Pass4sure C2150-612 Questions are updated and all C2150-612 answers are verified by experts. Once you have completely prepared with our C2150-612 exam prep kits you will be ready for the real C2150-612 exam without a problem. We have Renewal IBM C2150-612 dumps study guide. PASSED C2150-612 First attempt! Here What I Did.
NEW QUESTION 1
What is the correct procedure to both assign and add a note to an offense from the Graphical User Interface (GUI)?
- A. Both tasks must be done independently and can only be done on the Offenses Tab
- B. With the new release of 7.2.6 this can now be done in one step from the Offenses Tab only.
- C. Both tasks must be done independently but can be completed from both the Offenses Tab and the Offense Summary Page.
- D. With the new release of 7.2.6 this can now be done in one step, both from the Offenses Tab and the Offense Summary Page.
Answer: D
NEW QUESTION 2
Which Anomaly Detection Rule type can test events or flows of activity that are greater than or less than a specified range?
- A. Outlier Rule
- B. Anomaly Rule
- C. Threshold Rule
- D. Behavioral Rule
Answer: B
NEW QUESTION 3
Which three log sources are supported by QRadar? (Choose three.)
- A. Log files via SFTP
- B. Barracuda Web Filter
- C. TLS multiline Filter
- D. Oracle Database Listener
- E. Sourcefire Defense Center
- F. Java Database Connectivity (JDBC)
Answer: DEF
NEW QUESTION 4
Given the following supplied payload of a supported Juniper device: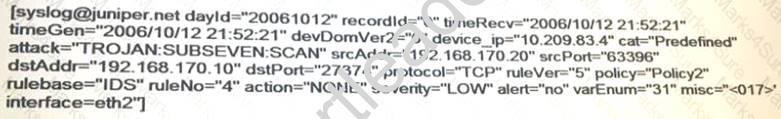
Which QRadar normalized fields will be populated?
- A. Policy, Attack, Source IP, Username
- B. Source IP, Destination I
- C. Destination Port, Protocol
- D. Source Port, Destination Port, Domain, Source Bytes
- E. Source IP, Destination IP, Destination Por
- F. Destination Bytes
Answer: B
NEW QUESTION 5
How is an event magnitude calculated?
- A. As the sum of the three properties Severity, Credibility and Relevance of the Event
- B. As the sum of the three properties Severity, Credibility and Importance of the Event
- C. As a weighted mean of the three properties Severity, Credibility and Relevance of the Event
- D. As a weighted mean of the three properties Severity, Credibility and Importance of the Event
Answer: C
NEW QUESTION 6
What is the difference between TCP and UDP?
- A. They use different port number ranges
- B. UDP is connectionless, whereas TCP is connection based
- C. TCP is connectionless, whereas UDP is connection based
- D. TCP runs on the application layer and UDP uses the Transport layer
Answer: B
NEW QUESTION 7
A Security Analyst found multiple connection attempts from suspicious remote IP addresses to a local host on the DMZ over port 80. After checking related events no successful exploits were detected.
Upon checking international documentation, this activity was part of an expected penetration test which requires no immediate investigation.
How can the Security Analyst ensure results of the penetration test are retained?
- A. Hide the offense and add a note with a reference to the penetration test findings
- B. Protect the offense to not allow it to delete automatically after the offense retention period has elapsed
- C. Close the offense and mark the source IP for Follow-Up to check if there are future events from the host
- D. Email the Offense Summary to the penetration team so they have the offense id, add a note, and close the Offense
Answer: B
Explanation:
References:
http://www.ibm.com/support/knowledgecenter/SSKMKU/com.ibm.qradar.doc/c_qradar_Off_Retention.html
NEW QUESTION 8
Which two high level Event Categories are used by QRadar? (Choose two.)
- A. Policy
- B. Direction
- C. Localization
- D. Justification
- E. Authentication
Answer: AE
NEW QUESTION 9
When QRadar processes an event it extracts normalized properties and custom properties. Which list includes only Normalized properties?
- A. Start time, Source IP, Username, Unix Filename
- B. Start time, Username, Unix Filename, RACF Profile
- C. Start time, Low Level Category, Source IP, Username
- D. Low Level Category, Source IP, Username, RACF Profile
Answer: C
NEW QUESTION 10
What is the purpose of coalescing?
- A. To reduce the number of events which count against EPS licenses
- B. To reduce the amount of data received by QRadar event collectors
- C. To reduce the amount of data going through the pipeline and stored onto disk
- D. To reduce the number of offenses generated by QRadar as part of the tun.ng process
Answer: A
NEW QUESTION 11
Which QRadar component provides the user interface that delivers real-time flow views?
