we provide Practical Red-Hat EX300 exam fees which are the best for clearing EX300 test, and to get certified by Red-Hat Red Hat Certified Engineer - RHCE (v6+v7). The EX300 Questions & Answers covers all the knowledge points of the real EX300 exam. Crack your Red-Hat EX300 Exam with latest dumps, guaranteed!
Red-Hat EX300 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
There were two systems:
system1, main system on which most of the configuration take place
system2, some configuration here
Configure repository.
Create a Repository for your virtual machines. The URL is http://station.network.0.example.com/content/rhel7.0/x86_64/dvd
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 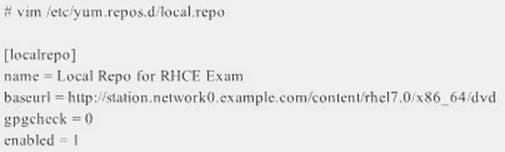
Save and Exit (:wq) Then run this: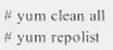
NEW QUESTION 2
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: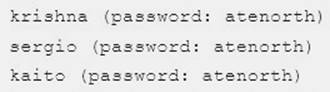
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
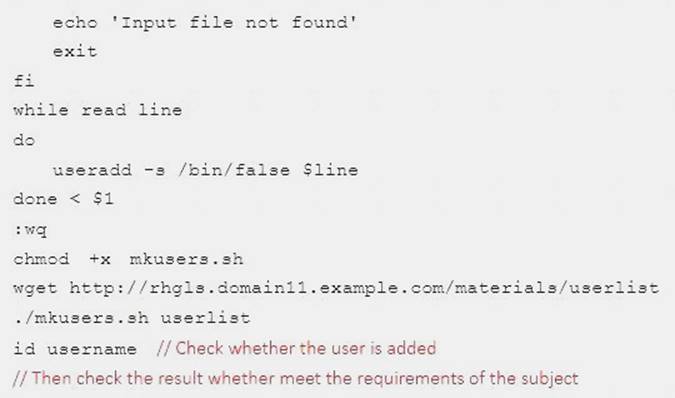
Create a script to add users
Create a script named /root/mkusers on the system1, this script can achieve to add local users for the system1,
and user names of these users are all from a file which contains the usernames list, and meet the following requirements at the same time:
This script is required to provide a parameter; this parameter is the file which contains the usernames list
This script need provide the following message: Usage/root/mkusers if it does not provide a parameter,
then exit and return the corresponding value
This script need provide the following message: Input file not found if it provides a name that does not exist, then exit and return the corresponding value
Create a user shell log into /bin/false
This script does not need to set password for users
You can get the usernames list from the following URL as a test:
http://rhgls. domain11.example.com/materials/ userlist
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 3
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: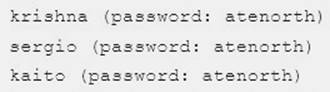
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
Implement/configure a Web Service.
