Want to know Passleader N10-009 Exam practice test features? Want to lear more about CompTIA CompTIA Network+ Exam certification experience? Study Printable CompTIA N10-009 answers to Replace N10-009 questions at Passleader. Gat a success with an absolute guarantee to pass CompTIA N10-009 (CompTIA Network+ Exam) test on your first attempt.
Also have N10-009 free dumps questions for you:
NEW QUESTION 1
A user tries to ping 192.168.1.100 from the command prompt on the 192.168.2.101 network but gets the following response: U.U.U.U. Which of the following needs to be configured for these networks to reach each other?
- A. Network address translation
- B. Default gateway
- C. Loopback
- D. Routing protocol
Answer: B
Explanation:
A default gateway is a device that routes traffic from one network to another network, such as the Internet. A default gateway is usually configured on each host device to specify the IP address of the router that connects the host’s network to other networks. In this case, the user’s device and the destination device are on different networks (192.168.1.0/24 and 192.168.2.0/24), so the user needs to configure a default gateway on their device to reach the destination device. References: https://partners.comptia.org/docs/default-source/resources/comptia-network-n10-008-exam-objectives-(2-0), https://www.techopedia.com/definition/25761/default-gateway
NEW QUESTION 2
A network technician is working at a new office location and needs to connect one laptop to another to transfer files. The laptops are newer models and do not have Ethernet ports. Access points are not available either. Which Of the following types Of wireless network SSIDs does the network technician need to configure to be able to connect the laptops together?
- A. Independent Basic Service Set
- B. Extended Service Set
- C. Distribution System Service
- D. Basic Service Set
Answer: C
Explanation:
An Independent Basic Service Set (IBSS) is a type of wireless network that does not require an access point or a wired network. An IBSS allows wireless devices to communicate directly with each other using ad hoc mode. An IBSS is also known as an ad hoc network or a peer-to-peer network. A network technician can configure an IBSS to connect two laptops together and transfer files.
References: Network+ Study Guide Objective 1.4: Explain the properties and characteristics of TCP/IP
NEW QUESTION 3
Due to a surge in business, a company is onboarding an unusually high number of salespeople. The salespeople are assigned desktops that are wired to the network. The last few salespeople to be onboarded are able to access corporate materials on the network but not sales-specific resources. Which of the following is MOST likely the cause?
- A. The switch was configured with port security.
- B. Newly added machines are running into DHCP conflicts.
- C. The IPS was not configured to recognize the new users.
- D. Recently added users were assigned to the wrong VLAN
Answer: D
NEW QUESTION 4
A network technician 13 troubleshooting a network issue for employees who have reported Issues with speed when accessing a server in another subnet. The server is in another building that is 410ft (125m) away from the employees' building. The 10GBASE-T connection between the two buildings uses Cat 5e. Which of the following BEST explains the speed issue?
- A. The connection type is not rated for that distance
- B. A broadcast storm is occurring on the subnet.
- C. The cable run has interference on it
- D. The connection should be made using a Cat 6 cable
Answer: D
Explanation:
The 10GBASE-T connection between the two buildings uses Cat 5e, which is not rated for a distance of 410ft (125m). According to the CompTIA Network+ Study Manual, for 10GBASE-T connections, "Cat 5e is rated for up to 55m, Cat 6a is rated for 100m, and Cat 7 is rated for 150m." Therefore, the speed issue is likely due to the fact that the connection type is not rated for the distance between the two buildings. To resolve the issue, the technician should consider using a Cat 6a or Cat 7 cable to increase the distance the connection is rated for.
NEW QUESTION 5
A city has hired a new employee who needs to be able to work when traveling at home and at the municipal sourcing of a neighboring city that snares services. The employee is issued a laptop, and a technician needs to train the employee on the appropriate solutions
for secure access to the network from all the possible locations On which of the following solutions would the technician MOST likely train the employee?
