It is more faster and easier to pass the CompTIA CAS-003 exam by using Download CompTIA CompTIA Advanced Security Practitioner (CASP) questuins and answers. Immediate access to the Improved CAS-003 Exam and find the same core area CAS-003 questions with professionally verified answers, then PASS your exam with a high score now.
Online CompTIA CAS-003 free dumps demo Below:
NEW QUESTION 1
Ann, a systems engineer, is working to identify an unknown node on the corporate network. To begin
her investigative work, she runs the following nmap command string: user@hostname:~$ sudo nmap –O 192.168.1.54
Based on the output, nmap is unable to identify the OS running on the node, but the following ports are open on the device:
TCP/22 TCP/111 TCP/512-514 TCP/2049 TCP/32778
Based on this information, which of the following operating systems is MOST likely running on the unknown node?
- A. Linux
- B. Windows
- C. Solaris
- D. OSX
Answer: C
Explanation:
TCP/22 is used for SSH; TCP/111 is used for Sun RPC; TCP/512-514 is used by CMD like exec, but automatic authentication is performed as with a login server, etc. These are all ports that are used when making use of the Sun Solaris operating system.
Incorrect Answers:
A: Linux operating system will not use those TCP ports.
B: The Windows Operating system makes use of different TCP ports. D: The OSX operating system makes use of other TCP ports. References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, p. 174
https://www.iana.org/assignments/service-names-port-numbers/service-names-portnumberHYPERLINK "https://www.iana.org/assignments/service-names-port-numbers/servicenames-
port-numbers.xml"s.xml https://en.wikipedia.org/wiki/Solaris_%28operating_sysHYPERLINK "https://en.wikipedia.org/wiki/Solaris_(operating_system)"tem%29 https://nmap.org/book/inst-windows.html
NEW QUESTION 2
An organization has decided to reduce labor costs by outsourcing back office processing of credit applications to a provider located in another country. Data sovereignty and privacy concerns raised by the security team resulted in the third-party provider only accessing and processing the data via remote desktop sessions. To facilitate communications and improve productivity, staff at the third party has been provided with corporate email accounts that are only accessible via the remote
desktop sessions. Email forwarding is blocked and staff at the third party can only communicate with staff within the organization. Which of the following additional controls should be implemented to prevent data loss? (Select THREE).
- A. Implement hashing of data in transit
- B. Session recording and capture
- C. Disable cross session cut and paste
- D. Monitor approved credit accounts
- E. User access audit reviews
- F. Source IP whitelisting
Answer: CEF
Explanation:
Data sovereignty is a legal concern where the data is governed by the laws of the country in which the data resides. In this scenario the company does not want the data to fall under the law of the country of the organization to whom back office process has be outsourced to. Therefore we must ensure that data can only be accessed on local servers and no copies are held on computers of the outsource partner. It is important therefore to prevent cut and paste operations.
Privacy concerns can be addressed by ensuring the unauthorized users do not have access to the dat
A. This can be accomplished though user access auditing, which needs to be reviewed on an ongoing basis; and source IP whitelisting, which is a list of IP addresses that are explicitly allowed access to the system.
Incorrect Answers:
A: Hashing is used to ensure data integrity. In other words, it ensures that the data has not been altered and is in its true, original state. This does not address data sovereignty and privacy concerns. B: Session recording and capture would represent an additional potential threat for privacy concerns should an unauthorized user access the recorded session data.
D: The monitoring of approved credit accounts is a processing issue. It is not related to data sovereignty or privacy concerns.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 17-19, 204, 247
NEW QUESTION 3
An IT manager is concerned about the cost of implementing a web filtering solution in an effort to mitigate the risks associated with malware and resulting data leakage. Given that the ARO is twice per year, the ALE resulting from a data leak is $25,000 and the ALE after implementing the web filter is $15,000. The web filtering solution will cost the organization $10,000 per year. Which of the following values is the single loss expectancy of a data leakage event after implementing the web filtering solution?
