It is impossible to pass EC-Council 312-49v10 exam without any help in the short term. Come to Pass4sure soon and find the most advanced, correct and guaranteed EC-Council 312-49v10 practice questions. You will get a surprising result by our Improve Computer Hacking Forensic Investigator (CHFI-v10) practice guides.
Check 312-49v10 free dumps before getting the full version:
NEW QUESTION 1
Robert, a cloud architect, received a huge bill from the cloud service provider, which usually doesn't happen. After analyzing the bill, he found that the cloud resource consumption was very high. He then examined the cloud server and discovered that a malicious code was running on the server, which was generating huge but harmless traffic from the server. This means that the server has been compromised by an attacker with the sole intention to hurt the cloud customer financially. Which attack is described in the above scenario?
- A. XSS Attack
- B. DDoS Attack (Distributed Denial of Service)
- C. Man-in-the-cloud Attack
- D. EDoS Attack (Economic Denial of Service)
Answer: B
NEW QUESTION 2
In Microsoft file structures, sectors are grouped together to form:
- A. Clusters
- B. Drives
- C. Bitstreams
- D. Partitions
Answer: A
NEW QUESTION 3
The offset in a hexadecimal code is:
- A. The last byte after the colon
- B. The 0x at the beginning of the code
- C. The 0x at the end of the code
- D. The first byte after the colon
Answer: B
NEW QUESTION 4
Richard is extracting volatile data from a system and uses the command doskey/history. What is he trying to extract?
- A. Events history
- B. Previously typed commands
- C. History of the browser
- D. Passwords used across the system
Answer: B
NEW QUESTION 5
When investigating a wireless attack, what information can be obtained from the DHCP logs?
- A. The operating system of the attacker and victim computers
- B. IP traffic between the attacker and the victim
- C. MAC address of the attacker
- D. If any computers on the network are running in promiscuous mode
Answer: C
NEW QUESTION 6
Which principle states that “anyone or anything, entering a crime scene takes something of the scene with them, and leaves something of themselves behind when they leave”?
- A. Locard's Exchange Principle
- B. Enterprise Theory of Investigation
- C. Locard's Evidence Principle
- D. Evidence Theory of Investigation
Answer: A
NEW QUESTION 7
Volatile Memory is one of the leading problems for forensics. Worms such as code Red are memory resident and do write themselves to the hard drive, if you turn the system off they disappear. In a lab environment, which of the following options would you suggest as the most appropriate to overcome the problem of capturing volatile memory?
- A. Use VMware to be able to capture the data in memory and examine it
- B. Give the Operating System a minimal amount of memory, forcing it to use a swap file
- C. Create a Separate partition of several hundred megabytes and place the swap file there
- D. Use intrusion forensic techniques to study memory resident infections
Answer: C
NEW QUESTION 8
When searching through file headers for picture file formats, what should be searched to find a JPEG file in hexadecimal format?
- A. FF D8 FF E0 00 10
- B. FF FF FF FF FF FF
- C. FF 00 FF 00 FF 00
- D. EF 00 EF 00 EF 00
Answer: A
NEW QUESTION 9
Which of the following commands shows you the names of all open shared files on a server and the number of file locks on each file?
- A. Net config
- B. Net file
- C. Net share
- D. Net sessions
Answer: B
NEW QUESTION 10
You are running known exploits against your network to test for possible vulnerabilities. To test the strength of your virus software, you load a test network to mimic your production network. Your software successfully blocks some simple macro and encrypted viruses. You decide to really test the software by using virus code where the code rewrites itself entirely and the signatures change from child to child, but the functionality stays the same. What type of virus is this that you are testing?
- A. Polymorphic
- B. Metamorphic
- C. Oligomorhic
- D. Transmorphic
Answer: B
NEW QUESTION 11
A forensic analyst has been tasked with investigating unusual network activity Inside a retail company's network. Employees complain of not being able to access services, frequent rebooting, and anomalies In log files. The Investigator requested log files from the IT administrator and after carefully reviewing them, he finds the following log entry: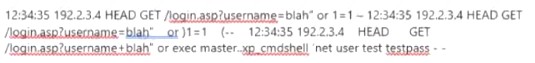
What type of attack was performed on the companies' web application?
- A. Directory transversal
- B. Unvalidated input
- C. Log tampering
- D. SQL injection
Answer: D
NEW QUESTION 12
You are assisting a Department of Defense contract company to become compliant with the stringent security policies set by the DoD. One such strict rule is that firewalls must only allow incoming connections that were first initiated by internal computers. What type of firewall must you implement to abide by this policy?
- A. Packet filtering firewall
- B. Circuit-level proxy firewall
- C. Application-level proxy firewall
- D. Stateful firewall
Answer: D
NEW QUESTION 13
Pick the statement which does not belong to the Rule 804. Hearsay Exceptions; Declarant Unavailable.
- A. Statement of personal or family history
- B. Prior statement by witness
- C. Statement against interest
- D. Statement under belief of impending death
Answer: D
NEW QUESTION 14
What type of analysis helps to identify the time and sequence of events in an investigation?
- A. Time-based
- B. Functional
- C. Relational
- D. Temporal
Answer: D
NEW QUESTION 15
Which of the following file contains the traces of the applications installed, run, or uninstalled from a system?
- A. Shortcut Files
- B. Virtual files
- C. Prefetch Files
- D. Image Files
Answer: A
NEW QUESTION 16
Which among the following acts has been passed by the U.S. Congress to protect investors from the possibility of fraudulent accounting activities by corporations?
- A. Federal Information Security Management act of 2002
- B. Gramm-Leach-Bliley act
- C. Health insurance Probability and Accountability act of 1996
- D. Sarbanes-Oxley act of 2002
Answer: D
NEW QUESTION 17
......
Thanks for reading the newest 312-49v10 exam dumps! We recommend you to try the PREMIUM Allfreedumps.com 312-49v10 dumps in VCE and PDF here: https://www.allfreedumps.com/312-49v10-dumps.html (701 Q&As Dumps)
