Want to know Exambible CS0-002 Exam practice test features? Want to lear more about CompTIA CompTIA Cybersecurity Analyst (CySA+) Certification Exam certification experience? Study Highest Quality CompTIA CS0-002 answers to Refresh CS0-002 questions at Exambible. Gat a success with an absolute guarantee to pass CompTIA CS0-002 (CompTIA Cybersecurity Analyst (CySA+) Certification Exam) test on your first attempt.
CompTIA CS0-002 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which of the following would MOST likely be included in the incident response procedure after a security breach of customer PII?
- A. Human resources
- B. Public relations
- C. Marketing
- D. Internal network operations center
Answer: B
NEW QUESTION 2
Which of the following types of policies is used to regulate data storage on the network?
- A. Password
- B. Acceptable use
- C. Account management
- D. Retention
Answer: D
NEW QUESTION 3
A security analyst is supporting an embedded software team. Which of the following is the BEST recommendation to ensure proper error handling at runtime?
- A. Perform static code analysis.
- B. Require application fuzzing.
- C. Enforce input validation
- D. Perform a code review
Answer: B
NEW QUESTION 4
A cybersecurity analyst is supposing an incident response effort via threat intelligence. Which of the following is the analyst MOST likely executing?
- A. Requirements analysis and collection planning
- B. Containment and eradication
- C. Recovery and post-incident review
- D. Indicator enrichment and research pivoting
Answer: D
NEW QUESTION 5
An analyst is performing penetration testing and vulnerability assessment activities against a new vehicle automation platform.
Which of the following is MOST likely an attack vector that is being utilized as part of the testing and assessment?
- A. FaaS
- B. RTOS
- C. SoC
- D. GPS
- E. CAN bus
Answer: E
NEW QUESTION 6
A security analyst is investigating a system compromise. The analyst verities the system was up to date on OS patches at the time of the compromise. Which of the following describes the type of vulnerability that was MOST likely expiated?
- A. Insider threat
- B. Buffer overflow
- C. Advanced persistent threat
- D. Zero day
Answer: D
NEW QUESTION 7
A company recently experienced a break-in whereby a number of hardware assets were stolen through unauthorized access at the back of the building. Which of the following would BEST prevent this type of theft from occurring in the future?
- A. Motion detection
- B. Perimeter fencing
- C. Monitored security cameras
- D. Badged entry
Answer: A
NEW QUESTION 8
A security analyst needs to assess the web server versions on a list of hosts to determine which are running a vulnerable version of the software and output that list into an XML file named Webserverlist. Xml. The host list is provided in a file named werbserverlist,text. Which of the fallowing Nmap commands would BEST accomplish this goal?
A)
B)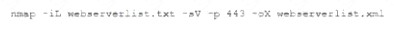
C)
D)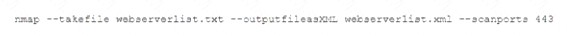
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: A
NEW QUESTION 9
An executive assistant wants to onboard a new cloud based product to help with business analytics and dashboarding. When of the following would be the BEST integration option for the service?
- A. Manually log in to the service and upload data files on a regular basis.
- B. Have the internal development team script connectivity and file translate to the new service.
- C. Create a dedicated SFTP sue and schedule transfers to ensue file transport security
- D. Utilize the cloud products API for supported and ongoing integrations
Answer: A
NEW QUESTION 10
A security analyst has observed several incidents within an organization that are affecting one specific piece of hardware on the network. Further investigation reveals the equipment vendor previously released a patch.
Which of the following is the MOST appropriate threat classification for these incidents?
- A. Known threat
- B. Zero day
- C. Unknown threat
- D. Advanced persistent threat
Answer: B
NEW QUESTION 11
After receiving reports latency, a security analyst performs an Nmap scan and observes the following output: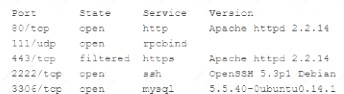
Which of the following suggests the system that produced output was compromised?
- A. Secure shell is operating of compromise on this system.
- B. There are no indicators of compromise on this system.
- C. MySQL services is identified on a standard PostgreSQL port.
- D. Standard HTP is open on the system and should be closed.
Answer: B
NEW QUESTION 12
An information security analyst observes anomalous behavior on the SCADA devices in a power plant. This behavior results in the industrial generators overheating and destabilizing the power supply.
