Exam Code: CS0-002 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: CompTIA Cybersecurity Analyst (CySA+) Certification Exam
Certification Provider: CompTIA
Free Today! Guaranteed Training- Pass CS0-002 Exam.
Free CS0-002 Demo Online For CompTIA Certifitcation:
NEW QUESTION 1
A web-based front end for a business intelligence application uses pass-through authentication to authenticate users The application then uses a service account, to perform queries and look up data m a database A security analyst discovers employees are accessing data sets they have not been authorized to use. Which of the following will fix the cause of the issue?
- A. Change the security model to force the users to access the database as themselves
- B. Parameterize queries to prevent unauthorized SQL queries against the database
- C. Configure database security logging using syslog or a SIEM
- D. Enforce unique session IDs so users do not get a reused session ID
Answer: B
NEW QUESTION 2
Approximately 100 employees at your company have received a phishing email. As a security analyst you have been tasked with handling this situation.
INSTRUCTIONS
Review the information provided and determine the following:
* 1. How many employees clicked on the link in the phishing email?
* 2. On how many workstations was the malware installed?
* 3. What is the executable file name or the malware?
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Select the following answer as per diagram below:
NEW QUESTION 3
A security technician is testing a solution that will prevent outside entities from spoofing the company's email domain, which is comptia.org. The testing is successful, and the security technician is prepared to fully implement the solution.
Which of the following actions should the technician take to accomplish this task?
- A. Add TXT @ "v=spf1 mx include:_spf.comptia.org all" to the DNS record.
- B. Add TXT @ "v=spf1 mx include:_spf.comptia.org all" to the email server.
- C. Add TXT @ "v=spf1 mx include:_spf.comptia.org +all" to the domain controller.
- D. Add TXT @ "v=spf1 mx include:_spf.comptia.org +all" to the web server.
Answer: A
NEW QUESTION 4
While analyzing logs from a WAF, a cybersecurity analyst finds the following: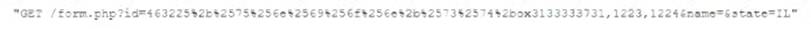
Which of the following BEST describes what the analyst has found?
- A. This is an encrypted GET HTTP request
- B. A packet is being used to bypass the WAF
- C. This is an encrypted packet
- D. This is an encoded WAF bypass
Answer: D
NEW QUESTION 5
Which of the following technologies can be used to house the entropy keys for task encryption on desktops and laptops?
- A. Self-encrypting drive
- B. Bus encryption
- C. TPM
- D. HSM
Answer: A
NEW QUESTION 6
A security analyst gathered forensics from a recent intrusion in preparation for legal proceedings. The analyst used EnCase to gather the digital forensics. cloned the hard drive, and took the hard drive home for further analysis. Which of the following of the security analyst violate?
- A. Cloning procedures
- B. Chain of custody
- C. Hashing procedures
- D. Virtualization
Answer: B
NEW QUESTION 7
A small electronics company decides to use a contractor to assist with the development of a new FPGA-based device. Several of the development phases will occur off-site at the contractor's labs.
Which of the following is the main concern a security analyst should have with this arrangement?
- A. Making multiple trips between development sites increases the chance of physical damage to the FPGAs.
- B. Moving the FPGAs between development sites will lessen the time that is available for security testing.
- C. Development phases occurring at multiple sites may produce change management issues.
- D. FPGA applications are easily cloned, increasing the possibility of intellectual property theft.
Answer: B
NEW QUESTION 8
An organization was alerted to a possible compromise after its proprietary data was found for sale on the Internet. An analyst is reviewing the logs from the next-generation UTM in an attempt to find evidence of this breach. Given the following output: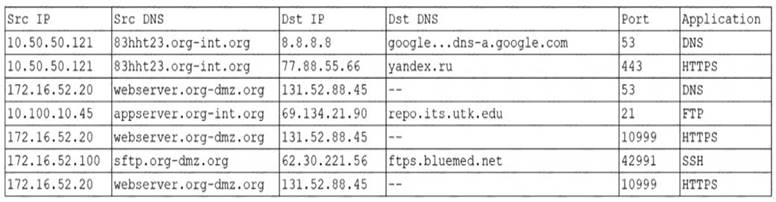
Which of the following should be the focus of the investigation?