Configure
a site http://systeml. domain11.example.com/ on the system1, then execute the following steps:
(1)
Download file from http://rhgls.domain11.example.com/materials/station.html and rename this files index.html, don’t modify the file contents;
(2) Copy the file index.html to your web server's DocumentRoot directory
(3) Clients from domain group3.example.com can access to this web service
(4) Clients from domain my133t.org deny access to this web service
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
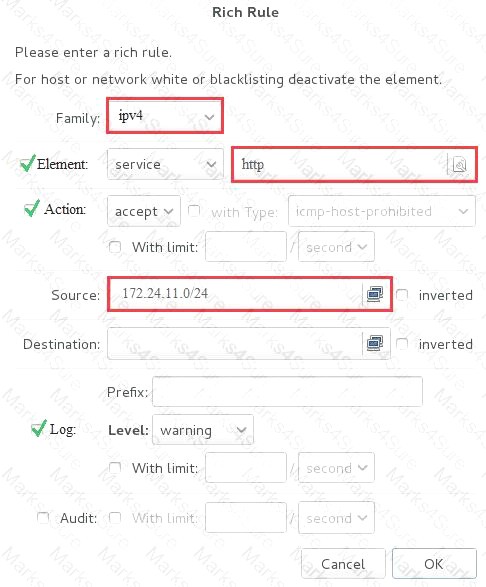
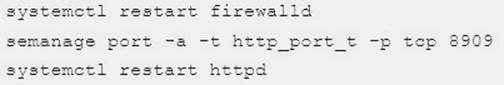
systemctl restart firewalld
NEW QUESTION 4
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: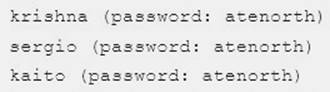
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
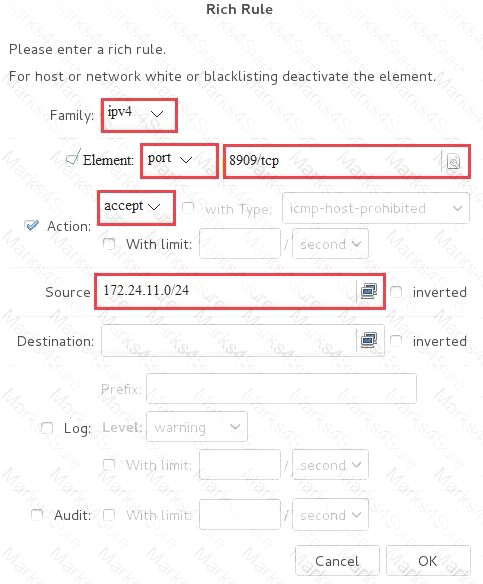
Dynamic WEB content
Configure dynamic web content to provide on the system1, as required:
Dynamic content provided by a virtual machine named dynamic.domain11.example.com
Virtual host listening on port 8909
Download a script from http://rhgls.domain11.example.com/materials/webapp.wsgi, then put it in the right place, don’t modify the file content in any situations
Dynamically
generated web page should be received when clients access http://dynamic.domain11example.com:8909.
This
http:// dynamic.domain11.example.com:8909/ must be able to be accessed by all system of domain11.example.com
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 5
There were two systems:
system1, main system on which most of the configuration take place
system2, some configuration here
Configure NFS mount.
Mount /nfsshare directory on desktopX under /public directory persistently at system boot time.
Mount /nfssecure/protected with krb5p secured share on desktopX beneath /secure/protected provided with keytab station.network0.example.com/pub/keytabs/desktopX.keytab"> http://station.network0.example.com/pub/keytabs/desktopX.keytab
The user harry is able to write files on /secure directory
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 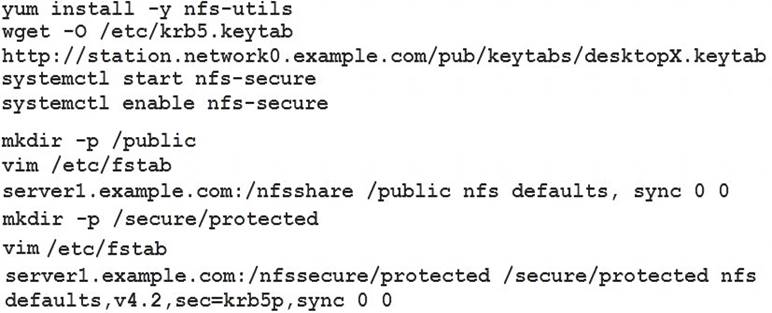
Verification from DesktopX: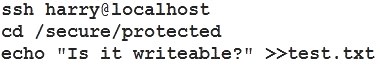
NEW QUESTION 6
Give Full Permission to owner user and owner group member but no permission to others on /data.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
We can change the permission of file/directory either character symbol method or numeric method. Permission:
r-Read w-Write
x-Execute Permission Category u- Owner User g- Owner Group
o- Others Operators
+ -> Add the Permissions
- ->Remove the Permissions = ->Assign the Permissions Numeric Method: 4 -> Read
2 -> Write
1 -> Execute
Total: 7, total for owner user, owner group member and for others: 777
1. chmod u+rwx /data
2 .chmod g+rwx /data
3. chmod o-rwx /data or
chmod 770 /data
4 Verify the /data: ls -ld /data
5. You will get drwxrwx---
NEW QUESTION 7
Whoever creates the file on /data make automatically owner group should be the group owner of /data directory.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
When user creates the file/directory, user owner will be user itself and group owner will be the primary group of the user.
