Accurate of 200-201 exam topics materials and questions pool for Cisco certification for candidates, Real Success Guaranteed with Updated 200-201 pdf dumps vce Materials. 100% PASS Understanding Cisco Cybersecurity Operations Fundamentals exam Today!
Cisco 200-201 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
A developer is working on a project using a Linux tool that enables writing processes to obtain these required results: If the process is unsuccessful, a negative value is returned.
If the process is unsuccessful, a negative value is returned. If the process is successful, 0 value is returned to the child process, and the process ID is sent to the parent process.
If the process is successful, 0 value is returned to the child process, and the process ID is sent to the parent process.
Which component results from this operation?
- A. parent directory name of a file pathname
- B. process spawn scheduled
- C. macros for managing CPU sets
- D. new process created by parent process
Answer: D
Explanation:
There are two tasks with specially distinguished process IDs: swapper or sched has process ID 0 and is responsible for paging, and is actually part of the kernel rather than a normal user-mode process. Process ID 1 is usually the init process primarily responsible for starting and shutting down the system. Originally, process ID 1 was not specifically reserved for init by any technical measures: it simply had this ID as a natural consequence of being the first process invoked by the kernel. More recent Unix systems typically have additional kernel components visible as 'processes', in which case PID 1 is actively reserved for the init process to maintain consistency with older systems
NEW QUESTION 2
Which system monitors local system operation and local network access for violations of a security policy?
- A. host-based intrusion detection
- B. systems-based sandboxing
- C. host-based firewall
- D. antivirus
Answer: A
Explanation:
HIDS is capable of monitoring the internals of a computing system as well as the network packets on its network interfaces. Host-based firewall is a piece of software running on a single Host that can restrict incoming and outgoing Network activity for that host only.
NEW QUESTION 3
What ate two categories of DDoS attacks? (Choose two.)
- A. split brain
- B. scanning
- C. phishing
- D. reflected
- E. direct
Answer: DE
NEW QUESTION 4
Which two components reduce the attack surface on an endpoint? (Choose two.)
- A. secure boot
- B. load balancing
- C. increased audit log levels
- D. restricting USB ports
- E. full packet captures at the endpoint
Answer: AD
NEW QUESTION 5
Which security principle is violated by running all processes as root or administrator?
- A. principle of least privilege
- B. role-based access control
- C. separation of duties
- D. trusted computing base
Answer: A
NEW QUESTION 6
What is the difference between deep packet inspection and stateful inspection?
- A. Deep packet inspection is more secure than stateful inspection on Layer 4
- B. Stateful inspection verifies contents at Layer 4 and deep packet inspection verifies connection at Layer 7
- C. Stateful inspection is more secure than deep packet inspection on Layer 7
- D. Deep packet inspection allows visibility on Layer 7 and stateful inspection allows visibility on Layer 4
Answer: D
NEW QUESTION 7
Which vulnerability type is used to read, write, or erase information from a database?
- A. cross-site scripting
- B. cross-site request forgery
- C. buffer overflow
- D. SQL injection
Answer: D
NEW QUESTION 8
Refer to the exhibit.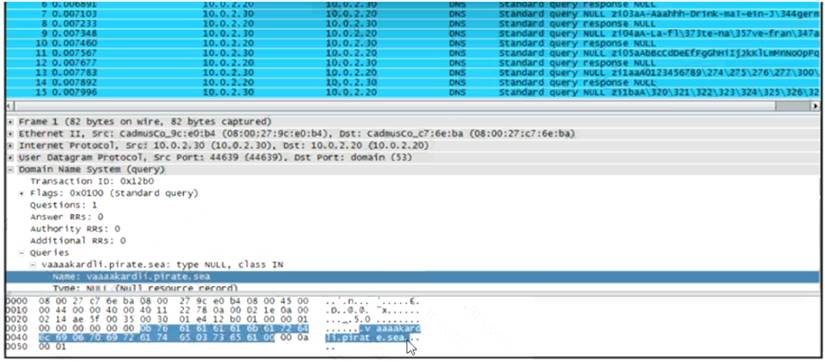
What is occurring?
