It is more faster and easier to pass the CompTIA CS0-003 exam by using Downloadable CompTIA CompTIA CySA+ Certification Beta Exam questuins and answers. Immediate access to the Renew CS0-003 Exam and find the same core area CS0-003 questions with professionally verified answers, then PASS your exam with a high score now.
Online CompTIA CS0-003 free dumps demo Below:
NEW QUESTION 1
A security analyst is trying to identify anomalies on the network routing. Which of the following functions can the analyst use on a shell script to achieve the objective most accurately?
- A. function x() { info=$(geoiplookup $1) && echo "$1 | $info" }
- B. function x() { info=$(ping -c 1 $1 | awk -F "/" ’END{print $5}’) && echo "$1 | $info" }
- C. function x() { info=$(dig $(dig -x $1 | grep PTR | tail -n 1 | awk -F ".in-addr" ’{print $1} ').origin.asn.cymru.com TXT +short) && echo "$1 | $info" }
- D. function x() { info=$(traceroute -m 40 $1 | awk ‘END{print $1}’) && echo "$1 | $info" }
Answer: C
Explanation:
The function that can be used on a shell script to identify anomalies on the network routing most accurately is:
function x() { info=(dig(dig -x $1 | grep PTR | tail -n 1 | awk -F “.in-addr” ’{print $1} ').origin.asn.cymru.com TXT +short) && echo “$1 | $info” }
This function takes an IP address as an argument and performs two DNS lookups using the dig command. The first lookup uses the -x option to perform a reverse DNS lookup and get the hostname associated with the IP address. The second lookup uses the origin.asn.cymru.com domain to get the autonomous system number (ASN) and other information related to the IP address. The function then prints the IP address and the ASN information, which can help identify any routing anomalies or inconsistencies
NEW QUESTION 2
Which of the following threat-modeling procedures is in the OWASP Web Security Testing Guide?
- A. Review Of security requirements
- B. Compliance checks
- C. Decomposing the application
- D. Security by design
Answer: C
Explanation:
The OWASP Web Security Testing Guide (WSTG) includes a section on threat modeling, which is a structured approach to identify, quantify, and address the security risks associated with an application. The first step in the threat modeling process is decomposing the application, which involves creating use cases, identifying entry points, assets, trust levels, and data flow diagrams for the application. This helps to understand the application and how it interacts with external entities, as well as to identify potential threats and vulnerabilities1. The other options are not part of the OWASP WSTG threat modeling process.
NEW QUESTION 3
A recent zero-day vulnerability is being actively exploited, requires no user interaction or privilege escalation, and has a significant impact to confidentiality and integrity but not to availability. Which of the following CVE metrics would be most accurate for this zero-day threat?
- A. CVSS: 31/AV: N/AC: L/PR: N/UI: N/S: U/C: H/1: K/A: L
- B. CVSS:31/AV:K/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:L
- C. CVSS:31/AV:N/AC:L/PR:N/UI:H/S:U/C:L/I:N/A:H
- D. CVSS:31/AV:L/AC:L/PR:R/UI:R/S:U/C:H/I:L/A:H
Answer: A
Explanation:
This answer matches the description of the zero-day threat. The attack vector is network (AV:N), the attack complexity is low (AC:L), no privileges are required (PR:N), no user interaction is required (UI:N), the scope is unchanged (S:U), the confidentiality and integrity impacts are high (C:H/I:H), and the availability impact is low (A:L). Official References: https://nvd.nist.gov/vuln-metrics/cvss
NEW QUESTION 4
A cryptocurrency service company is primarily concerned with ensuring the accuracy of the data on one of its systems. A security analyst has been tasked with prioritizing vulnerabilities for remediation for the system. The analyst will use the following CVSSv3.1 impact metrics for prioritization: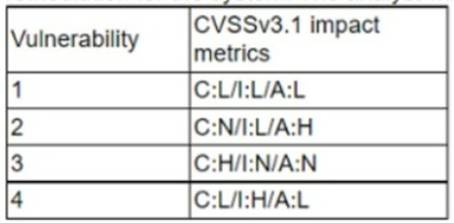
Which of the following vulnerabilities should be prioritized for remediation?
