Cause all that matters here is passing the EC-Council 312-50v11 exam. Cause all that you need is a high score of 312-50v11 Certified Ethical Hacker Exam (CEH v11) exam. The only one thing you need to do is downloading Actualtests 312-50v11 exam study guides now. We will not let you down with our money-back guarantee.
Free demo questions for EC-Council 312-50v11 Exam Dumps Below:
NEW QUESTION 1
Due to a slowdown of normal network operations, the IT department decided to monitor internet traffic for all of the employees. From a legal standpoint, what would be troublesome to take this kind of measure?
- A. All of the employees would stop normal work activities
- B. IT department would be telling employees who the boss is
- C. Not informing the employees that they are going to be monitored could be an invasion of privacy.
- D. The network could still experience traffic slow down.
Answer: C
NEW QUESTION 2
Shellshock allowed an unauthorized user to gain access to a server. It affected many Internet-facing services, which OS did it not directly affect?
- A. Linux
- B. Unix
- C. OS X
- D. Windows
Answer: D
NEW QUESTION 3
A large mobile telephony and data network operator has a data center that houses network elements. These are essentially large computers running on Linux. The perimeter of the data center is secured with firewalls and IPS systems.
What is the best security policy concerning this setup?
- A. Network elements must be hardened with user ids and strong password
- B. Regular security tests and audits should be performed.
- C. As long as the physical access to the network elements is restricted, there is no need for additional measures.
- D. There is no need for specific security measures on the network elements as long as firewalls and IPS systems exist.
- E. The operator knows that attacks and down time are inevitable and should have a backup site.
Answer: A
NEW QUESTION 4
One of your team members has asked you to analyze the following SOA record. What is the version? Rutgers.edu.SOA NS1.Rutgers.edu ipad.college.edu (200302028 3600 3600 604800 2400.) (Choose four.)
- A. 200303028
- B. 3600
- C. 604800
- D. 2400
- E. 60
- F. 4800
Answer: A
NEW QUESTION 5
In the context of Windows Security, what is a 'null' user?
- A. A user that has no skills
- B. An account that has been suspended by the admin
- C. A pseudo account that has no username and password
- D. A pseudo account that was created for security administration purpose
Answer: C
NEW QUESTION 6
Which of the following program infects the system boot sector and the executable files at the same time?
- A. Polymorphic virus
- B. Stealth virus
- C. Multipartite Virus
- D. Macro virus
Answer: C
NEW QUESTION 7
What is the role of test automation in security testing?
- A. It is an option but it tends to be very expensive.
- B. It should be used exclusivel
- C. Manual testing is outdated because of low speed and possible test setup inconsistencies.
- D. Test automation is not usable in security due to the complexity of the tests.
- E. It can accelerate benchmark tests and repeat them with a consistent test setu
- F. But it cannot replace manual testing completely.
Answer: D
NEW QUESTION 8
Which of the following tools performs comprehensive tests against web servers, including dangerous files and CGIs?
- A. Nikto
- B. John the Ripper
- C. Dsniff
- D. Snort
Answer: A
NEW QUESTION 9
What is correct about digital signatures?
- A. A digital signature cannot be moved from one signed document to another because it is the hash of the original document encrypted with the private key of the signing party.
- B. Digital signatures may be used in different documents of the same type.
- C. A digital signature cannot be moved from one signed document to another because it is a plain hash of the document content.
- D. Digital signatures are issued once for each user and can be used everywhere until they expire.
Answer: A
NEW QUESTION 10
You have successfully logged on a Linux system. You want to now cover your trade Your login attempt may be logged on several files located in /var/log. Which file does NOT belongs to the list:
- A. user.log
- B. auth.fesg
- C. wtmp
- D. btmp
Answer: C
NEW QUESTION 11
Hackers often raise the trust level of a phishing message by modeling the email to look similar to the internal email used by the target company. This includes using logos, formatting, and names of the target company. The phishing message will often use the name of the company CEO, President, or Managers. The time a hacker spends performing research to locate this information about a company is known as?
- A. Exploration
- B. Investigation
- C. Reconnaissance
- D. Enumeration
Answer: C
NEW QUESTION 12
What ports should be blocked on the firewall to prevent NetBIOS traffic from not coming through the firewall if your network is comprised of Windows NT, 2000, and XP?
- A. 110
- B. 135
- C. 139
- D. 161
- E. 445
- F. 1024
Answer: BCE
NEW QUESTION 13
Which results will be returned with the following Google search query? site:target.com – site:Marketing.target.com accounting
- A. Results from matches on the site marketing.target.com that are in the domain target.com but do not include the word accounting.
- B. Results matching all words in the query.
