Exambible 200-201 Questions are updated and all 200-201 answers are verified by experts. Once you have completely prepared with our 200-201 exam prep kits you will be ready for the real 200-201 exam without a problem. We have Renew Cisco 200-201 dumps study guide. PASSED 200-201 First attempt! Here What I Did.
Online Cisco 200-201 free dumps demo Below:
NEW QUESTION 1
An investigator is examining a copy of an ISO file that is stored in CDFS format. What type of evidence is this file?
- A. data from a CD copied using Mac-based system
- B. data from a CD copied using Linux system
- C. data from a DVD copied using Windows system
- D. data from a CD copied using Windows
Answer: B
Explanation:
CDfs is a virtual file system for Unix-like operating systems; it provides access to data and audio tracks on Compact Discs. When the CDfs driver mounts a Compact Disc, it represents each track as a file. This is consistent with the Unix convention "everything is a file". Source: https://en.wikipedia.org/wiki/CDfs
NEW QUESTION 2
What is the difference between deep packet inspection and stateful inspection?
- A. Stateful inspection verifies contents at Layer 4. and deep packet inspection verifies connection at Layer 7.
- B. Stateful inspection is more secure than deep packet inspection on Layer 7.
- C. Deep packet inspection is more secure than stateful inspection on Layer 4.
- D. Deep packet inspection allows visibility on Layer 7, and stateful inspection allows visibility on Layer 4.
Answer: D
NEW QUESTION 3
What is a collection of compromised machines that attackers use to carry out a DDoS attack?
- A. subnet
- B. botnet
- C. VLAN
- D. command and control
Answer: B
NEW QUESTION 4
Which open-sourced packet capture tool uses Linux and Mac OS X operating systems?
- A. NetScout
- B. tcpdump
- C. SolarWinds
- D. netsh
Answer: B
NEW QUESTION 5
What is the relationship between a vulnerability and a threat?
- A. A threat exploits a vulnerability
- B. A vulnerability is a calculation of the potential loss caused by a threat
- C. A vulnerability exploits a threat
- D. A threat is a calculation of the potential loss caused by a vulnerability
Answer: A
NEW QUESTION 6
A security expert is working on a copy of the evidence, an ISO file that is saved in CDFS format. Which type of evidence is this file?
- A. CD data copy prepared in Windows
- B. CD data copy prepared in Mac-based system
- C. CD data copy prepared in Linux system
- D. CD data copy prepared in Android-based system
Answer: A
NEW QUESTION 7
A user received an email attachment named "Hr405-report2609-empl094.exe" but did not run it. Which category of the cyber kill chain should be assigned to this type of event?
- A. installation
- B. reconnaissance
- C. weaponization
- D. delivery
Answer: D
NEW QUESTION 8
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
- A. MAC is controlled by the discretion of the owner and DAC is controlled by an administrator
- B. MAC is the strictest of all levels of control and DAC is object-based access
- C. DAC is controlled by the operating system and MAC is controlled by an administrator
- D. DAC is the strictest of all levels of control and MAC is object-based access
Answer: B
NEW QUESTION 9
Which tool gives the ability to see session data in real time?
- A. tcpdstat
- B. trafdump
- C. tcptrace
- D. trafshow
Answer: C
NEW QUESTION 10
Which technology prevents end-device to end-device IP traceability?
- A. encryption
- B. load balancing
- C. NAT/PAT
- D. tunneling
Answer: C
NEW QUESTION 11
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario'?
- A. X 509 certificates
- B. RADIUS server
- C. CA server
- D. web application firewall
Answer: A
NEW QUESTION 12
Refer to the exhibit.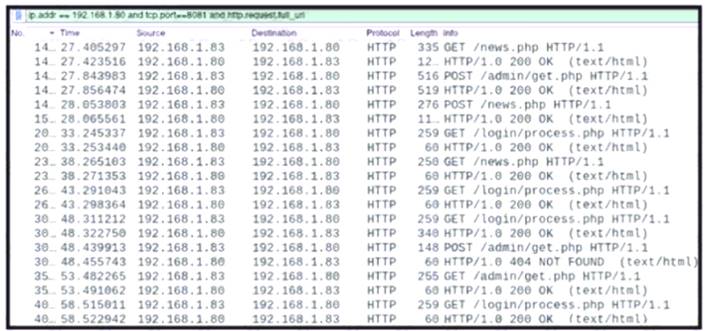
A network administrator is investigating suspicious network activity by analyzing captured traffic. An engineer notices abnormal behavior and discovers that the default user agent is present in the headers of
requests and data being transmitted What is occurring?