- A. ARP flood
- B. DNS amplification
- C. ARP poisoning
- D. DNS tunneling
Answer: D
NEW QUESTION 9
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?
- A. The threat actor used a dictionary-based password attack to obtain credentials.
- B. The threat actor gained access to the system by known credentials.
- C. The threat actor used the teardrop technique to confuse and crash login services.
- D. The threat actor used an unknown vulnerability of the operating system that went undetected.
Answer: C
NEW QUESTION 10
Which category relates to improper use or disclosure of PII data?
- A. legal
- B. compliance
- C. regulated
- D. contractual
Answer: C
NEW QUESTION 11
At which layer is deep packet inspection investigated on a firewall?
- A. internet
- B. transport
- C. application
- D. data link
Answer: C
Explanation:
Deep packet inspection is a form of packet filtering usually carried out as a function of your firewall. It is applied at the Open Systems Interconnection's application layer. Deep packet inspection evaluates the contents of a packet that is going through a checkpoint.
NEW QUESTION 12
Which security technology allows only a set of pre-approved applications to run on a system?
- A. application-level blacklisting
- B. host-based IPS
- C. application-level whitelisting
- D. antivirus
Answer: C
NEW QUESTION 13
What is a difference between SOAR and SIEM?
- A. SOAR platforms are used for threat and vulnerability management, but SIEM applications are not
- B. SIEM applications are used for threat and vulnerability management, but SOAR platforms are not
- C. SOAR receives information from a single platform and delivers it to a SIEM
- D. SIEM receives information from a single platform and delivers it to a SOAR
Answer: A
NEW QUESTION 14
Refer to the exhibit.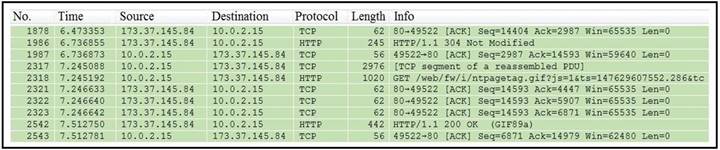
Which packet contains a file that is extractable within Wireshark?
- A. 2317
- B. 1986
- C. 2318
- D. 2542
Answer: D
NEW QUESTION 15
What describes the impact of false-positive alerts compared to false-negative alerts?
- A. A false negative is alerting for an XSS attac
- B. An engineer investigates the alert and discovers that an XSS attack happened A false positive is when an XSS attack happens and no alert is raised
- C. A false negative is a legitimate attack triggering a brute-force aler
- D. An engineer investigates the alert and finds out someone intended to break into the system A false positive is when no alert and no attack is occurring
- E. A false positive is an event alerting for a brute-force attack An engineer investigates the alert and discovers that a legitimate user entered the wrong credential several times A false negative is when a threat actor tries to brute-force attack a system and no alert is raised.
- F. A false positive is an event alerting for an SQL injection attack An engineer investigates the alert and discovers that an attack attempt was blocked by IPS A false negative is when the attack gets detected but succeeds and results in a breach.
Answer: C
NEW QUESTION 16
How does certificate authority impact a security system?
- A. It authenticates client identity when requesting SSL certificate
- B. It validates domain identity of a SSL certificate
- C. It authenticates domain identity when requesting SSL certificate
- D. It validates client identity when communicating with the server
Answer: B
NEW QUESTION 17
What is the difference between indicator of attack (loA) and indicators of compromise (loC)?
- A. loA is the evidence that a security breach has occurred, and loC allows organizations to act before the vulnerability can be exploited.
- B. loA refers to the individual responsible for the security breach, and loC refers to the resulting loss.
- C. loC is the evidence that a security breach has occurred, and loA allows organizations to act before the vulnerability can be exploited.
- D. loC refers to the individual responsible for the security breach, and loA refers to the resulting loss.
Answer: C
NEW QUESTION 18
Which of these describes SOC metrics in relation to security incidents?
- A. time it takes to detect the incident
- B. time it takes to assess the risks of the incident
- C. probability of outage caused by the incident
- D. probability of compromise and impact caused by the incident
Answer: A
NEW QUESTION 19
......
Recommend!! Get the Full 200-201 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/200-201-dumps.html (New 263 Q&As Version)
