Master the N10-009 CompTIA Network+ Exam content and be ready for exam day success quickly with this Examcollection N10-009 practice exam. We guarantee it!We make it a reality and give you real N10-009 questions in our CompTIA N10-009 braindumps.Latest 100% VALID CompTIA N10-009 Exam Questions Dumps at below page. You can use our CompTIA N10-009 braindumps and pass your exam.
Free demo questions for CompTIA N10-009 Exam Dumps Below:
NEW QUESTION 1
Which of the following network devices can perform routing between VLANs?
- A. Layer 2 switch
- B. Layer 3 switch
- C. Load balancer
- D. Bridge
Answer: B
Explanation:
https://www.practicalnetworking.net/stand-alone/routing-between- vlans/#:~:text=A%20router%20will%20perform%20the,to%20communicate%20with%20on e%20another.
NEW QUESTION 2
A network administrator notices excessive wireless traffic occurring on an access point after normal business hours. The access point is located on an exterior wall. Which of the following should the administrator do to limit wireless access outside the building?
- A. Set up a private VLAN.
- B. Disable roaming on the WAP.
- C. Change to a directional antenna.
- D. Stop broadcasting of the SSID.
Answer: C
Explanation:
A directional antenna is a type of antenna that radiates or receives radio waves in a specific direction. This can help limit wireless access outside the building by focusing the signal towards the intended area and reducing the signal strength in other directions. A private VLAN is a feature that isolates network devices within a VLAN. Disabling roaming on the WAP prevents wireless clients from switching to another WAP when the signal is weak. Stopping broadcasting of the SSID hides the network name from wireless clients, but does not prevent them from connecting if they know the SSID.
References: CompTIA Network+ Certification Exam Objectives Version 7.0 (N10-007), Objective 3.1: Given a scenario, install and configure wireless LAN infrastructure and implement the appropriate technologies in support of wireless capable devices.
NEW QUESTION 3
Which of the following transceiver types can support up to 40Gbps?
- A. SFP+
- B. QSFP+
- C. QSFP
- D. SFP
Answer: B
Explanation:
QSFP+ is a transceiver type that can support up to 40Gbps. It stands for Quad Small Form-factor Pluggable Plus and uses four lanes of data to achieve high-speed transmission. It is commonly used for data center and high-performance computing applications. References: https://www.cisco.com/c/en/us/products/collateral/interfaces-modules/transceiver-modules/data_sheet_c78-660083.html
NEW QUESTION 4
A security engineer wants to provide a secure, dedicated, alternate access method into an IT network infrastructure to administer connected devices and IT assets. Which of the following is the engineer most likely to implement?
- A. Remote desktop gateway
- B. Authentication and authorization controls
- C. Out-of-band management
- D. Secure Shell
Answer: C
Explanation:
Out-of-band management is a method of accessing network devices and IT assets through a dedicated channel that is separate from the normal data traffic. This provides a secure and alternate way to administer the network infrastructure, especially in case of failures or emergencies. Remote desktop gateway is a service that allows remote access to desktops and applications on a network. Authentication and authorization controls are mechanisms that verify the identity and permissions of users and devices on a network. Secure Shell is a protocol that encrypts the communication between a client and a server on a network.
NEW QUESTION 5
A network device is configured to send critical events to a syslog server; however, the following alerts are not being received:
Severity 5 LINK-UPDOWN: Interface 1/1, changed state to down Severity 5 LINK-UPDOWN: Interface 1/3, changed state to down
Which of the following describes the reason why the events are not being received?
- A. The network device is not configured to log that level to the syslog server
- B. The network device was down and could not send the event
- C. The syslog server is not compatible with the network device
- D. The syslog server did not have the correct MIB loaded to receive the message
Answer: A
Explanation:
The reason why the alerts are not being received is that the network device is not configured to log that level to the syslog server. The severity level for the events may need to be adjusted in order for them to be sent to the syslog server. References: Network+ Certification Study Guide, Chapter 8: Network Troubleshooting
NEW QUESTION 6
A network technician 13 troubleshooting a specific port on a switch. Which of the following commands should the technician use to see the port configuration?