There is one Special Permission SGID, when you set the SGID bit on directory. When users create the file/directory automatically owner group will be same as a parent.
1. chmod g+s /data
2. Verify using: ls -ld /data You will get: drwxrws---
NEW QUESTION 8
There are Mail servers, Web Servers, DNS Servers and Log Server. Log Server is already configured. You should configure the mail server, web server and dns server to send the logs to log server.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
According to question, log server is already configured. We have to configure the mail, web and dns server for log redirection. In mail, web and dns server:
vi /etc/syslog.conf mail.* @logserveraddress
service syslog restart
mail is the facility and * means the priority. It sends logs of mail services into log server.
NEW QUESTION 9
In accordance with the following requirements to deploy ssh login service:
harry belongs to example.com which can remote login your systems.
However, users of remote.test cannot use ssh login to your machine.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 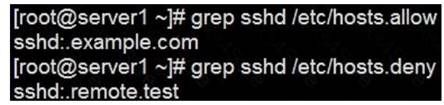
Notice:
tcp_wrappers has two configuration files and their priority level is /etc/hosts.allow->/etc/hosts.deny
NEW QUESTION 10
Install the Cron Schedule for jeff user to display "Hello" on daily 5:30.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Login as a root user
cat >schedule.txt
30 05 * * * /bin/echo "Hello"
crontab -u jeff schedule.txt
service crond restart
The cron system is essentially a smart alarm clock. When the alarm sounds, Linux runs the commands of your choice automatically. You can set the alarm clock to run at all sorts of regular time intervals. Alternatively, the system allows you to run the command of your choice once, at a specified time in the future.
Red Hat configured the cron daemon, crond. By default, it checks a series of directories for jobs to run, every minute of every hour of every day. The crond checks the /var/spool/cron directory for jobs by user. It also checks for scheduled jobs for the computer under /etc/crontab and in the /etc/cron.d directory. Here is the format of a line in crontab. Each of these columns is explained in more detail:
#minute, hour, day of month, month, day of week, command
* * * * * command
Entries in a crontab Command Line Field Value
Minute 0-59
Hour Based on a 24-hour clock; for example, 23 = 11 p.m. Day of month 1-31
Month 1-12, or jan, feb, mar, etc.
Day of week 0-7; where 0 and 7 are both Sunday; or sun, mon, tue, etc. Command: The command you want to run
NEW QUESTION 11
Add a cron schedule to take full backup of /home on every day at 5:30 pm to /dev/st0 device.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
1. vi /var/schedule
30 17 * * * /sbin/dump -0u /dev/st0 /dev/hda7
2. crontab /var/schedule
3. service crond restart
We can add the cron schedule either by specifying the scripts path on /etc/crontab file or by creating on text file on crontab pattern.
cron helps to schedule on recurring events. Pattern of cron is: Minute Hour Day of Month Month Day of Week Commands
0-59 0-23 1-31 1-12 0-7 where 0 and 7 mean Sunday.
Note * means every. To execute the command on every two minutes */2.