- A. $0
- B. $7,500
- C. $10,000
- D. $12,500
- E. $15,000
Answer: B
Explanation:
The annualized loss expectancy (ALE) is the product of the annual rate of occurrence (ARO) and the single loss expectancy (SLE). It is mathematically expressed as: ALE = ARO x SLE
Single Loss Expectancy (SLE) is mathematically expressed as: Asset value (AV) x Exposure Factor (EF) SLE = AV x EF - Thus the Single Loss Expectancy (SLE) = ALE/ARO = $15,000 / 2 = $ 7,500 References:
http://www.financeformulas.net/Return_on_Investment.html https://en.wikipedia.org/wiki/Risk_assessment
NEW QUESTION 4
A systems administrator recently joined an organization and has been asked to perform a security assessment of controls on the organization’s file servers, which contain client data from a number of sensitive systems. The administrator needs to compare documented access requirements to the access implemented within the file system.
Which of the following is MOST likely to be reviewed during the assessment? (Select two.)
- A. Access control list
- B. Security requirements traceability matrix
- C. Data owner matrix
- D. Roles matrix
- E. Data design document
- F. Data access policies
Answer: DF
NEW QUESTION 5
An advanced threat emulation engineer is conducting testing against a client’s network. The engineer conducts the testing in as realistic a manner as possible. Consequently, the engineer has been gradually ramping up the volume of attacks over a long period of time. Which of the following combinations of techniques would the engineer MOST likely use in this testing? (Choose three.)
- A. Black box testing
- B. Gray box testing
- C. Code review
- D. Social engineering
- E. Vulnerability assessment
- F. Pivoting
- G. Self-assessment
- H. White teaming
- I. External auditing
Answer: AEF
NEW QUESTION 6
Company A has noticed abnormal behavior targeting their SQL server on the network from a rogue IP
address. The company uses the following internal IP address ranges: 192.10.1.0/24 for the corporate site and 192.10.2.0/24 for the remote site. The Telco router interface uses the 192.10.5.0/30 IP range.
Instructions: Click on the simulation button to refer to the Network Diagram for Company A. Click on Router 1, Router 2, and the Firewall to evaluate and configure each device.