- A. Site-to-site VPNs between the two city locations and client-to-site software on the employee's laptop tor all other remote access
- B. Client-to-site VPNs between the travel locations and site-to-site software on the employee's laptop for all other remote access
- C. Client-to-site VPNs between the two city locations and site-to-site software on the employee's laptop for all other remote access
- D. Site-to-site VPNs between the home and city locations and site-to-site software on the employee's laptop for all other remote access
Answer: A
Explanation:
The technician would most likely train the employee on using site-to-site VPNs between the two city locations and client-to-site software on the employee’s laptop for all other remote access. A VPN (Virtual Private Network) is a technology that creates a secure and encrypted tunnel over a public network such as the Internet. It allows remote users or sites to access a private network as if they were directly connected to it. A site-to- site VPN connects two or more networks, such as branch offices or data centers, using a VPN gateway device at each site. A client-to-site VPN connects individual users, such as mobile workers or telecommuters, using a VPN client software on their devices. In this scenario, the employee needs to access the network from different locations, such as home, travel, or another city. Therefore, the technician would train the employee on how to use site-to-site VPNs to connect to the network from another city location that shares services, and how to use client-to-site software to connect to the network from home or travel locations. References: https://www.cisco.com/c/en/us/support/docs/security- vpn/ipsec-negotiation-ike-protocols/14106-how-vpn-works.html
NEW QUESTION 6
A network resource was accessed by an outsider as a result of a successful phishing
campaign. Which of the following strategies should be employed to mitigate the effects of phishing?
- A. Multifactor authentication
- B. Single sign-on
- C. RADIUS
- D. VPN
Answer: A
Explanation:
Multifactor authentication is a security measure that requires users to provide multiple pieces of evidence before they can access a network resource. This could include requiring users to enter a username, password, and a code sent to the user's mobile phone before they are allowed access. This ensures that the user is who they say they are, reducing the risk of malicious actors gaining access to network resources as a result of a successful phishing campaign.
NEW QUESTION 7
Which of the following records can be used to track the number of changes on a DNS zone?
- A. SOA
- B. SRV
- C. PTR
- D. NS
Answer: A
Explanation:
The DNS ‘start of authority’ (SOA) record stores important information about a domain or zone such as the email address of the administrator, when the domain was last updated, and how long the server should wait between refreshes. All DNS zones need an SOA record in order to conform to IETF standards. SOA records are also important for zone transfers.
NEW QUESTION 8
A branch of a company recently switched to a new ISP. The network engineer was given a new IP range to assign. The ISP assigned 196.26.4.0/26, and the branch gateway router now has the following configurations on the interface that peers to the ISP: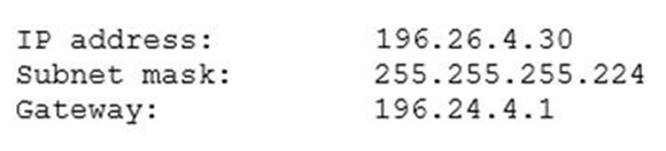
The network engineer observes that all users have lost Internet connectivity. Which of the following describes the issue?
- A. The incorrect subnet mask was configured
- B. The incorrect gateway was configured
- C. The incorrect IP address was configured
- D. The incorrect interface was configured
Answer: C
Explanation:
The IP address configured on the router interface is 196.26.4.1/26, which belongs to the IP range assigned by the ISP (196.26.4.0/26). However, this IP address is not valid for this interface because it is the network address of the subnet, which cannot be assigned to any host device. The network address is the first address of a subnet that identifies the subnet itself. The valid IP addresses for this subnet are from 196.26.4.1 to 196.26.4.62, excluding the network address (196.26.4.0) and the broadcast address (196.26.4.63). The router interface should be configured with a valid IP address within this range to restore Internet connectivity for all users. References: https://partners.comptia.org/docs/default-source/resources/comptia-network-n10-008-exam-objectives-(2-0), https://www.techopedia.com/definition/24136/network-address
NEW QUESTION 9
A company hired a technician to find all the devices connected within a network. Which of the following software tools would BEST assist the technician in completing this task?
- A. IP scanner
- B. Terminal emulator
- C. NetFlow analyzer
- D. Port scanner
Answer: A
Explanation:
To find all devices connected within a network, a technician can use an IP scanner. An IP scanner sends a ping request to all IP addresses within a specified range and then identifies the active devices that respond to the request.
NEW QUESTION 10
The following configuration is applied to a DHCP server connected to a VPN concentrator: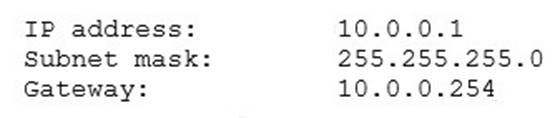
There are 300 non-concurrent sales representatives who log in for one hour a day to upload reports, and 252 of these representatives are able to connect to the VPN without any Issues. The remaining sales representatives cannot connect to the VPN over the course of the day. Which of the following can be done to resolve the issue without utilizing additional resources?
