Cause all that matters here is passing the Cisco 200-201 exam. Cause all that you need is a high score of 200-201 Understanding Cisco Cybersecurity Operations Fundamentals exam. The only one thing you need to do is downloading Pass4sure 200-201 exam study guides now. We will not let you down with our money-back guarantee.
Free demo questions for Cisco 200-201 Exam Dumps Below:
NEW QUESTION 1
Refer to the exhibit.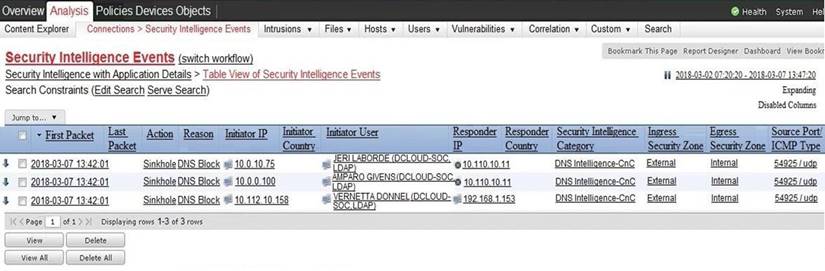
Which two elements in the table are parts of the 5-tuple? (Choose two.)
- A. First Packet
- B. Initiator User
- C. Ingress Security Zone
- D. Source Port
- E. Initiator IP
Answer: DE
NEW QUESTION 2
Which regular expression matches "color" and "colour"?
- A. colo?ur
- B. col[08]+our
- C. colou?r
- D. col[09]+our
Answer: C
NEW QUESTION 3
What is an advantage of symmetric over asymmetric encryption?
- A. A key is generated on demand according to data type.
- B. A one-time encryption key is generated for data transmission
- C. It is suited for transmitting large amounts of data.
- D. It is a faster encryption mechanism for sessions
Answer: D
NEW QUESTION 4
What is the difference between inline traffic interrogation (TAPS) and traffic mirroring (SPAN)?
- A. TAPS interrogation is more complex because traffic mirroring applies additional tags to data and SPAN does not alter integrity and provides full duplex network.
- B. SPAN results in more efficient traffic analysis, and TAPS is considerably slower due to latency caused by mirroring.
- C. TAPS replicates the traffic to preserve integrity, and SPAN modifies packets before sending them to other analysis tools
- D. SPAN ports filter out physical layer errors, making some types of analyses more difficult, and TAPS receives all packets, including physical errors.
Answer: D
NEW QUESTION 5
What is the difference between a threat and a risk?
- A. Threat represents a potential danger that could take advantage of a weakness in a system
- B. Risk represents the known and identified loss or danger in the system
- C. Risk represents the nonintentional interaction with uncertainty in the system
- D. Threat represents a state of being exposed to an attack or a compromise, either physically or logically.
Answer: A
Explanation:
A threat is any potential danger to an asset. If a vulnerability exists but has not yet been exploited—or, more importantly, it is not yet publicly known—the threat is latent and not yet realized.
NEW QUESTION 6
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
- A. Tapping interrogation replicates signals to a separate port for analyzing traffic
- B. Tapping interrogations detect and block malicious traffic
- C. Inline interrogation enables viewing a copy of traffic to ensure traffic is in compliance with security policies
- D. Inline interrogation detects malicious traffic but does not block the traffic
Answer: A
Explanation:
A network TAP is a simple device that connects directly to the cabling infrastructure to split or copy packets for use in analysis, security, or general network management
NEW QUESTION 7
An engineer runs a suspicious file in a sandbox analysis tool to see the outcome. The analysis report shows that outbound callouts were made post infection.
Which two pieces of information from the analysis report are needed to investigate the callouts? (Choose two.)
- A. signatures
- B. host IP addresses
- C. file size
- D. dropped files
- E. domain names
Answer: BE
NEW QUESTION 8
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
- A. server name, trusted subordinate CA, and private key
- B. trusted subordinate CA, public key, and cipher suites
- C. trusted CA name, cipher suites, and private key
- D. server name, trusted CA, and public key
Answer: D
NEW QUESTION 9
Refer to the exhibit.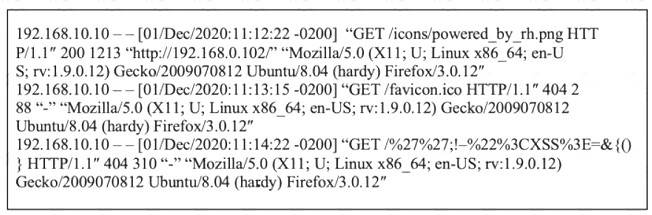
What is occurring within the exhibit?
- A. regular GET requests
- B. XML External Entities attack
- C. insecure deserialization
- D. cross-site scripting attack
Answer: A
NEW QUESTION 10
How does statistical detection differ from rule-based detection?