Task 1: Display and examine the logs and status of Router 1, Router 2, and Firewall interfaces.
Task 2: Reconfigure the appropriate devices to prevent the attacks from continuing to target the SQL server and other servers on the corporate network.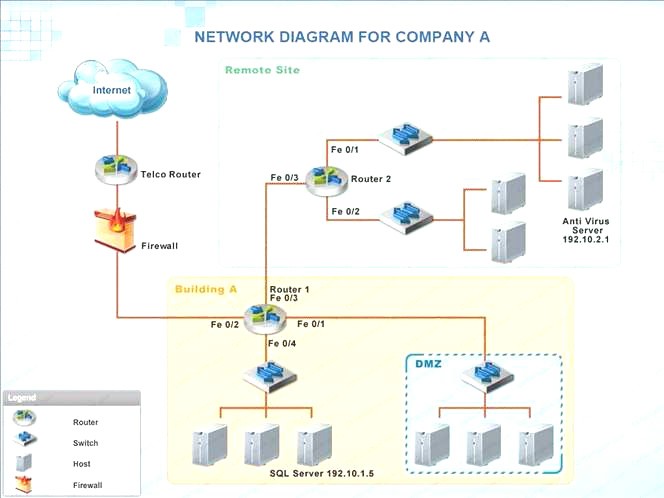
- A. Check the answer below
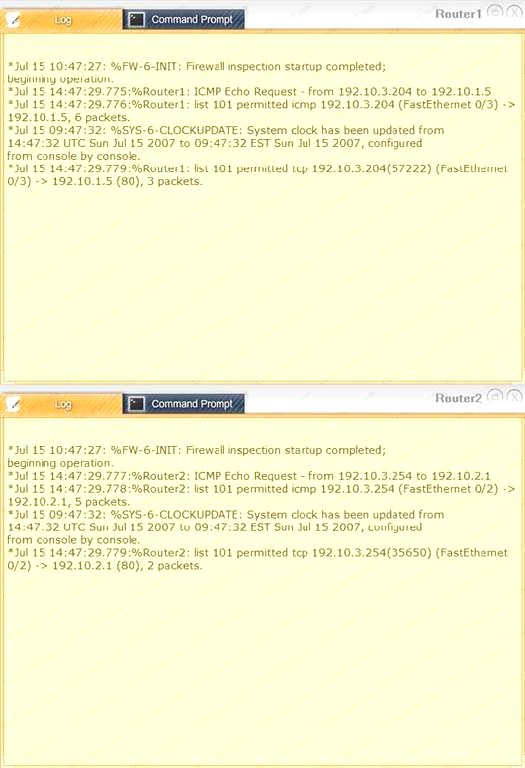
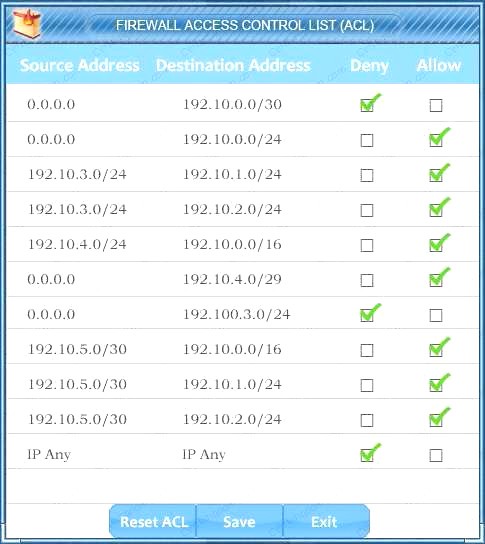
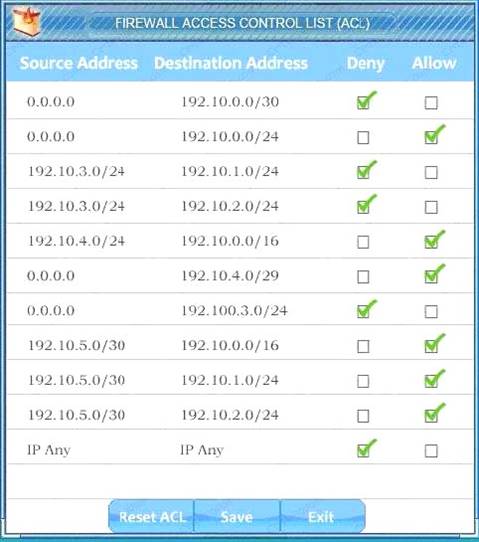 We have traffic coming from two rogue IP addresses: 192.10.3.204 and 192.10.3.254 (both in the 192.10.30.0/24 subnet) going to IPs in the corporate site subnet (192.10.1.0/24) and the remote site subnet (192.10.2.0/24). We need to Deny (block) this traffic at the firewall by ticking the following two checkboxes:
We have traffic coming from two rogue IP addresses: 192.10.3.204 and 192.10.3.254 (both in the 192.10.30.0/24 subnet) going to IPs in the corporate site subnet (192.10.1.0/24) and the remote site subnet (192.10.2.0/24). We need to Deny (block) this traffic at the firewall by ticking the following two checkboxes:
- B. Check the answer below
 We have traffic coming from two rogue IP addresses: 192.10.3.204 and 192.10.3.254 (both in the 192.10.30.0/24 subnet) going to IPs in the corporate site subnet (192.10.1.0/24) and the remote site subnet (192.10.2.0/24). We need to Deny (block) this traffic at the firewall by ticking the following two checkboxes:
We have traffic coming from two rogue IP addresses: 192.10.3.204 and 192.10.3.254 (both in the 192.10.30.0/24 subnet) going to IPs in the corporate site subnet (192.10.1.0/24) and the remote site subnet (192.10.2.0/24). We need to Deny (block) this traffic at the firewall by ticking the following two checkboxes:
Answer: A
NEW QUESTION 7
An agency has implemented a data retention policy that requires tagging data according to type before storing it in the data repository. The policy requires all business emails be automatically deleted after two years. During an open records investigation, information was found on an employee’s work computer concerning a conversation that occurred three years prior and proved damaging to the agency’s reputation. Which of the following MOST likely caused the data leak?