- A. indicators of denial-of-service attack due to the frequency of requests
- B. garbage flood attack attacker is sending garbage binary data to open ports
- C. indicators of data exfiltration HTTP requests must be plain text
- D. cache bypassing attack: attacker is sending requests for noncacheable content
Answer: D
NEW QUESTION 13
A threat actor penetrated an organization's network. Using the 5-tuple approach, which data points should the analyst use to isolate the compromised host in a grouped set of logs?
- A. event name, log source, time, source IP, and host name
- B. protocol, source IP, source port, destination IP, and destination port
- C. event name, log source, time, source IP, and username
- D. protocol, log source, source IP, destination IP, and host name
Answer: B
NEW QUESTION 14
Which type of evidence supports a theory or an assumption that results from initial evidence?
- A. probabilistic
- B. indirect
- C. best
- D. corroborative
Answer: D
Explanation:
Corroborating evidence (or corroboration) is evidence that tends to support a theory or an assumption deduced by some initial evidence. This corroborating evidence confirms the proposition. Cisco CyberOps Associate CBROPS 200-201 Official Cert Guide
NEW QUESTION 15
Refer to the exhibit.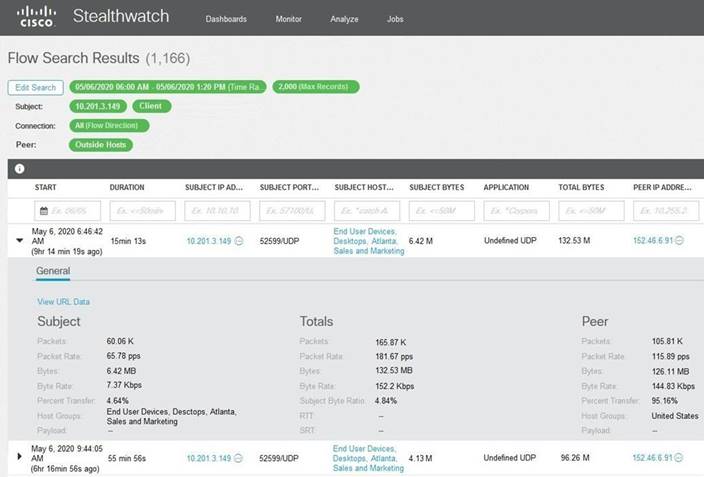
What is the potential threat identified in this Stealthwatch dashboard?
- A. Host 10.201.3.149 is sending data to 152.46.6.91 using TCP/443.
- B. Host 152.46.6.91 is being identified as a watchlist country for data transfer.
- C. Traffic to 152.46.6.149 is being denied by an Advanced Network Control policy.
- D. Host 10.201.3.149 is receiving almost 19 times more data than is being sent to host 152.46.6.91.
Answer: D
NEW QUESTION 16
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
- A. central key management server
- B. web of trust
- C. trusted certificate authorities
- D. registration authority data
Answer: C
NEW QUESTION 17
Which type of data consists of connection level, application-specific records generated from network traffic?
- A. transaction data
- B. location data
- C. statistical data
- D. alert data
Answer: A
NEW QUESTION 18
What is a difference between inline traffic interrogation and traffic mirroring?
- A. Inline inspection acts on the original traffic data flow
- B. Traffic mirroring passes live traffic to a tool for blocking
- C. Traffic mirroring inspects live traffic for analysis and mitigation
- D. Inline traffic copies packets for analysis and security
Answer: A
Explanation:
Inline traffic interrogation analyzes traffic in real time and has the ability to prevent certain traffic from being forwarded Traffic mirroring doesn't pass the live traffic instead it copies traffic from one or more source ports and sends the copied traffic to one or more destinations for analysis by a network analyzer or other monitoring device
NEW QUESTION 19
......
P.S. Certleader now are offering 100% pass ensure 200-201 dumps! All 200-201 exam questions have been updated with correct answers: https://www.certleader.com/200-201-dumps.html (263 New Questions)