Which of the following would BEST identify potential indicators of compromise?
- A. Use Burp Suite to capture packets to the SCADA device's IP.
- B. Use tcpdump to capture packets from the SCADA device IP.
- C. Use Wireshark to capture packets between SCADA devices and the management system.
- D. Use Nmap to capture packets from the management system to the SCADA devices.
Answer: C
NEW QUESTION 13
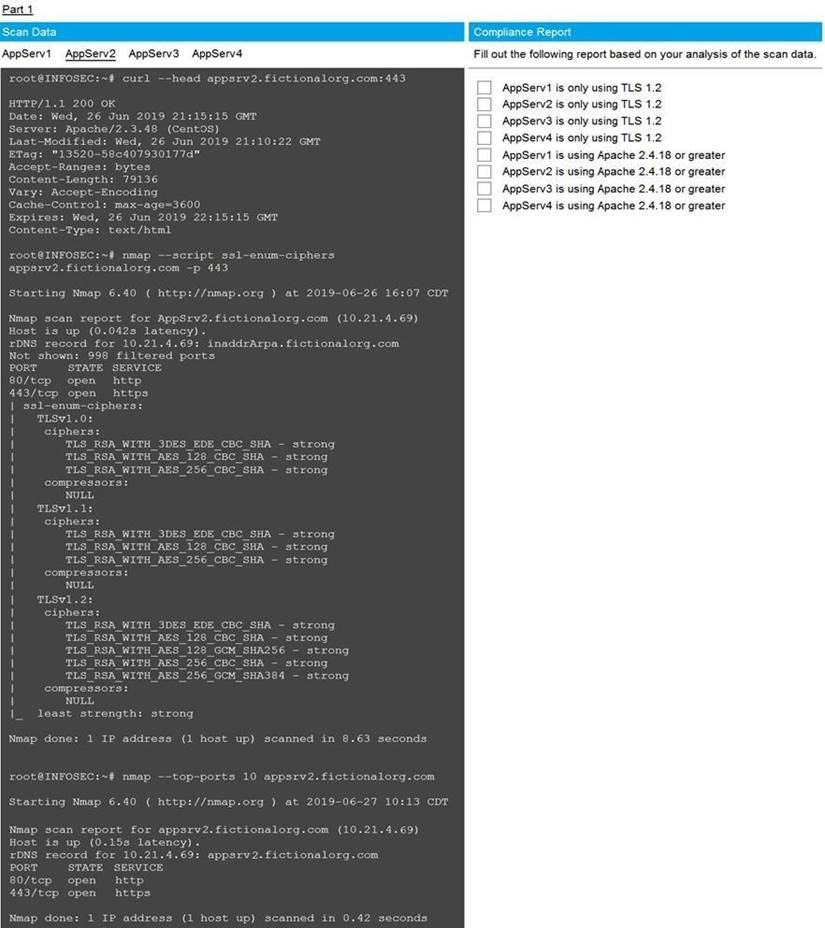
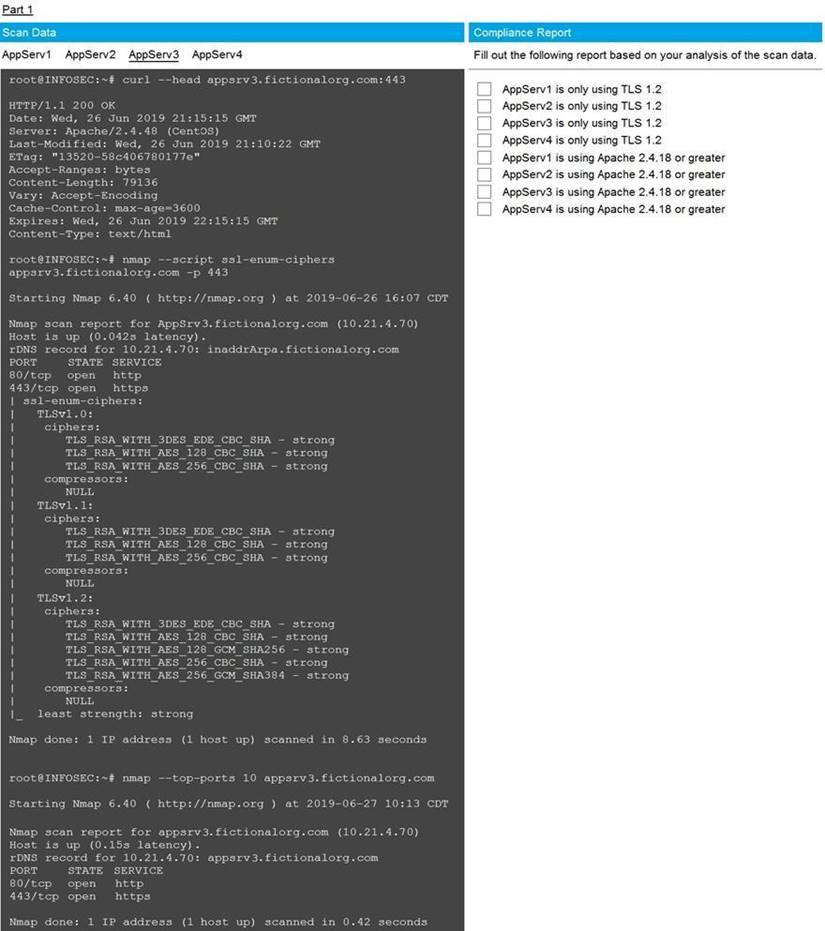
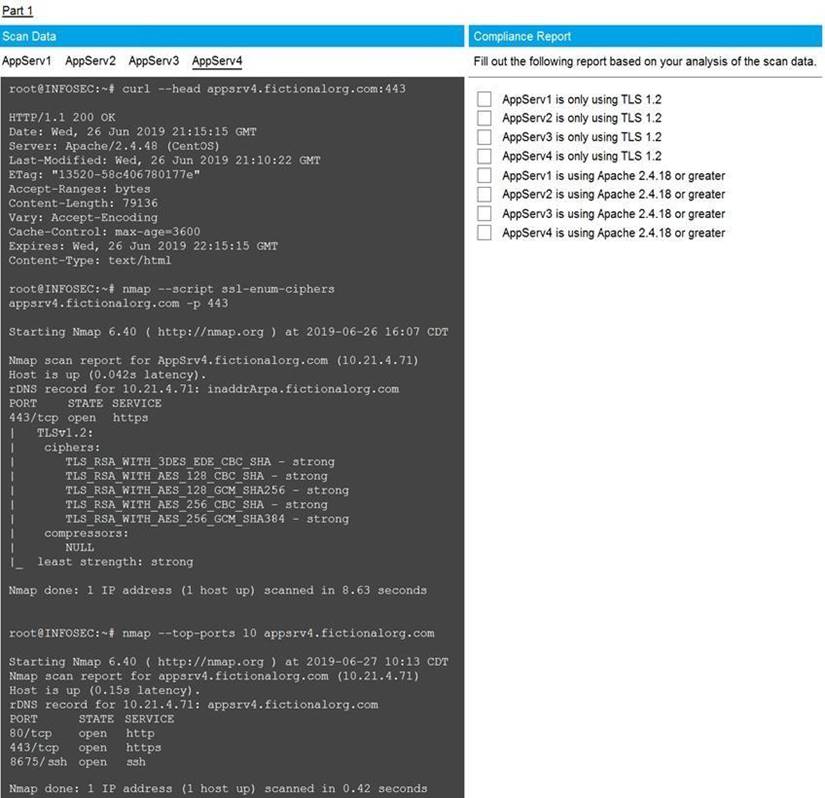
You are a cybersecurity analyst tasked with interpreting scan data from Company A's servers. You must verify the requirements are being met for all of the servers and recommend changes if you find they are not.
The company's hardening guidelines indicate the following:
• TLS 1.2 is the only version of TLS running.
• Apache 2.4.18 or greater should be used.
• Only default ports should be used. INSTRUCTIONS
Using the supplied data, record the status of compliance with the company's guidelines for each server.