- A. Decrease the lease duration
- B. Reboot the DHCP server
- C. Install a new VPN concentrator
- D. Configure a new router
Answer: A
Explanation:
Decreasing the lease duration on the DHCP server will cause clients to renew their IP address leases more frequently, freeing up IP addresses for other clients to use. References: CompTIA Network+ Certification Study Guide, Chapter 3: IP Addressing.
NEW QUESTION 11
Which of the following documents dictates the uptimes that were agreed upon by the involved parties?
- A. MOU
- B. BYOD
- C. SLA
- D. NDA
Answer: C
Explanation:
An SLA (Service Level Agreement) is a document that defines the expected level of service and performance guaranteed by a service provider to a customer. It usually specifies metrics such as uptime, availability, reliability, response time, and compensation or penalties for not meeting the agreed standards. An SLA is a way of ensuring that both parties are clear about their roles and responsibilities, and that the customer receives the quality of service they paid for.
NEW QUESTION 12
A user reports having intermittent connectivity issues to the company network. The network configuration for the user reveals the following:
IP address: 192.168.1.10
Subnet mask: 255.255.255.0
Default gateway: 192.168.1.254
The network switch shows the following ARP table:
Which of the following is the most likely cause of the user's connection issues?
- A. A port with incorrect VLAN assigned
- B. A switch with spanning tree conflict
- C. Another PC with manually configured IP
- D. A router with overlapping route tables
Answer: C
Explanation:
This is the most likely cause of the user’s connection issues, because the ARP table of the
switch shows that there are two devices with the same IP address of 192.168.1.10, but different MAC addresses. This indicates that there is an IP address conflict on the network, where two devices are trying to use the same IP address. This can cause intermittent connectivity issues, as the switch may not be able to forward packets to the correct destination .
NEW QUESTION 13
During an incident, an analyst sends reports regularly to the investigation and leadership teams. Which of the following best describes how Pll should be safeguarded during an incident?
- A. Implement data encryption and store the data so only the company has access.
- B. Ensure permissions are limited to the investigation team and encrypt the data.
- C. Implement data encryption and create a standardized procedure for deleting data that is no longer needed.
- D. Ensure the permissions are open only to the company.
Answer: C
Explanation:
PII stands for Personally Identifiable Information, which is any data that can be used to identify, contact, or locate a specific individual, such as name, address, phone number, email, social security number, and so on. PII should be safeguarded during an incident to protect the privacy and security of the individuals involved, and to comply with the legal and ethical obligations of the organization. One way to safeguard PII during an incident is to implement data encryption, which is a process of transforming data into an unreadable format that can only be accessed by authorized parties who have the decryption key. Data encryption can prevent unauthorized access, modification, or disclosure of PII by malicious actors or third parties. Another way to safeguard PII during an incident is to create a standardized procedure for deleting data that is no longer needed, such as after the incident is resolved or the investigation is completed. Deleting data that is no longer needed can reduce the risk of data breaches, data leaks, or data theft, and can also save storage space and resources. A standardized procedure for deleting data can ensure that the data is erased securely and completely, and that the deletion process is documented and audited.
References
✑ 1: CompTIA Network+ N10-008 Certification Study Guide, page 304-305
✑ 2: CompTIA Network+ N10-008 Exam Subnetting Quiz, question 13
✑ 3: CompTIA Network+ N10-008 Certification Practice Test, question 5
✑ 4: Data Encryption – N10-008 CompTIA Network+ : 3.1
NEW QUESTION 14
A network administrator installed a new data and VoIP network. Users are now experiencing poor call quality when making calls. Which of the following should the administrator do to increase VoIP performance?
- A. Configure a voice VLAN.
- B. Configure LACP on all VoIP phones.
- C. Configure PoE on the network.
- D. Configure jumbo frames on the network.
Answer: A
Explanation:
"Benefits of Voice VLAN
It ensures that your VoIP (Voice over Internet Phone) devices do not have to contend directly with all the broadcasts and other traffic from the data VLAN. A voice VLAN can simplify network configuration in some circumstances."
https://community.fs.com/blog/auto-voip-vs-voice-vlan-what-s-the-difference.html Jumbo Frames
"When jumbo frames on a VoIP/UC network are enabled, it can cause the same kind of
delay to your network transmissions."