- C. Results for matches on target.com and Marketing.target.com that include the word “accounting”
- D. Results matching “accounting” in domain target.com but not on the site Marketing.target.com
Answer: D
NEW QUESTION 14
You work for Acme Corporation as Sales Manager. The company has tight network security restrictions. You are trying to steal data from the company's Sales database (Sales.xls) and transfer them to your home computer. Your company filters and monitors traffic that leaves from the internal network to the Internet. How will you achieve this without raising suspicion?
- A. Encrypt the Sales.xls using PGP and e-mail it to your personal gmail account
- B. Package the Sales.xls using Trojan wrappers and telnet them back your home computer
- C. You can conceal the Sales.xls database in another file like photo.jpg or other files and send it out in an innocent looking email or file transfer using Steganography techniques
- D. Change the extension of Sales.xls to sales.txt and upload them as attachment to your hotmail account
Answer: C
NEW QUESTION 15
A company’s policy requires employees to perform file transfers using protocols which encrypt traffic. You suspect some employees are still performing file transfers using unencrypted protocols because the employees do not like changes. You have positioned a network sniffer to capture traffic from the laptops used by employees in the data ingest department. Using Wireshark to examine the captured traffic, which command can be used as display filter to find unencrypted file transfers?
- A. tcp.port = = 21
- B. tcp.port = 23
- C. tcp.port = = 21 | | tcp.port = =22
- D. tcp.port ! = 21
Answer: A
NEW QUESTION 16
The establishment of a TCP connection involves a negotiation called three-way handshake. What type of message does the client send to the server in order to begin this negotiation?
- A. ACK
- B. SYN
- C. RST
- D. SYN-ACK
Answer: B
NEW QUESTION 17
A technician is resolving an issue where a computer is unable to connect to the Internet using a wireless access point. The computer is able to transfer files locally to other machines, but cannot successfully reach the Internet. When the technician examines the IP address and default gateway they are both on the 192.168.1.0/24. Which of the following has occurred?
- A. The computer is not using a private IP address.
- B. The gateway is not routing to a public IP address.
- C. The gateway and the computer are not on the same network.
- D. The computer is using an invalid IP address.
Answer: B
NEW QUESTION 18
An attacker has installed a RAT on a host. The attacker wants to ensure that when a user attempts to go to "www.MyPersonalBank.com", the user is directed to a phishing site.
Which file does the attacker need to modify?
- A. Boot.ini
- B. Sudoers
- C. Networks
- D. Hosts
Answer: D
NEW QUESTION 19
An attacker, using a rogue wireless AP, performed an MITM attack and injected an HTML code to embed a malicious applet in all HTTP connections.
When users accessed any page, the applet ran and exploited many machines. Which one of the following tools the hacker probably used to inject HTML code?
- A. Wireshark
- B. Ettercap
- C. Aircrack-ng
- D. Tcpdump
Answer: B
NEW QUESTION 20
How can you determine if an LM hash you extracted contains a password that is less than 8 characters long?
- A. There is no way to tell because a hash cannot be reversed
- B. The right most portion of the hash is always the same
- C. The hash always starts with AB923D
- D. The left most portion of the hash is always the same
- E. A portion of the hash will be all 0's
Answer: B
NEW QUESTION 21
Study the following log extract and identify the attack.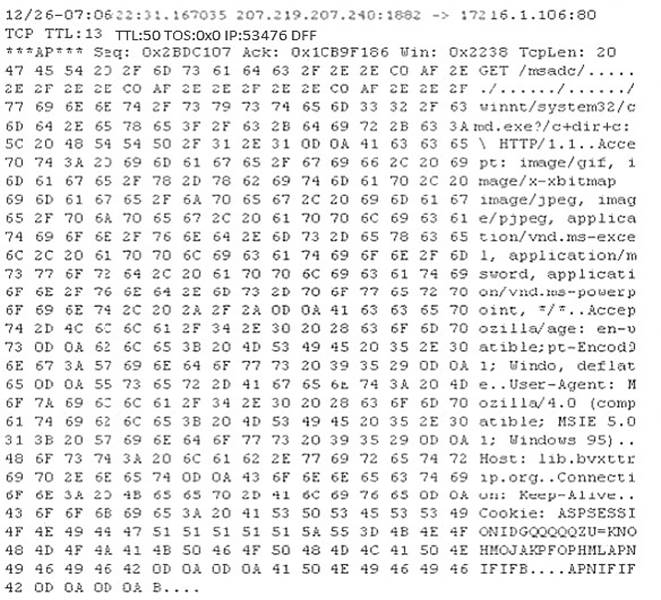
- A. Hexcode Attack
- B. Cross Site Scripting
- C. Multiple Domain Traversal Attack
- D. Unicode Directory Traversal Attack
Answer: D
NEW QUESTION 22
......
P.S. Easily pass 312-50v11 Exam with 254 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy 312-50v11 Dumps: https://www.2passeasy.com/dumps/312-50v11/ (254 New Questions)