NEW QUESTION 12
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: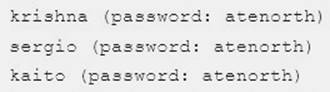
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
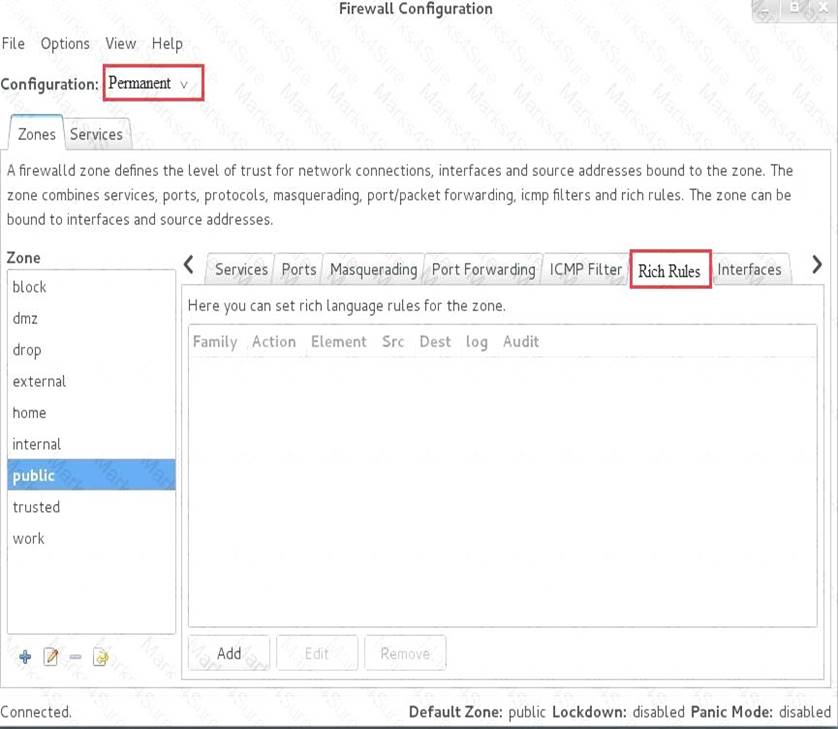
Configure port forwarding on the system1, as required:
1. The systems in the network 172.24.11.0/24, local port 5423 for accessing system1 will be forwarded to 80
(2) This setting must be permanent
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Use Graphical interface to configure
Use firewall-config to open the Graphical interface in CLI Adjust the configuration: drop-down menu to permanent Add a strategy to the public area of the “Port Forwarding”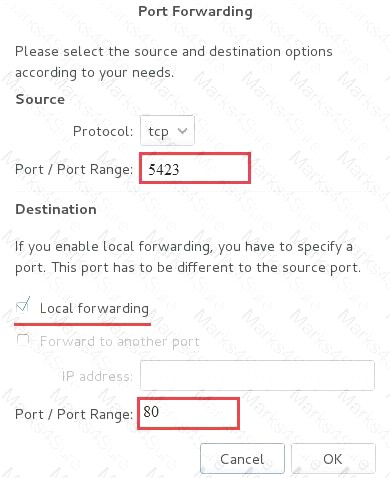
systemctl restart firewalld.service // Reload the firewall strategy
NEW QUESTION 13
Configure
the web server, which can be accessed by http://station.domain30.example.com.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 14
There were two systems:
system1, main system on which most of the configuration take place
system2, some configuration here
Customize the User Environment
Create a command called qstat on both serverX and desktop.
It should be able to execute the following command (ps –eo pid, tid, class, rtprio, ni, pri, psr, pcpu, stat, wchan:14, comm).
The command should be executable by all users.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 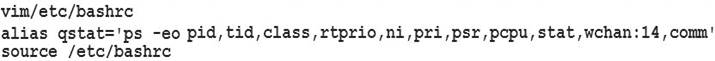
NEW QUESTION 15
Prevent Mary from performing user configuration tasks in your system.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 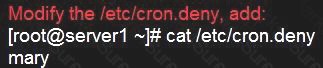
Conclusions:
1. I find that it is common to add various service access limits in the exam RHCE. The exercises like: require
one network segment can be accessed another network segments can not be accessed, the following are some conclusions for various service:
tcp_wrappers:/etc/hosts.allow,/etc/hosts.deny
tcp_wrappers can filter the TCP’s accessing service. TCP whether has the filtering function which depends on this service whether use the function library of tcp_wrappers, or this service whether has the xinetd process of starting function of tcp_wrappers. tcp_wrappers’s main configuration file is /etc/hosts.allow,/etc/hosts.deny.