"VoIP uses will always not benefit from jumbo frame, as VoIP like gaming, is latency and time sensitive. Jumbo Frame for Internet Purpose: You will not see any performance boost as the files that came across the internet does not support jumbo frame."
https://www.ankmax.com/newsinfo/1358641.html#:~:text=VoIP%20uses%20will%20always
%20not,does%20not%20support%20jumbo%20frame.
"To summarize this general best practice guide, you should NOT enable jumbo frame feature as a general home user."
NEW QUESTION 15
A user is required to log in to a main web application, which then grants the user access to all other programs needed to complete job-related tasks. Which of the following authentication methods does this setup describe?
- A. SSO
- B. RADIUS
- C. TACACS+
- D. Multifactor authentication
- E. 802.1X
Answer: A
Explanation:
The authentication method that this setup describes is SSO (Single Sign- On). SSO is a technique that allows a user to log in once to a main web application and then access multiple other applications or services without having to re-enter credentials. SSO simplifies the user experience and reduces the number of passwords to remember and manage. References: CompTIA Network+ N10-008 Certification Study Guide, page 371; The Official CompTIA Network+ Student Guide (Exam N10-008), page 14-5.
NEW QUESTION 16
A technician is equipped with a tablet, a smartphone, and a laptop to troubleshoot a switch with the help of support over the phone. However, the technician is having issues interconnecting all these tools in troubleshooting the switch. Which Of the following should the technician use to gain connectivity?
- A. PAN
- B. WAN
- C. LAN
- D. MAN
Answer: A
Explanation:
A PAN stands for Personal Area Network and it is a type of network that connects devices within a small range, such as a few meters. A PAN can use wireless technologies such as Bluetooth or Wi-Fi to interconnect devices such as tablets, smartphones, and laptops. A technician can use a PAN to gain connectivity among these tools and troubleshoot the switch.
References: Network+ Study Guide Objective 1.2: Explain devices, applications, protocols and services at their appropriate OSI layers.
NEW QUESTION 17
At which of the following OSI model layers does routing occur?
- A. Data link
- B. Transport
- C. Physical
- D. Network
Answer: D
NEW QUESTION 18
A company joins a bank's financial network and establishes a connection to the clearinghouse servers in the range 192 168.124.0/27. An IT technician then realizes the range exists within the VM pool at the data center. Which of the following is the BEST way for the technician to connect to the bank's servers?
- A. NAT
- B. PAT
- C. CIDR
- D. SLAAC
Answer: A
NEW QUESTION 19
A divide-and-conquer approach is a troubleshooting method that involves breaking a complex problem into smaller and more manageable parts, and then testing each part to isolate the cause of the problem. In this scenario, the technician is using a divide-and- conquer approach by pinging the default gateway and DNS server of the workstation, which are two possible sources of connectivity issues. By pinging these devices, the technician can determine if the problem is related to the local network or the external network.
Which of the following most likely requires the use of subinterfaces?
- A. A router with only one available LAN port
- B. A firewall performing deep packet inspection
- C. A hub utilizing jumbo frames
- D. A switch using Spanning Tree Protocol
Answer: A
Explanation:
Subinterfaces are logical divisions of a physical interface that allow a router to communicate with multiple networks using a single LAN port. Subinterfaces can have different IP addresses, VLANs, and routing protocols. They are useful for reducing the number of physical interfaces and cables needed, as well as improving network performance and security.
References:
✑ Subinterfaces - CompTIA Network+ N10-008 Domain 1.21 - YouTube1
✑ CompTIA Network+ Certification Exam Objectives, page 92
NEW QUESTION 20
A technician is installing the Wi-Fi infrastructure for legacy industrial machinery at a warehouse. The equipment only supports 802.11a and 802.11b standards. Speed of transmission is the top business requirement. Which of the following is the correct maximum speed for this scenario?
- A. 11Mbps
- B. 54Mbps
- C. 128Mbps
- D. 144Mbps
Answer: B
Explanation:
802.11b (Wi-Fi 1) 11 Mbps
100 meter maximum effective range 802.11a (Wi-Fi 2)
54 Mbps
50 meter maximum effective range
NEW QUESTION 21
......
Recommend!! Get the Full N10-009 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/N10-009-exam-dumps.html (New 111 Q&As Version)