- A. The employee manually changed the email client retention settings to prevent deletion of emails
- B. The file that contained the damaging information was mistagged and retained on the server for longer than it should have been
- C. The email was encrypted and an exception was put in place via the data classification application
- D. The employee saved a file on the computer’s hard drive that contained archives of emails, which were more than two years old
Answer: D
NEW QUESTION 8
A breach was caused by an insider threat in which customer PII was compromised. Following the breach, a lead security analyst is asked to determine which vulnerabilities the attacker used to access company resources. Which of the following should the analyst use to remediate the vulnerabilities?
- A. Protocol analyzer
- B. Root cause analyzer
- C. Behavioral analytics
- D. Data leak prevention
Answer: D
NEW QUESTION 9
A security architect is implementing security measures in response to an external audit that found vulnerabilities in the corporate collaboration tool suite. The report identified the lack of any mechanism to provide confidentiality for electronic correspondence between users and between users and group mailboxes. Which of the following controls would BEST mitigate the identified vulnerability?
- A. Issue digital certificates to all users, including owners of group mailboxes, and enable S/MIME
- B. Federate with an existing PKI provider, and reject all non-signed emails
- C. Implement two-factor email authentication, and require users to hash all email messages upon receipt
- D. Provide digital certificates to all systems, and eliminate the user group or shared mailboxes
Answer: A
NEW QUESTION 10
An SQL database is no longer accessible online due to a recent security breach. An investigation reveals that unauthorized access to the database was possible due to an SQL injection vulnerability. To prevent this type of breach in the future, which of the following security controls should be put in place before bringing the database back online? (Choose two.)
- A. Secure storage policies
- B. Browser security updates
- C. Input validation
- D. Web application firewall
- E. Secure coding standards
- F. Database activity monitoring
Answer: CF
NEW QUESTION 11
A pharmacy gives its clients online access to their records and the ability to review bills and make payments. A new SSL vulnerability on a specific platform was discovered, allowing an attacker to capture the data between the end user and the web server providing these services. After the new vulnerability, it was determined that web services provided are being impacted by this new threat. Which of the following data types MOST likely at risk of exposure based on this new threat? (Select Two)
- A. Cardholder data
- B. Intellectual property
- C. Personal health information
- D. Employee records
- E. Corporate financial data
Answer: AC
NEW QUESTION 12
There have been some failures of the company’s internal facing website. A security engineer has found the WAF to be the root cause of the failures. System logs show that the WAF has been unavailable for 14 hours over the past month, in four separate situations. One of these situations was a two hour scheduled maintenance time, aimed at improving the stability of the WAF. Using the MTTR based on the last month’s performance figures, which of the following calculations is the percentage of uptime assuming there were 722 hours in the month?
- A. 92.24 percent
- B. 98.06 percent
- C. 98.34 percent
- D. 99.72 percent
Answer: B
Explanation:
A web application firewall (WAF) is an appliance, server plugin, or filter that applies a set of rules to an HTTP conversation. Generally, these rules cover common attacks such as cross-site scripting (XSS) and SQL injection. By customizing the rules to your application, many attacks can be identified and blocked.
14h of down time in a period of 772 supposed uptime = 14/772 x 100 = 1.939 % Thus the % of uptime = 100% - 1.939% = 98.06%
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 43, 116
NEW QUESTION 13
A completely new class of web-based vulnerabilities has been discovered. Claims have been made that all common web-based development frameworks are susceptible to attack. Proof-of-concept details have emerged on the Internet. A security advisor within a company has been asked to provide recommendations on how to respond quickly to these vulnerabilities. Which of the following BEST describes how the security advisor should respond?
- A. Assess the reliability of the information source, likelihood of explogtability, and impact to hosted dat
- B. Attempt to explogt via the proof-of-concept cod
- C. Consider remediation options.
- D. Hire an independent security consulting agency to perform a penetration test of the web server
- E. Advise management of any ‘high’ or ‘critical’ penetration test findings and put forward recommendations for mitigation.
- F. Review vulnerability write-ups posted on the Interne
- G. Respond to management with a recommendation to wait until the news has been independently verified by software vendors providing the web application software.
