It is more faster and easier to pass the CompTIA CS0-002 exam by using Vivid CompTIA CompTIA Cybersecurity Analyst (CySA+) Certification Exam questuins and answers. Immediate access to the Most recent CS0-002 Exam and find the same core area CS0-002 questions with professionally verified answers, then PASS your exam with a high score now.
Free CS0-002 Demo Online For CompTIA Certifitcation:
NEW QUESTION 1
While preparing of an audit of information security controls in the environment an analyst outlines a framework control that has the following requirements:
• All sensitive data must be classified
• All sensitive data must be purged on a quarterly basis
• Certificates of disposal must remain on file for at least three years
This framework control is MOST likely classified as:
- A. prescriptive
- B. risk-based
- C. preventive
- D. corrective
Answer: A
NEW QUESTION 2
During an investigation, an incident responder intends to recover multiple pieces of digital media. Before removing the media, the responder should initiate:
- A. malware scans.
- B. secure communications.
- C. chain of custody forms.
- D. decryption tools.
Answer: C
NEW QUESTION 3
An analyst is working with a network engineer to resolve a vulnerability that was found in a piece of legacy hardware, which is critical to the operation of the organization's production line. The legacy hardware does not have third-party support, and the OEM manufacturer of the controller is no longer in operation. The analyst documents the activities and verifies these actions prevent remote exploitation of the vulnerability.
Which of the following would be the MOST appropriate to remediate the controller?
- A. Segment the network to constrain access to administrative interfaces.
- B. Replace the equipment that has third-party support.
- C. Remove the legacy hardware from the network.
- D. Install an IDS on the network between the switch and the legacy equipment.
Answer: A
NEW QUESTION 4
A security analyst gathered forensics from a recent intrusion in preparation for legal proceedings. The analyst used EnCase to gather the digital forensics. cloned the hard drive, and took the hard drive home for further analysis. Which of the following of the security analyst violate?
- A. Cloning procedures
- B. Chain of custody
- C. Hashing procedures
- D. Virtualization
Answer: B
NEW QUESTION 5
A security analyst implemented a solution that would analyze the attacks that the organization’s firewalls failed to prevent. The analyst used the existing systems to enact the solution and executed the following command.
S sudo nc -1 -v -c maildemon . py 25 caplog, txt
Which of the following solutions did the analyst implement?
- A. Log collector
- B. Crontab mail script
- C. Snikhole
- D. Honeypot
Answer: A
NEW QUESTION 6
A cybersecurity analyst is reading a daily intelligence digest of new vulnerabilities The type of vulnerability that should be disseminated FIRST is one that:
- A. enables remote code execution that is being exploited in the wild.
- B. enables data leakage but is not known to be m the environment
- C. enables lateral movement and was reported as a proof of concept
- D. affected the organization in the past but was probably contained and eradicated
Answer: C
NEW QUESTION 7
A security team is implementing a new vulnerability management program in an environment that has a historically poor security posture. The team is aware of issues patch management in the environment and expects a large number of findings. Which of the following would be the MOST efficient way to increase the security posture of the organization in the shortest amount of time?
- A. Create an SLA stating that remediation actions must occur within 30 days of discovery for all levels of vulnerabilities.
- B. Incorporate prioritization levels into the remediation process and address critical findings first.
- C. Create classification criteria for data residing on different servers and provide remediation only for servers housing sensitive data.
- D. Implement a change control policy that allows the security team to quickly deploy patches in the production environment to reduce the risk of any vulnerabilities found.
Answer: B
NEW QUESTION 8
A security analyst was alerted to a tile integrity monitoring event based on a change to the vhost-paymonts .c onf file The output of the diff command against the known-good backup reads as follows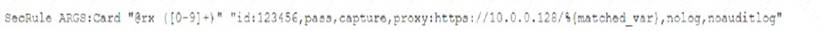
Which of the following MOST likely occurred?
- A. The file was altered to accept payments without charging the cards
- B. The file was altered to avoid logging credit card information
- C. The file was altered to verify the card numbers are valid.
- D. The file was altered to harvest credit card numbers
Answer: A
NEW QUESTION 9
The help desk noticed a security analyst that emails from a new email server are not being sent out. The new email server was recently to the existing ones. The analyst runs the following command on the new server.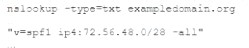
Given the output, which of the following should the security analyst check NEXT?
- A. The DNS name of the new email server
- B. The version of SPF that is being used
- C. The IP address of the new email server
- D. The DMARC policy
Answer: B
NEW QUESTION 10
Which of the following technologies can be used to house the entropy keys for task encryption on desktops and laptops?
- A. Self-encrypting drive
- B. Bus encryption
- C. TPM
- D. HSM
Answer: A
NEW QUESTION 11
A small electronics company decides to use a contractor to assist with the development of a new FPGA-based device. Several of the development phases will occur off-site at the contractor's labs.
Which of the following is the main concern a security analyst should have with this arrangement?
- A. Making multiple trips between development sites increases the chance of physical damage to the FPGAs.
- B. Moving the FPGAs between development sites will lessen the time that is available for security testing.
- C. Development phases occurring at multiple sites may produce change management issues.
- D. FPGA applications are easily cloned, increasing the possibility of intellectual property theft.
Answer: B
NEW QUESTION 12
A company recently experienced a break-in whereby a number of hardware assets were stolen through unauthorized access at the back of the building. Which of the following would BEST prevent this type of theft from occurring in the future?
- A. Motion detection
- B. Perimeter fencing
- C. Monitored security cameras
- D. Badged entry
Answer: A
NEW QUESTION 13
After receiving reports latency, a security analyst performs an Nmap scan and observes the following output: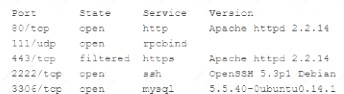
Which of the following suggests the system that produced output was compromised?
- A. Secure shell is operating of compromise on this system.
- B. There are no indicators of compromise on this system.
- C. MySQL services is identified on a standard PostgreSQL port.
- D. Standard HTP is open on the system and should be closed.
Answer: B
NEW QUESTION 14
A developer wrote a script to make names and other Pll data unidentifiable before loading a database export into the testing system Which of the following describes the type of control that is being used?
- A. Data encoding
- B. Data masking
- C. Data loss prevention
- D. Data classification
Answer: C
NEW QUESTION 15
Which of the following are components of the intelligence cycle? (Select TWO.)
- A. Collection
- B. Normalization
- C. Response
- D. Analysis
- E. Correction
- F. Dissension
Answer: BE
NEW QUESTION 16
......
P.S. Easily pass CS0-002 Exam with 220 Q&As Allfreedumps.com Dumps & pdf Version, Welcome to Download the Newest Allfreedumps.com CS0-002 Dumps: https://www.allfreedumps.com/CS0-002-dumps.html (220 New Questions)