And the priority of the documents in hosts. allow is higher than hosts. deny. Visit will be passed if no match was found.
sshd,vsftpd can use the filtering service of tcp_wrappers. Configuration example: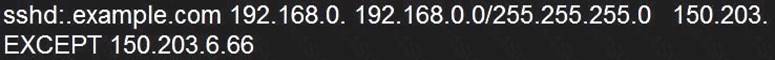
Notice:
The two configuration files’ syntax can refer to hosts_access (5) and hosts_options(5) sshd_config
There are four parameters in this configuration file: DenyUsers, AllowUsers, DenyGroups, AllowGroups, they are used to limit some users or user groups to proceed Remote Login through the SSH. These parameters’ priority level is DenyUsers->AllowUsers->DenyGroups->AllowGroups
Configuration example: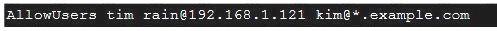
httpd Service
Through the /etc/httpd/conf/httpd.conf in parameters, can add <Directory> to control the url access. Just as: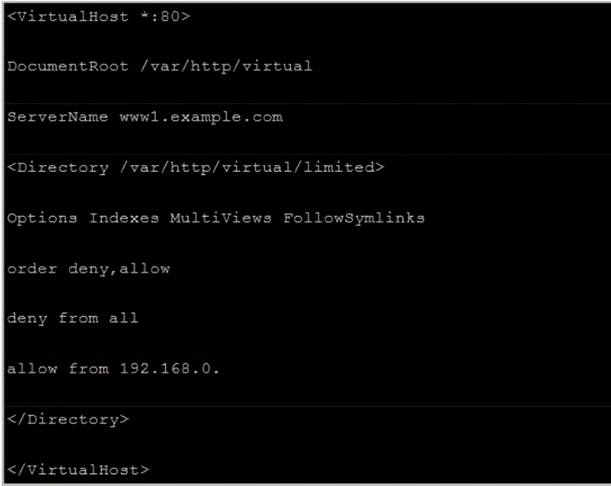
Notice:
So pay attention, deny’s and allow’s priority level in order deny,allow is: the backer has the higher priority level. But here, allow’s priority has a higher priority level.
nfs Service
nfs service directly control the visits through file /etc/exports, just as:
samba Service
Parameter hosts allow in /etc/samba/smb.conf which is used as Access Control, just as: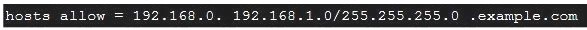
2. Paying attention to use Mount parameters: _netdev,defaults when you are mounting ISCSI disk.
3. Stop the NetworkManager
/etc/init.d/NetworkManager stop chkconfig NetworkManager off
4. When you are deploying ifcfg-ethX, add parameters: PEERDNS=no
5. Empty the firewall in RHCSARHCE: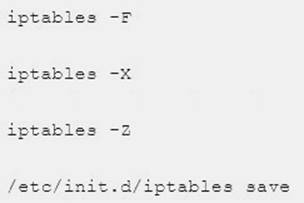
6. Narrow lv steps: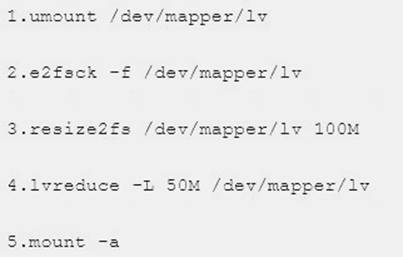
7. Mount the using command - swap which is newly added in /etc/fstab
8. If Verification is not passed when you are installing software, can import public key: rpm import
/etc/pki/rpm…/…release and so on. In yum.repo, you also can deploy gpgkey, for example, gpgkey=/etc/pki/rpm…/…release
9. When you are using “Find” command to search and keep these files, paying attention to use cp -a to copy files if you use user name and authority as your searching methods.
NEW QUESTION 16
Make Secondary belongs the jeff and marion users on sysusers group. But harold user should not belongs to sysusers group.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
usermod -G sysusers jeff
usermod -G sysuser marion
Verify by reading /etc/group file Note:
Using usermod command we can make user belongs to different group. There are two types of group one primary and another is secondary. Primary group can be only one but user can belong to more than one group as secondary.
usermod -g groupname username - To change the primary group of the user. usermod -G groupname username
- To make user belongs to secondary group.
