we provide Pinpoint EC-Council 312-50v11 study guide which are the best for clearing 312-50v11 test, and to get certified by EC-Council Certified Ethical Hacker Exam (CEH v11). The 312-50v11 Questions & Answers covers all the knowledge points of the real 312-50v11 exam. Crack your EC-Council 312-50v11 Exam with latest dumps, guaranteed!
Also have 312-50v11 free dumps questions for you:
NEW QUESTION 1
Which of the following is assured by the use of a hash?
- A. Authentication
- B. Confidentiality
- C. Availability
- D. Integrity
Answer: D
NEW QUESTION 2
Which of the following statements is FALSE with respect to Intrusion Detection Systems?
- A. Intrusion Detection Systems can be configured to distinguish specific content in network packets
- B. Intrusion Detection Systems can easily distinguish a malicious payload in an encrypted traffic
- C. Intrusion Detection Systems require constant update of the signature library
- D. Intrusion Detection Systems can examine the contents of the data n context of the network protocol
Answer: B
NEW QUESTION 3
A user on your Windows 2000 network has discovered that he can use L0phtcrack to sniff the SMB exchanges which carry user logons. The user is plugged into a hub with 23 other systems.
However, he is unable to capture any logons though he knows that other users are logging in. What do you think is the most likely reason behind this?
- A. There is a NIDS present on that segment.
- B. Kerberos is preventing it.
- C. Windows logons cannot be sniffed.
- D. L0phtcrack only sniffs logons to web servers.
Answer: B
NEW QUESTION 4
Which of the following programming languages is most susceptible to buffer overflow attacks, due to its lack of a built-in bounds checking mechanism?
Code:
#include <string.h> int main(){char buffer[8];
strcpy(buffer, ““11111111111111111111111111111””);} Output: Segmentation fault
- A. C#
- B. Python
- C. Java
- D. C++
Answer: D
NEW QUESTION 5
Based on the following extract from the log of a compromised machine, what is the hacker really trying to steal?
- A. har.txt
- B. SAM file
- C. wwwroot
- D. Repair file
Answer: B
NEW QUESTION 6
Under what conditions does a secondary name server request a zone transfer from a primary name server?
- A. When a primary SOA is higher that a secondary SOA
- B. When a secondary SOA is higher that a primary SOA
- C. When a primary name server has had its service restarted
- D. When a secondary name server has had its service restarted
- E. When the TTL falls to zero
Answer: A
NEW QUESTION 7
How does a denial-of-service attack work?
- A. A hacker prevents a legitimate user (or group of users) from accessing a service
- B. A hacker uses every character, word, or letter he or she can think of to defeat authentication
- C. A hacker tries to decipher a password by using a system, which subsequently crashes the network
- D. A hacker attempts to imitate a legitimate user by confusing a computer or even another person
Answer: A
NEW QUESTION 8
You have gained physical access to a Windows 2008 R2 server which has an accessible disc drive. When you attempt to boot the server and log in, you are unable to guess the password. In your toolkit, you have an Ubuntu 9.10 Linux LiveCD. Which Linux-based tool can change any user’s password or activate disabled Windows accounts?
- A. John the Ripper
- B. SET
- C. CHNTPW
- D. Cain & Abel
Answer: C
NEW QUESTION 9
Which of the following is the best countermeasure to encrypting ransomwares?
- A. Use multiple antivirus softwares
- B. Pay a ransom
- C. Keep some generation of off-line backup
- D. Analyze the ransomware to get decryption key of encrypted data
Answer: C
NEW QUESTION 10
Every company needs a formal written document which spells out to employees precisely what they are allowed to use the company's systems for, what is prohibited, and what will happen to them if they break the rules. Two printed copies of the policy should be given to every employee as soon as possible after they join the organization. The employee should be asked to sign one copy, which should be safely filed by the company. No one should be allowed to use the company's computer systems until they have signed the policy in acceptance of its terms.
What is this document called?
- A. Information Audit Policy (IAP)
- B. Information Security Policy (ISP)
- C. Penetration Testing Policy (PTP)
- D. Company Compliance Policy (CCP)
Answer: B
NEW QUESTION 11
An attacker runs netcat tool to transfer a secret file between two hosts.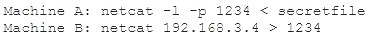
He is worried about information being sniffed on the network.
How would the attacker use netcat to encrypt the information before transmitting onto the wire?
- A. Machine A: netcat -l -p -s password 1234 < testfileMachine B: netcat <machine A IP> 1234
- B. Machine A: netcat -l -e magickey -p 1234 < testfileMachine B: netcat <machine A IP> 1234
- C. Machine A: netcat -l -p 1234 < testfile -pw passwordMachine B: netcat <machine A IP> 1234 -pw password
- D. Use cryptcat instead of netcat
Answer: D
NEW QUESTION 12
Which of the following is the structure designed to verify and authenticate the identity of individuals within the enterprise taking part in a data exchange?
