Our pass rate is high to 98.9% and the similarity percentage between our 156-215.80 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Check-Point 156-215.80 exam in just one try? I am currently studying for the Check-Point 156-215.80 exam. Latest Check-Point 156-215.80 Test exam practice questions and answers, Try Check-Point 156-215.80 Brain Dumps First.
Also have 156-215.80 free dumps questions for you:
NEW QUESTION 1
Fill in the blank: Browser-based Authentication sends users to a web page to acquire identities using ____ .
- A. User Directory
- B. Captive Portal and Transparent Kerberos Authentication
- C. Captive Portal
- D. UserCheck
Answer: B
Explanation:
To enable Identity Awareness:
Log in to SmartDashboard.
From the Network Objects tree, expand the Check Point branch.
Double-click the Security Gateway on which to enable Identity Awareness.
In the Software Blades section, select Identity Awareness on the Network Security tab.
The Identity Awareness
Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
NEW QUESTION 2
In the Check Point three-tiered architecture, which of the following is NOT a function of the Security Management Server (Security Management Server)?
- A. Display policies and logs on the administrator's workstation.
- B. Verify and compile Security Policies.
- C. Processing and sending alerts such as SNMP traps and email notifications.
- D. Store firewall logs to hard drive storage.
Answer: A
NEW QUESTION 3
What are the three authentication methods for SIC?
- A. Passwords, Users, and standards-based SSL for the creation of security channels
- B. Certificates, standards-based SSL for the creation of secure channels, and 3DES or AES128 for encryption
- C. Packet Filtering, certificates, and 3DES or AES128 for encryption
- D. Certificates, Passwords, and Tokens
Answer: B
Explanation:
Secure Internal Communication (SIC)
Secure Internal Communication (SIC) lets Check Point platforms and products authenticate with each other. The SIC procedure creates a trusted status between gateways, management servers and other Check Point components. SIC is required to install polices on gateways and to send logs between gateways and management servers.
These security measures make sure of the safety of SIC:
Certificates for authentication
Standards-based SSL for the creation of the secure channel
3DES for encryption
References:
NEW QUESTION 4
When you upload a package or license to the appropriate repository in SmartUpdate, where is the package or license stored
- A. Security Gateway
- B. Check Point user center
- C. Security Management Server
- D. SmartConsole installed device
Answer: C
Explanation:
SmartUpdate installs two repositories on the Security Management server:
License & Contract Repository, which is stored on all platforms in the directory $FWDIR\conf\.
Package Repository, which is stored:
on Windows machines in C:\SUroot.
on UNIX machines in /var/suroot.
The Package Repository requires a separate license, in addition to the license for the Security Management server. This license should stipulate the number of nodes that can be managed in the Package Repository.
NEW QUESTION 5
Which SmartConsole component can Administrators use to track changes to the Rule Base?
- A. WebUI
- B. SmartView Tracker
- C. SmartView Monitor
- D. SmartReporter
Answer: B
NEW QUESTION 6
Jennifer McHanry is CEO of ACME. She recently bought her own personal iPad. She wants use her iPad to access the internal Finance Web server. Because the iPad is not a member of the Active Directory domain, she cannot identify seamlessly with AD Query. However, she can enter her AD credentials in the Captive Portal and then get the same access as on her office computer. Her access to resources is based on rules in the R77 Firewall Rule Base.
To make this scenario work, the IT administrator must:
1) Enable Identity Awareness on a gateway and select Captive Portal as one of the Identity Sources.
2) In the Portal Settings window in the User Access section, make sure that Name and password login is selected.
3) Create a new rule in the Firewall Rule Base to let Jennifer McHanry access network destinations. Select accept as the Action.
4) Install policy.
Ms McHanry tries to access the resource but is unable. What should she do?
- A. Have the security administrator select the Action field of the Firewall Rule “Redirect HTTP connections to an authentication (captive) portal”.
- B. Have the security administrator reboot the firewall.
- C. Have the security administrator select Any for the Machines tab in the appropriate Access Role.
- D. Install the Identity Awareness agent on her iPad.
Answer: A
NEW QUESTION 7
How would you deploy TE250X Check Point appliance just for email traffic and in-line mode without a Check Point Security Gateway?
- A. Install appliance TE250X on SpanPort on LAN switch in MTA mode
- B. Install appliance TE250X in standalone mode and setup MTA
- C. You can utilize only Check Point Cloud Services for this scenario
- D. It is not possible, always Check Point SGW is needed to forward emails to SandBlast appliance
Answer: C
NEW QUESTION 8
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
- A. Source Address
- B. Destination Address
- C. TCP Acknowledgment Number
- D. Source Port
Answer: C
NEW QUESTION 9
By default, which port does the WebUI listen on?
- A. 80
- B. 4434
- C. 443
- D. 8080
Answer: C
Explanation:
To configure Security Management Server on Gaia:
Open a browser to the WebUI: https:<//Gaia management IP address>
NEW QUESTION 10
The Gaia operating system supports which routing protocols?
- A. BGP, OSPF, RIP
- B. BGP, OSPF, EIGRP, PIM, IGMP
- C. BGP, OSPF, RIP, PIM, IGMP
- D. BGP, OSPF, RIP, EIGRP
Answer: A
Explanation:
The Advanced Routing Suite
The Advanced Routing Suite CLI is available as part of the Advanced Networking Software Blade.