- A. webserver.org-dmz.org
- B. sftp.org-dmz.org
- C. 83hht23.org-int.org
- D. ftps.bluemed.net
Answer: A
NEW QUESTION 9
Which of the following is the MOST important objective of a post-incident review?
- A. Capture lessons learned and improve incident response processes
- B. Develop a process for containment and continue improvement efforts
- C. Identify new technologies and strategies to remediate
- D. Identify a new management strategy
Answer: A
NEW QUESTION 10
Which of the following sets of attributes BEST illustrates the characteristics of an insider threat from a security perspective?
- A. Unauthorized, unintentional, benign
- B. Unauthorized, intentional, malicious
- C. Authorized, intentional, malicious
- D. Authorized, unintentional, benign
Answer: C
NEW QUESTION 11
An analyst identifies multiple instances of node-to-node communication between several endpoints within the 10.200.2.0/24 network and a user machine at the IP address 10.200.2.5. This user machine at the IP address 10.200.2.5 is also identified as initiating outbound communication during atypical business hours with several IP addresses that have recently appeared on threat feeds.
Which of the following can be inferred from this activity?
- A. 10.200.2.0/24 is infected with ransomware.
- B. 10.200.2.0/24 is not routable address space.
- C. 10.200.2.5 is a rogue endpoint.
- D. 10.200.2.5 is exfiltrating data.
Answer: D
NEW QUESTION 12
During an incident, a cybersecurity analyst found several entries in the web server logs that are related to an IP with a bad reputation . Which of the following would cause the analyst to further review the incident?
A)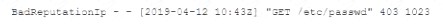
B)
C)
D)
E)
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer: D
NEW QUESTION 13
A security analyst has received reports of very slow, intermittent access to a public-facing corporate server. Suspecting the system may be compromised, the analyst runs the following commands: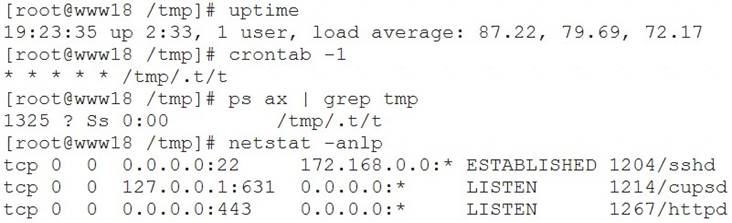
Based on the output from the above commands, which of the following should the analyst do NEXT to further the investigation?
- A. Run crontab -r; rm -rf /tmp/.t to remove and disable the malware on the system.
- B. Examine the server logs for further indicators of compromise of a web application.
- C. Run kill -9 1325 to bring the load average down so the server is usable again.
- D. Perform a binary analysis on the /tmp/.t/t file, as it is likely to be a rogue SSHD server.
Answer: B
NEW QUESTION 14
Ransomware is identified on a company's network that affects both Windows and MAC hosts. The command and control channel for encryption for this variant uses TCP ports from 11000 to 65000. The channel goes to good1. Iholdbadkeys.com, which resolves to IP address 72.172.16.2.
Which of the following is the MOST effective way to prevent any newly infected systems from actually encrypting the data on connected network drives while causing the least disruption to normal Internet traffic?
- A. Block all outbound traffic to web host good1 iholdbadkeys.com at the border gateway.
- B. Block all outbound TCP connections to IP host address 172.172.16.2 at the border gateway.
- C. Block all outbound traffic on TCP ports 11000 to 65000 at the border gateway.
- D. Block all outbound traffic on TCP ports 11000 to 65000 to IP host address 172.172.16.2 at the border gateway.
Answer: A
NEW QUESTION 15
An audit has revealed an organization is utilizing a large number of servers that are running unsupported operating systems.
As part of the management response phase of the audit, which of the following would BEST demonstrate senior management is appropriately aware of and addressing the issue?
- A. Copies of prior audits that did not identify the servers as an issue
- B. Project plans relating to the replacement of the servers that were approved by management
- C. Minutes from meetings in which risk assessment activities addressing the servers were discussed
- D. ACLs from perimeter firewalls showing blocked access to the servers
- E. Copies of change orders relating to the vulnerable servers
Answer: C
NEW QUESTION 16
......
P.S. Easily pass CS0-002 Exam with 186 Q&As Downloadfreepdf.net Dumps & pdf Version, Welcome to Download the Newest Downloadfreepdf.net CS0-002 Dumps: https://www.downloadfreepdf.net/CS0-002-pdf-download.html (186 New Questions)