NEW QUESTION 17
Whoever creates the files/directories on /storage group owner should be automatically should be the same group owner of /storage.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
chmod g+s /storage
Verify using: ls -ld /stora Note:
Permission should be like:
drwxrws--- 2 root sysusers 4096 Mar 16 18:08 /storage If SGID bit is set on directory then who every users creates the files on directory group owner automatically the owner of parent directory.
To set the SGID bit: chmod g+s directory
To Remove the SGID bit: chmod g-s directory
NEW QUESTION 18
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: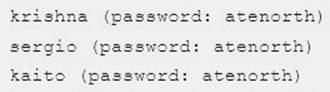
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
Configure the Access to the Web Content
Create a directory private under the directory DocumentRoot in the web server on the system1, requirements are the following:
Download a file copy to this directory from http://rhgls.domain11.example.com/materials/private.html
and rename it as index.html.
Don’t make any changes to this file content
Any users from the system1 can browse the content of the private, but cannot access this directory content through other systems
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 19
Arrange
a web service address is: http://serverX.example.com, X is the number of your exam machine. Deploy it in accordance with the following requirements:
Download ftp//instructor.example.com/pub/rhce/server.html
Cannot do any modification to file document server.html
Rename file document server.html as index.html
Copy the file document server.html to DocumentRoo
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 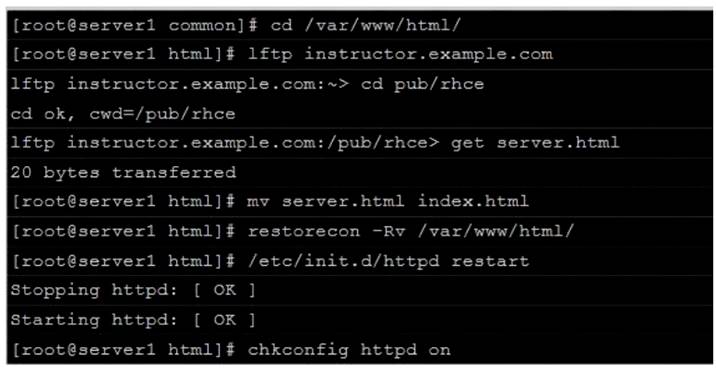
NEW QUESTION 20
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: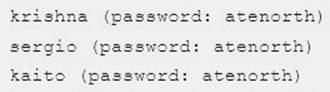
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
Configure the iSCSI Server
Configure the system1 to provide a ISCSI service disk named iqn.2014- 09.com.example.domain11:system1 and meet the following requirements at the same time:
The Server Port is 3260
Use iSCSI-store as its back-end volume, its size is 3G
