct any type of investigations on anyone and therefore can't assist you
- D. ISP's never maintain log files so they would be of no use to your investigation
Answer: B
NEW QUESTION 16
With the standard Linux second extended file system (Ext2fs), a file is deleted when the inode internal link count reaches .
- A. 10
- B. 100
- C. 1
Answer: A
NEW QUESTION 17
......
P.S. Downloadfreepdf.net now are offering 100% pass ensure 312-49v10 dumps! All 312-49v10 exam questions have been updated with correct answers: https://www.downloadfreepdf.net/312-49v10-pdf-download.html (701 New Questions)