- A. SOA
- B. biometrics
- C. single sign on
- D. PKI
Answer: D
NEW QUESTION 13
Study the snort rule given below and interpret the rule. alert tcp any any --> 192.168.1.0/24 111 (content:"|00 01 86 a5|"; msG. "mountd access";)
- A. An alert is generated when a TCP packet is generated from any IP on the 192.168.1.0 subnet and destined to any IP on port 111
- B. An alert is generated when any packet other than a TCP packet is seen on the network and destined for the 192.168.1.0 subnet
- C. An alert is generated when a TCP packet is originated from port 111 of any IP address to the 192.168.1.0 subnet
- D. An alert is generated when a TCP packet originating from any IP address is seen on the network and destined for any IP address on the 192.168.1.0 subnet on port 111
Answer: D
NEW QUESTION 14
What does the following command in netcat do? nc -l -u -p55555 < /etc/passwd
- A. logs the incoming connections to /etc/passwd file
- B. loads the /etc/passwd file to the UDP port 55555
- C. grabs the /etc/passwd file when connected to UDP port 55555
- D. deletes the /etc/passwd file when connected to the UDP port 55555
Answer: C
NEW QUESTION 15
Bob is going to perform an active session hijack against Brownies Inc. He has found a target that allows session oriented connections (Telnet) and performs the sequence prediction on the target operating system. He manages to find an active session due to the high level of traffic on the network. What is Bob supposed to do next?
- A. Take over the session
- B. Reverse sequence prediction
- C. Guess the sequence numbers
- D. Take one of the parties offline
Answer: C
NEW QUESTION 16
User A is writing a sensitive email message to user B outside the local network. User A has chosen to use PKI to secure his message and ensure only user B can read the sensitive email. At what layer of the OSI layer does the encryption and decryption of the message take place?
- A. Application
- B. Transport
- C. Session
- D. Presentation
Answer: D
NEW QUESTION 17
You are trying to break into a highly classified top-secret mainframe computer with highest security system in place at Merclyn Barley Bank located in Los Angeles.
You know that conventional hacking doesn't work in this case, because organizations such as banks are generally tight and secure when it comes to protecting their systems.
In other words, you are trying to penetrate an otherwise impenetrable system. How would you proceed?
- A. Look for "zero-day" exploits at various underground hacker websites in Russia and China and buy the necessary exploits from these hackers and target the bank's network
- B. Try to hang around the local pubs or restaurants near the bank, get talking to a poorly-paid or disgruntled employee, and offer them money if they'll abuse their access privileges by providing you with sensitive information
- C. Launch DDOS attacks against Merclyn Barley Bank's routers and firewall systems using 100, 000 or more "zombies" and "bots"
- D. Try to conduct Man-in-the-Middle (MiTM) attack and divert the network traffic going to the Merclyn Barley Bank's Webserver to that of your machine using DNS Cache Poisoning techniques
Answer: B
NEW QUESTION 18
Identify the web application attack where the attackers exploit vulnerabilities in dynamically generated web pages to inject client-side script into web pages viewed by other users.
- A. LDAP Injection attack
- B. Cross-Site Scripting (XSS)
- C. SQL injection attack
- D. Cross-Site Request Forgery (CSRF)
Answer: B
NEW QUESTION 19
Which of the following is not a Bluetooth attack?
- A. Bluedriving
- B. Bluesmacking
- C. Bluejacking
- D. Bluesnarfing
Answer: A
NEW QUESTION 20
Tess King is using the nslookup command to craft queries to list all DNS information (such as Name Servers, host names, MX records, CNAME records, glue records (delegation for child Domains), zone serial number, TimeToLive (TTL) records, etc) for a Domain.
What do you think Tess King is trying to accomplish? Select the best answer.
- A. A zone harvesting
- B. A zone transfer
- C. A zone update
- D. A zone estimate
Answer: B
NEW QUESTION 21
What is one of the advantages of using both symmetric and asymmetric cryptography in SSL/TLS?
- A. Supporting both types of algorithms allows less-powerful devices such as mobile phones to use symmetric encryption instead.
- B. Symmetric algorithms such as AES provide a failsafe when asymmetric methods fail.
- C. Symmetric encryption allows the server to security transmit the session keys out-of-band.
- D. Asymmetric cryptography is computationally expensive in compariso
- E. However, it is well-suited to securely negotiate keys for use with symmetric cryptography.
Answer: A
NEW QUESTION 22
......
Recommend!! Get the Full 312-50v11 dumps in VCE and PDF From Dumps-files.com, Welcome to Download: https://www.dumps-files.com/files/312-50v11/ (New 254 Q&As Version)
