Master the 312-50v12 Certified Ethical Hacker Exam (CEHv12) content and be ready for exam day success quickly with this Ucertify 312-50v12 exam topics. We guarantee it!We make it a reality and give you real 312-50v12 questions in our EC-Council 312-50v12 braindumps.Latest 100% VALID EC-Council 312-50v12 Exam Questions Dumps at below page. You can use our EC-Council 312-50v12 braindumps and pass your exam.
EC-Council 312-50v12 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed?
- A. Reverse Social Engineering
- B. Tailgating
- C. Piggybacking
- D. Announced
Answer: B
Explanation:
· Identifying operating systems, services, protocols and devices,
· Collecting unencrypted information about usernames and passwords,
· Capturing network traffic for further analysis
are passive network sniffing methods since with the help of them we only receive information and do not make any changes to the target network. When modifying and replaying the captured network traffic, we are already starting to make changes and actively interact with it.
NEW QUESTION 2
A security analyst uses Zenmap to perform an ICMP timestamp ping scan to acquire information related to the current time from the target host machine.
Which of the following Zenmap options must the analyst use to perform the ICMP timestamp ping scan?
- A. -PY
- B. -PU
- C. -PP
- D. -Pn
Answer: C
NEW QUESTION 3
Attacker Simon targeted the communication network of an organization and disabled the security controls of NetNTLMvl by modifying the values of LMCompatibilityLevel, NTLMMinClientSec, and RestrictSendingNTLMTraffic. He then extracted all the non-network logon tokens from all the active processes to masquerade as a legitimate user to launch further attacks. What is the type of attack performed by Simon?
- A. Internal monologue attack
- B. Combinator attack
- C. Rainbow table attack
- D. Dictionary attack
Answer: A
NEW QUESTION 4
Andrew is an Ethical Hacker who was assigned the task of discovering all the active devices hidden by a restrictive firewall in the IPv4 range in a given target network.
Which of the following host discovery techniques must he use to perform the given task?
- A. UDP scan
- B. TCP Maimon scan
- C. arp ping scan
- D. ACK flag probe scan
Answer: C
Explanation:
One of the most common Nmap usage scenarios is scanning an Ethernet LAN. Most LANs, especially those that use the private address range granted by RFC 1918, do not always use the overwhelming majority of IP addresses. When Nmap attempts to send a raw IP packet, such as an ICMP echo request, the OS must determine a destination hardware (ARP) address, such as the target IP, so that the Ethernet frame can be properly addressed. .. This is required to issue a series of ARP requests. This is best illustrated by an example where a ping scan is attempted against an Area Ethernet host. The –send-ip option tells Nmap to send IP-level packets (rather than raw Ethernet), even on area networks. The Wireshark output of the three ARP requests and their timing have been pasted into the session.
Raw IP ping scan example for offline targetsThis example took quite a couple of seconds to finish because the (Linux) OS sent three ARP requests at 1 second intervals before abandoning the host. Waiting for a few seconds is excessive, as long as the ARP response usually arrives within a few milliseconds. Reducing this timeout period is not a priority for OS vendors, as the overwhelming majority of packets are sent to the host that actually exists. Nmap, on the other hand, needs to send packets to 16 million IP s given a target like 10.0.0.0/8. Many targets are pinged in parallel, but waiting 2 seconds each is very delayed.
There is another problem with raw IP ping scans on the LAN. If the destination host turns out to be unresponsive, as in the previous example, the source host usually adds an incomplete entry for that destination IP to the kernel ARP table. ARP tablespaces are finite and some operating systems become unresponsive when full. If Nmap is used in rawIP mode (–send-ip), Nmap may have to wait a few minutes for the ARP cache entry to expire before continuing host discovery.
ARP scans solve both problems by giving Nmap the highest priority. Nmap issues raw ARP requests and handles retransmissions and timeout periods in its sole discretion. The system ARP cache is bypassed. The example shows the difference. This ARP scan takes just over a tenth of the time it takes for an equivalent IP.
Example b ARP ping scan of offline target
In example b, neither the -PR option nor the -send-eth option has any effect. This is often because ARP has a default scan type on the Area Ethernet network when scanning Ethernet hosts that Nmap discovers. This includes traditional wired Ethernet as 802.11 wireless networks. As mentioned above, ARP scanning is not only more efficient, but also more accurate. Hosts frequently block IP-based ping packets, but usually cannot block ARP requests or responses and communicate over the network.Nmap uses ARP instead of all targets on equivalent targets, even if different ping types (such as -PE and -PS) are specified. LAN.. If you do not need to attempt an ARP scan at all, specify –send-ip as shown in Example a “Raw IP Ping Scan for Offline Targets”.