- A. show route
- B. show Interface
- C. show arp
- D. show port
Answer: B
Explanation:
To see the configuration of a specific port on a switch, the network technician should use the "show interface" command. This command provides detailed information about the interface, including the current configuration, status, and statistics for the interface.
NEW QUESTION 7
A company’s VolP phone connection is cutting in and out. Which of the following should be configured to resolve this issue?
- A. 802.1 Q tagging
- B. Jumbo frames
- C. Native VLAN
- D. Link aggregation
Answer: A
Explanation:
* 802.1 Q tagging is a method of adding a VLAN identifier to an Ethernet frame to indicate which VLAN the frame belongs to. This allows different VLANs to share the same physical link and device without interfering with each other. 802.1 Q tagging also supports a quality of service (QoS) scheme that can prioritize different classes of traffic based on the priority code point (PCP) field in the tag12
VoIP phone connection issues can be caused by network congestion, packet loss, jitter, or latency, which affect the quality and reliability of voice transmission over the Internet. By using 802.1 Q tagging, VoIP traffic can be separated from other data traffic and assigned a higher priority level, which reduces the chances of dropping or delaying voice packets. 802.1 Q tagging can also improve the security and scalability of VoIP networks by isolating different voice domains and preventing unauthorized access34
NEW QUESTION 8
A network administrator is investigating a network event that is causing all communication to stop. The network administrator is unable to use SSH to connect to the switch but is able to gain access using the serial console port. While monitoring port statistics, the
administrator sees the following: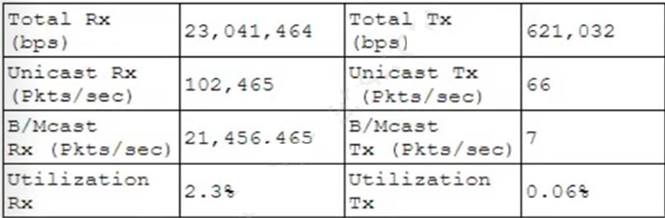
Which of the following is MOST likely causing the network outage?
- A. Duplicate IP address
- B. High collisions
- C. Asynchronous route
- D. Switch loop
Answer: B
NEW QUESTION 9
A company's web server is hosted at a local ISP. This is an example of:
- A. allocation.
- B. an on-premises data center.
- C. a branch office.
- D. a cloud provider.
Answer: D
NEW QUESTION 10
A local service provider connected 20 schools in a large city with a fiber-optic switched network. Which of the following network types did the provider set up?
- A. LAN
- B. MAN
- C. CAN
- D. WAN
Answer: B
Explanation:
MAN stands for Metropolitan Area Network, and it is a type of network that covers a large geographic area, such as a city or a county. MANs are often used to connect multiple LANs (Local Area Networks) within a region, such as schools, offices, or government buildings. MANs typically use high-speed and high-capacity transmission media, such as fiber-optic cables, to provide fast and reliable data communication. MANs can also provide access to WANs (Wide Area Networks), such as the Internet, or other services, such as cable TV or VoIP.
The other options are not correct because they are not the type of network that covers a large city. They are:
✑ LAN. LAN stands for Local Area Network, and it is a type of network that covers a
small geographic area, such as a home, an office, or a building. LANs are often used to connect multiple devices, such as computers, printers, or phones, within a single network. LANs typically use low-cost and low-capacity transmission media, such as twisted-pair cables, to provide data communication. LANs can also provide access to other networks, such as MANs or WANs, through routers or gateways.
✑ CAN. CAN stands for Campus Area Network, and it is a type of network that
covers a moderate geographic area, such as a university, a hospital, or a military base. CANs are often used to connect multiple LANs within a campus, such as different departments, buildings, or facilities. CANs typically use medium-cost and medium-capacity transmission media, such as coaxial cables, to provide data communication. CANs can also provide access to other networks, such as MANs or WANs, through routers or gateways.
✑ WAN. WAN stands for Wide Area Network, and it is a type of network that covers
a very large geographic area, such as a country, a continent, or the world. WANs are often used to connect multiple MANs or LANs across different regions, such as
different cities, states, or countries. WANs typically use high-cost and high- capacity transmission media, such as satellite links, to provide data communication. WANs can also provide access to various services, such as the Internet, email, or VPN.