- A. QRadar Viewer
- B. QRadar Console
- C. QRadar Flow Collector
- D. QRadar Flow Processor
Answer: B
Explanation:
References:
http://www.ibm.com/support/knowledgecenter/en/SS42VS_7.2.7/com.ibm.qradar.doc/shc_qradar_comps.html
NEW QUESTION 12
What is a Device Support Module (DSM) function within QRadar?
- A. Unites data received from logs
- B. Provides Vendor specific configuration information
- C. Scans log information based on a set of rules to output offenses
- D. Parses event information for SIEM products received from external sources
Answer: D
NEW QUESTION 13
What is the definition of asset profile on QRadar?
- A. It is any network endpoint that sends or receives data across a network infrastructure.
- B. It is all the information that IBM Security QRadar SIEM collected over time about a specific asset.
- C. It is the information servers and hosts in a network provide to assist users when resolving security issues.
- D. It is an application used to configure and distribute settings to devices and computers in an organization, school, or business.
Answer: B
NEW QUESTION 14
Which approach allows a rule to test for Active Directory (AD) group membership?
- A. Import the AD membership information into the Asset Database using AXIS and use an asset rule test
- B. Use the built-in LDAP integration to execute a search for each event as it is received by the EventProcessor to test for group membership
- C. Maintain reference data for the AD group(s) of interest containing lists of usernames and then add rule tests to see if the normalized username is in the reference data
- D. Export the AD group membership information to a CSV file and place it inthe /store/AD_mapping.csv file on the console, then use the "is a member of AD group' test in the rule
Answer: B
NEW QUESTION 15
What is the default reason for closing an Offense within QRadar?
- A. Actioned
- B. Non-Issue
- C. Blocked Traffic
- D. Acceptable Traffic
Answer: B
Explanation:
References:
https://www.ibm.com/support/knowledgecenter/SS42VS_7.2.1/com.ibm.qradar.doc_7.2.1/t_qradar_closing_offe
NEW QUESTION 16
What is the default view when a user first logs in to QRadar?
- A. Report Tab
- B. Offense Tab
- C. Dashboard tab
- D. Messages menu
Answer: C
Explanation:
References:
http://www.ibm.com/support/knowledgecenter/SSKMKU/com.ibm.qradar.doc/c_qradar_dash_tab.html
NEW QUESTION 17
A Security Analyst is looking on the Assets Tab at an asset with offenses associated to it.
With a "Right Click" on the IP address, where could the Security Analyst go to obtain all offenses associated with it?
- A. Information > Asset Profile
- B. Navigate > View by Network
- C. Run Vulnerability Scan > Source offenses
- D. Navigate > View Source Summary or Destination Summary
Answer: C
NEW QUESTION 18
What is a primary goal with the use of building blocks?
- A. A method to create reusable rule responses
- B. A reusable test stack that can be used in other rules
- C. A method to generate reference set updates without using a rule
- D. A method to create new events back into the pipeline without using a rule
Answer: B
NEW QUESTION 19
Which three options are available on the New Search on the My Offenses and All Offenses pages (Choose three.)
- A. Notes
- B. Source IP
- C. Magnitude
- D. Attack Name
- E. Malware Name
- F. Specific Interval
Answer: BDF
NEW QUESTION 20
Which advantage of a report helps distinguish it from a search?
- A. Scheduling is available.
- B. It can be added as a dashboard item.
- C. It can be labeled for later use.
- D. A report can be assigned to specific users.
Answer: A
NEW QUESTION 21
What is indicated by an event on an existing log in QRadar that has a Low Level Category of “Unknown”?
- A. That event could not be parsed
- B. That event arrived out of order from the original device
- C. That event was from a device that is not supported by QRadar
- D. That the event was parsed, but not mapped to an existing QRadar category
Answer: D
Explanation:
References:
https://www.ibm.com/support/knowledgecenter/SSKMKU/com.ibm.dsm.doc/c_DSM_guide_UniversalLEEF_e
NEW QUESTION 22
What are two characteristics of a SIEM? (Choose two.)
- A. Log Management
- B. System Deployment
- C. Endpoint Software patching
- D. Enterprise User management
- E. Event Normalization & Correlation
Answer: AE
NEW QUESTION 23
What is the largest differentiator between a flow and event?
- A. Events occur at a moment in time while flows have a duration.
- B. Events can be forwarded to another destination, but flows cannot.
- C. Events allow for the creation of custom properties, but flows cannot.
- D. Flows only contribute to local correlated rules, while events are global.
Answer: A
NEW QUESTION 24
......
Recommend!! Get the Full C2150-612 dumps in VCE and PDF From Exambible, Welcome to Download: https://www.exambible.com/C2150-612-exam/ (New 106 Q&As Version)
