We provide real 200-201 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Cisco 200-201 Exam quickly & easily. The 200-201 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Cisco 200-201 dumps pdf and vce product and material, you can easily pass the 200-201 exam.
Free demo questions for Cisco 200-201 Exam Dumps Below:
NEW QUESTION 1
Refer to the exhibit.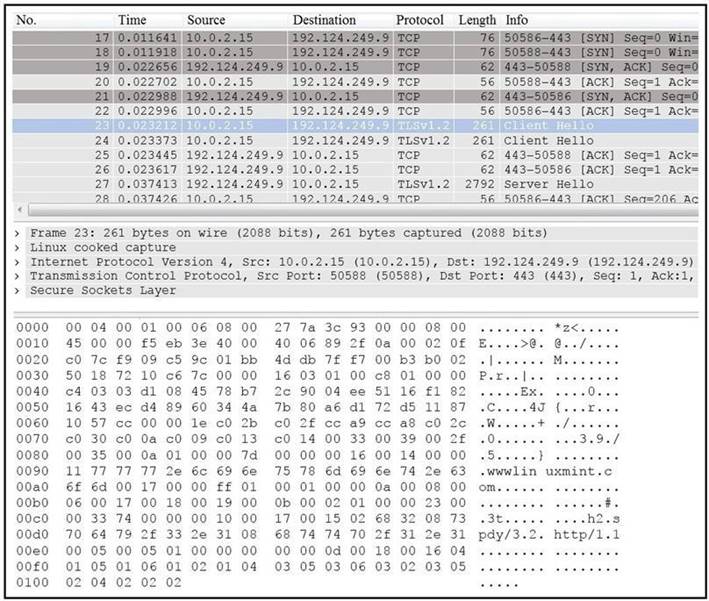
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.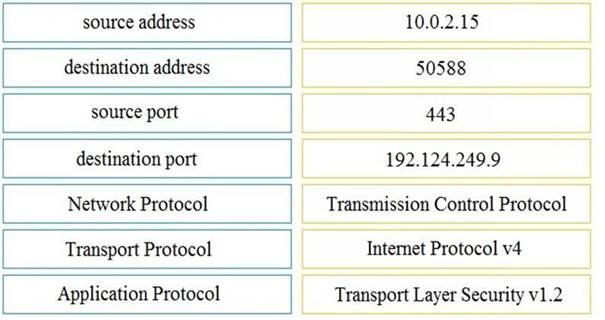
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
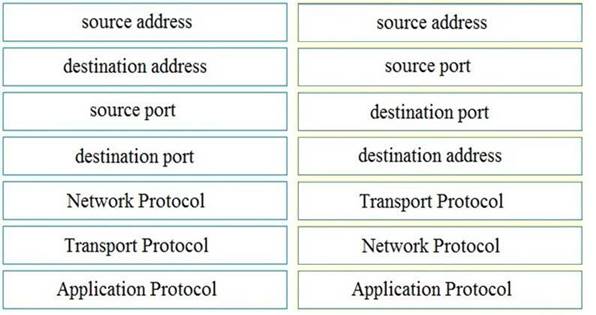
NEW QUESTION 2
Refer to the exhibit.
An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
- A. Identified a firewall device preventing the pert state from being returned.
- B. Identified open SMB ports on the server
- C. Gathered information on processes running on the server
- D. Gathered a list of Active Directory users
Answer: C
NEW QUESTION 3
Drag and drop the uses on the left onto the type of security system on the right.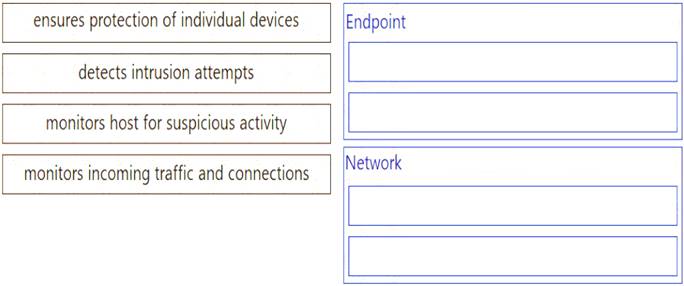
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
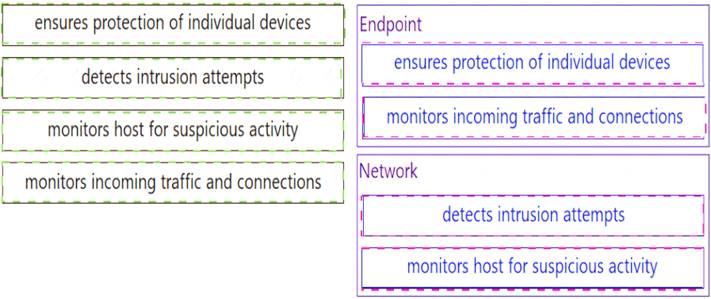
NEW QUESTION 4
Refer to the exhibit.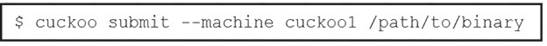
Which event is occurring?
- A. A binary named "submit" is running on VM cuckoo1.