- A. 1
- B. 2
- C. 3
- D. 4
Answer: B
Explanation:
Vulnerability 2 has the highest impact metrics, specifically the highest attack vector (AV) and attack complexity (AC) values. This means that the vulnerability is more likely to be exploited and more difficult to remediate.
References:
✑ CVSS v3.1 Specification Document, section 2.1.1 and 2.1.2
✑ The CVSS v3 Vulnerability Scoring System, section 3.1 and 3.2
NEW QUESTION 5
A penetration tester submitted data to a form in a web application, which enabled the penetration tester to retrieve user credentials. Which of the following should be recommended for remediation of this application vulnerability?
- A. Implementing multifactor authentication on the server OS
- B. Hashing user passwords on the web application
- C. Performing input validation before allowing submission
- D. Segmenting the network between the users and the web server
Answer: C
Explanation:
Performing input validation before allowing submission is the best recommendation for remediation of this application vulnerability. Input validation is a technique that checks the data entered by users or attackers against a set of rules or constraints, such as data type, length, format, or range. Input validation can prevent common web application attacks such as SQL injection, cross-site scripting (XSS), or command injection, which exploit the lack of input validation to execute malicious code or commands on the server or the client side. By validating the input before allowing submission, the web application can reject or sanitize any malicious or unexpected input, and protect the user credentials and other sensitive data from being compromised12. References: Input Validation - OWASP, 4 Most Common Application Vulnerabilities and Possible Remediation
NEW QUESTION 6
An analyst finds that an IP address outside of the company network that is being used to run network and vulnerability scans across external-facing assets. Which of the following steps of an attack framework is the analyst witnessing?
- A. Exploitation
- B. Reconnaissance
- C. Command and control
- D. Actions on objectives
Answer: B
Explanation:
Reconnaissance is the first stage in the Cyber Kill Chain and involves researching potential targets before carrying out any penetration testing. The reconnaissance stage may include identifying potential targets, finding their vulnerabilities, discovering which third parties are connected to them (and what data they can access), and exploring existing entry points as well as finding new ones. Reconnaissance can take place both online and offline. In this case, an analyst finds that an IP address outside of the company network is being used to run network and vulnerability scans across external- facing assets. This indicates that the analyst is witnessing reconnaissance activity by an attacker. Official References: https://www.lockheedmartin.com/en- us/capabilities/cyber/cyber-kill-chain.html
NEW QUESTION 7
A payroll department employee was the target of a phishing attack in which an attacker impersonated a department director and requested that direct deposit information be updated to a new account. Afterward, a deposit was made into the unauthorized account. Which of the following is one of the first actions the incident response team should take when they receive notification of the attack?
- A. Scan the employee's computer with virus and malware tools.
- B. Review the actions taken by the employee and the email related to the event
- C. Contact human resources and recommend the termination of the employee.
- D. Assign security awareness training to the employee involved in the incident.
Answer: B
Explanation:
In case of a phishing attack, it’s crucial to review what actions were taken by the employee and analyze the phishing email to understand its nature and impact.References: CompTIA CySA+ Study Guide: Exam CS0-003, 3rd Edition, Chapter 6, page 246; CompTIA CySA+ CS0-003 Certification Study Guide, Chapter 6, page 255.
NEW QUESTION 8
A security analyst noticed the following entry on a web server log:
Warning: fopen (http://127.0.0.1:16) :
failed to open stream:
Connection refused in /hj/var/www/showimage.php on line 7
Which of the following malicious activities was most likely attempted?
- A. XSS
- B. CSRF
- C. SSRF
- D. RCE
Answer: C
Explanation:
The malicious activity that was most likely attempted is SSRF (Server-Side Request Forgery). This is a type of attack that exploits a vulnerable web application to make requests to other resources on behalf of the web server. In this case, the attacker tried to use the fopen function to access the local loopback address (127.0.0.1) on port 16, which could be a service that is not intended to be exposed to the public. The connection was refused, indicating that the port was closed or filtered. References: CompTIA CySA+ Study Guide: Exam CS0-003, 3rd Edition, Chapter 2: Software and Application Security, page 66.
