It is impossible to pass EC-Council 312-50v11 exam without any help in the short term. Come to Ucertify soon and find the most advanced, correct and guaranteed EC-Council 312-50v11 practice questions. You will get a surprising result by our Down to date Certified Ethical Hacker Exam (CEH v11) practice guides.
Online 312-50v11 free questions and answers of New Version:
NEW QUESTION 1
Which of the following tools can be used for passive OS fingerprinting?
- A. nmap
- B. tcpdump
- C. tracert
- D. ping
Answer: B
NEW QUESTION 2
During a black-box pen test you attempt to pass IRC traffic over port 80/TCP from a compromised web enabled host. The traffic gets blocked; however, outbound HTTP traffic is unimpeded. What type of firewall is inspecting outbound traffic?
- A. Circuit
- B. Stateful
- C. Application
- D. Packet Filtering
Answer: B
NEW QUESTION 3
Which of the following is an extremely common IDS evasion technique in the web world?
- A. Spyware
- B. Subnetting
- C. Unicode Characters
- D. Port Knocking
Answer: C
NEW QUESTION 4
A zone file consists of which of the following Resource Records (RRs)?
- A. DNS, NS, AXFR, and MX records
- B. DNS, NS, PTR, and MX records
- C. SOA, NS, AXFR, and MX records
- D. SOA, NS, A, and MX records
Answer: D
NEW QUESTION 5
A pen tester is configuring a Windows laptop for a test. In setting up Wireshark, what river and library are required to allow the NIC to work in promiscuous mode?
- A. Libpcap
- B. Awinpcap
- C. Winprom
- D. Winpcap
Answer: D
NEW QUESTION 6
A company’s security policy states that all Web browsers must automatically delete their HTTP browser cookies upon terminating. What sort of security breach is this policy attempting to mitigate?
- A. Attempts by attackers to access the user and password information stored in the company’s SQL database.
- B. Attempts by attackers to access Web sites that trust the Web browser user by stealing the user’s authentication credentials.
- C. Attempts by attackers to access password stored on the user’s computer without the user’s knowledge.
- D. Attempts by attackers to determine the user’s Web browser usage patterns, including when sites were visited and for how long.
Answer: B
NEW QUESTION 7
Suppose your company has just passed a security risk assessment exercise. The results display that the risk of the breach in the main company application is 50%. Security staff has taken some measures and
implemented the necessary controls. After that, another security risk assessment was performed showing that risk has decreased to 10%. The risk threshold for the application is 20%. Which of the following risk decisions will be the best for the project in terms of its successful continuation with the most business profit?
- A. Accept the risk
- B. Introduce more controls to bring risk to 0%
- C. Mitigate the risk
- D. Avoid the risk
Answer: A
NEW QUESTION 8
OpenSSL on Linux servers includes a command line tool for testing TLS. What is the name of the tool and the correct syntax to connect to a web server?
- A. openssl s_client -site www.website.com:443
- B. openssl_client -site www.website.com:443
- C. openssl s_client -connect www.website.com:443
- D. openssl_client -connect www.website.com:443
Answer: C
NEW QUESTION 9
You are tasked to perform a penetration test. While you are performing information gathering, you find an employee list in Google. You find the receptionist’s email, and you send her an email changing the source email to her boss’s email (boss@company). In this email, you ask for a pdf with information. She reads your email and sends back a pdf with links. You exchange the pdf links with your malicious links (these links contain malware) and send back the modified pdf, saying that the links don’t work. She reads your email, opens the links, and her machine gets infected. You now have access to the company network. What testing method did you use?
- A. Social engineering
- B. Piggybacking
- C. Tailgating
- D. Eavesdropping
Answer: A
NEW QUESTION 10
What is the algorithm used by LM for Windows2000 SAM?
- A. MD4
- B. DES
- C. SHA
- D. SSL
Answer: B
NEW QUESTION 11
You are working as a Security Analyst in a company XYZ that owns the whole subnet range of 23.0.0.0/8 and 192.168.0.0/8.
While monitoring the data, you find a high number of outbound connections. You see that IP’s owned by XYZ (Internal) and private IP’s are communicating to a Single Public IP. Therefore, the Internal IP’s are sending data to the Public IP.
After further analysis, you find out that this Public IP is a blacklisted IP, and the internal communicating devices are compromised.