The question contains two parts: make sure you complete Part 1 and Part 2. Make recommendations for issues based ONLY on the hardening guidelines provided.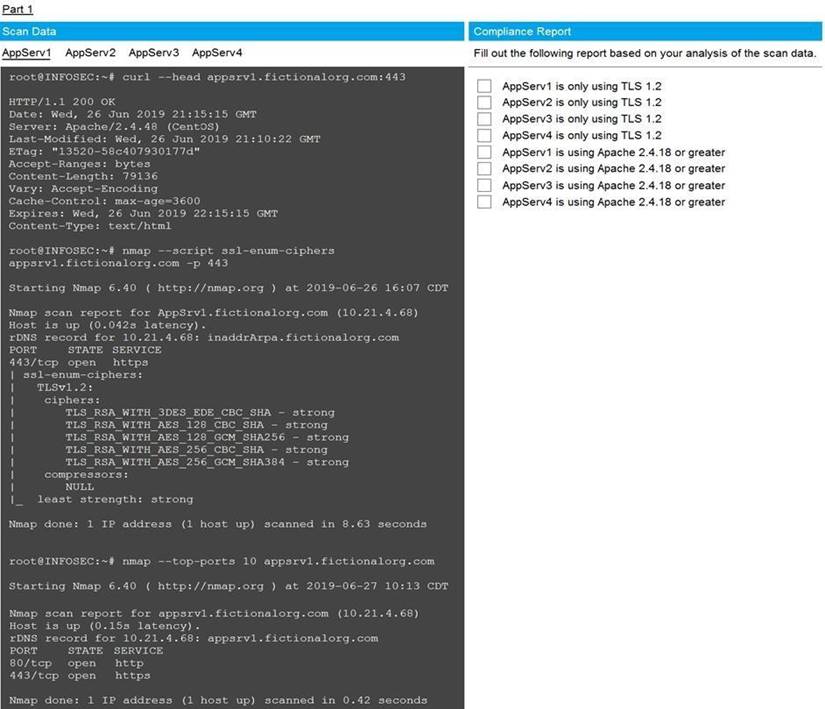

- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Part 1 Answer
Check on the following:
AppServ1 is only using TLS.1.2
AppServ4 is only using TLS.1.2
AppServ1 is using Apache 2.4.18 or greater
AppServ3 is using Apache 2.4.18 or greater
AppServ4 is using Apache 2.4.18 or greater
Part 2 Answer
Recommendation:
Recommendation is to disable TLS v1.1 on AppServ2 and AppServ3. Also upgrade AppServ2 Apache to version 2.4.48 from its current version of 2.3.48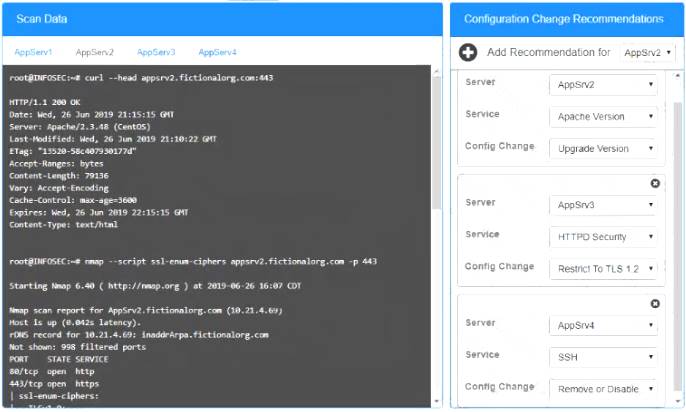
NEW QUESTION 14
As a proactive threat-hunting technique, hunters must develop situational cases based on likely attack scenarios derived from the available threat intelligence information. After forming the basis of the scenario, which of the following may the threat hunter construct to establish a framework for threat assessment?
- A. Critical asset list
- B. Threat vector
- C. Attack profile
- D. Hypothesis
Answer: A
NEW QUESTION 15
An organization wants to move non-essential services into a cloud computing environment. Management has a cost focus and would like to achieve a recovery time objective of 12 hours. Which of the following cloud recovery strategies would work BEST to attain the desired outcome?
- A. Duplicate all services in another instance and load balance between the instances.
- B. Establish a hot site with active replication to another region within the same cloud provider.
- C. Set up a warm disaster recovery site with the same cloud provider in a different region
- D. Configure the systems with a cold site at another cloud provider that can be used for failover.
Answer: C
NEW QUESTION 16
......
P.S. Easily pass CS0-002 Exam with 186 Q&As DumpSolutions.com Dumps & pdf Version, Welcome to Download the Newest DumpSolutions.com CS0-002 Dumps: https://www.dumpsolutions.com/CS0-002-dumps/ (186 New Questions)