NEW QUESTION 9
A recent penetration test discovered that several employees were enticed to assist attackers by visiting specific websites and running downloaded files when prompted by phone calls. Which of the following would best address this issue?
- A. Increasing training and awareness for all staff
- B. Ensuring that malicious websites cannot be visited
- C. Blocking all scripts downloaded from the internet
- D. Disabling all staff members' ability to run downloaded applications
Answer: A
Explanation:
Increasing training and awareness for all staff is the best way to address the issue of employees being enticed to assist attackers by visiting specific websites and running downloaded files when prompted by phone calls. This issue is an example of social engineering, which is a technique that exploits human psychology and behavior to manipulate people into performing actions or divulging information that benefit the attackers. Social engineering can take many forms, such as phishing, vishing, baiting, quid pro quo, or impersonation. The best defense against social engineering is to educate and train the staff on how to recognize and avoid common social engineering tactics, such as:
✑ Verifying the identity and legitimacy of the caller or sender before following their instructions or clicking on any links or attachments
✑ Being wary of unsolicited or unexpected requests for information or action, especially if they involve urgency, pressure, or threats
✑ Reporting any suspicious or anomalous activity to the security team or the appropriate authority
✑ Following the organization’s policies and procedures on security awareness and best practices
Official References:
✑ https://partners.comptia.org/docs/default-source/resources/comptia-cysa-cs0-002- exam-objectives
✑ https://www.comptia.org/certifications/cybersecurity-analyst
✑ https://www.comptia.org/blog/the-new-comptia-cybersecurity-analyst-your- questions-answered
NEW QUESTION 10
A SOC manager is establishing a reporting process to manage vulnerabilities. Which of the following would be the best solution to identify potential loss incurred by an issue?
- A. Trends
- B. Risk score
- C. Mitigation
- D. Prioritization
Answer: B
Explanation:
A risk score is a numerical value that represents the potential impact and likelihood of a vulnerability being exploited. It can help to identify the potential loss incurred by an issue and prioritize remediation efforts accordingly. https://www.comptia.org/training/books/cysa-cs0-003-study-guide
NEW QUESTION 11
A company's user accounts have been compromised. Users are also reporting that the company's internal portal is sometimes only accessible through HTTP, other times; it is accessible through HTTPS. Which of the following most likely describes the observed activity?
- A. There is an issue with the SSL certificate causinq port 443 to become unavailable for HTTPS access
- B. An on-path attack is being performed by someone with internal access that forces users into port 80
- C. The web server cannot handle an increasing amount of HTTPS requests so it forwards users to port 80
- D. An error was caused by BGP due to new rules applied over the company's internal routers
Answer: B
Explanation:
An on-path attack is a type of man-in-the-middle attack where an attacker intercepts and modifies network traffic between two parties. In this case, someone with internal access may be performing an on-path attack by forcing users into port 80, which is used for HTTP communication, instead of port 443, which is used for HTTPS communication. This would allow the attacker to compromise the user accounts and access the company’s internal portal.
NEW QUESTION 12
A cybersecurity analyst has recovered a recently compromised server to its previous state. Which of the following should the analyst perform next?
- A. Eradication
- B. Isolation
- C. Reporting
- D. Forensic analysis
Answer: D
Explanation:
After recovering a compromised server to its previous state, the analyst should perform forensic analysis to determine the root cause, impact, and scope of the incident, as well as to identify any indicators of compromise, evidence, or artifacts that can be used for further investigation or prosecution. References: CompTIA CySA+ Study Guide: Exam CS0-003, 3rd Edition, Chapter 6, page 244; CompTIA CySA+ CS0-003 Certification Study Guide, Chapter 6, page 253.
NEW QUESTION 13
Security analysts review logs on multiple servers on a daily basis. Which of the following implementations will give the best central visibility into the events occurring throughout the corporate environment without logging in to the servers individually?
- A. Deploy a database to aggregate the logging.
- B. Configure the servers to forward logs to a SIEM-
- C. Share the log directory on each server to allow local access,
- D. Automate the emailing of logs to the analysts.