For organizations looking to implement scalable, fault-tolerant, secure networks, the Advanced Networking blade enables them to run industry-standard dynamic routing protocols including BGP, OSPF, RIPv1, and RIPv2 on security gateways. OSPF, RIPv1, and RIPv2 enable dynamic routing over a single autonomous system—like a single department, company, or service provider—to avoid network failures. BGP provides dynamic routing support across more complex networks involving multiple autonomous systems—such as when a company uses two service providers or divides a network into multiple areas with different administrators responsible for the performance of each.
NEW QUESTION 11
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule base and checked for viruses. But it is not accelerated. What is the most likely reason that the traffic is not accelerated?
- A. There is a virus foun
- B. Traffic is still allowed but not accelerated
- C. The connection required a Security server
- D. Acceleration is not enabled
- E. The traffic is originating from the gateway itself
Answer: D
NEW QUESTION 12
Anti-Spoofing is typically set up on which object type?
- A. Security Gateway
- B. Host
- C. Security Management object
- D. Network
Answer: A
NEW QUESTION 13
Which NAT rules are prioritized first?
- A. Post-Automatic/Manual NAT rules
- B. Manual/Pre-Automatic NAT
- C. Automatic Hide NAT
- D. Automatic Static NAT
Answer: B
NEW QUESTION 14
Fill in the blank: The _____ feature allows administrators to share a policy with other policy packages.
- A. Shared policy packages
- B. Shared policies
- C. Concurrent policy packages
- D. Concurrent policies
Answer: A
NEW QUESTION 15
Fill in the blanks: The Application Layer Firewalls inspect traffic through the ____ layer(s) of the TCP/IP model and up to and including the ____ layer.
- A. Lower; Application
- B. First two; Internet
- C. First two; Transport
- D. Upper; Application
Answer: A
NEW QUESTION 16
Choose the SmartLog property that is TRUE.
- A. SmartLog has been an option since release R71.10.
- B. SmartLog is not a Check Point product.
- C. SmartLog and SmartView Tracker are mutually exclusive.
- D. SmartLog is a client of SmartConsole that enables enterprises to centrally track log records and security activity with Google-like search.
Answer: D
NEW QUESTION 17
What protocol is specifically used for clustered environments?
- A. Clustered Protocol
- B. Synchronized Cluster Protocol
- C. Control Cluster Protocol
- D. Cluster Control Protocol
Answer: D
NEW QUESTION 18
MegaCorp's security infrastructure separates Security Gateways geographically. You must request a central license for one remote Security Gateway.
How do you apply the license?
- A. Using the remote Gateway's IP address, and attaching the license to the remote Gateway via SmartUpdate.
- B. Using your Security Management Server's IP address, and attaching the license to the remote Gateway via SmartUpdate.
- C. Using the remote Gateway's IP address, and applying the license locally with command cplic put.
- D. Using each of the Gateway's IP addresses, and applying the licenses on the Security Management Server with the command cprlic put.
Answer: B
NEW QUESTION 19
Which of the following actions do NOT take place in IKE Phase 1?
- A. Peers agree on encryption method.
- B. Diffie-Hellman key is combined with the key material to produce the symmetrical IPsec key.
- C. Peers agree on integrity method.
- D. Each side generates a session key from its private key and peer's public key.
Answer: B
NEW QUESTION 20
Which of the following is NOT an attribute of packer acceleration?
- A. Source address
- B. Protocol
- C. Destination port
- D. Application Awareness
Answer: D
NEW QUESTION 21
Mesh and Star are two types of VPN topologies. Which statement below is TRUE about these types of communities?
- A. A star community requires Check Point gateways, as it is a Check Point proprietary technology.
- B. In a star community, satellite gateways cannot communicate with each other.
- C. In a mesh community, member gateways cannot communicate directly with each other.
- D. In a mesh community, all members can create a tunnel with any other member.
Answer: D
NEW QUESTION 22
Phase 1 of the two-phase negotiation process conducted by IKE operates in a_____ mode.
- A. Main
- B. Authentication
- C. Quick
- D. High Alert
Answer: A
NEW QUESTION 23
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
- A. None, Security Management Server would be installed by itself.
- B. SmartConsole
- C. SecureClient
- D. SmartEvent
Answer: D
Explanation:
There are different deployment scenarios for Check Point software products.
Standalone Deployment - The Security Management Server and the Security Gateway are installed on the same computer or appliance.
NEW QUESTION 24
Which two of these Check Point Protocols are used by ?
- A. ELA and CPD
- B. FWD and LEA
- C. FWD and CPLOG
- D. ELA and CPLOG
Answer: B
NEW QUESTION 25
Examine the following Rule Base.
What can we infer about the recent changes made to the Rule Base?
- A. Rule 7 was created by the 'admin' administrator in the current session
- B. 8 changes have been made by administrators since the last policy installation
- C. The rules 1, 5 and 6 cannot be edited by the 'admin' administrator
- D. Rule 1 and object webserver are locked by another administrator
Answer: D
Explanation:
On top of the print screen there is a number "8" which consists for the number of changes made and not saved. Session Management Toolbar (top of SmartConsole)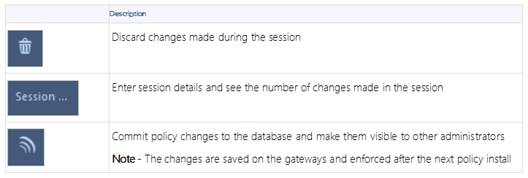
NEW QUESTION 26
......
P.S. Allfreedumps.com now are offering 100% pass ensure 156-215.80 dumps! All 156-215.80 exam questions have been updated with correct answers: https://www.allfreedumps.com/156-215.80-dumps.html (485 New Questions)