This service just can be accessed by system2.domian11.example.com
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 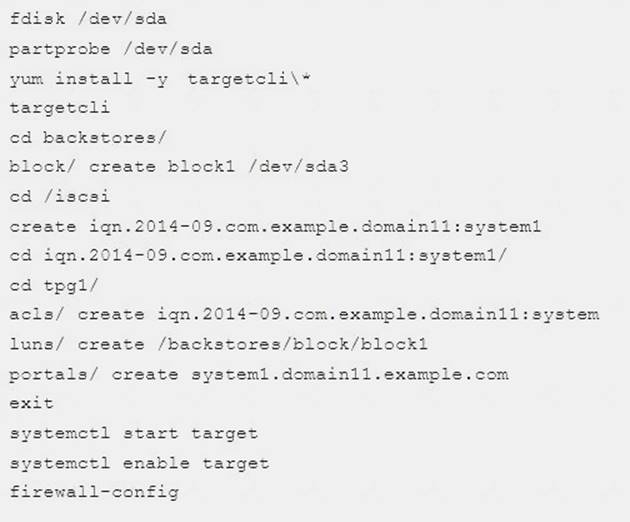
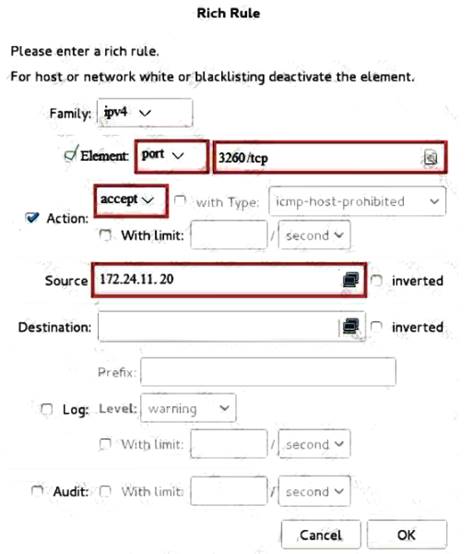
systecmctl restart firewalld
NEW QUESTION 21
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: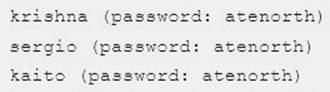
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
Configure IPV6 Address
Configure interface eth0 on your test system, using the following IPV6 addresses:
1) The address of system1 should be 2003:ac18::305/64
(2) The address of system2 should be 2003:ac18::30a/64
(3) Both two systems must be able to communicate with systems in network 2003:ac18/64
(4) The address must still take effect after restart
(5) Both two systems must maintain the current Ipv4 address and can communicate
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Solution: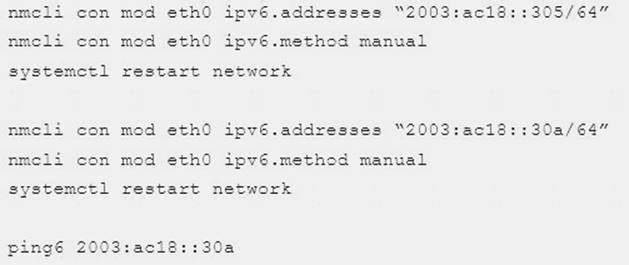
NEW QUESTION 22
Configure the ftp to allow anonymously download the directory /var/ftp/pub, and reject the domain t3gg.com to access.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 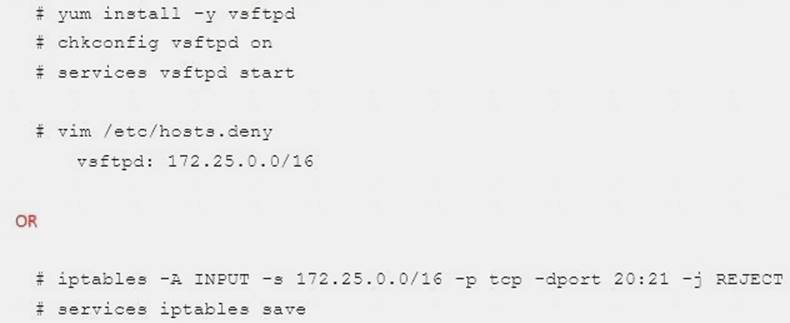
NEW QUESTION 23
Create a Shell script /root/program:
The shell script will come back to “user” parameter when you are entering “kernel” parameter.
The shell script will come back to “kernel” when you are entering “user” parameter.
It will output the standard error when this script “usage:/root/program kernel|user” don’t input any parameter or the parameter you inputted is entered as the requirements.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 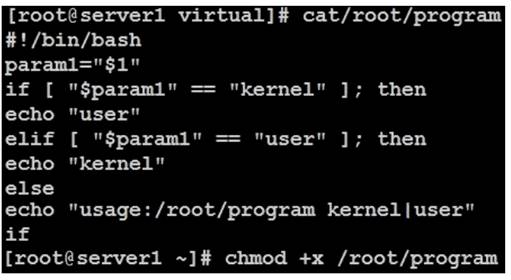
NEW QUESTION 24
Configure a mail alias to your MTA, for example, send emails to harry but mary actually is receiving emails. Answer:
Please see explanation
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 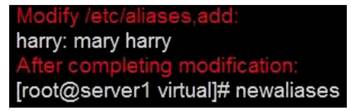
Notice:
This problem is a trap. The question no 31 requires that harry must be able to receive remote emails but the problems in the question no 32 requires mary to receive harry’s emails. So harry must be added when you are deploying aliases.