References1: What is a Metropolitan Area Network (MAN)? - Definition from
Techopedia2: Network+ (Plus) Certification | CompTIA IT Certifications3: What is a Local Area Network (LAN)? - Definition from Techopedia4: What is a Campus Area Network (CAN)? - Definition from Techopedia5: What is a Wide Area Network (WAN)? - Definition from Techopedia
NEW QUESTION 11
A network technician is deploying multiple switches for a new office. The switches are separately managed and need to be cabled in to support dual firewalls in a HA setup. Which of the following should the technician enable to support proper stability of the network switches?
- A. NTP
- B. CDMA
- C. STP
- D. LACP
- E. 802.1Q
Answer: C
Explanation:
STP stands for Spanning Tree Protocol, which is a network protocol that prevents loops in a switched network by blocking redundant links. STP allows only one active path between any two network devices, and dynamically reconfigures the network topology in case of link failures or changes. STP is essential for proper stability of the network switches, especially when they are cabled in a redundant or complex topology that involves multiple switches and firewalls. Without STP, loops can cause broadcast storms, MAC address table instability, and duplicate frames, which can degrade the network performance and availability. References: [CompTIA Network+ Certification Exam Objectives], Spanning Tree Protocol (STP) Explained | NetworkLessons.com
NEW QUESTION 12
Which of the following is the primary function of the core layer of the three-tiered model?
- A. Routing
- B. Repeating
- C. Bridging
- D. Switching
Answer: A
Explanation:
https://www.omnisecu.com/cisco-certified-network-associate-ccna/three-tier-hierarchical-network-model.php
Core Layer consists of biggest, fastest, and most expensive routers with the highest model numbers and Core Layer is considered as the back bone of networks. Core Layer routers are used to merge geographically separated networks. The Core Layer routers move information on the network as fast as possible. The switches operating at core layer switches packets as fast as possible.
NEW QUESTION 13
A consultant is working with two international companies. The companies will be sharing cloud resources for a project. Which of the following documents would provide an agreement on how to utilize the resources?
- A. MOU
- B. NDA
- C. AUP
- D. SLA
Answer: A
Explanation:
A memorandum of understanding (MOU) is a document that describes an agreement between two or more parties on how to utilize shared resources for a project. An MOU is not legally binding, but it outlines the expectations and responsibilities of each party involved in the collaboration. An MOU can be used when two international companies want to share cloud resources for a project without creating a formal contract. References: https://www.comptia.org/training/books/network-n10-008-study-guide (page 405)
NEW QUESTION 14
A network administrator received reports that a 40Gb connection is saturated. The only server the administrator can use for data collection in that location has a 10Gb connection to the network. Which of the following is the best method to use on the server to determine the source of the saturation?
- A. Port mirroring
- B. Log aggregation
- C. Flow data
- D. Packet capture
Answer: C
Explanation:
Flow data is a summary of network traffic that can be used to monitor and analyze network performance, utilization, and security. Flow data can provide information such as source and destination IP addresses, ports, protocols, bytes, packets, and timestamps. Flow data can be collected using protocols such as NetFlow, sFlow, or IPFIX. Flow data can help identify the source of network saturation without requiring a full packet capture, which would be impractical on a 40Gb connection with a 10Gb server.
References:
✑ CompTIA Network+ N10-008 Certification Exam Objectives, page 51
✑ CompTIA Network+ N10-008 Cert Guide, Chapter 11: Switching Technologies2
NEW QUESTION 15
A technician notices that equipment is being moved around and misplaced in the server room, even though the room has locked doors and cabinets. Which of the following would be the BEST solution to identify who is responsible?
- A. Install motion detection
- B. Install cameras.
- C. Install tamper detection.
- D. Hire a security guard.
Answer: B
Explanation:
Installing cameras in the server room is the best solution to identify who is responsible for the equipment being moved and misplaced. Cameras provide a way to monitor the server room in real time and can be used to identify suspicious activity. Additionally, they provide a way to review past activity and allow you to review footage to determine who may be responsible for the misplacement of equipment.