If you give Nmap control to send raw Ethernet frames, Nmap can also adjust the source MAC address. If you have the only PowerBook in your security conference room and a large ARP scan is initiated from an
Apple-registered MAC address, your head may turn to you. Use the –spoof-mac option to spoof the MAC
address as described in the MAC Address Spoofing section.
NEW QUESTION 5
Consider the following Nmap output: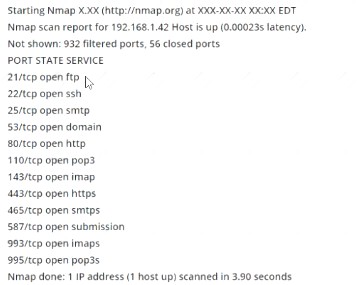
what command-line parameter could you use to determine the type and version number of the web server?
- A. -sv
- B. -Pn
- C. -V
- D. -ss
Answer: A
Explanation:
C:\Users\moi>nmap -h | findstr " -sV" -sV: Probe open ports to determine service/version info
NEW QUESTION 6
infecting a system with malware and using phishing to gain credentials to a system or web application are examples of which phase of the ethical hacking methodology?
- A. Reconnaissance
- B. Maintaining access
- C. Scanning
- D. Gaining access
Answer: D
Explanation:
This phase having the hacker uses different techniques and tools to realize maximum data from the system.
they’re –• Password cracking – Methods like Bruteforce, dictionary attack, rule-based attack, rainbow table a used. Bruteforce is trying all combinations of the password. Dictionary attack is trying an inventory of meaningful words until the password matches. Rainbow table takes the hash value of the password and compares with pre-computed hash values until a match is discovered.• Password attacks – Passive attacks like wire sniffing, replay attack. Active online attack like Trojans, keyloggers, hash injection, phishing. Offline attacks like pre-computed hash, distributed network and rainbow. Non electronic attack like shoulder surfing, social engineering and dumpster diving.
NEW QUESTION 7
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.1.1.3. He also needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router, nobody can access the ftp, and the permitted hosts cannot access the Internet. According to the next configuration, what is happening in the network?
access-list 102 deny tcp any any
access-list 104 permit udp host 10.0.0.3 any
access-list 110 permit tcp host 10.0.0.2 eq www any
access-list 108 permit tcp any eq ftp any
- A. The ACL 104 needs to be first because is UDP
- B. The first ACL is denying all TCP traffic and the other ACLs are being ignored by the router
- C. The ACL for FTP must be before the ACL 110
- D. The ACL 110 needs to be changed to port 80
Answer: B
Explanation:
https://www.cisco.com/c/en/us/support/docs/ip/access-lists/26448-ACLsamples.html
Since the first line prohibits any TCP traffic (access-list 102 deny tcp any any), the lines below will simply be ignored by the router. Below you will find the example from CISCO documentation.
This figure shows that FTP (TCP, port 21) and FTP data (port 20) traffic sourced from NetB destined to NetA is denied, while all other IP traffic is permitted.
Diagram Description automatically generated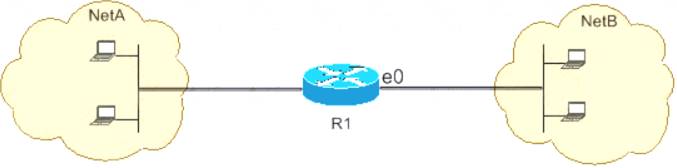
FTP uses port 21 and port 20. TCP traffic destined to port 21 and port 20 is denied and everything else is explicitly permitted. access-list 102 deny tcp any any eq ftp
access-list 102 deny tcp any any eq ftp access-list 102 deny tcp any any eq ftp-data
access-list 102 deny tcp any any eq ftp-data  access-list 102 permit ip any any
access-list 102 permit ip any any
NEW QUESTION 8
Which of the following Google advanced search operators helps an attacker in gathering information about websites that are similar to a specified target URL?
- A. [inurl:]
- B. [related:]
- C. [info:]
- D. [site:]
Answer: B
Explanation:
related:This operator displays websites that are similar or related to the URL specified.