- H. Notify all customers about the threat to their hosted dat
- I. Bring the web servers down into“maintenance mode” until the vulnerability can be reliably mitigated through a vendor patc
Answer: A
Explanation:
The first thing you should do is verify the reliability of the claims. From there you can assess the likelihood of the vulnerability affecting your systems. If it is determined that your systems are likely to be affected by the explogt, you need to determine what impact an attack will have on your hosted dat
A. Now that you know what the impact will be, you can test the explogt by using the proof-ofconcept code. That should help you determine your options for dealing with the threat
(remediation). Incorrect Answers:
B: While penetration testing your system is a good idea, it is unnecessary to hire an independent security consulting agency to perform a penetration test of the web servers. You know what the vulnerability is so you can test it yourself with the proof-of-concept code.
C: Security response should be proactive. Waiting for the threat to be verified by the software vendor will leave the company vulnerable if the vulnerability is real.
D: Bringing down the web servers would prevent the vulnerability but would also render the system useless. Furthermore, customers would expect a certain level of service and may even have a service level agreement in place with guarantees of uptime.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 375-376
NEW QUESTION 14
The risk manager at a small bank wants to use quantitative analysis to determine the ALE of running a business system at a location which is subject to fires during the year. A risk analyst reports to the risk manager that the asset value of the business system is $120,000 and, based on industry data, the exposure factor to fires is only 20% due to the fire suppression system installed at the site. Fires occur in the area on average every four years. Which of the following is the ALE?
- A. $6,000
- B. $24,000
- C. $30,000
- D. $96,000
Answer: A
Explanation:
Single Loss Expectancy (SLE) is mathematically expressed as: Asset value (AV) x Exposure Factor (EF) SLE = AV x EF = $120 000 x 20% = $ 24,000 (this is over 4 years)
Thus ALE = $ 24,000 / 4 = $ 6,000
References: hHYPERLINK
"http://www.financeformulas.net/Return_on_Investment.html"ttp://www.financeformulas.net/Retu rn_on_Investment.htHYPERLINK "http://www.financeformulas.net/Return_on_Investment.html"ml https://en.wikipedia.org/wiki/Risk_assessmeHYPERLINK "https://en.wikipedia.org/wiki/Risk_assessment"nt
Project Management Institute, A Guide to the Project Management Body of Knowledge (PMBOK Guide), 5th Edition, Project Management Institute, Inc., Newtown Square, 2013, p. 198
McMillan, Troy and Robin Abernathy, CompTIA Advanced Security Practitioner (CASP) CAS-002 Cert Guide, Pearson Education, Indianapolis, 2015, p. 305
NEW QUESTION 15
A security administrator is shown the following log excerpt from a Unix system:
2013 Oct 10 07:14:57 web14 sshd[1632]: Failed password for root from 198.51.100.23 port 37914 ssh2
2013 Oct 10 07:14:57 web14 sshd[1635]: Failed password for root from 198.51.100.23 port 37915 ssh2
2013 Oct 10 07:14:58 web14 sshd[1638]: Failed password for root from 198.51.100.23 port 37916 ssh2
2013 Oct 10 07:15:59 web14 sshd[1640]: Failed password for root from 198.51.100.23 port 37918 ssh2
2013 Oct 10 07:16:00 web14 sshd[1641]: Failed password for root from 198.51.100.23 port 37920 ssh2
2013 Oct 10 07:16:00 web14 sshd[1642]: Successful login for root from 198.51.100.23 port 37924 ssh2
Which of the following is the MOST likely explanation of what is occurring and the BEST immediate response? (Select TWO).
- A. An authorized administrator has logged into the root account remotely.
- B. The administrator should disable remote root logins.
- C. Isolate the system immediately and begin forensic analysis on the host.
- D. A remote attacker has compromised the root account using a buffer overflow in sshd.
- E. A remote attacker has guessed the root password using a dictionary attack.
- F. Use iptables to immediately DROP connections from the IP 198.51.100.23.
- G. A remote attacker has compromised the private key of the root account.