NEW QUESTION 25
RHCE Test Configuration Instructions
Information for the two systems you will use in test is the following:
system1.group3.example.com: is one of the main sever. system2.group3.example.com: mainly used as a client. Password for both of the two systems is atenorth
System’s IP is provided by DHCP, you can regard it as normal, or you can reset to Static IP in accordance with the following requirements:
system1.group3.example.com: 172.24.3.5
system2.group3.example.com: 172.24.3.10 The subnet mask is 255.255.255.0
Your system is a member of DNS domain group3.example.com. All systems in DNS domain group3.example.com are all in subnet 172.24.3.0/255.255.255.0, the same all systems in this subnet are also in group3.example.com, unless specialized, all network services required to be configured can be accessed by systems of domain group3.
host.group3.example.com provides a centralized authentication service domain
GROUP3.EXAMPLE.COM, both system1 and system2 have already been pre-configured to be the client for this domain, this domain provides the following user account: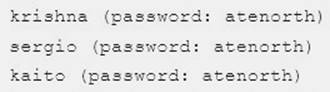
Firewall is enabled by default, you can turn it off when deemed appropriate, other settings about firewall may be in separate requirements.
Your system will be restarted before scoring, so please ensure that all modifications and service configurations you made still can be operated after the restart without manual intervention, virtual machine instances of all examinations must be able to enter the correct multi-user level after restart without manual assistance, it will be scored zero if the test using virtual machine system cannot be restarted or be properly restarted.
Corresponding distribution packages for the testing using operating system Red Hat Enterprise Linux version can be found in the following link:
http://server1.group3.example.com/rhel
Part of the requirements include host security, ensure your host security limit does not prevent the request to allow the host and network, although you correctly configured the network service but would have to allow the host or network is blocked, this also does not score.
You will notice that some requirements which clearly do not allow services be accessed by service domain my133t.org, systems of this domain are in subnet 172.25.1.0/252.255.255.0, and systems of these subnets also belong to my 133t.org domain.
PS: Notice that some test questions may depend on other exam questions, for example, you might be asked to perform a series of restrictions on a user, but this user creation may be required in other questions. For convenient identification, each exam question has some radio buttons to help you identify which questions you have already completed or not completed. Certainly, you do not need to care these buttons if you don’t need them.
Configure iSCSI Clients
Configure the system2 to make it can link to iqn.2014-09.com.example.domain11:system1 provided by the system, meet the following requirements at the same time:
Block device iSCSI contains a 2100MIB partition, and is formatted as ext4.
This partition mount to the /mnt/data and mount automatically during the system start-up.
1. iSCSI device automatically loads during the system start-up.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 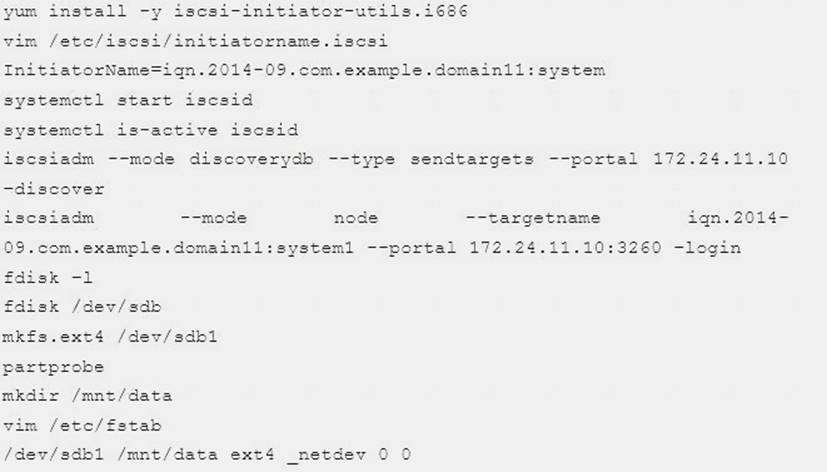
NEW QUESTION 26
......
Thanks for reading the newest EX300 exam dumps! We recommend you to try the PREMIUM Dumps-hub.com EX300 dumps in VCE and PDF here: https://www.dumps-hub.com/EX300-dumps.html (88 Q&As Dumps)