NEW QUESTION 9
Bobby, an attacker, targeted a user and decided to hijack and intercept all their wireless communications. He installed a fake communication tower between two authentic endpoints to mislead the victim. Bobby used this virtual tower to interrupt the data transmission between the user and real tower, attempting to hijack an active session, upon receiving the users request. Bobby manipulated the traffic with the virtual tower and redirected the victim to a malicious website. What is the attack performed by Bobby in the above scenario?
- A. Wardriving
- B. KRACK attack
- C. jamming signal attack
- D. aLTEr attack
Answer: D
Explanation:
aLTEr attacks are usually performed on LTE devices Attacker installs a virtual (fake) communication tower between two authentic endpoints intending to mislead the victim This virtual tower is used to interrupt the data transmission between the user and real tower attempting to hijack the active session.
https://alter-attack.net/media/breaking_lte_on_layer_two.pdf
The new aLTEr attack can be used against nearly all LTE connected endpoints by intercepting traffic and redirecting it to malicious websites together with a particular approach for Apple iOS devices.
This attack works by taking advantage of a style flaw among the LTE network — the information link layer (aka: layer-2) of the LTE network is encrypted with AES-CTR however it’s not integrity-protected, that is why an offender will modify the payload.
As a result, the offender is acting a classic man-in-the-middle wherever they’re movement as a cell tower to the victim.
Diagram Description automatically generated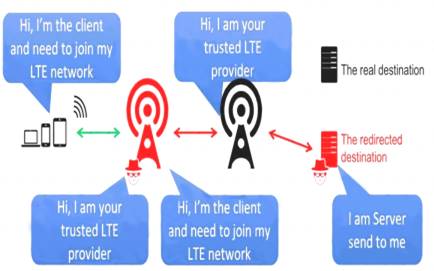
NEW QUESTION 10
At what stage of the cyber kill chain theory model does data exfiltration occur?
- A. Actions on objectives
- B. Weaponization
- C. installation
- D. Command and control
Answer: A
Explanation:
The longer an adversary has this level of access, the greater the impact. Defenders must detect this stage as quickly as possible and deploy tools which can enable them to gather forensic evidence. One example would come with network packet captures, for damage assessment. Only now, after progressing through the primary six phases, can intruders take actions to realize their original objectives. Typically, the target of knowledge exfiltration involves collecting, encrypting and extracting information from the victim(s) environment; violations of knowledge integrity or availability are potential objectives also . Alternatively, and most ordinarily , the intruder may only desire access to the initial victim box to be used as a hop point to compromise additional systems and move laterally inside the network. Once this stage is identified within an environment, the implementation of prepared reaction plans must be initiated. At a minimum, the plan should include a comprehensive communication plan, detailed evidence must be elevated to the very best ranking official or board , the deployment of end-point security tools to dam data loss and preparation for briefing a CIRT Team. Having these resources well established beforehand may be a “MUST” in today’s quickly evolving landscape of cybersecurity threats
NEW QUESTION 11
Bob, a system administrator at TPNQM SA, concluded one day that a DMZ is not needed if he properly configures the firewall to allow access just to servers/ports, which can have direct internet access, and block the access to workstations.
Bob also concluded that DMZ makes sense just when a stateful firewall is available, which is not the case of TPNQM SA.
In this context, what can you say?
- A. Bob can be right since DMZ does not make sense when combined with stateless firewalls
- B. Bob is partially righ
- C. He does not need to separate networks if he can create rules by destination IPs, one by one
- D. Bob is totally wron
- E. DMZ is always relevant when the company has internet servers and workstations
- F. Bob is partially righ
- G. DMZ does not make sense when a stateless firewall is available
Answer: C
NEW QUESTION 12
which of the following information security controls creates an appealing isolated environment for hackers to prevent them from compromising critical targets while simultaneously gathering information about the hacker?