- H. Change the root password immediately to a password not found in a dictionar
Answer: CE
Explanation:
The log shows six attempts to log in to a system. The first five attempts failed due to ‘failed password’. The sixth attempt was a successful login. Therefore, the MOST likely explanation of what is occurring is that a remote attacker has guessed the root password using a dictionary attack.
The BEST immediate response is to isolate the system immediately and begin forensic analysis on the host. You should isolate the system to prevent any further access to it and prevent it from doing any damage to other systems on the network. You should perform a forensic analysis on the system to determine what the attacker did on the system after gaining access.
Incorrect Answers:
A: It is unlikely that an authorized administrator has logged into the root account remotely. It is unlikely that an authorized administrator would enter an incorrect password five times.
B: Disabling remote root logins is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
D: The log does not suggest a buffer overflow attack; the failed passwords suggest a dictionary attack. F: Using iptables to immediately DROP connections from the IP 198.51.100.23 is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
G: The log does not suggest a remote attacker has compromised the private key of the root account; the failed passwords suggest a dictionary attack.
H: Changing the root password is a good idea but it is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
NEW QUESTION 16
Compliance with company policy requires a quarterly review of firewall rules. A new administrator is asked to conduct this review on the internal firewall sitting between several internal networks. The intent of this firewall is to make traffic more restrictive. Given the following information answer the questions below:
User Subnet: 192.168.1.0/24 Server Subnet: 192.168.2.0/24 Finance Subnet:192.168.3.0/24 Instructions: To perform the necessary tasks, please modify the DST port, Protocol, Action, and/or Rule Order columns. Firewall ACLs are read from the top down
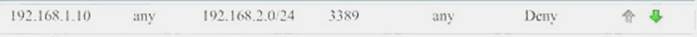
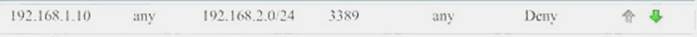
Task 1) An administrator added a rule to allow their machine terminal server access to the server subnet. This rule is not working. Identify the rule and correct this issue.
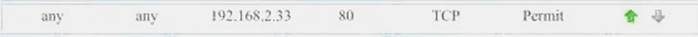
Task 2) All web servers have been changed to communicate solely over SSL. Modify the appropriate rule to allow communications.
Task 3) An administrator added a rule to block access to the SQL server from anywhere on the network. This rule is not working. Identify and correct this issue.
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.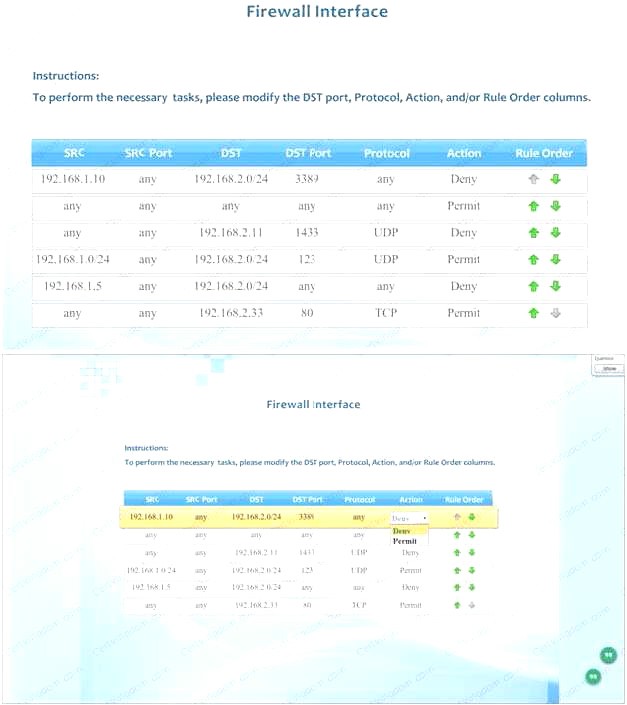
- A. Check the answer below
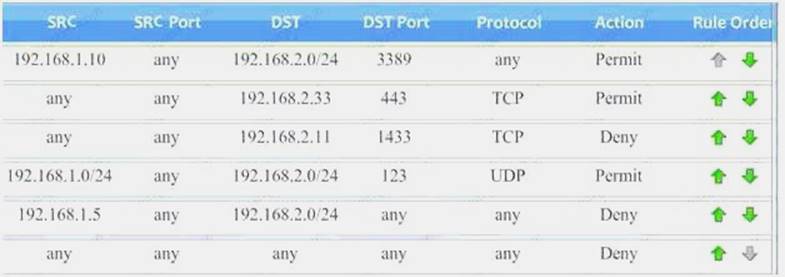 Task 1) An administrator added a rule to allow their machine terminal server access to the server subne
Task 1) An administrator added a rule to allow their machine terminal server access to the server subne - B. This rule is not workin
- C. Identify the rule and correct this issue.The rule shown in the image below is the rule in questio
- D. It is not working because the action is set to Den
- E. This needs to be set to Permit.
