We provide real CS0-002 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass CompTIA CS0-002 Exam quickly & easily. The CS0-002 PDF type is available for reading and printing. You can print more and practice many times. With the help of our CompTIA CS0-002 dumps pdf and vce product and material, you can easily pass the CS0-002 exam.
Check CS0-002 free dumps before getting the full version:
NEW QUESTION 1
Bootloader malware was recently discovered on several company workstations. All the workstations run Windows and are current models with UEFI capability.
Which of the following UEFI settings is the MOST likely cause of the infections?
- A. Compatibility mode
- B. Secure boot mode
- C. Native mode
- D. Fast boot mode
Answer: A
NEW QUESTION 2
A security analyst received an email with the following key: Xj3XJ3LLc
A second security analyst received an email with following key: 3XJ3xjcLLC
The security manager has informed the two analysts that the email they received is a key that allows access to the company’s financial segment for maintenance. This is an example of:
- A. dual control
- B. private key encryption
- C. separation of duties
- D. public key encryption
- E. two-factor authentication
Answer: A
NEW QUESTION 3
An audit has revealed an organization is utilizing a large number of servers that are running unsupported operating systems.
As part of the management response phase of the audit, which of the following would BEST demonstrate senior management is appropriately aware of and addressing the issue?
- A. Copies of prior audits that did not identify the servers as an issue
- B. Project plans relating to the replacement of the servers that were approved by management
- C. Minutes from meetings in which risk assessment activities addressing the servers were discussed
- D. ACLs from perimeter firewalls showing blocked access to the servers
- E. Copies of change orders relating to the vulnerable servers
Answer: C
NEW QUESTION 4
A malicious hacker wants to gather guest credentials on a hotel 802.11 network. Which of the following tools is the malicious hacker going to use to gain access to information found on the hotel network?
- A. Nikto
- B. Aircrak-ng
- C. Nessus
- D. tcpdump
Answer: A
NEW QUESTION 5
A security analyst has discovered trial developers have installed browsers on all development servers in the company's cloud infrastructure and are using them to browse the Internet. Which of the following changes should the security analyst make to BEST protect the environment?
- A. Create a security rule that blocks Internet access in the development VPC
- B. Place a jumpbox m between the developers' workstations and the development VPC
- C. Remove the administrator profile from the developer user group in identity and access management
- D. Create an alert that is triggered when a developer installs an application on a server
Answer: A
NEW QUESTION 6
A security analyst is reviewing the logs from an internal chat server. The chat.log file is too large to review manually, so the analyst wants to create a shorter log file that only includes lines associated with a user demonstrating anomalous activity. Below is a snippet of the log: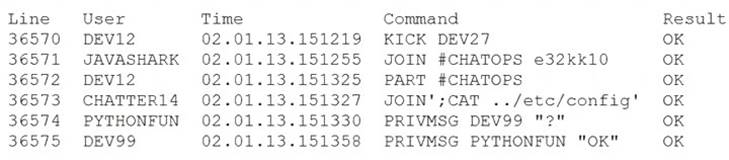
Which of the following commands would work BEST to achieve the desired result?
- A. grep -v chatter14 chat.log
- B. grep -i pythonfun chat.log
- C. grep -i javashark chat.log
- D. grep -v javashark chat.log
- E. grep -v pythonfun chat.log
- F. grep -i chatter14 chat.log
Answer: D
NEW QUESTION 7
An information security analyst observes anomalous behavior on the SCADA devices in a power plant. This behavior results in the industrial generators overheating and destabilizing the power supply.
Which of the following would BEST identify potential indicators of compromise?
- A. Use Burp Suite to capture packets to the SCADA device's IP.
- B. Use tcpdump to capture packets from the SCADA device IP.
- C. Use Wireshark to capture packets between SCADA devices and the management system.
- D. Use Nmap to capture packets from the management system to the SCADA devices.
Answer: C
NEW QUESTION 8
A security analyst needs to reduce the overall attack surface.
Which of the following infrastructure changes should the analyst recommend?
- A. Implement a honeypot.
- B. Air gap sensitive systems.
- C. Increase the network segmentation.