- A. intrusion detection system
- B. Honeypot
- C. BotnetD Firewall
Answer: B
Explanation:
A honeypot may be a trap that an IT pro lays for a malicious hacker, hoping that they will interact with it during a way that gives useful intelligence. It’s one among the oldest security measures in IT, but beware: luring hackers onto your network, even on an isolated system, are often a dangerous game.honeypot may be a good starting place: “A honeypot may be a computer or computing system intended to mimic likely targets of cyberattacks.” Often a honeypot are going to be deliberately configured with known vulnerabilities in situation to form a more tempting or obvious target for attackers. A honeypot won’t contain production data or participate in legitimate traffic on your network — that’s how you’ll tell anything happening within it’s a results of an attack. If someone’s stopping by, they’re up to no good.That definition covers a various array of systems, from bare-bones virtual machines that only offer a couple of vulnerable systems to ornately constructed fake networks spanning multiple servers. and therefore the goals of these who build honeypots can vary widely also , starting from defense thorough to academic research. additionally , there’s now an entire marketing category of deception technology that, while not meeting the strict definition of a honeypot, is certainly within the same family. But we’ll get thereto during a moment.honeypots aim to permit close analysis of how hackers do their dirty work. The team controlling the honeypot can watch the techniques hackers use to infiltrate systems, escalate privileges, and otherwise run amok through target networks. These sorts of honeypots are found out by security companies, academics, and government agencies looking to look at the threat landscape. Their creators could also be curious about learning what kind of attacks are out there, getting details on how specific sorts of attacks work, or maybe trying to lure a specific hackers within the hopes of tracing the attack back to its source. These systems are often inbuilt fully isolated lab environments, which ensures that any breaches don’t end in non-honeypot machines falling prey to attacks.Production honeypots, on the opposite hand, are usually deployed in proximity to some organization’s production infrastructure, though measures are taken to isolate it the maximum amount as possible. These honeypots often serve both as bait to distract hackers who could also be trying to interrupt into that organization’s network, keeping them faraway from valuable data or services; they will also function a canary within the coalpit , indicating that attacks are underway and are a minimum of partially succeeding.
NEW QUESTION 13
Which of the following tools performs comprehensive tests against web servers, including dangerous files and CGIs?
- A. Nikto
- B. John the Ripper
- C. Dsniff
- D. Snort
Answer: A
Explanation:
https://en.wikipedia.org/wiki/Nikto_(vulnerability_scanner)
Nikto is a free software command-line vulnerability scanner that scans web servers for dangerous files/CGIs, outdated server software, and other problems. It performs generic and server types specific checks. It also captures and prints any cookies received. The Nikto code itself is free software, but the data files it uses to drive the program are not.
NEW QUESTION 14
Which regulation defines security and privacy controls for Federal information systems and organizations?
- A. HIPAA
- B. EU Safe Harbor
- C. PCI-DSS
- D. NIST-800-53
Answer: D
Explanation:
NIST Special Publication 800-53 provides a catalog of security and privacy controls for all U.S. federal information systems except those related to national security. It is published by the National Institute of Standards and Technology, which is a non-regulatory agency of the United States Department of Commerce.
NIST develops and issues standards, guidelines, and other publications to assist federal agencies in implementing the Federal Information Security Modernization Act of 2014 (FISMA) and to help with managing cost-effective programs to protect their information and information systems.
NEW QUESTION 15
Study the snort rule given below and interpret the rule. alert tcp any any --> 192.168.1.0/24 111 (content:"|00 01 86 a5|"; msG. "mountd access";)
- A. An alert is generated when a TCP packet is generated from any IP on the 192.168.1.0 subnet and destined to any IP on port 111
- B. An alert is generated when any packet other than a TCP packet is seen on the network and destined for the 192.168.1.0 subnet
- C. An alert is generated when a TCP packet is originated from port 111 of any IP address to the 192.168.1.0 subnet
- D. An alert is generated when a TCP packet originating from any IP address is seen on the network and destined for any IP address on the 192.168.1.0 subnet on port 111
Answer: D
NEW QUESTION 16
A company’s policy requires employees to perform file transfers using protocols which encrypt traffic. You suspect some employees are still performing file transfers using unencrypted protocols because the employees do not like changes. You have positioned a network sniffer to capture traffic from the laptops used by employees in the data ingest department. Using Wireshark to examine the captured traffic, which command can be used as display filter to find unencrypted file transfers?
- A. tcp.port = = 21
- B. tcp.port = 23
- C. tcp.port = = 21 | | tcp.port = =22
- D. tcp.port ! = 21
Answer: A
NEW QUESTION 17
Bella, a security professional working at an it firm, finds that a security breach has occurred while transferring important files. Sensitive data, employee usernames. and passwords are shared In plaintext, paving the way for hackers 10 perform successful session hijacking. To address this situation. Bella Implemented a protocol that sends data using encryption and digital certificates. Which of the following protocols Is used by Bella?