 Task 2) All web servers have been changed to communicate solely over SS
Task 2) All web servers have been changed to communicate solely over SS - F. Modify the appropriate rule to allow communications.The web servers rule is shown in the image belo
- G. Port 80 (HTTP) needs to be changed to port 443 for HTTPS (HTTP over SSL).
 Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ
Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ - H. This rule is not workin
- I. Identify and correct this issue.The SQL Server rule is shown in the image belo
- J. It is not working because the protocol is wron
- K. It should be TCP, not UDP.
 Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.The network time rule is shown in the image below.
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.The network time rule is shown in the image below.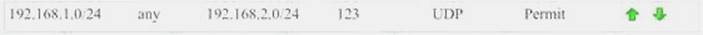 However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul
However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul - L. To block all other traffic, the ‘any’ rule needs to be set to Deny, not Permit and the rule needs to be placed below all the other rules (it needs to be placed atthe bottom of the list to the rule is enumerated last).

- M. Check the answer below
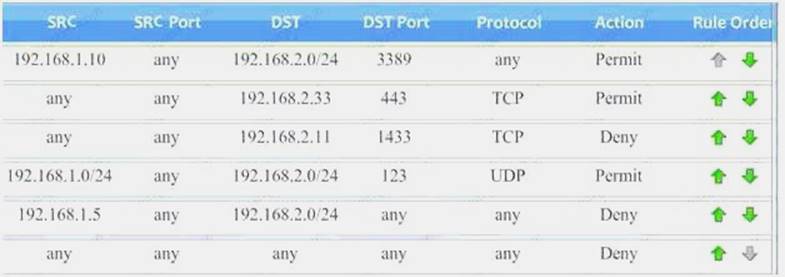 Task 1) An administrator added a rule to allow their machine terminal server access to the server subne
Task 1) An administrator added a rule to allow their machine terminal server access to the server subne - N. This rule is not workin
- O. Identify the rule and correct this issue.The rule shown in the image below is the rule in questio
- P. It is not working because the action is set to Den
- Q. This needs to be set to Permit.
 Task 2) All web servers have been changed to communicate solely over SS
Task 2) All web servers have been changed to communicate solely over SS - R. Modify the appropriate rule to allow communications.The web servers rule is shown in the image belo
- S. Port 80 (HTTP) needs to be changed to port 443 for HTTPS (HTTP over SSL).Task 3) An administrator added a rule to block access to the SQL server from anywhere on the networ
- T. This rule is not workin
- . Identify and correct this issue.The SQL Server rule is shown in the image belo
- . It is not working because the protocol is wron
- . It should be TCP, not UDP.
 Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that noother traffic is allowed.The network time rule is shown in the image below.However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that noother traffic is allowed.The network time rule is shown in the image below.However, this rule is not being used because the ‘any’ rule shown below allows all traffic and the rule is placed above the network time rul - . To block all other traffic, the ‘any’ rule needs to be set to Deny, not Permit and the rule needs to be placed below all the other rules (it needs to be placed atthe bottom of the list to the rule is enumerated last).

Answer: A
NEW QUESTION 17
......
Thanks for reading the newest CAS-003 exam dumps! We recommend you to try the PREMIUM Dumps-hub.com CAS-003 dumps in VCE and PDF here: https://www.dumps-hub.com/CAS-003-dumps.html (555 Q&As Dumps)