- D. Implement a cloud-based architecture.
Answer: C
NEW QUESTION 9
The security team at a large corporation is helping the payment-processing team to prepare for a regulatory compliance audit and meet the following objectives: Reduce the number of potential findings by the auditors.
Reduce the number of potential findings by the auditors. Limit the scope of the audit to only devices used by the payment-processing team for activities directly impacted by the regulations.
Limit the scope of the audit to only devices used by the payment-processing team for activities directly impacted by the regulations. Prevent the external-facing web infrastructure used by other teams from coming into scope.
Prevent the external-facing web infrastructure used by other teams from coming into scope. Limit the amount of exposure the company will face if the systems used by the payment-processing
Limit the amount of exposure the company will face if the systems used by the payment-processing
team are compromised.
Which of the following would be the MOST effective way for the security team to meet these objectives?
- A. Limit the permissions to prevent other employees from accessing data owned by the business unit.
- B. Segment the servers and systems used by the business unit from the rest of the network.
- C. Deploy patches to all servers and workstations across the entire organization.
- D. Implement full-disk encryption on the laptops used by employees of the payment-processing team.
Answer: B
NEW QUESTION 10
The inability to do remote updates of certificates, keys, software, and firmware is a security issue commonly associated with:
- A. web servers on private networks
- B. HVAC control systems
- C. smartphones
- D. firewalls and UTM devices
Answer: D
NEW QUESTION 11
A security manager has asked an analyst to provide feedback on the results of a penetration lest. After reviewing the results the manager requests information regarding the possible exploitation of vulnerabilities Much of the following information data points would be MOST useful for the analyst to provide to the security manager who would then communicate the risk factors to senior management? (Select TWO)
- A. Probability
- B. Adversary capability
- C. Attack vector
- D. Impact
- E. Classification
- F. Indicators of compromise
Answer: AD
NEW QUESTION 12
A company's modem response team is handling a threat that was identified on the network Security analysts have as at remote sites. Which of the following is the MOST appropriate next step in the incident response plan?
- A. Quarantine the web server
- B. Deploy virtual firewalls
- C. Capture a forensic image of the memory and disk
- D. Enable web server containerization
Answer: B
NEW QUESTION 13
A Chief Information Security Officer (CISO) is concerned the development team, which consists of contractors, has too much access to customer data. Developers use personal workstations, giving the company little to no visibility into the development activities.
Which of the following would be BEST to implement to alleviate the CISO's concern?
- A. DLP
- B. Encryption
- C. Test data
- D. NDA
Answer: D
NEW QUESTION 14
A security analyst is reviewing vulnerability scan results and notices new workstations are being flagged as having outdated antivirus signatures. The analyst observes the following plugin output:
Antivirus is installed on the remote host:
Installation path: C:\Program Files\AVProduct\Win32\ Product Engine: 14.12.101
Engine Version: 3.5.71
Scanner does not currently have information about AVProduct version 3.5.71. It may no longer be supported.
The engine version is out of date. The oldest supported version from the vendor is 4.2.11. The analyst uses the vendor's website to confirm the oldest supported version is correct. Which of the following BEST describes the situation?
- A. This is a false positive, and the scanning plugin needs to be updated by the vendor.
- B. This is a true negative, and the new computers have the correct version of the software.
- C. This is a true positive, and the new computers were imaged with an old version of the software.
- D. This is a false negative, and the new computers need to be updated by the desktop team.
Answer: C
NEW QUESTION 15
A security analyst discovers a vulnerability on an unpatched web server that is used for testing machine learning on Bing Data sets. Exploitation of the vulnerability could cost the organization $1.5 million in lost productivity. The server is located on an isolated network segment that has a 5% chance of being compromised. Which of the following is the value of this risk?
- A. $75.000
- B. $300.000
- C. $1.425 million
- D. $1.5 million
Answer: A
NEW QUESTION 16
......
Recommend!! Get the Full CS0-002 dumps in VCE and PDF From Dumpscollection.com, Welcome to Download: https://www.dumpscollection.net/dumps/CS0-002/ (New 220 Q&As Version)