- B. A binary is being submitted to run on VM cuckoo1
- C. A binary on VM cuckoo1 is being submitted for evaluation
- D. A URL is being evaluated to see if it has a malicious binary
Answer: B
Explanation:
https://cuckoo.readthedocs.io/en/latest/usage/submit/
NEW QUESTION 5
What is obtained using NetFlow?
- A. session data
- B. application logs
- C. network downtime report
- D. full packet capture
Answer: A
NEW QUESTION 6
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
Solution:
Delivery: This step involves transmitting the weapon to the target.
Weaponization: In this step, the intruder creates a malware weapon like a virus, worm or such in order to exploit the vulnerabilities of the target. Depending on the target and the purpose of the attacker, this malware can exploit new, undetected vulnerabilities (also known as the zero-day exploits) or it can focus on a combination of different vulnerabilities.
Reconnaissance: In this step, the attacker / intruder chooses their target. Then they conduct an in-depth research on this target to identify its vulnerabilities that can be exploited.
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 7
What is the difference between statistical detection and rule-based detection models?
- A. Rule-based detection involves the collection of data in relation to the behavior of legitimate users over a period of time
- B. Statistical detection defines legitimate data of users over a period of time and rule-based detection defines it on an IF/THEN basis
- C. Statistical detection involves the evaluation of an object on its intended actions before it executes that behavior
- D. Rule-based detection defines legitimate data of users over a period of time and statistical detection defines it on an IF/THEN basis
Answer: B
NEW QUESTION 8
Which NIST IR category stakeholder is responsible for coordinating incident response among various business units, minimizing damage, and reporting to regulatory agencies?
- A. CSIRT
- B. PSIRT
- C. public affairs
- D. management
Answer: D
NEW QUESTION 9
What does an attacker use to determine which network ports are listening on a potential target device?
- A. man-in-the-middle
- B. port scanning
- C. SQL injection
- D. ping sweep
Answer: B
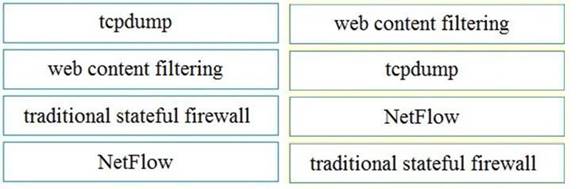
NEW QUESTION 10
Refer to the exhibit.
Which type of attack is being executed?
- A. SQL injection
- B. cross-site scripting
- C. cross-site request forgery
- D. command injection
Answer: A
NEW QUESTION 11
Which are two denial-of-service attacks? (Choose two.)
- A. TCP connections
- B. ping of death
- C. man-in-the-middle
- D. code-red
- E. UDP flooding
Answer: BE
NEW QUESTION 12
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
- A. detection and analysis
- B. post-incident activity
- C. vulnerability management
- D. risk assessment
- E. vulnerability scoring
Answer: AB
NEW QUESTION 13
An intruder attempted malicious activity and exchanged emails with a user and received corporate information, including email distribution lists. The intruder asked the user to engage with a link in an email. When the fink launched, it infected machines and the intruder was able to access the corporate network.
Which testing method did the intruder use?
- A. social engineering
- B. eavesdropping
- C. piggybacking
- D. tailgating
Answer: A
NEW QUESTION 14
What is the function of a command and control server?
- A. It enumerates open ports on a network device
- B. It drops secondary payload into malware
- C. It is used to regain control of the network after a compromise
- D. It sends instruction to a compromised system
Answer: D
NEW QUESTION 15
During which phase of the forensic process are tools and techniques used to extract information from the collected data?
- A. investigation
- B. examination
- C. reporting
- D. collection
Answer: D
NEW QUESTION 16
Refer to the exhibit.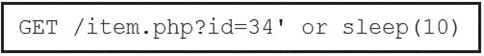
This request was sent to a web application server driven by a database. Which type of web server attack is represented?
- A. parameter manipulation
- B. heap memory corruption
- C. command injection
- D. blind SQL injection
Answer: D
NEW QUESTION 17
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
- A. The RST flag confirms the beginning of the TCP connection, and the ACK flag responds when the datafor the payload is complete
- B. The ACK flag confirms the beginning of the TCP connection, and the RST flag responds when the data for the payload is complete
- C. The RST flag confirms the receipt of the prior segment, and the ACK flag allows for the spontaneous termination of a connection
- D. The ACK flag confirms the receipt of the prior segment, and the RST flag allows for the spontaneous termination of a connection
Answer: D
NEW QUESTION 18
Drag and drop the technology on the left onto the data type the technology provides on the right.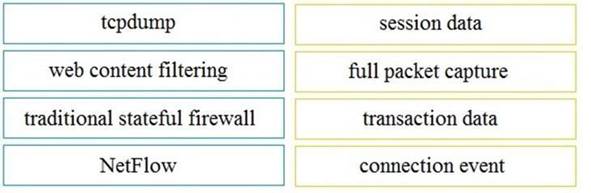
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 19
......
100% Valid and Newest Version 200-201 Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/200-201-dumps.html (New 263 Q&As)