- A. Statistical detection involves the evaluation of events, and rule-based detection requires an evaluated set of events to function.
- B. Statistical detection defines legitimate data over time, and rule-based detection works on a predefined set of rules
- C. Rule-based detection involves the evaluation of events, and statistical detection requires an evaluated set of events to function Rule-based detection defines
- D. legitimate data over a period of time, and statistical detection works on a predefined set of rules
Answer: B
NEW QUESTION 11
Refer to the exhibit.
An engineer is reviewing a Cuckoo report of a file. What must the engineer interpret from the report?
- A. The file will appear legitimate by evading signature-based detection.
- B. The file will not execute its behavior in a sandbox environment to avoid detection.
- C. The file will insert itself into an application and execute when the application is run.
- D. The file will monitor user activity and send the information to an outside source.
Answer: B
NEW QUESTION 12
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
- A. decision making
- B. rapid response
- C. data mining
- D. due diligence
Answer: D
NEW QUESTION 13
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
- A. DAC requires explicit authorization for a given user on a given object, and RBAC requires specific conditions.
- B. RBAC access is granted when a user meets specific conditions, and in DAC, permissions are applied on user and group levels.
- C. RBAC is an extended version of DAC where you can add an extra level of authorization based on time.
- D. DAC administrators pass privileges to users and groups, and in RBAC, permissions are applied to specific groups
Answer: A
NEW QUESTION 14
Refer to the exhibit.
Which component is identifiable in this exhibit?
- A. Trusted Root Certificate store on the local machine
- B. Windows PowerShell verb
- C. Windows Registry hive
- D. local service in the Windows Services Manager
Answer: C
Explanation:
https://docs.microsoft.com/en-us/windows/win32/sysinfo/registry-hives https://ldapwiki.com/wiki/HKEY_LOCAL_MACHINE#:~:text=HKEY_LOCAL_MACHINE%20Windows%2
NEW QUESTION 15
An analyst discovers that a legitimate security alert has been dismissed. Which signature caused this impact on network traffic?
- A. true negative
- B. false negative
- C. false positive
- D. true positive
Answer: B
Explanation:
A false negative occurs when the security system (usually a WAF) fails to identify a threat. It produces a “negative” outcome (meaning that no threat has been observed), even though a threat exists.
NEW QUESTION 16
How does an SSL certificate impact security between the client and the server?
- A. by enabling an authenticated channel between the client and the server
- B. by creating an integrated channel between the client and the server
- C. by enabling an authorized channel between the client and the server
- D. by creating an encrypted channel between the client and the server
Answer: D
NEW QUESTION 17
Refer to the exhibit.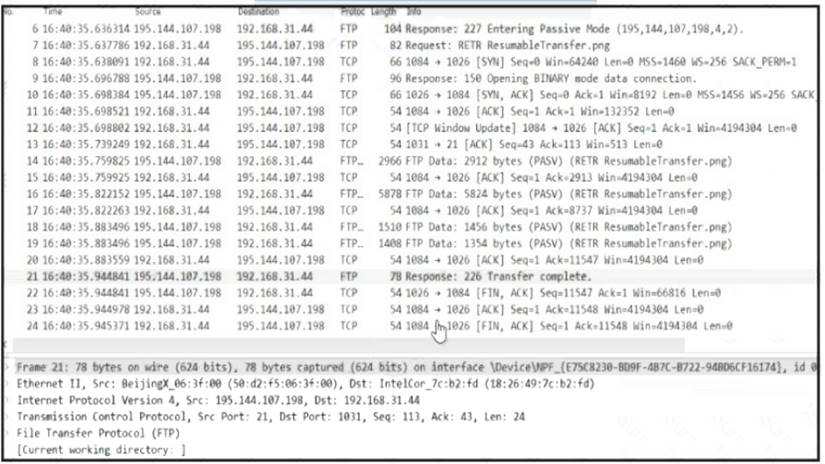
Which frame numbers contain a file that is extractable via TCP stream within Wireshark?
- A. 7,14, and 21
- B. 7 and 21
- C. 14,16,18, and 19
- D. 7 to 21
Answer: B
NEW QUESTION 18
How is NetFlow different from traffic mirroring?
- A. NetFlow collects metadata and traffic mirroring clones data.
- B. Traffic mirroring impacts switch performance and NetFlow does not.
- C. Traffic mirroring costs less to operate than NetFlow.
- D. NetFlow generates more data than traffic mirroring.
Answer: A
NEW QUESTION 19
......
P.S. Easily pass 200-201 Exam with 263 Q&As DumpSolutions.com Dumps & pdf Version, Welcome to Download the Newest DumpSolutions.com 200-201 Dumps: https://www.dumpsolutions.com/200-201-dumps/ (263 New Questions)