What kind of attack does the above scenario depict?
- A. Botnet Attack
- B. Spear Phishing Attack
- C. Advanced Persistent Threats
- D. Rootkit Attack
Answer: A
NEW QUESTION 12
John the Ripper is a technical assessment tool used to test the weakness of which of the following?
- A. Passwords
- B. File permissions
- C. Firewall rulesets
- D. Usernames
Answer: A
NEW QUESTION 13
Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool "SIDExtractor". Here is the output of the SIDs: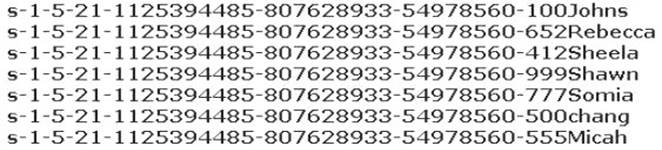
From the above list identify the user account with System Administrator privileges.
- A. John
- B. Rebecca
- C. Sheela
- D. Shawn
- E. Somia
- F. Chang
- G. Micah
Answer: F
NEW QUESTION 14
Which utility will tell you in real time which ports are listening or in another state?
- A. Netstat
- B. TCPView
- C. Nmap
- D. Loki
Answer: B
NEW QUESTION 15
When discussing passwords, what is considered a brute force attack?
- A. You attempt every single possibility until you exhaust all possible combinations or discover the password
- B. You threaten to use the rubber hose on someone unless they reveal their password
- C. You load a dictionary of words into your cracking program
- D. You create hashes of a large number of words and compare it with the encrypted passwords
- E. You wait until the password expires
Answer: A
NEW QUESTION 16
You just set up a security system in your network. In what kind of system would you find the following string of characters used as a rule within its configuration? alert tcp any any -> 192.168.100.0/24 21 (msg: ““FTP on the network!””;)
- A. A firewall IPTable
- B. FTP Server rule
- C. A Router IPTable
- D. An Intrusion Detection System
Answer: D
NEW QUESTION 17
Bob is doing a password assessment for one of his clients. Bob suspects that security policies are not in place. He also suspects that weak passwords are probably the norm throughout the company he is evaluating. Bob is familiar with password weaknesses and key loggers.
Which of the following options best represents the means that Bob can adopt to retrieve passwords from his clients hosts and servers?
- A. Hardware, Software, and Sniffing.
- B. Hardware and Software Keyloggers.
- C. Passwords are always best obtained using Hardware key loggers.
- D. Software only, they are the most effective.
Answer: A
NEW QUESTION 18
Which definition among those given below best describes a covert channel?
- A. A server program using a port that is not well known.
- B. Making use of a protocol in a way it is not intended to be used.
- C. It is the multiplexing taking place on a communication link.
- D. It is one of the weak channels used by WEP which makes it insecure
Answer: B
NEW QUESTION 19
You are the Network Admin, and you get a complaint that some of the websites are no longer accessible. You try to ping the servers and find them to be reachable. Then you type the IP address and then you try on the browser, and find it to be accessible. But they are not accessible when you try using the URL.
What may be the problem?
- A. Traffic is Blocked on UDP Port 53
- B. Traffic is Blocked on TCP Port 80
- C. Traffic is Blocked on TCP Port 54
- D. Traffic is Blocked on UDP Port 80
Answer: A
NEW QUESTION 20
While scanning with Nmap, Patin found several hosts which have the IP ID of incremental sequences. He then decided to conduct: nmap -Pn -p- -si kiosk.adobe.com www.riaa.com. kiosk.adobe.com is the host with incremental IP ID sequence. What is the purpose of using "-si" with Nmap?
- A. Conduct stealth scan
- B. Conduct ICMP scan
- C. Conduct IDLE scan
- D. Conduct silent scan
Answer: A
NEW QUESTION 21
Which of the following algorithms can be used to guarantee the integrity of messages being sent, in transit, or stored?
- A. symmetric algorithms
- B. asymmetric algorithms
- C. hashing algorithms
- D. integrity algorithms
Answer: C
NEW QUESTION 22
......
P.S. Surepassexam now are offering 100% pass ensure 312-50v11 dumps! All 312-50v11 exam questions have been updated with correct answers: https://www.surepassexam.com/312-50v11-exam-dumps.html (254 New Questions)
