Our pass rate is high to 98.9% and the similarity percentage between our 312-49v10 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the EC-Council 312-49v10 exam in just one try? I am currently studying for the EC-Council 312-49v10 exam. Latest EC-Council 312-49v10 Test exam practice questions and answers, Try EC-Council 312-49v10 Brain Dumps First.
Free 312-49v10 Demo Online For EC-Council Certifitcation:
NEW QUESTION 1
The efforts to obtain information before a trail by demanding documents, depositions, questioned and answers written under oath, written requests for admissions of fact and examination of the scene is a description of what legal term?
- A. Detection
- B. Hearsay
- C. Spoliation
- D. Discovery
Answer: D
NEW QUESTION 2
Jessica works as systems administrator for a large electronics firm. She wants to scan her network quickly to detect live hosts by using ICMP ECHO Requests. What type of scan is Jessica going to perform?
- A. Tracert
- B. Smurf scan
- C. Ping trace
- D. ICMP ping sweep
Answer: D
NEW QUESTION 3
In a forensic examination of hard drives for digital evidence, what type of user is most likely to have the most file slack to analyze?
- A. one who has NTFS 4 or 5 partitions
- B. one who uses dynamic swap file capability
- C. one who uses hard disk writes on IRQ 13 and 21
- D. one who has lots of allocation units per block or cluster
Answer: D
NEW QUESTION 4
The given image displays information about date and time of installation of the OS along with service packs, patches, and sub-directories. What command or tool did the investigator use to view this output?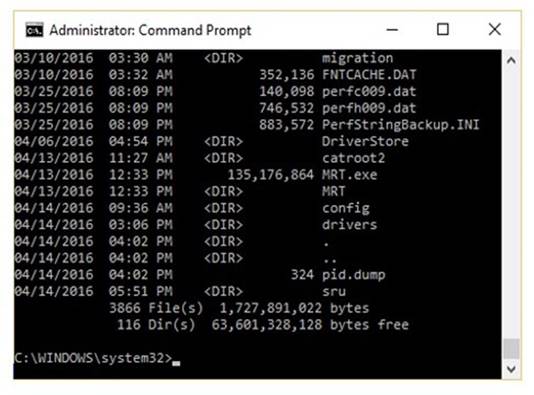
- A. dir /o:d
- B. dir /o:s
- C. dir /o:e
- D. dir /o:n
Answer: A
NEW QUESTION 5
Sally accessed the computer system that holds trade secrets of the company where she Is employed. She knows she accessed It without authorization and all access (authorized and unauthorized) to this computer Is monitored.To cover her tracks. Sally deleted the log entries on this computer. What among the following best describes her action?
- A. Password sniffing
- B. Anti-forensics
- C. Brute-force attack
- D. Network intrusion
Answer: B
NEW QUESTION 6
Which of the following tasks DOES NOT come under the investigation phase of a cybercrime forensics investigation case?
- A. Data collection
- B. Secure the evidence
- C. First response
- D. Data analysis
Answer: C
NEW QUESTION 7
Which of the following attack uses HTML tags like <script></script>?
- A. Phishing
- B. XSS attack
- C. SQL injection
- D. Spam
Answer: B
NEW QUESTION 8
To which phase of the computer forensics investigation process does "planning and budgeting of a forensics lab" belong?
- A. Post-investigation phase
- B. Reporting phase
- C. Pre-investigation phase
- D. Investigation phase
Answer: C
NEW QUESTION 9
Malware analysis can be conducted in various manners. An investigator gathers a suspicious executable file and uploads It to VirusTotal in order to confirm whether the file Is malicious, provide information about Its functionality, and provide Information that will allow to produce simple network signatures. What type of malware analysis was performed here?
- A. Static
- B. Volatile
- C. Dynamic
- D. Hybrid
Answer: D
NEW QUESTION 10
Which of the following options will help users to enable or disable the last access time on a system running Windows 10 OS?
- A. wmic service
- B. Reg.exe
- C. fsutil
- D. Devcon
Answer: C
NEW QUESTION 11
Which layer in the loT architecture is comprised of hardware parts such as sensors, RFID tags, and devices that play an important role in data collection?
- A. Middleware layer
- B. Edge technology layer
- C. Application layer
- D. Access gateway layer
Answer: B
NEW QUESTION 12
When should an MD5 hash check be performed when processing evidence?
- A. After the evidence examination has been completed
- B. On an hourly basis during the evidence examination
- C. Before and after evidence examination
- D. Before the evidence examination has been completed
Answer: C
NEW QUESTION 13
Which of the following Windows-based tool displays who is logged onto a computer, either locally or remotely?
- A. Tokenmon
- B. PSLoggedon
- C. TCPView
- D. Process Monitor
Answer: B
NEW QUESTION 14
Shane, a forensic specialist, is investigating an ongoing attack on a MySQL database server hosted on a Windows machine with SID “WIN-ABCDE12345F.” Which of the following log file will help Shane in tracking all the client connections and activities performed on the database server?
- A. WIN-ABCDE12345F.err
- B. WIN-ABCDE12345F-bin.n
- C. WIN-ABCDE12345F.pid
- D. WIN-ABCDE12345F.log
Answer: D
NEW QUESTION 15
Sniffers that place NICs in promiscuous mode work at what layer of the OSI model?
- A. Network
- B. Transport
- C. Physical
- D. Data Link
Answer: C
NEW QUESTION 16
Which of the following statements is TRUE about SQL Server error logs?
- A. SQL Server error logs record all the events occurred on the SQL Server and its databases
- B. Forensic investigator uses SQL Server Profiler to view error log files
- C. Error logs contain IP address of SQL Server client connections
- D. Trace files record, user-defined events, and specific system events
Answer: B
NEW QUESTION 17
......
P.S. Surepassexam now are offering 100% pass ensure 312-49v10 dumps! All 312-49v10 exam questions have been updated with correct answers: https://www.surepassexam.com/312-49v10-exam-dumps.html (701 New Questions)