- A. FTP
- B. HTTPS
- C. FTPS
- D. IP
Answer: C
Explanation:
The File Transfer Protocol (FTP) is a standard organization convention utilized for the exchange of PC records from a worker to a customer on a PC organization. FTP is based on a customer worker model engineering utilizing separate control and information associations between the customer and the server.[1] FTP clients may validate themselves with an unmistakable book sign-in convention, ordinarily as a username and secret key, however can interface namelessly if the worker is designed to permit it. For secure transmission that ensures the username and secret phrase, and scrambles the substance, FTP is frequently made sure about with SSL/TLS (FTPS) or supplanted with SSH File Transfer Protocol (SFTP).
The primary FTP customer applications were order line programs created prior to working frameworks had graphical UIs, are as yet dispatched with most Windows, Unix, and Linux working systems.[2][3] Many FTP customers and mechanization utilities have since been created for working areas, workers, cell phones, and equipment, and FTP has been fused into profitability applications, for example, HTML editors.
NEW QUESTION 18
A technician is resolving an issue where a computer is unable to connect to the Internet using a wireless access point. The computer is able to transfer files locally to other machines, but cannot successfully reach the Internet. When the technician examines the IP address and default gateway they are both on the 192.168.1.0/24. Which of the following has occurred?
- A. The computer is not using a private IP address.
- B. The gateway is not routing to a public IP address.
- C. The gateway and the computer are not on the same network.
- D. The computer is using an invalid IP address.
Answer: B
Explanation:
https://en.wikipedia.org/wiki/Private_network
In IP networking, a private network is a computer network that uses private IP address space. Both the IPv4 and the IPv6 specifications define private IP address ranges. These addresses are commonly used for local area networks (LANs) in residential, office, and enterprise environments.
Private network addresses are not allocated to any specific organization. Anyone may use these addresses without approval from regional or local Internet registries. Private IP address spaces were originally defined to assist in delaying IPv4 address exhaustion. IP packets originating from or addressed to a private IP address cannot be routed through the public Internet.
The Internet Engineering Task Force (IETF) has directed the Internet Assigned Numbers Authority (IANA) to reserve the following IPv4 address ranges for private networks:
· 10.0.0.0 – 10.255.255.255
· 172.16.0.0 – 172.31.255.255
· 192.168.0.0 – 192.168.255.255
Backbone routers do not allow packets from or to internal IP addresses. That is, intranet machines, if no measures are taken, are isolated from the Internet. However, several technologies allow such machines to connect to the Internet.
· Mediation servers like IRC, Usenet, SMTP and Proxy server
· Network address translation (NAT)
· Tunneling protocol
NOTE: So, the problem is just one of these technologies.
NEW QUESTION 19
The security team of Debry Inc. decided to upgrade Wi-Fi security to thwart attacks such as dictionary attacks and key recovery attacks. For this purpose, the security team started implementing cutting-edge technology that uses a modern key establishment protocol called the simultaneous authentication of equals (SAE), also known as dragonfly key exchange, which replaces the PSK concept. What is the Wi-Fi encryption technology implemented by Debry Inc.?
- A. WEP
- B. WPA
- C. WPA2
- D. WPA3
Answer: C
NEW QUESTION 20
What is not a PCI compliance recommendation?
- A. Use a firewall between the public network and the payment card data.
- B. Use encryption to protect all transmission of card holder data over any public network.
- C. Rotate employees handling credit card transactions on a yearly basis to different departments.
- D. Limit access to card holder data to as few individuals as possible.
Answer: C
Explanation:
https://www.pcisecuritystandards.org/pci_security/maintaining_payment_security Build and Maintain a Secure Network
* 1. Install and maintain a firewall configuration to protect cardholder data.
* 2. Do not use vendor-supplied defaults for system passwords and other security parameters.
Protect Cardholder Data
* 3. Protect stored cardholder data.
* 4. Encrypt transmission of cardholder data across open, public networks.
Maintain a Vulnerability Management Program
* 5. Use and regularly update anti-virus software or programs.
* 6. Develop and maintain secure systems and applications.
Implement Strong Access Control Measures
* 7. Restrict access to cardholder data by business need-to-know.
* 8. Assign a unique ID to each person with computer access.
* 9. Restrict physical access to cardholder data.
Regularly Monitor and Test Networks
* 10. Track and monitor all access to network resources and cardholder data.
* 11. Regularly test security systems and processes.
Maintain an Information Security Policy
* 12. Maintain a policy that addresses information security for employees and contractors.
NEW QUESTION 21
......
Thanks for reading the newest 312-50v12 exam dumps! We recommend you to try the PREMIUM Thedumpscentre.com 312-50v12 dumps in VCE and PDF here: https://www.thedumpscentre.com/312-50v12-dumps/ (503 Q&As Dumps)