Answer: B
Explanation:
The best implementation to give the best central visibility into the events occurring throughout the corporate environment without logging in to the servers individually is B. Configure the servers to forward logs to a SIEM.
A SIEM (Security Information and Event Management) is a security solution that helps organizations detect, analyze, and respond to security threats before they disrupt business1. SIEM tools collect, aggregate, and correlate log data from various sources across an organization’s network, such as applications, devices, servers, and users. SIEM tools also provide real-time alerts, dashboards, reports, and incident response capabilities to help security teams identify and mitigate cyberattacks2345.
By configuring the servers to forward logs to a SIEM, the security analysts can have a central view of potential threats and monitor security incidents across the corporate environment without logging in to the servers individually. This can save time, improve efficiency, and enhance security posture2345.
Deploying a database to aggregate the logging (A) may not provide the same level of analysis, correlation, and alerting as a SIEM tool. Sharing the log directory on each server to allow local access © may not be scalable or secure for a large number of servers. Automating the emailing of logs to the analysts (D) may not be timely or effective for real- time threat detection and response. Therefore, B is the best option among the choices given.
NEW QUESTION 14
During security scanning, a security analyst regularly finds the same vulnerabilities in a critical application. Which of the following recommendations would best mitigate this problem if applied along the SDLC phase?
- A. Conduct regular red team exercises over the application in production
- B. Ensure that all implemented coding libraries are regularly checked
- C. Use application security scanning as part of the pipeline for the CI/CDflow
- D. Implement proper input validation for any data entry form
Answer: C
Explanation:
Application security scanning is a process that involves testing and analyzing applications for security vulnerabilities, such as injection flaws, broken authentication, cross-site scripting, and insecure configuration. Application security scanning can help identify and fix security issues before they become exploitable by attackers. Using application security scanning as part of the pipeline for the continuous integration/continuous delivery (CI/CD) flow can help mitigate the problem of finding the same vulnerabilities in a critical application during security scanning. This is because application security scanning can be integrated into the development lifecycle and performed automatically and frequently as part of the CI/CD process.
NEW QUESTION 15
A security analyst is performing an investigation involving multiple targeted Windows malware binaries. The analyst wants to gather intelligence without disclosing information to the attackers. Which of the following actions would allow the analyst to achieve the objective?
- A. Upload the binary to an air gapped sandbox for analysis
- B. Send the binaries to the antivirus vendor
- C. Execute the binaries on an environment with internet connectivity
- D. Query the file hashes using VirusTotal
Answer: A
Explanation:
The best action that would allow the analyst to gather intelligence without disclosing information to the attackers is to upload the binary to an air gapped sandbox for analysis. An air gapped sandbox is an isolated environment that has no connection to any external network or system. Uploading the binary to an air gapped sandbox can prevent any communication or interaction between the binary and the attackers, as well as any potential harm or infection to other systems or networks. An air gapped sandbox can also allow the analyst to safely analyze and observe the behavior, functionality, or characteristics of the binary.
NEW QUESTION 16
Which of the following is an important aspect that should be included in the lessons-learned step after an incident?
- A. Identify any improvements or changes in the incident response plan or procedures
- B. Determine if an internal mistake was made and who did it so they do not repeat the error
- C. Present all legal evidence collected and turn it over to iaw enforcement
- D. Discuss the financial impact of the incident to determine if security controls are well spent
Answer: A
Explanation:
An important aspect that should be included in the lessons-learned step after an incident is to identify any improvements or changes in the incident response plan or procedures. The lessons-learned step is a process that involves reviewing and evaluating the incident response activities and outcomes, as well as identifying and documenting any strengths, weaknesses, gaps, or best practices. Identifying any improvements or changes in the incident response plan or procedures can help enhance the security posture, readiness, or capability of the organization for future incidents
NEW QUESTION 17
......
P.S. Dumps-hub.com now are offering 100% pass ensure CS0-003 dumps! All CS0-003 exam questions have been updated with correct answers: https://www.dumps-hub.com/CS0-003-dumps.html (150 New Questions)
