Exam Code: CS0-002 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: CompTIA Cybersecurity Analyst (CySA+) Certification Exam
Certification Provider: CompTIA
Free Today! Guaranteed Training- Pass CS0-002 Exam.
CompTIA CS0-002 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which of the following types of policies is used to regulate data storage on the network?
- A. Password
- B. Acceptable use
- C. Account management
- D. Retention
Answer: D
NEW QUESTION 2
An organization wants to move non-essential services into a cloud computing environment. Management has a cost focus and would like to achieve a recovery time objective of 12 hours. Which of the following cloud recovery strategies would work BEST to attain the desired outcome?
- A. Duplicate all services in another instance and load balance between the instances.
- B. Establish a hot site with active replication to another region within the same cloud provider.
- C. Set up a warm disaster recovery site with the same cloud provider in a different region
- D. Configure the systems with a cold site at another cloud provider that can be used for failover.
Answer: C
NEW QUESTION 3
A security analyst is trying to determine if a host is active on a network. The analyst first attempts the following: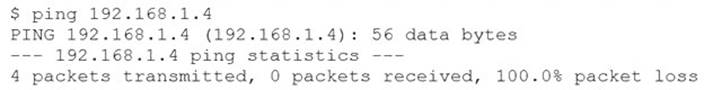
The analyst runs the following command next: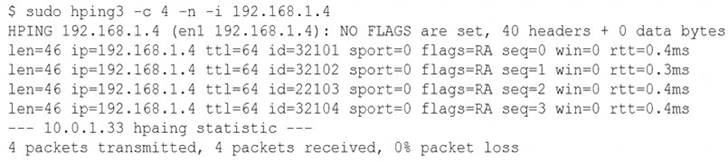
Which of the following would explain the difference in results?
- A. ICMP is being blocked by a firewall.
- B. The routing tables for ping and hping3 were different.
- C. The original ping command needed root permission to execute.
- D. hping3 is returning a false positive.
Answer: A
NEW QUESTION 4
A security analyst is reviewing the following web server log: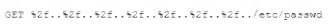
Which of the following BEST describes the issue?
- A. Directory traversal exploit
- B. Cross-site scripting
- C. SQL injection
- D. Cross-site request forgery
Answer: A
NEW QUESTION 5
An executive assistant wants to onboard a new cloud based product to help with business analytics and dashboarding. When of the following would be the BEST integration option for the service?
- A. Manually log in to the service and upload data files on a regular basis.
- B. Have the internal development team script connectivity and file translate to the new service.
- C. Create a dedicated SFTP sue and schedule transfers to ensue file transport security
- D. Utilize the cloud products API for supported and ongoing integrations
Answer: A
NEW QUESTION 6
As part of a review of modern response plans, which of the following is MOST important for an organization lo understand when establishing the breach notification period?
- A. Organizational policies
- B. Vendor requirements and contracts
- C. Service-level agreements
- D. Legal requirements
Answer: D
NEW QUESTION 7
An organization has several system that require specific logons Over the past few months, the security analyst has noticed numerous failed logon attempts followed by password resets. Which of the following should the analyst do to reduce the occurrence of legitimate failed logons and password resets?
- A. Use SSO across all applications
- B. Perform a manual privilege review
- C. Adjust the current monitoring and logging rules
- D. Implement multifactor authentication
Answer: B
NEW QUESTION 8
Which of the following BEST articulates the benefit of leveraging SCAP in an organization’s cybersecurity analysis toolset?
- A. It automatically performs remedial configuration changes to enterprise security services
- B. It enables standard checklist and vulnerability analysis expressions for automation
- C. It establishes a continuous integration environment for software development operations
- D. It provides validation of suspected system vulnerabilities through workflow orchestration
Answer: B
NEW QUESTION 9
A security analyst is reviewing the following log entries to identify anomalous activity:
Which of the following attack types is occurring?
- A. Directory traversal
- B. SQL injection
- C. Buffer overflow
- D. Cross-site scripting
Answer: A
NEW QUESTION 10
A new on-premises application server was recently installed on the network. Remote access to the server was enabled for vendor support on required ports, but recent security reports show large amounts of data are being sent to various unauthorized networks through those ports. Which of the following configuration changes must be implemented to resolve this security issue while still allowing remote vendor access?
- A. Apply a firewall application server rule.
- B. Whitelist the application server.
- C. Sandbox the application server.
- D. Enable port security.
- E. Block the unauthorized networks.
Answer: B
NEW QUESTION 11
A security analyst is evaluating two vulnerability management tools for possible use in an organization. The analyst set up each of the tools according to the respective vendor's instructions and generated a report of vulnerabilities that ran against the same target server.
Tool A reported the following: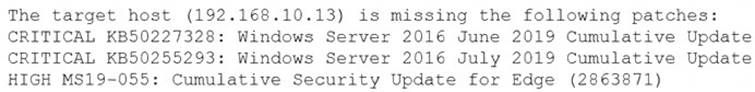
Tool B reported the following: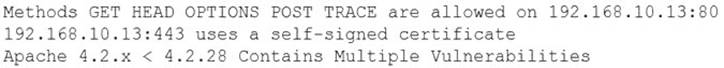
Which of the following BEST describes the method used by each tool? (Choose two.)
- A. Tool A is agent based.
- B. Tool A used fuzzing logic to test vulnerabilities.
- C. Tool A is unauthenticated.
- D. Tool B utilized machine learning technology.
- E. Tool B is agent based.
- F. Tool B is unauthenticated.
Answer: CE
NEW QUESTION 12
A security analyst discovered a specific series of IP addresses that are targeting an organization. None of the attacks have been successful. Which of the following should the security analyst perform NEXT?
- A. Begin blocking all IP addresses within that subnet.
- B. Determine the attack vector and total attack surface.
- C. Begin a kill chain analysis to determine the impact.
- D. Conduct threat research on the IP addresses
Answer: D
NEW QUESTION 13
It is important to parameterize queries to prevent:
- A. the execution of unauthorized actions against a database.
- B. a memory overflow that executes code with elevated privileges.
- C. the establishment of a web shell that would allow unauthorized access.
- D. the queries from using an outdated library with security vulnerabilities.
Answer: A
NEW QUESTION 14
After a breach involving the exfiltration of a large amount of sensitive data a security analyst is reviewing the following firewall logs to determine how the breach occurred: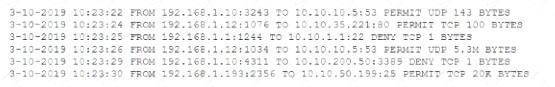
Which of the following IP addresses does the analyst need to investigate further?
- A. 192.168.1.1
- B. 192.168.1.10
- C. 192.168.1.12
- D. 192.168.1.193
Answer: C
NEW QUESTION 15
The computer incident response team at a multinational company has determined that a breach of sensitive data has occurred in which a threat actor has compromised the organization’s email system. Per the incident response procedures, this breach requires notifying the board immediately. Which of the following would be the BEST method of communication?
- A. Post of the company blog
- B. Corporate-hosted encrypted email
- C. VoIP phone call
- D. Summary sent by certified mail
- E. Externally hosted instant message
Answer: C
NEW QUESTION 16
......
Recommend!! Get the Full CS0-002 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/CS0-002-dumps.html (New 220 Q&As Version)