NEW QUESTION 16
A technician is consolidating a topology with multiple SSlDs into one unique SSiD deployment. Which of the following features will be possible after this new configuration?
- A. Seamless roaming
- B. Basic service set
- C. WPA
- D. MU-MIMO
Answer: A
NEW QUESTION 17
An administrator would like to create a fault-tolerant ring between three switches within a Layer 2 network. Which of the following Ethernet features should the administrator employ?
- A. Spanning Tree Protocol
- B. Open Shortest Path First
- C. Port mirroring
- D. An interior gateway protocol
Answer: A
Explanation:
Spanning Tree Protocol (STP) is a network protocol that ensures a loop-free topology in Ethernet networks by actively blocking certain links and enabling others. STP prevents loops by putting some of the links in a blocking state, effectively creating a loop- free topology. This ensures that there is only one active path between two devices, which helps prevent network loops and the associated problems (such as broadcast storms) that can result from them. STP is used to create a fault-tolerant ring between three switches within a Layer 2 network.
NEW QUESTION 18
Which of the following describes a network in which users and devices need to mutually authenticate before any network resource can be accessed?
- A. Least privilege
- B. Local authentication
- C. Zero trust
- D. Need to know
Answer: C
Explanation:
A zero trust network is a network in which users and devices need to mutually authenticate before any network resource can be accessed. A zero trust network assumes that no one and nothing can be trusted by default, even if they were previously verified or are within the network perimeter. A zero trust network uses various technologies and practices, such as data and log aggregation, cybersecurity analytics, continuous diagnostics and mitigation, user behavior analytics, microsegmentation, and identity and access management, to enforce granular and dynamic policies based on the context and behavior of the users and devices123.
References:
✑ What is Zero Trust? | Internet of Things | CompTIA3
✑ The Death of the Perimeter: Zero Trust is (Almost) Here to Stay | Cybersecurity | CompTIA2
✑ CompTIA Network+ Certification Exam N10-008 Practice Test 17 -
ExamCompass1
NEW QUESTION 19
Which of the following physical security methods Is the MOST effective to prevent tailgating?
- A. Biometrics in an access control vestibule
- B. IP cameras with motion detection
- C. Smart lockers with tamper protection
- D. Badge readers plus a PIN pad
Answer: A
Explanation:
Biometrics is a type of authentication that uses a person’s physical characteristics, such as fingerprints, iris, or face, to verify their identity. An access control vestibule is a small room or area that separates two spaces and allows only one person to enter or exit at a time. Biometrics in an access control vestibule is the most effective physical security method to prevent tailgating, which is the unauthorized entry of a person behind another person who has legitimate access.
References: Network+ Study Guide Objective 5.1: Summarize the importance of physical security controls.
NEW QUESTION 20
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution. Which of the following
records should be used to accomplish the task?
- A. TXT
- B. AAA
- C. PTR
- D. CNAME
Answer: D
Explanation:
CNAME stands for Canonical Name, and it is a type of DNS record that creates an alias for another domain name. A CNAME record can be used to redirect a network resource that has been moved to a different location, such as a SaaS solution. For example, if a web server that was previously hosted on the local network with the domain name www.example.com is now hosted by a SaaS provider with the domain name www.saasprovider.com, a CNAME record can be created to point www.example.com to www.saasprovider.com. This way, the users can still access the web server using the original domain name, and the DNS server will resolve it to the new domain name. References
✑ CNAME is one of the common DNS record types covered in Objective 1.6 of the
CompTIA Network+ N10-008 certification exam1.
✑ CNAME can be used to redirect a network resource that has been moved to a different location23.
✑ CNAME creates an alias for another domain name23.
1: CompTIA Network+ Certification Exam Objectives, page 4 2: DNS Record Types – N10- 008 CompTIA Network+ : 1.6 3: The Official CompTIA Network+ Student Guide (Exam N10-008), Chapter 1, page 32
NEW QUESTION 21
......
P.S. Easily pass N10-009 Exam with 111 Q&As Dumps-hub.com Dumps & pdf Version, Welcome to Download the Newest Dumps-hub.com N10-009 Dumps: https://www.dumps-hub.com/N10-009-dumps.html (111 New Questions)
